Home > Storage > PowerScale (Isilon) > Product Documentation > Protocols > PowerScale OneFS NFS Design Considerations and Best Practices > Network security considerations
Network security considerations
-
Network security is always the important area to focus on, attacks from a malicious attacker would result in a disaster and may result in service interruption to end users. As a security recommendation, shown in Figure 8, you should setup an external firewall with appropriate rules and policies to allow only the trusted clients and servers can access the cluster. Meanwhile, allow restricted access only to the ports that are required for communication and block access to all other ports on the cluster.
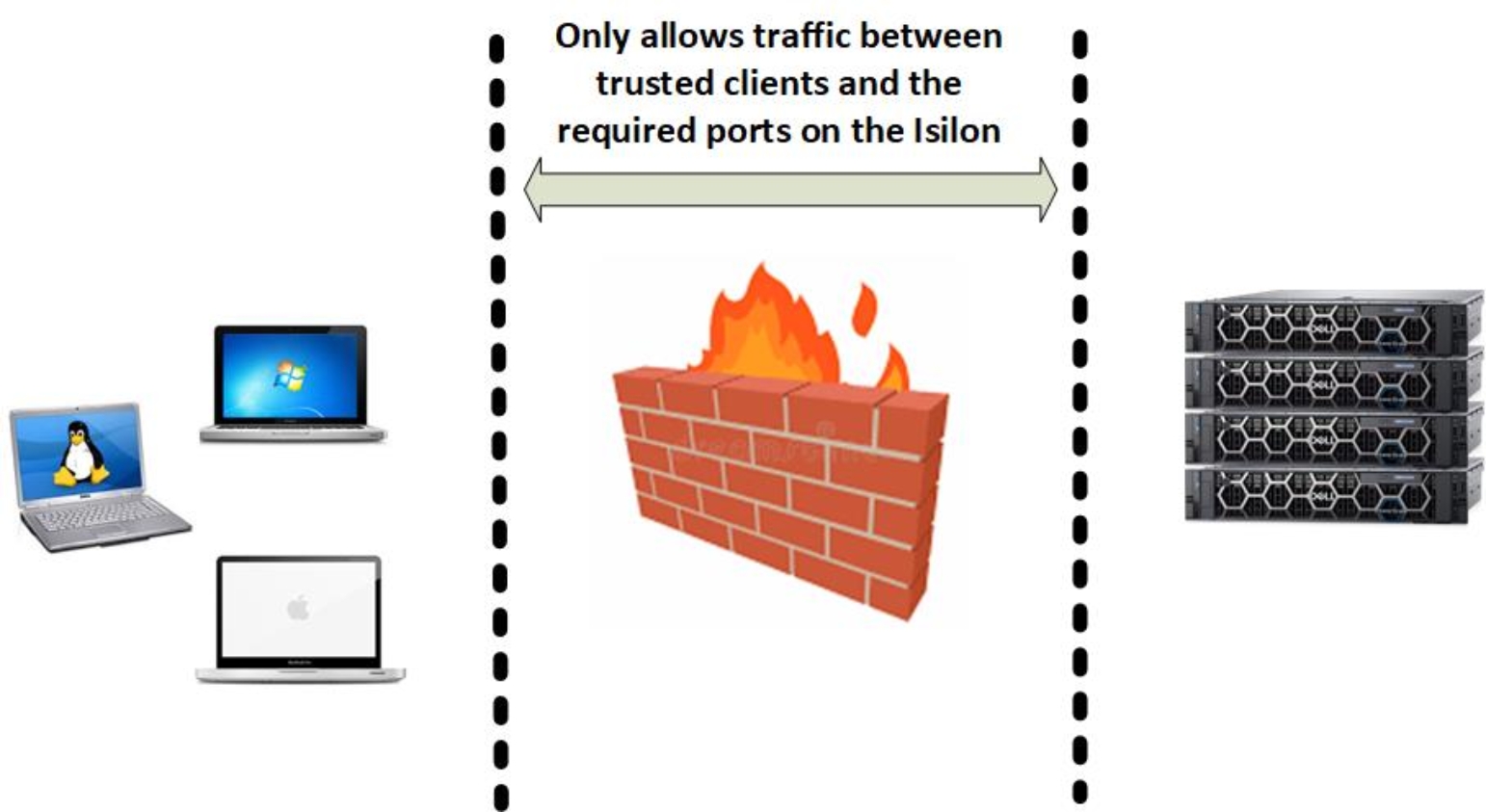
Figure 8. Protect PowerScale system with an external firewall
Table 2 shows the required ports for a client to access data in OneFS cluster over NFS protocol. As NFSv3 requires additional auxiliary protocol (mount, NLM, NSM) to provide mount service and lock capability, all of the ports in the table are required to access cluster using NFSv3. For NFSv4.x, a single protocol provides all functionalities that NFSv3 offers and only supports TCP as the transport protocol, so it is firewall friendly and only the TCP 2049 is required for a client to access cluster using NFSv4.x.
Table 2. TCP/UDP port requirement for NFS service
Port
Service
Protocol
Connection
Usage description
2049
nfs
TCP/UDP
Inbound
As NFSv3 supports both TCP and UDP in OneFS, so both of two transport protocols ports are required for NFSv3.
However, NFSv4.x supports only TCP in OneFS, so only the TCP 2049 port is needed if only the NFSv4.x service is required in your environment.
300
mountd
TCP/UDP
Inbound
NFSv3 mount service.
302
statd
TCP/UDP
Inbound
NFSv3 Network Status Monitor (NSM)
304
lockd
TCP/UDP
Inbound
NFSv3 Network Lock Manager (NLM)
111
rpc.bind
TCP/UDP
Inbound
ONC RPC portmapper that is used to locate services such as NFS, mountd. Only used by NFSv3 if NFSv4.x running on the standard registered TCP port 2049.
See NFS over RDMA for details about the RDMA-related port.
