Home > Storage > PowerScale (Isilon) > Product Documentation > Protocols > PowerScale OneFS NFS Design Considerations and Best Practices > OneFS protocol audit
OneFS protocol audit
-
OneFS allows you to audit protocol activities. All audit data is stored and protected in the cluster file system and organized by audit topic. Starting in OneFS 8.0, protocol audit tracks and stores activity performed through SMB, NFS, and HDFS protocol connections in an access zone level. You can specify which events to log in each access zone. For example, you might want to audit the default set of protocol events in the System access zone but audit only successful attempts to delete files in a different access zone.
The audit events are logged on the individual nodes where the SMB, NFS, or HDFS client initiated the activity. The events are then stored in a binary file under /ifs/.ifsvar/audit/logs. The logs automatically roll over to a new file after the size reaches 1 GB.
OneFS integration with Dell Common Event Enabler (CEE) enables third-party auditing applications to collect and analyze protocol auditing logs. Figure 5 shows a logical data flow in an NFS environment when using CEE and third-party applications. During the NFS client access the PowerScale cluster over NFS, the event will be stored as configured to the cluster, the OneFS daemon isi_adudit_cee exports protocol audit events to CEE, and then the CEE will forward protocol audit events to the consumer application.
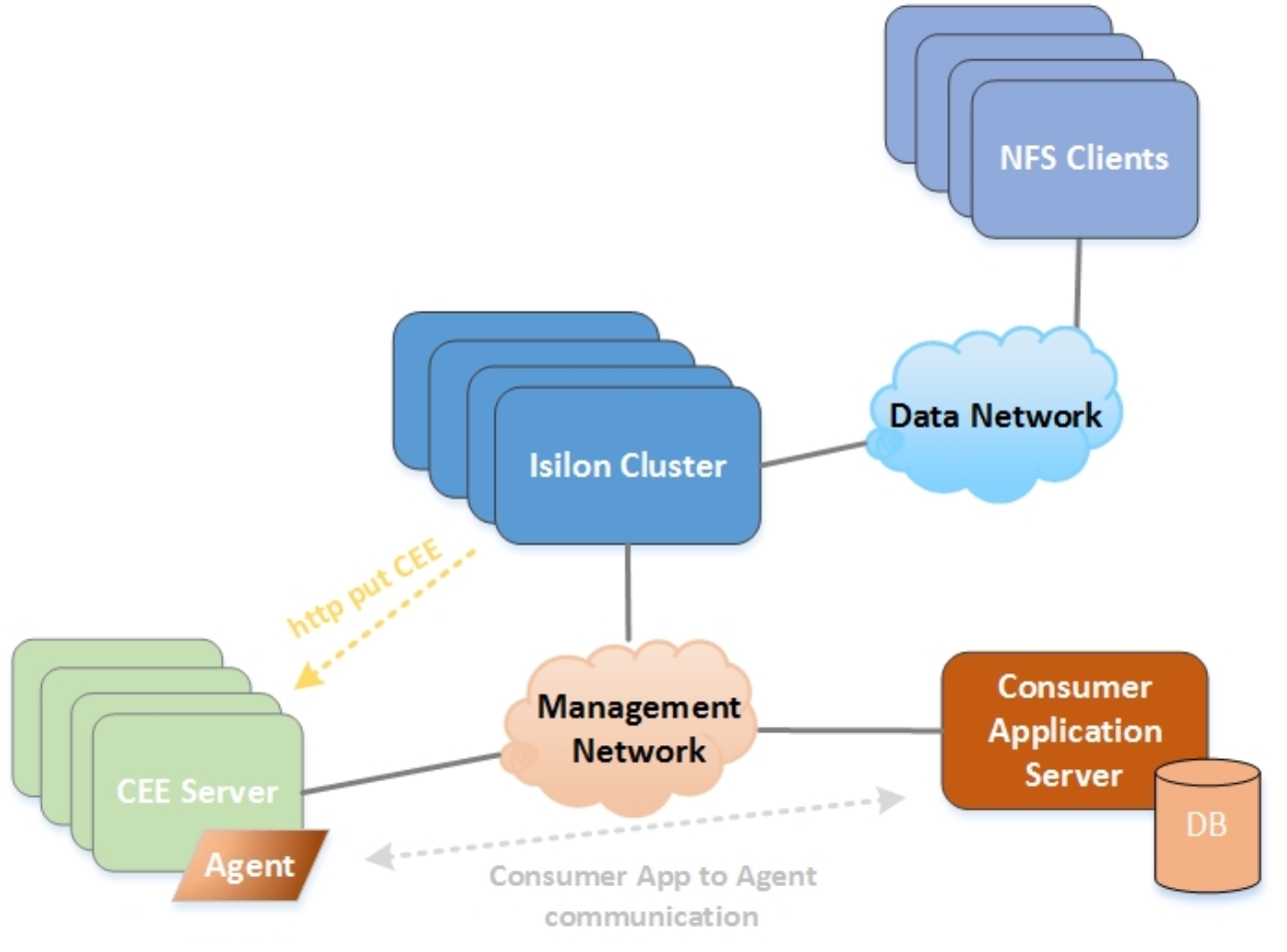
Figure 5. Protocol audit logical data flow
Note: Dell CEE does not support forwarding HDFS protocol events to a third-party application.
By default, the tracked events are create, close, delete, rename, and set_security. For the details of supported event types and its description, refer to the Auditing chapter of OneFS Web Administration Guide. Because each audited event consumes system resources, we recommend that you configure zones only for events that are needed by your auditing application. In addition, we recommend that you install and configure third-party auditing applications before you enable the OneFS auditing feature. Otherwise, all the events that are logged are forwarded to the auditing application, and a large backlog causes a delay in receiving the most current events.
