Home > Storage > PowerScale (Isilon) > Product Documentation > Protocols > PowerScale OneFS NFS Design Considerations and Best Practices > Packet capture tool and analysis
Packet capture tool and analysis
-
It is useful to capture NFS packet during the troubleshooting. You can figure out the communication details between the server and client. On Linux environment, you can use tcpdump tool to capture the traffic on the server or client. For the usage of tcpdump, you can refer to the man page of tcpdump. For OneFS cluster, it is more convenient to use isi_netlogger command tool to capture the traffic in the cluster on more than one node. You can get the usage through the help output using isi_netlogger –h. Below is an example scenario about how to use these tools to analysis the NFS traffic and get the information as needed.
Assuming that an application has an issue to read/write a file on the cluster, we need to verify and find out if the actual file in the network traffic is same as the file that the application reported. So that we need to find the filename according to the filehandle in the captured packet. We use isi_netlogger to capture the packet and use Wireshark to analyze the .pcap file.
- Running the following command captures the packets on the interface mlxen2 (IP 172.16.200.41) of OneFS cluster node number 1. And only capture the traffic to and from the application host 172.16.200.160.
isi_netlogger –l mlxen2 –n 1 host 172.16.200.160
- The captured file will be stored at /ifs/netlog by OneFS. You can download the file to your local machine, and open it using Wireshark which is a feature-rich network packet analysis tool. Find the operation which accesses the file on OneFS cluster, as shows in Figure 20.
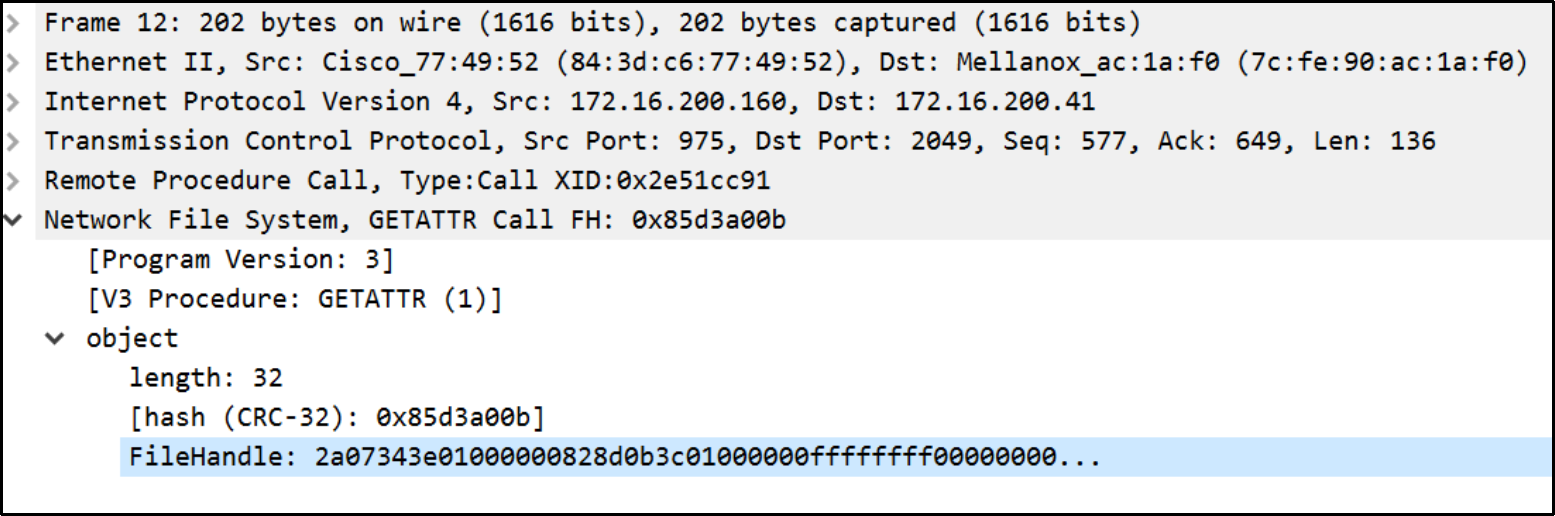
Figure 20. The NFSv3 operation filehandle
Filehandle in OneFS NFSv3 is a 32 bytes structure contains the following parts:
- File system ID (4 bytes): the exported file system identifier.
- Export (4 bytes): the unique export identifier.
- File ID (8 bytes): the file's logical inode number (LIN).
- Snap ID (4 bytes): the snapshot identifier of the root of the mount.
- Portal (4 bytes): the snapshot portal depth.
- Root LIN (8 bytes): the LIN of the root of the export.
Figure 21 is the filehandle broken into each section, the LIN in the packet capture is represented in little-endian format rather than a big-endian format. So the actual file’s LIN in OneFS is 00:00:00:01:3c:0b:8d:82 (13c0b8d82).
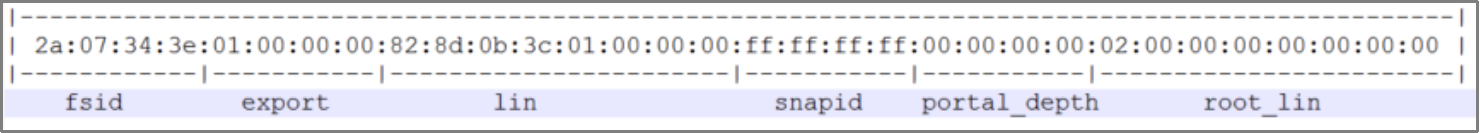
Figure 21. NFSv3 filehandle in OneFS
- Find the file path on the OneFS cluster for the obtained LIN using command isi get –L 13c0b8d82, the output is similar to the following.
# isi get -L 13c0b8d82
A valid path for LIN 0x13c0b8d82 is /ifs/test.txt
