Home > Storage > PowerScale (Isilon) > Product Documentation > Management and Migration > PowerScale OneFS Authentication, Identity Management, and Authorization > Importance of user mappings
Importance of user mappings
-
If user mappings are not available or are not configured correctly, asymmetrical tokens are created. An asymmetrical token is where a user has access to a file from a certain protocol but is denied access from the other protocol. The inconsistent access is because the user’s access token is different when accessing the file from each protocol, as shown in the following example:
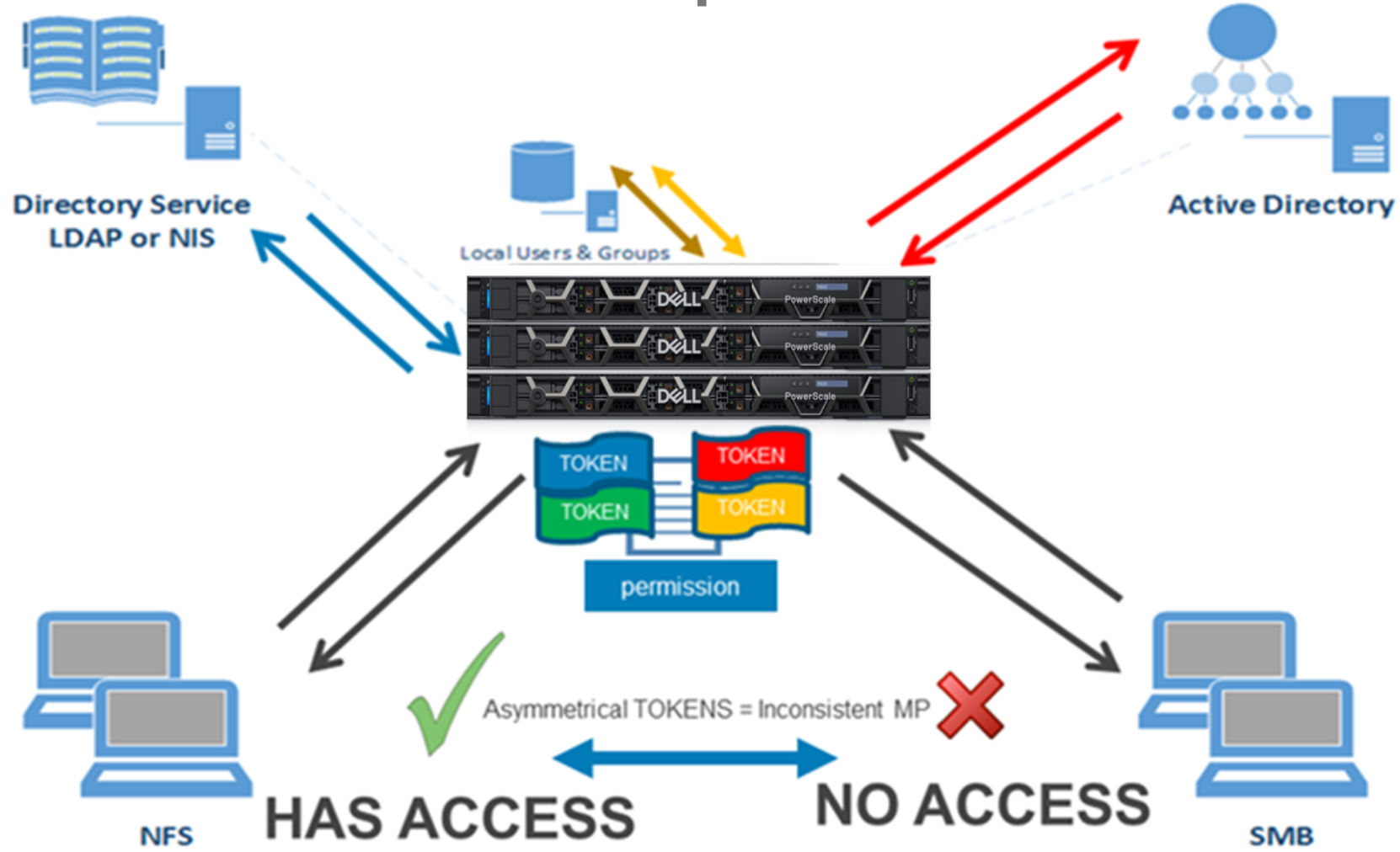
Figure 14. Asymmetrical tokens
Asymmetrical tokens lead to asymmetrical access. In the preceding example, for illustration purposes, the file permission is the “blue permission identity” and requires the blue ID portion of the access token. The blue portion is notating the UID with GIDs. When the same user tries to access the file from NFS and SMB, the following events occur:
- NFS: The user logs in to access the file with the blue permission. At login, OneFS reaches out to LDAP. The user is found, and the blue half of the token is generated with a real UID and associated GIDs. Because mapping is not configured, a lookup in Active Directory fails, and a fake green portion is assigned for the SID. However, if the file permission is based on the UID and the user has a real UID in the token, the user is granted access.
- SMB: The user logs in to access the file with the blue permission. At login, OneFS reaches out to Active Directory. The user is found, and the red half, or SID, of the token, is generated with a real SID. Because mapping is not configured, a lookup in LDAP fails, and a fake yellow portion is assigned for the UID and corresponding GIDs. Because the file permission is based on the UID and the user has a fake UID in the token, access is denied.
On the contrary, configured user mapping leads to symmetrical tokens, irrespective of the access protocol. A symmetrical token grants equal access to the same user, which is the basis of the Unified Permission Model. OneFS user mapping provides a consistent multi-protocol experience when accessing the same file from NFS or SMB, as illustrated in the following figure:
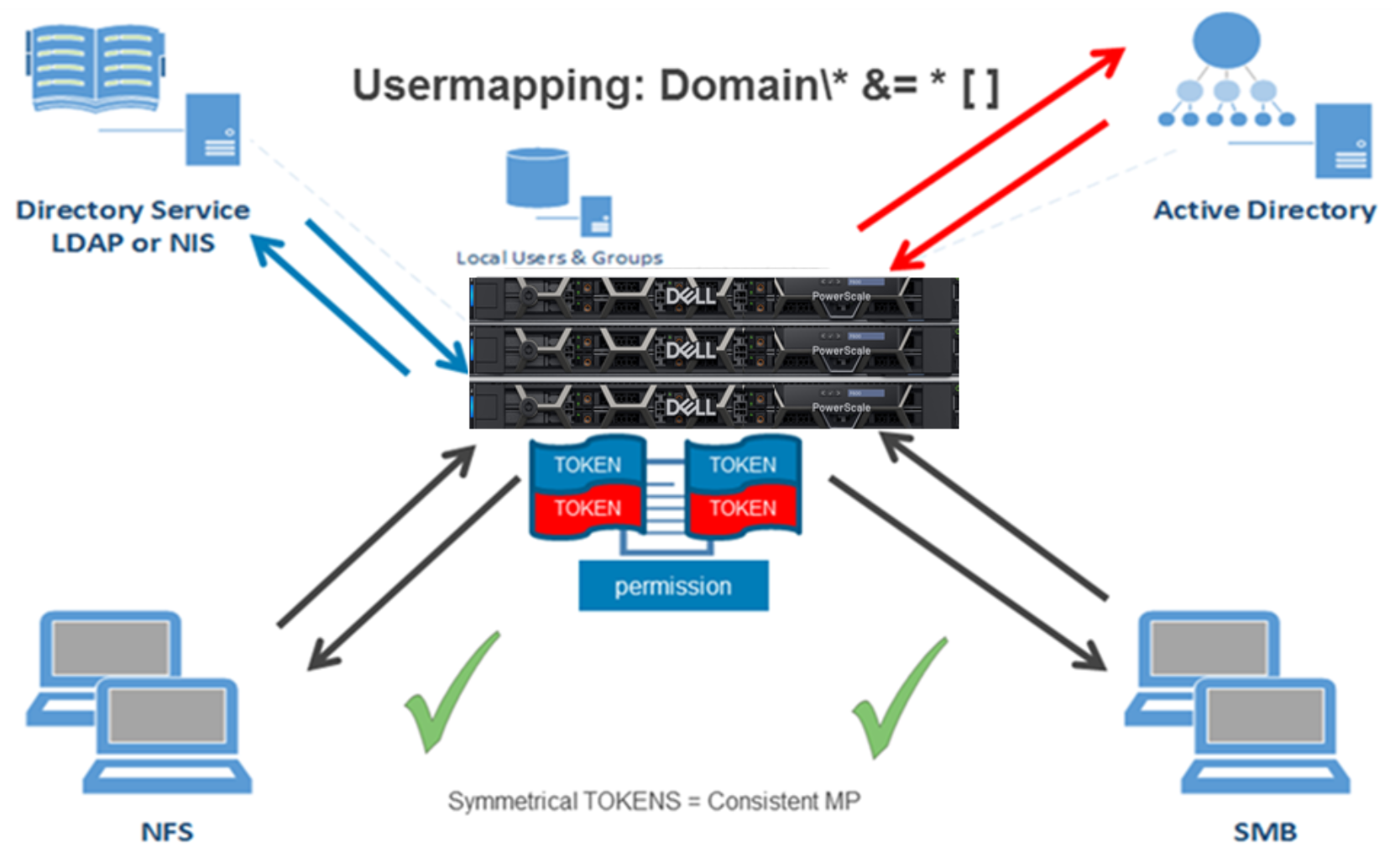
Figure 15. Symmetrical tokens
Symmetrical tokens lead to symmetrical access. In the preceding example, the file permission is again the “blue permission” and requires the “blue ID” portion of the access token. The blue is notating the UID with GIDs. When the same user tries to access the file from NFS and SMB, the following events occur:
- NFS: The user logs in to access the file with the blue permission. At login, OneFS reaches out to LDAP. The user is found, and the blue half of the token is generated with a real UID and associated GIDs. Because mapping is configured, a lookup in Active Directory occurs, and a real red portion is assigned for the SID. The file permission is based on the UID, and the user has a real UID and SID in the token. Thus, permission is granted.
- SMB: The user logs in to access the file with the blue permission. At login, OneFS reaches out to Active Directory. The user is found, and the red half, or SID, of the token is generated with a real SID. Because mapping is configured, a lookup in LDAP occurs, and a real blue portion is assigned for the UID and corresponding GIDs. Because the file permission is based on the UID and the user has a real UID in the token, access is granted.
