Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > PowerScale Cyber Protection Suite Reference Architecture > Ransomware Defender
Ransomware Defender
-
At the core of the PowerScale cybersecurity framework is Ransomware Defender. The solution combines scalability with real-time event processing to detect and stop ransomware attacks. Detecting changes to users' normal file system access patterns, Ransomware Defender can take defensive measures to prevent major damage and minimize recovery times when administrator-defined thresholds are met. If Ransomware Defender detects ransomware attack behavior, it initiates multiple defensive measures, including locking users from file shares, either immediately or over a period of time. Besides timed Auto Lockout rules, there is an automatic response escalation in case multiple infections are detected simultaneously, even if an administrator is not available. Further, the event triggers an automated snapshot creation upon initial detection for a ground-zero restore point.
User behavior detection is based on known consistent ransomware access patterns early in the attack lifecycle, as displayed in the following image. Historically, ransomware follows a specific pattern, as described in the section Ransomware lifecycle. Ransomware Defender monitors clusters for these specific events that are abnormal to typical user patterns. These include excessive encryption or movement of files that are not consistent with user behavior.

Figure 7. Ransomware Defender Event Triggers
Ransomware Defender is accessed through Eyeglass, as shown in the following figure. Alerts, configuration, and status are all managed through Eyeglass. Administrators may already be familiar with Eyeglass for its extensive data replication and failover capabilities.
Figure 8. Ransomware Defender
Ransomware Defender monitors PowerScale clusters constantly, for specific activity that indicates a ransomware attack, using a fully automated learning mode to monitor behavior and avoid false positives. Further refining the detection, protection can be customized for more sensitive data. When a ransomware event is detected, access from the infected user’s account to PowerScale is blocked. Ransomware Defender can manage multiple clusters, each with multiple shares. If ransomware activity is detected on one share in a cluster, the user loses access to all managed shares and clusters. As soon as ransomware activity has been detected and a user has been temporarily blocked, a notification is sent immediately to the administrator. Ransomware Defender only locks out the infected user, allowing other users to access the cluster. Because the security lockout is applied across the security stack, the locked-out user's other devices are also inaccessible.
When an active event occurs, Ransomware Defender displays the event state, severity, infected share, and other critical event information. In the following figure, a user is locked out and the associated snapshots are displayed.
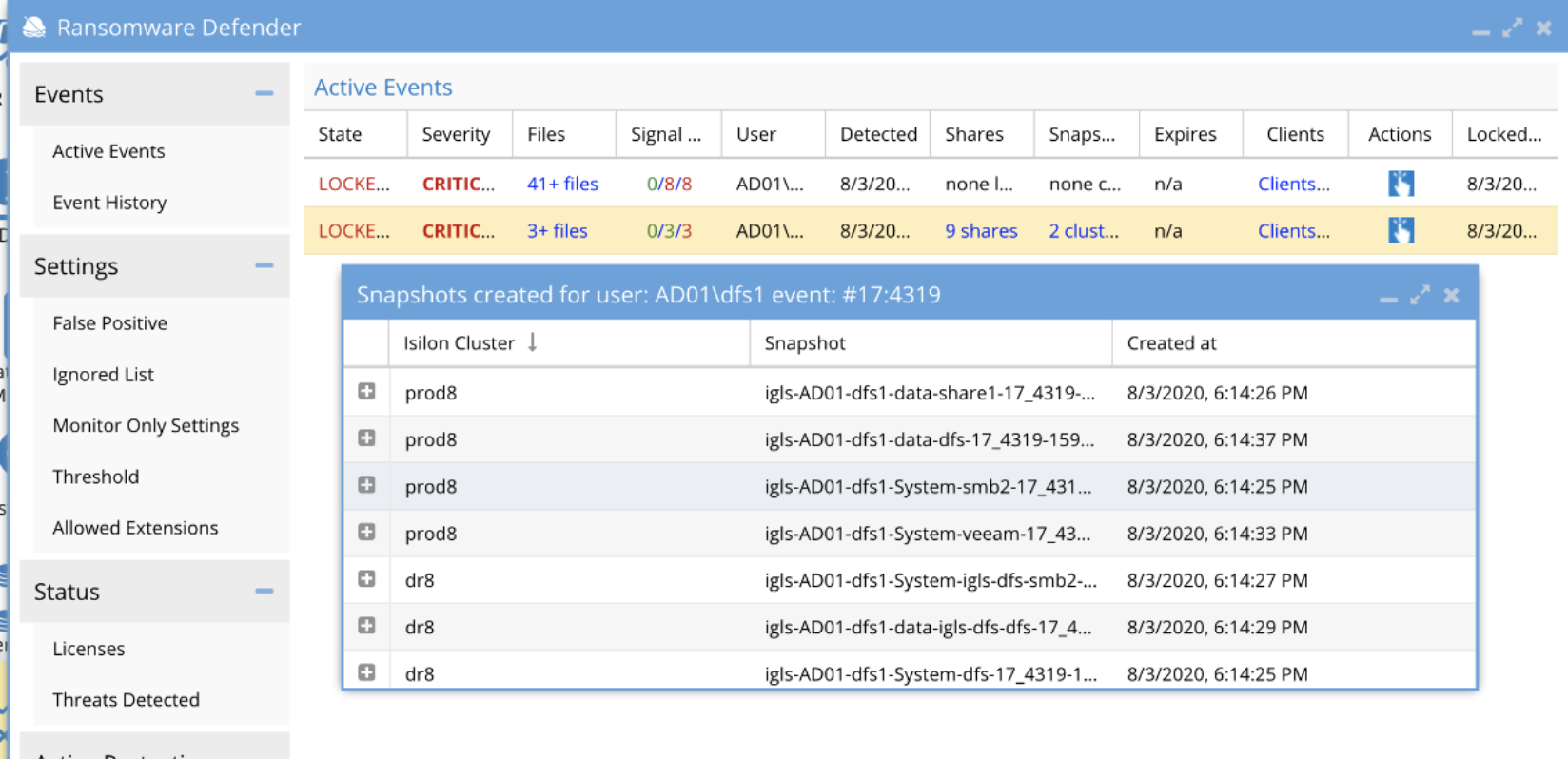
Figure 9. Ransomware Defender locked out user event
If an active event is detected, Ransomware Defender’s user behavior detection retains all associated security data, as shown in the following table.
Table 3. Active event security data
Active Event Data
Explanation
Actions
The history of all steps taken during the detection is listed with time stamps. All share lockout or snapshot creation tracking is logged. All future actions stay with the event history. If an event is archived, the history stays with the event in the “Event History” tab.
Client IP
The IP address of the user’s PC that is infected.
File Event
A discrete event published by PowerScale’s event stream based on a user action, for example: open file, close file, write or read to file.
Files
The list of files associated to the detection for the specified user.
Lock Out
The date and time of the security event
Ransomware Event
A collection of signals whose combined Signal Strengths exceeds the user-set threshold in Eyeglass.
Shares
List of shares that were locked out
Signal
Occurrence of one or more File Events that have been flagged by one or more threat detectors as a potential Ransomware Event.
Signal Strength
For a given Signal, the number of threat detectors that were triggered. A higher Signal Strength has a higher probability of being a Ransomware Event.
Snapshots
List of snapshots of SMB share paths taken during the lockout
Threat Detectors
Logic used by Eyeglass Ransomware Defender to determine if a group of File Events is potentially associated with a Ransomware attack. There are multiple independent threat detectors used by Eyeglass Ransomware Defender during analysis that are assessed in parallel.
User
The user or NFS IP of the locked-out account
Ransomware events are based on signal strength thresholds. The threat level and associated action are listed in the following table.
Table 4. Ransomware Defender signal strength threshold
Threat Level
Ransomware Defender Action
Warning
Eyeglass sends an email to notify any subscribed administrator(s) of the threat but takes no direct action.
Major
Eyeglass begins a “delayed lockout” procedure. Notify the administrator(s) that a threat has been detected, and the user will be locked out after X minutes, unless the admin logs in and explicitly cancels the action. The grace period is configurable in Eyeglass settings.
Critical
The user lockout is immediate, and the administrator(s) are notified.
Administrators configure the threshold for detected ransomware events with an associated signal strength, interval, grace period, and an option to escalate the alerts based on the occurrence of events.
The threat detection Signal Strength measures the severity of a user's File Event behavior. A higher count indicates a more severe detection. A Signal Strength column can be found in the Active Events or Event History tab of the Eyeglass Ransomware Defender window, as highlighted in the following figure.

Figure 10. Active Events Signal Strength
Further, the signal strengths are based on specific threat detectors that contributed to the event, as displayed in the following figure.
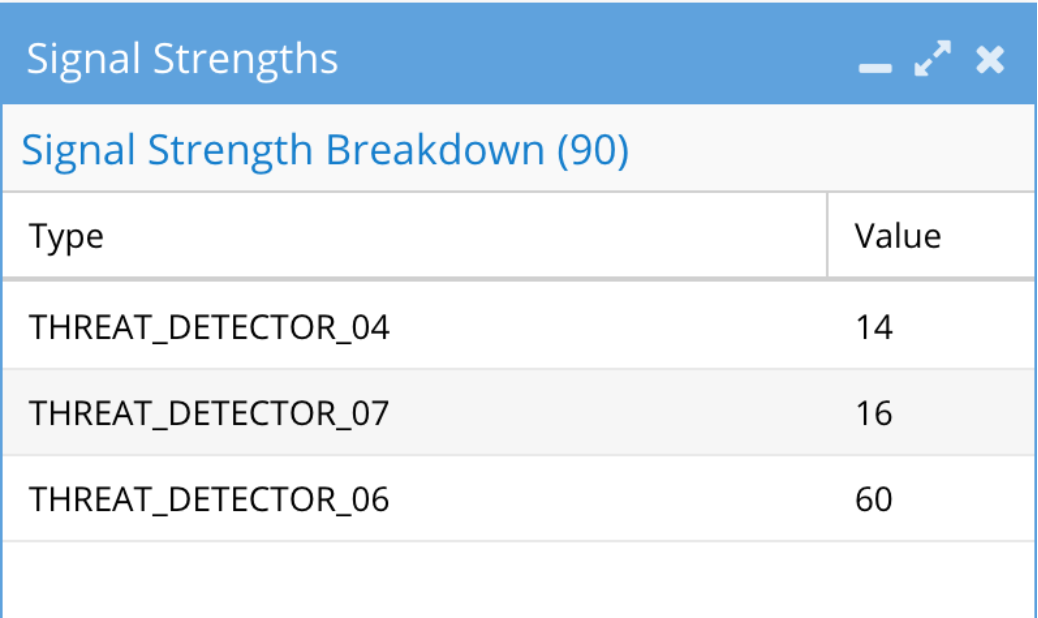
Figure 11. Signal strength threat detectors
Note: The threat detectors are not documented for enhanced security and are for support only.
The Threshold menu also includes an option to Automatically learn from events in monitor state allowing administrators to use events for learning the normal access patterns. When a threshold is reached, administrators can take a snapshot and/or mark the event as Critical on Mode. The Critical on Mode option disables the automatic lockout feature for critical events and applies a major event delayed lockout. Furthermore, for each of the threshold levels, an event can be associated across multiple vectors, based on a combination of signal strength, interval, and duration, as shown in the following figure. The multiple vectors allow administrators to define varying combinations that could be indicative of an attack.
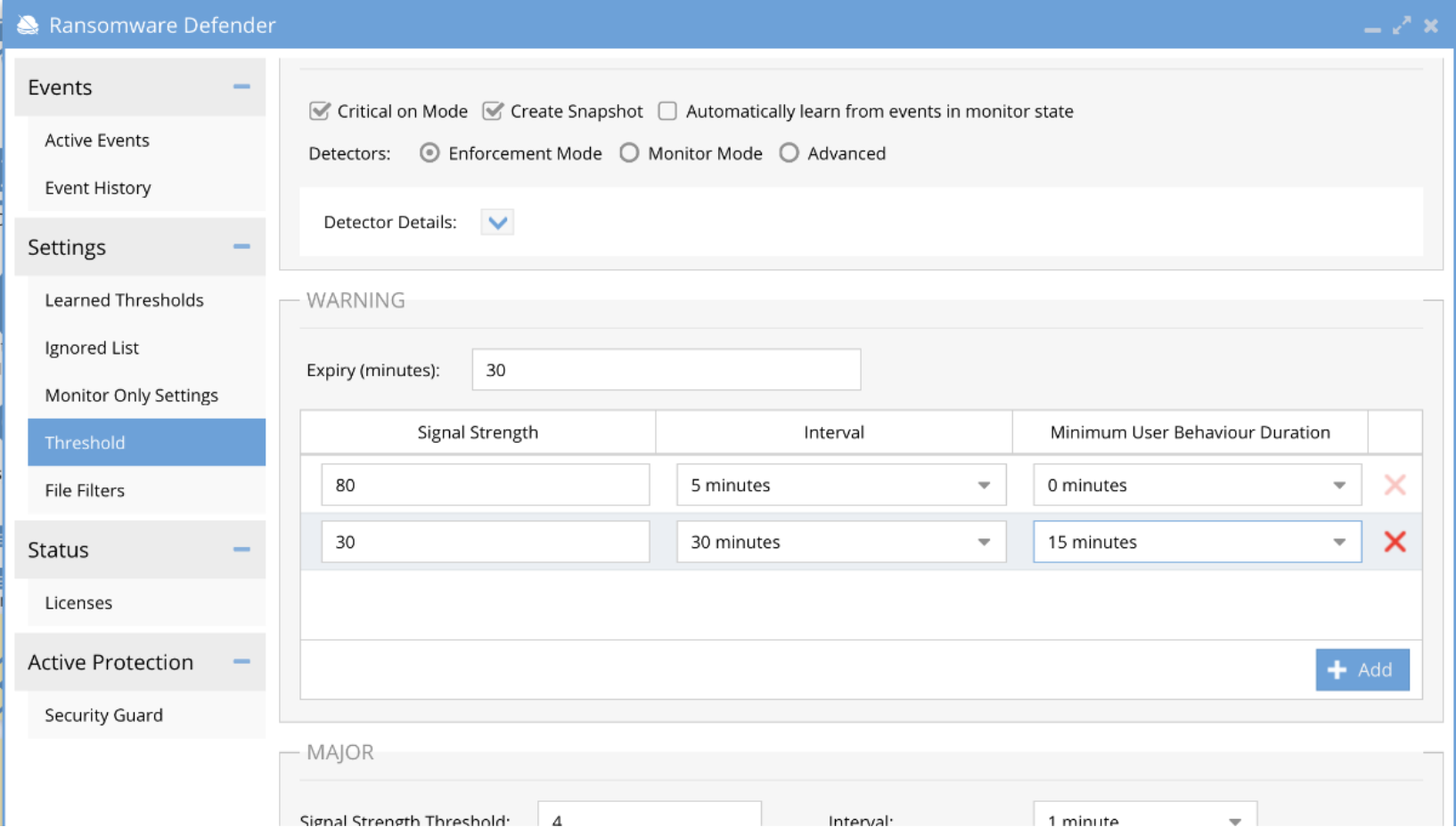
Figure 12. Ransomware Defender threshold options
Security guardA critical part of security best practices is ensuring threat detection systems are active and ready. Ransomware Defender includes a “Security Guard” feature, which simulates a ransomware attack to validate all components are functioning, including alerting and lockout of user sessions. The feature can simulate an attack on demand or on a scheduled interval that may be required by regulatory security requirements. During the simulation, administrators are notified through the defined event thresholds, and a detailed log is available after the attack. The simulated attack includes options define the Active Directory user and specify a single or multiple clusters, as displayed in the following figure. Further customizing the attack, an option is also available for a custom file extension.
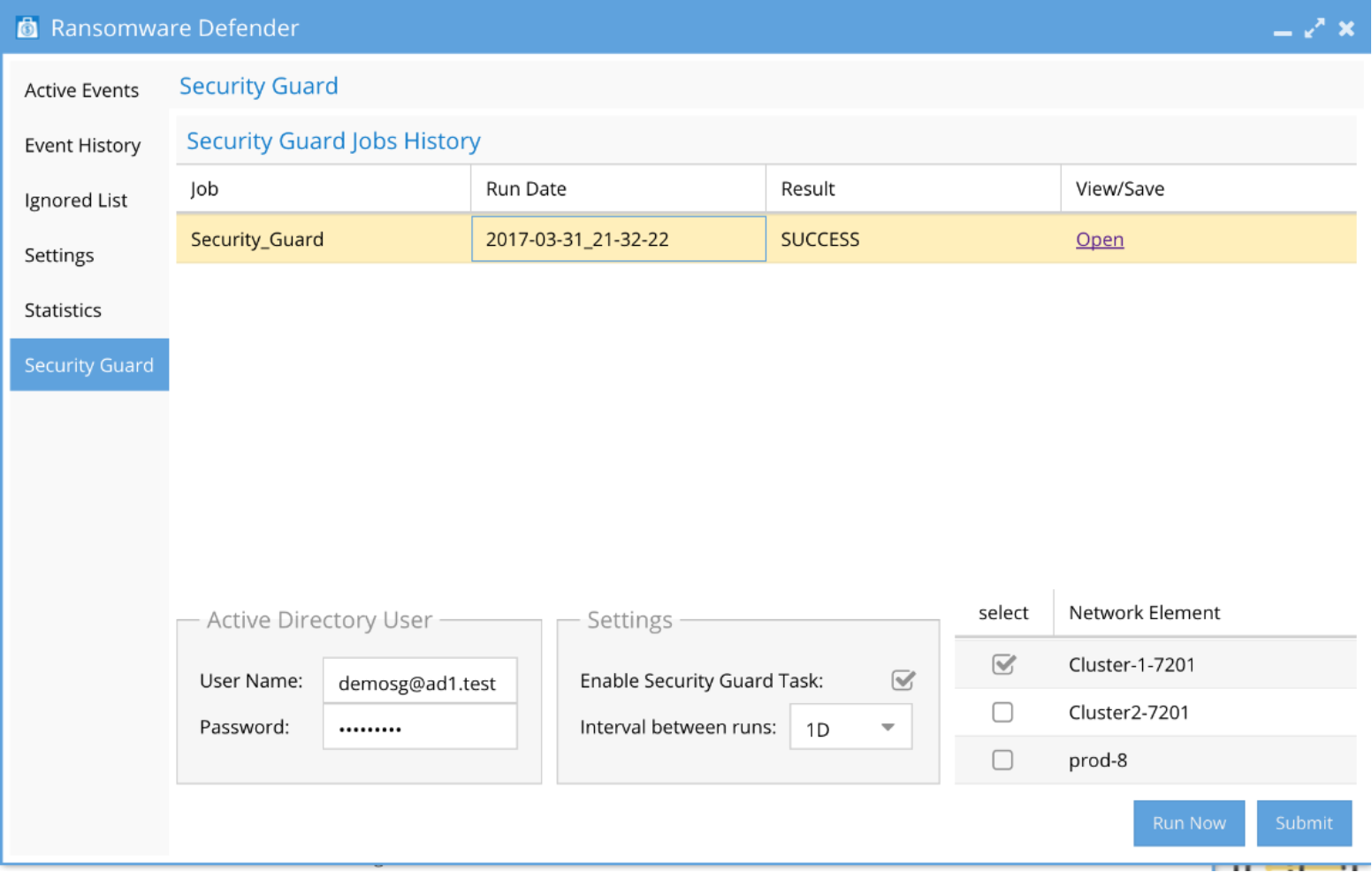
Figure 13. Security Guard
Honeypot tripwireHoneypots are an important part of vulnerability management. It is essentially a “fake” share or file that mimics the original. The goal is that the hacker attacks the fake honeypot instead of the actual data, allowing the system to lock the user out early in the attack. Typically, a honeypot is used where sensitive data exists and allows for faster detection times at these locations in the file system. Ransomware Defender allows honeypots in as many locations as needed.
Cyber Recovery Manager
Ransomware Defender contains a Cyber Recovery Manager that automates data recovery using a OneFS snapshot after a ransomware attack. Based on information from audit events, Ransomware Defender is aware of the time an attack took place. Using this timestamp, the Cyber Recovery Manager, can then list the available snapshots to restore before the attack took place.
In the Ransomware Defender module, the event history information contains an “Action” option where the Cyber Recovery Manager option is available, as displayed in the following image.
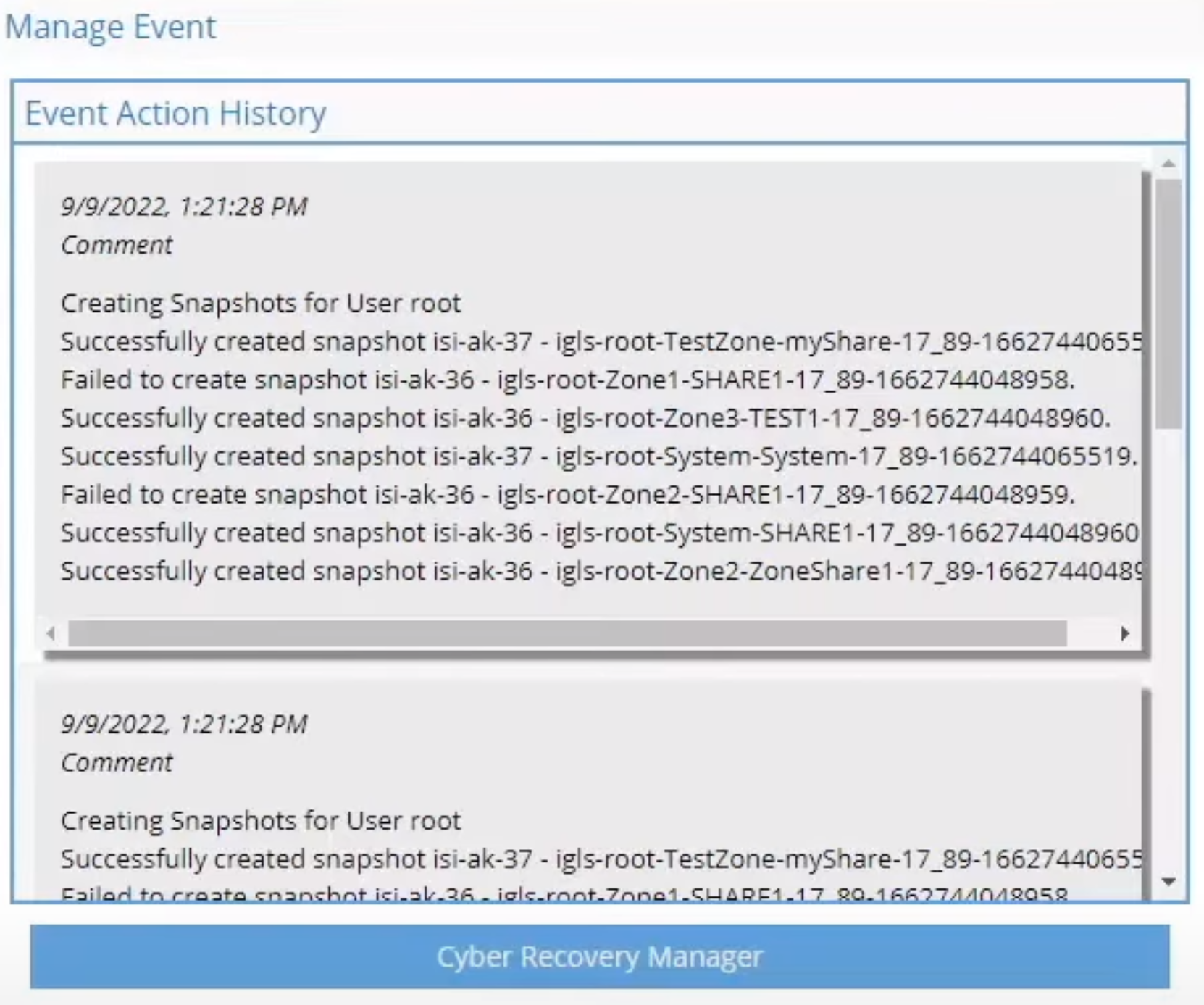
Figure 14. Cyber Recovery Manager
Clicking the Cyber Recovery Manager option lists the files that have been compromised from a ransomware attack. The following figure shows the last known snapshots associated with the compromised files. Simply select the snapshot and click Recover.
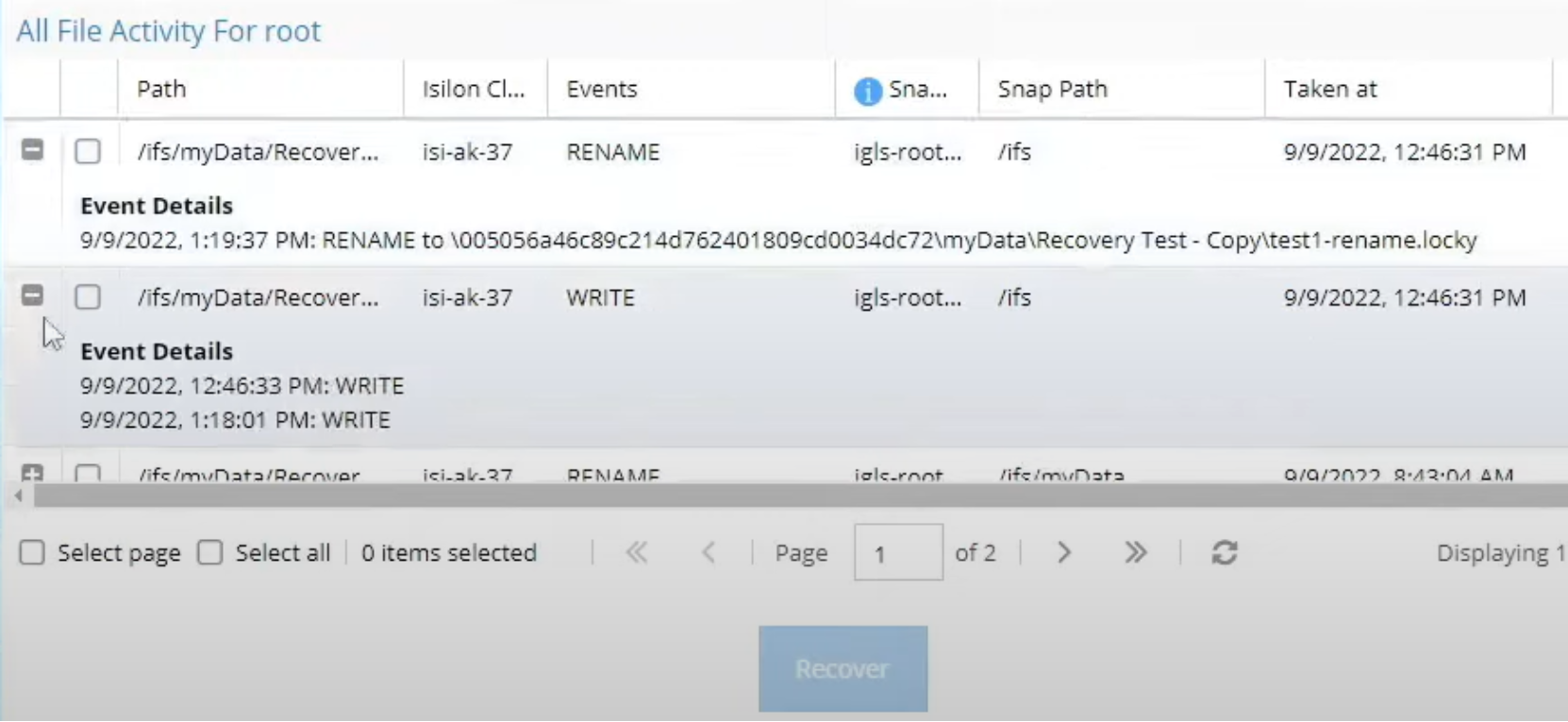
Figure 15. Cyber Recovery Manager file recovery
Because cyber incidents require a post-mortem analysis, the Cyber Recovery Manager assists in the analysis. An automated quarantine feature moves impacted files to a hidden location for inspection in the future. The quarantine also removes file visibility from users.
Zero Trust API
The Zero Trust API is an add-on component to Ransomware Defender and enables integration with third party SIEMs and XDRs. A Security Information and Event Management System, or SIEM, facilitates the identifying and addressing of potential vulnerabilities and threats before they disrupt a company's operations. Using SIEM technology, event log data is collected from different sources, analyzed in real-time, and action is taken by Ransomware Defender if abnormal behavior is spotted. Depending on the security stack implementation a SIEM may be sharing data with an XDR. However, the security stack implementation varies according to the environment.
An Extended Detection and Response (XDR) solution gathers and correlates data across multiple layers of security, including email, endpoint, server, cloud workload, and network. An XDR also collects data from other security systems, such as Endpoint Detection and Response (EDR), Network Detection and Response (NDR), SIEM, and other threat related data. Alternatively, some security implementations might have the EDR and NDR sharing data with the SIEM.
The Zero Trust API allows integration with XDRs and SIEMs, integrating with an organization’s security stack and further protecting PowerScale clusters. As a result, you can detect threats sooner, conduct investigations more quickly, and improve response times through security analysis. The integration provides a cohesive security approach across the corporate network by linking storage, network, endpoints, servers, and email domains using a bi-directional API, bridging the security intelligence gap at the storage domain.
Through the bi-directional API security event analysis spans across detection vectors through the data, application, and network layers, as displayed in the following figure. This allows the security system to identify suspicious activity quickly, because it can draw on data from multiple sources to identify potential threats. As a result, it can detect malicious activity earlier and take action to prevent it from escalating through the data center layers. For example, if a threat is detected from the security stack, this can be configured to trigger a user lockout across monitored PowerScale clusters and a SnapshotIQ snapshot.
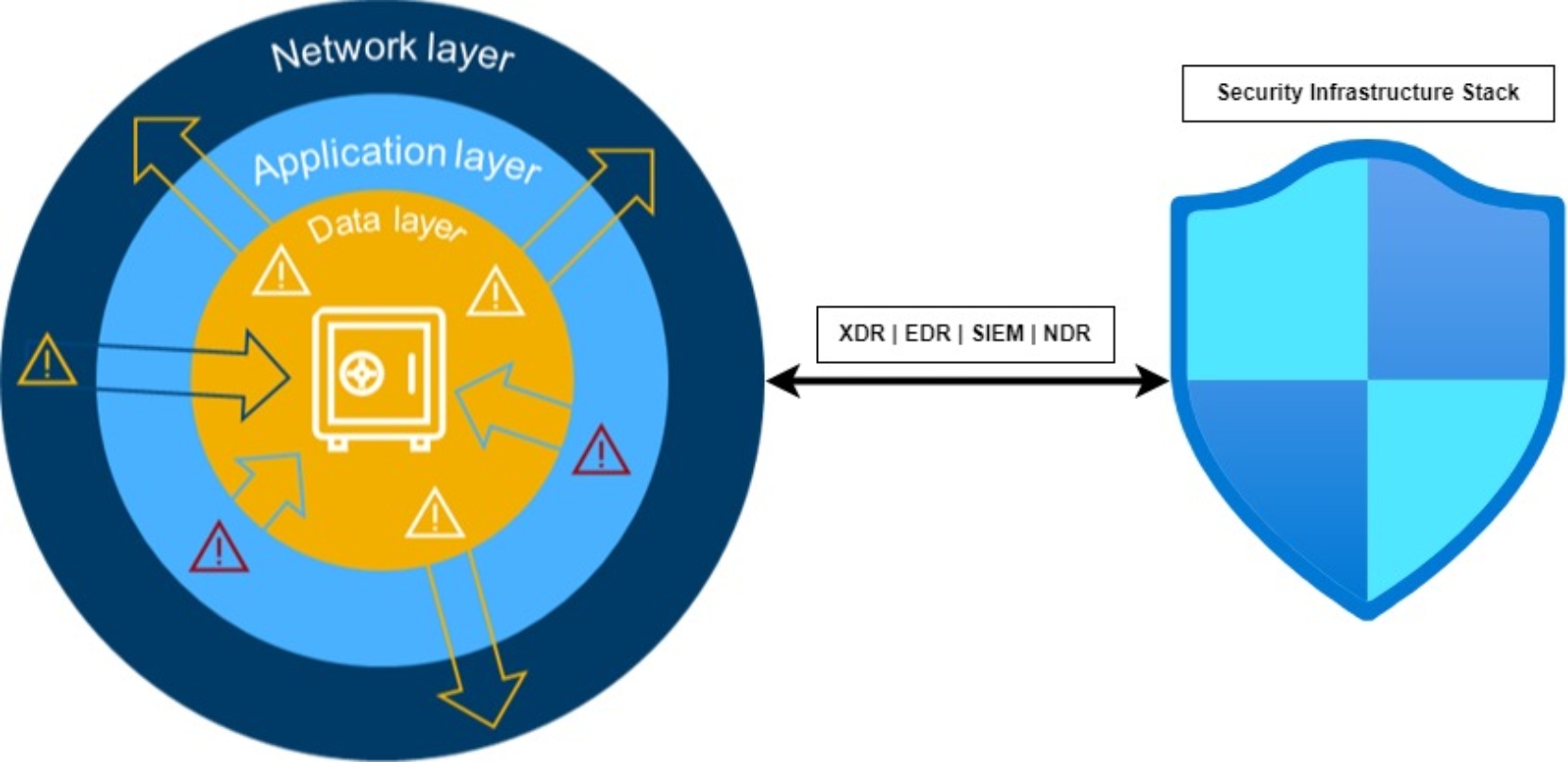
Figure 16. Zero Trust API
The Security Infrastructure Stack now correlates data across domains and through the layers, allowing Ransomware Defender to monitor current threat levels. Application Server threats trigger an API call for OneFS to create immutable SnapshotIQ snapshots of critical data. Compromised user threats trigger an access denial to PowerScale storage with AD & SMB share aware lockouts. Further, SyncIQ replication to the PowerScale Vault Cluster is blocked until the active threat is cleared.
Progress Flowmon ADS
A typical Enterprise Security Infrastructure Stack collects and analyzes threat data across all devices, endpoints, and network infrastructure. Network Detection and Response (NDR) is a critical part of the stack to detect suspicious network activity and unknown threats early in the attack lifecycle. NDRs monitor and analyze network traffic, alerting of suspicious network traffic patterns that deviate from a baseline or expected characteristics.
Other components of network security monitoring are an Intrusion Detection System (IDS) and Threat Intelligence feeds (TI). IDS is a passive monitoring system, that detects known threats using a database of signatures. Altogether, NDR and IDS secure network infrastructure and the alerts allow security administrators to respond to an attack before it reaches a PowerScale cluster.
The Progress Flowmon Anomaly Detection System (ADS) detects anomalies in network traffic to expose malicious behavior and indicators of compromise through NDR, IDS, TI, and other detection methods. Flowmon ADS shares the network status with Ransomware Defender through the bi-directional Zero Trust API. If a network anomaly occurs, Flowmon ADS notifies Ransomware Defender, triggering a OneFS snapshot and stopping replication to the Cyber Recovery Vault, as illustrated in the figure below.

Figure 17. Flowmon ADS event flow with Ransomware Defender
Threats are detected through Flowmon’s end-to-end network security, including Network Performance Monitoring and Diagnostics (NPMD) and Application Performance Monitoring (APM). Further, Flowmon assists with meeting the regulation requirements for the NIS2 cybersecurity directive. For more information on the Progress Flowmon integration with the Zero Trust API, see the Progress Flowmon and Zero Trust API Datasheet.
AirGap Enterprise
The AirGap Enterprise module add-on to Ransomware Defender retains an offline copy of a dataset in an automated cyber vault. The offline dataset copy is logically segmented from the production network, providing two critical advantages. First, the dataset is stored in a secure offline vault, protecting it from enterprise network threats. A second advantage is planning for a ransomware attack that cripples business operations. By using an offline dataset, you can quickly restore operations to the point in time when the last copy of the dataset was made, thus minimizing the impact and damage associated with the ransomware attack as a whole. Further, if a dataset is readily available to restore, payment of the ransom is not a consideration, potentially saving millions of dollars. The AirGap cyber vault also complies with the NIST cybersecurity framework best practices.
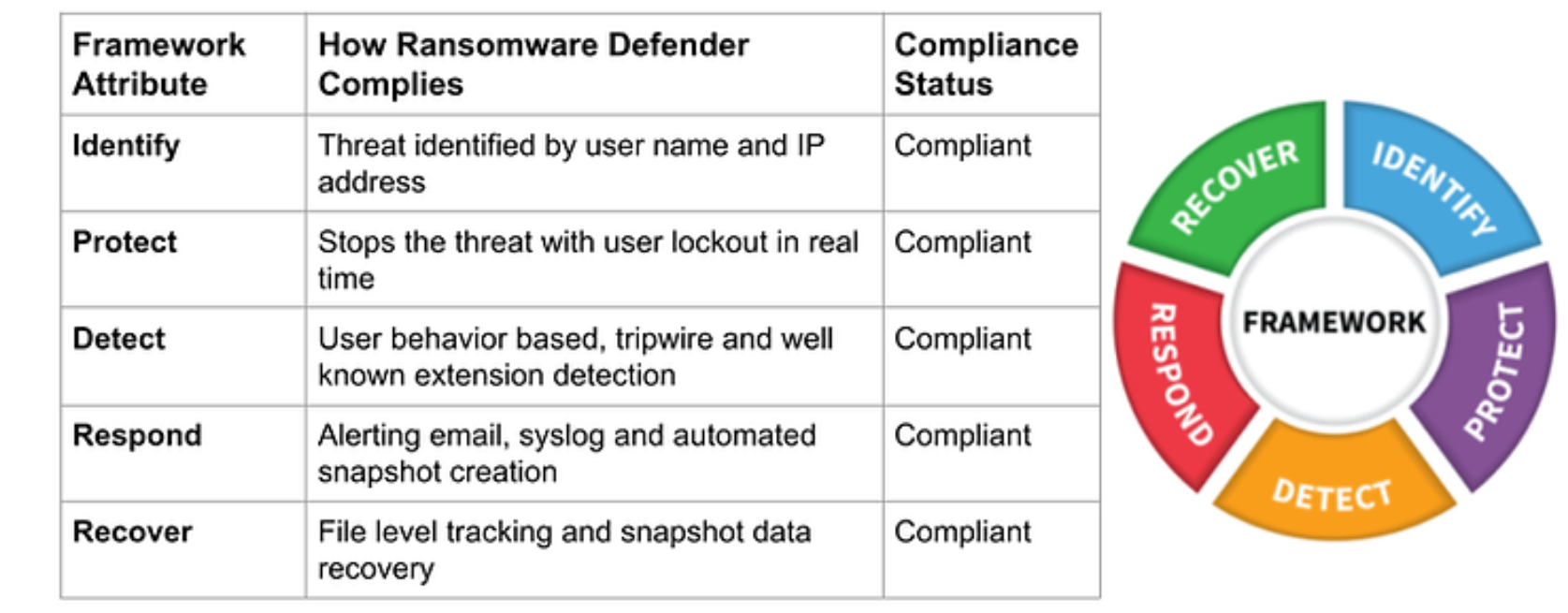
Figure 18. Ransomware Defender compliance with NIST cybersecurity framework
As part of the inside-the-vault hardened solution, full automation and in-band management allow access through a virtual machine within the cyber vault. The Smart Airgap technology ensures that data is only replicated when it is safe to do so. Further, the airgap mode provides a low-cost, fully automated solution. Optionally, a physical fiber cutter and firewall are available for the cyber vault.
Similar to the other modules in the PowerScale Cyber Protection Suite, you can access and manage the AirGap Agent through Eyeglass, as shown in the following figure.
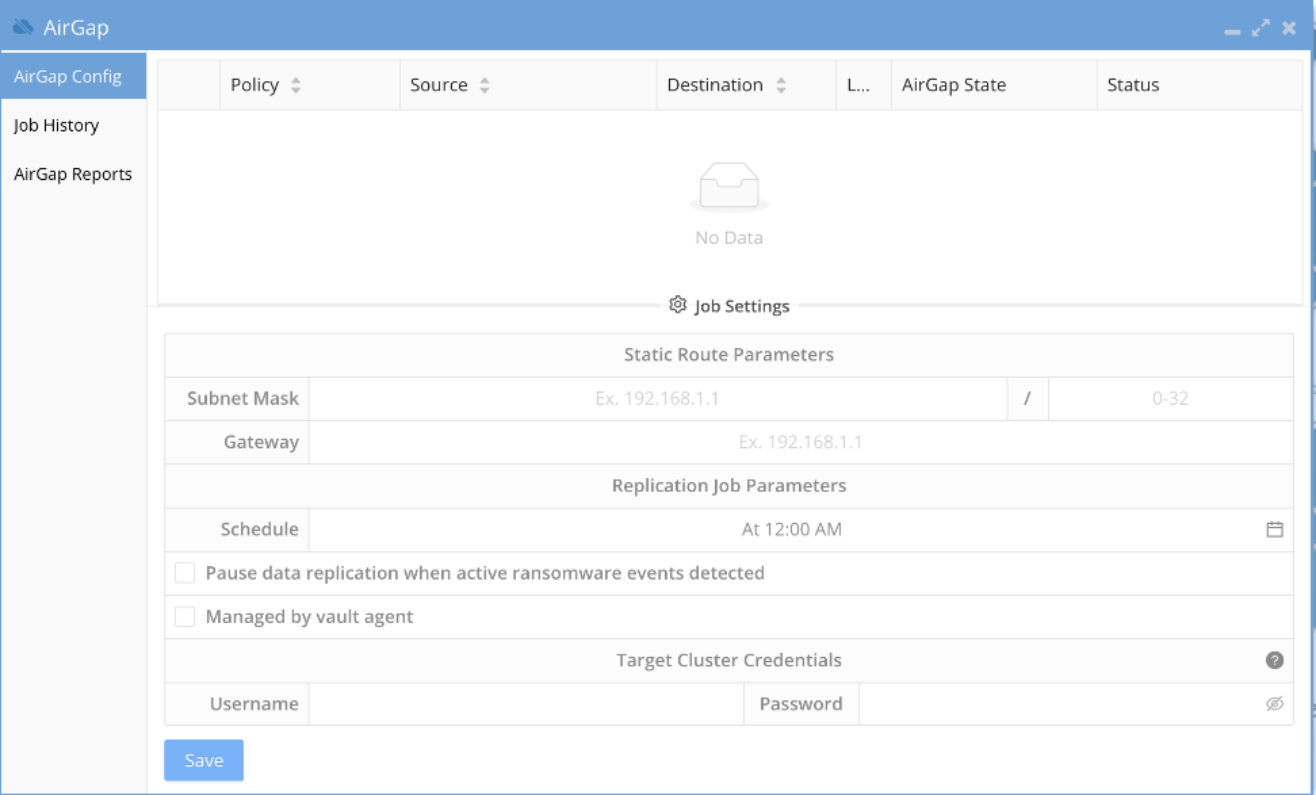
Figure 19. AirGap configuration
By only allowing data replication after a security clearance has been granted, the Cyber Recovery Vault is completely protected from unauthorized access. Note that under normal operating conditions, the PowerScale Vault Cluster does not have network access outside of the Cyber Recovery Vault and stores the business continuity dataset. The Enterprise AirGap Agent performs data and security checks periodically, at a frequency defined by an administrator. If a security clearance is granted, the Enterprise AirGap Agent replicates only the changed data blocks to the PowerScale vault cluster’s business continuity dataset.
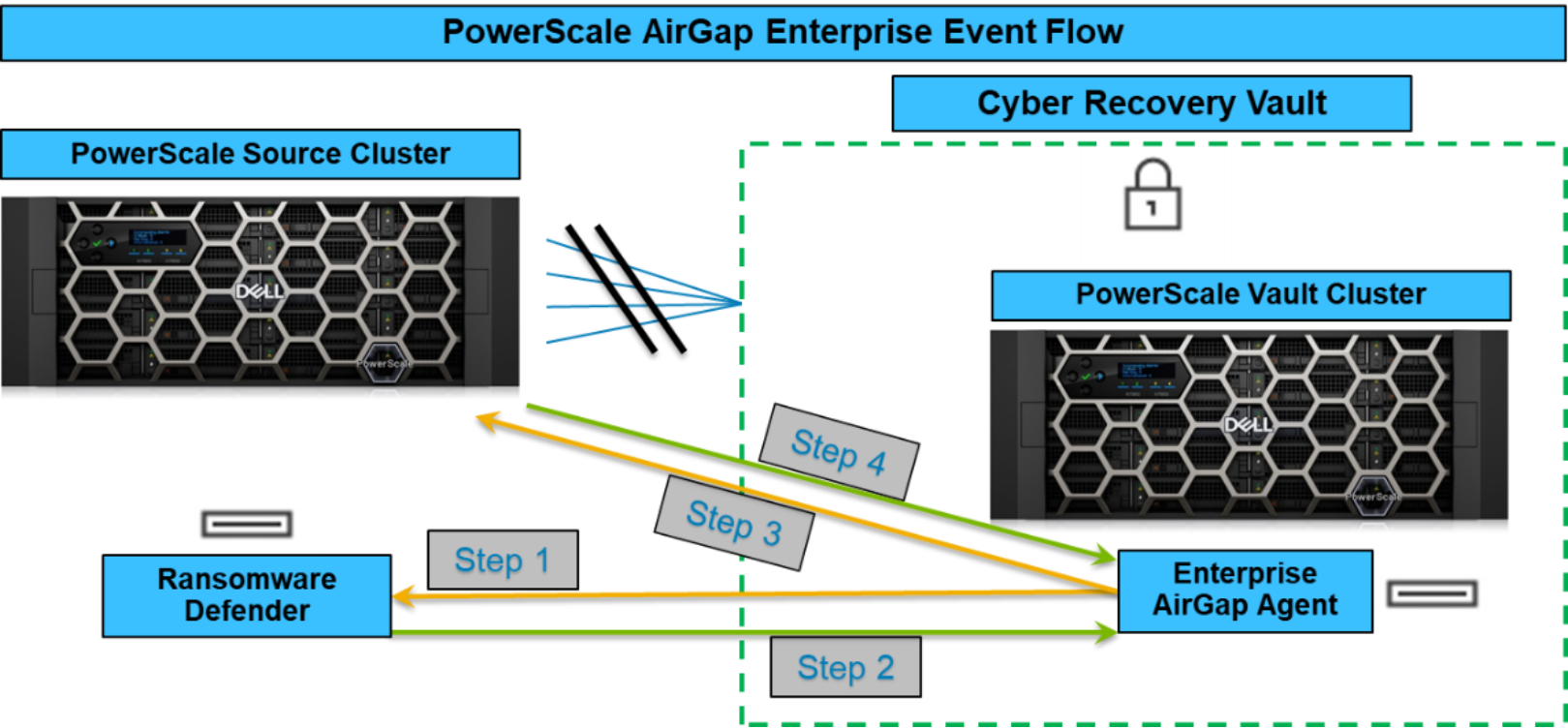
Figure 20. PowerScale AirGap Enterprise Event Flow
The AirGap Enterprise module runs through the following logical flow of steps, corresponding to the steps in Figure 20, to perform a security check and replicate changed data blocks:
- At an administrator-specified frequency, the Enterprise AirGap agent adds network interfaces to query the Ransomware Defender agent outside the vault, for any active ransomware events. If active ransomware events are found, the process stops here, and the Enterprise AirGap agent removes the network interfaces, securing the Cyber Recovery Vault.
- If no active ransomware events are detected, Ransomware Defender grants a security clearance to the Enterprise AirGap agent to proceed.
- The Enterprise AirGap agent then queries the PowerScale source cluster to start replication to the PowerScale vault cluster. The PowerScale source cluster checks for updates to the business continuity dataset. If the PowerScale source cluster reports no changes to the business continuity dataset, the process stops here and the Enterprise AirGap Agent removes the network interfaces, securing the Cyber Recovery Vault.
- If the PowerScale source cluster reports updates to the business continuity dataset, data replication may commence, only copying the changed data blocks. The Enterprise AirGap agent monitors the replication process.
- Finally, when the replication is complete, the Enterprise AirGap Agent removes the network interfaces, securing the Cyber Recovery Vault. In the future, the process starts again at Step 1, based on the configured frequency.
