Home > Storage > PowerScale (Isilon) > Product Documentation > Protocols > PowerScale OneFS NFS Design Considerations and Best Practices > AIMA (Authentication, Identity Management, Access)
AIMA (Authentication, Identity Management, Access)
-
When a user connects to a PowerScale cluster, OneFS checks the directory services to which the user’s access zone is connected for an account for the user. If OneFS finds an account that matches the user’s login name, OneFS verifies the user’s identity to authenticate the user. During authentication, OneFS creates an access token for the user. The token contains the user’s full identity including group memberships and OneFS uses the token later to check access to directories and files.
When OneFS authenticates users with different directory services, OneFS maps a user’s account from one directory service to the user’s accounts in other directory services within an access zone—a process known as user mapping. A Windows user account managed in Active Directory, for example, is mapped by default to a corresponding UNIX account with the same name in NIS or LDAP.
As a result, with a single token, a user can access files that were stored by a Windows computer over SMB and files that were stored by a Linux computer over NFS.
Similarly, because OneFS provides multiprotocol access to files, it must translate the permissions of Linux and UNIX files to the access control lists of Windows files. As a result, a user who connects to the cluster with a Linux computer over NFS can access files that were stored on the cluster by a Windows user with SMB.
The following diagram Figure 4 summarizes how directory services, identity mapping, policies, and permissions play a role in the OneFS system of authentication and access control. For more details about AIMA, refer to OneFS Multiprotocol Security Guide.
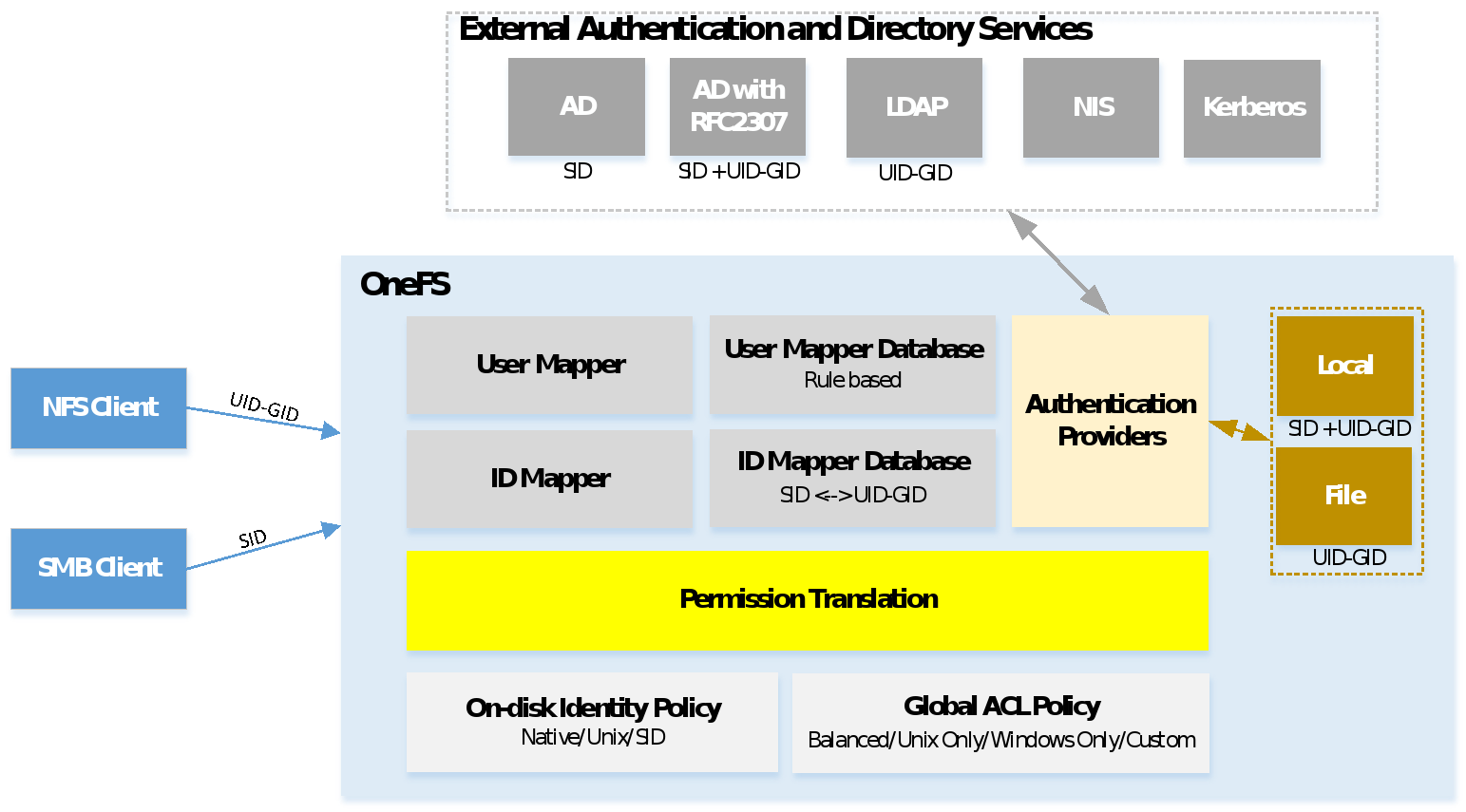
Figure 4. OneFS authentication and access control
No overlapping ID ranges and avoid common ID ranges
In the case that you contain multiple identity sources, like LDAP and Active Directory with RFC2307, you should ensure that the UID and GID ranges do not overlap. Besides, OneFS also allocates a UID and GID as needed. The default range from which OneFS automatically allocate a UID and GID is 1,000,000 to 2,000,000. Other identity source ID range must not overlap with the OneFS default range. If UIDs and GIDs overlap across two or more directory services, some users could have right to access to other users’ files.
In addition, there are UIDs and GIDs below 1000 are reserved for system, do not assign them to users or groups in the identity source.
User mapping in multiple directory services
When the name of an account in different directory services match exactly, OneFS automatically combines their access tokens into a single token. AIMA requires that SAMAccount name is populated in AD for each user. For example, the user-mapping service maps, by default, a Windows account named CORP\jane from Active Directory to a UNIX account named jane from LDAP and generates an access token that combines the group membership information from the two accounts. OneFS also automatically maps two groups with the same name. Besides the automatic user mapping, OneFS allows the administrator to map users from different directory services manually from the WebUI and CLI.
The following are some considerations for user mapping:
- Employ a consistent username strategy: The simplest configurations name users consistently, so that each UNIX user corresponds to a similarly named Windows user. Such a convention allows rules with wildcard characters to match names and map them without explicitly specifying each pair of accounts.
- Do not use UPNs in mapping rules: You cannot use a user principal name (UPN) in a user-mapping rule. A UPN is an Active Directory domain and username that are combined into an Internet-style name with an @ symbol, such as an email address: jane@example. If you include a UPN in a rule, the mapping service ignores it and may return an error. Instead, specify names in the format DOMAIN\\user (as the backslash is a special character, using additional backslash as the escape character on OneFS).
- Group rules by type and order them: The system processes every mapping rule by default, which can present problems when you apply a deny-all rule—for example, to deny access to all unknown users. In addition, replacement rules might interact with rules that contain wildcard characters. To minimize complexity, group rules by type and organize them in the following order: replacement rules, join/add/insert rules, allow/deny rules.
