Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > PowerScale Cyber Protection Suite Reference Architecture > Easy Auditor
Easy Auditor
-
Easy Auditor protects and secures PowerScale clusters by simplifying auditing operations for compliance, security, and other daily checks. Through real-time auditing capabilities, proactive data protection can be achieved by automating responses to security events using SnapshotIQ snapshots and enabling real-time locking out of user data access. With support for billions of audit records, Easy Auditor scales to clusters of any size. The PowerScale Cyber Protection Suite uses Easy Auditor for security features that complement the other modules in the suite, enhancing the overall suite’s security posture. Audit and security data is shared with Ransomware Defender for analysis and actionable threats.
Similar to Ransomware Defender, Easy Auditor is also accessed through Eyeglass. Alerts, configuration, and status are all managed through Eyeglass.
Easy Auditor provides default reports and customizable reports to meet all auditing and security requirements. The default reports can be refined to meet regulatory or security requirements. The default reports include the following:
- Stale User Access Report: This report is used to determine which users might not require access to SMB shares based on access patterns. This is a security report that can be shared with departments that manage SMB share access. The report lists users that have accessed data using SMB shares and calculates the last read or write of each share the user has access to, based on AD group membership. The report also lists users that can mount shares and whether users have accessed data during the reporting time period.
- Access User Report: The report maps user to share access, detecting users with excessive permissions and confirming existing share access that may not align with security policies. The report generates a list of shares and a list of Active Directory (AD) users and groups that have access to a SMB share. The AD groups can be expanded to a list of users for administrators that do not have access to AD. Typically, this report is used to determine which users may not require access to SMB shares, based AD group membership. This is a security report that can be shared with departments that manage SMB share access.
- Login Monitor Report: This is a compliance report that satisfies HIPAA and PCI Requirements to track login to systems that store compliance data.
- Employee Exit Report: This report would be run prior to an employee leaving an organization and provides a view of all files the user accessed in any way over the last 30 days. The report is typically part of an HR process, displaying user activity by day over the last 30 days.
Reports are sent through email on a specified frequency and are available to view at any time in the “Finished Reports” tab, as shown in the following figure.
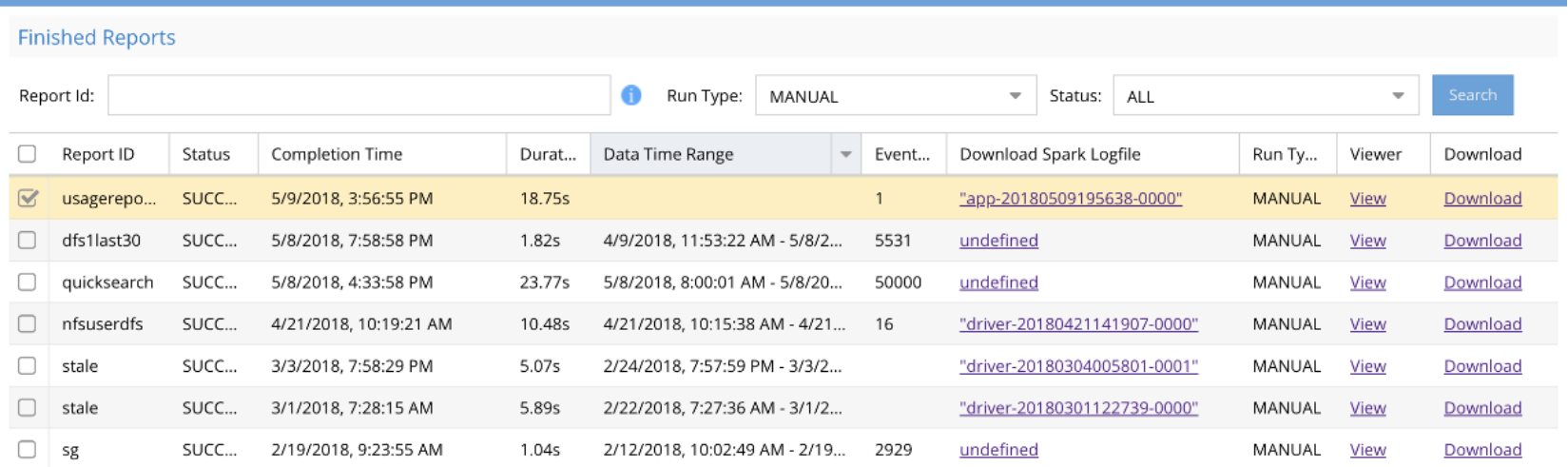
Figure 21. Finished Reports
The customizable reports are based on user, paths, files extension, file action, and a date range as shown in the following figure.

Figure 22. Report Query Builder
Active Auditor
Rather than simply reporting threats to administrators and creating additional workload for administrators to read through lengthy reports, Active Auditor automates security through real-time audit triggers. For example, if two associated event triggers occur, send an alert. The triggers are fully customizable policies based on user, path, file extension, source IP address and more, to detect any condition in real time. The Active Auditor configuration window is shown in the following figure.

Figure 23. Active Auditor configuration
The real-time auditing triggers include a fully customizable set of and/or rules, allowing administrators to configure extremely granular triggers, as shown in the following figure.

Figure 24. Granular real-time auditing triggers
When an active event occurs with Active Auditor, administrators are provided a detailed log of the event and are provided a set of actions to select, as shown in the following figure.

Honeypot
Active Auditor can be configured for honeypot detection, to detect an insider threat looking for open shares to read data. The trigger is configured to activate any time the honeypot directory is accessed.
Mass delete protection
Active Auditor’s mass delete protection feature monitors users who delete files on any share or export up to a threshold defined by an administrator over a specified period of time. Real-time detectors count deletions made by a user and raise alerts when policies are violated. A built-in protection option takes a snapshot of SMB shares if the user is suspected of destroying data. Furthermore, snapshots are created for all SMB shares to which the suspected user has access. In the event of accidental deletions, recovery is simplified through automatically applied snapshots. The following figure displays the Mass Delete Configuration window.

Figure 25. Mass Delete Configuration
Additionally, Mass Delete responses can be configured, as shown in the following figure.
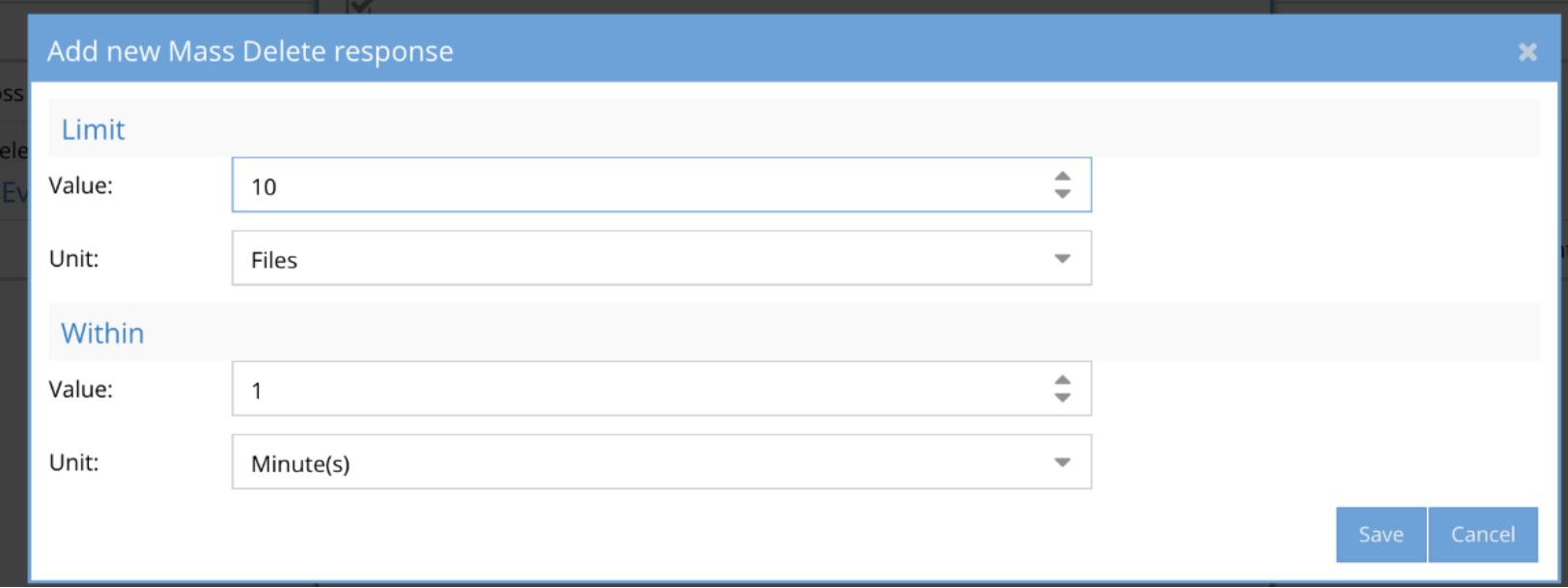
Figure 26. Mass Delete Response
Data loss prevention
Active Auditor’s data loss prevention feature monitors users who copy files on any secure share or path. The feature provides real-time monitoring of secured data from bulk copy operations that are not authorized or an indication of a potential data loss scenario. An auto applied accounting quota is used to monitor the capacity of the file system path. Administrators specify a percentage of the data any user can read from the path before the audit trigger is detected. The triggers create an alert that includes the date, time, and IP address of the event. The Data Loss Prevent Configuration window is shown in the following figure.
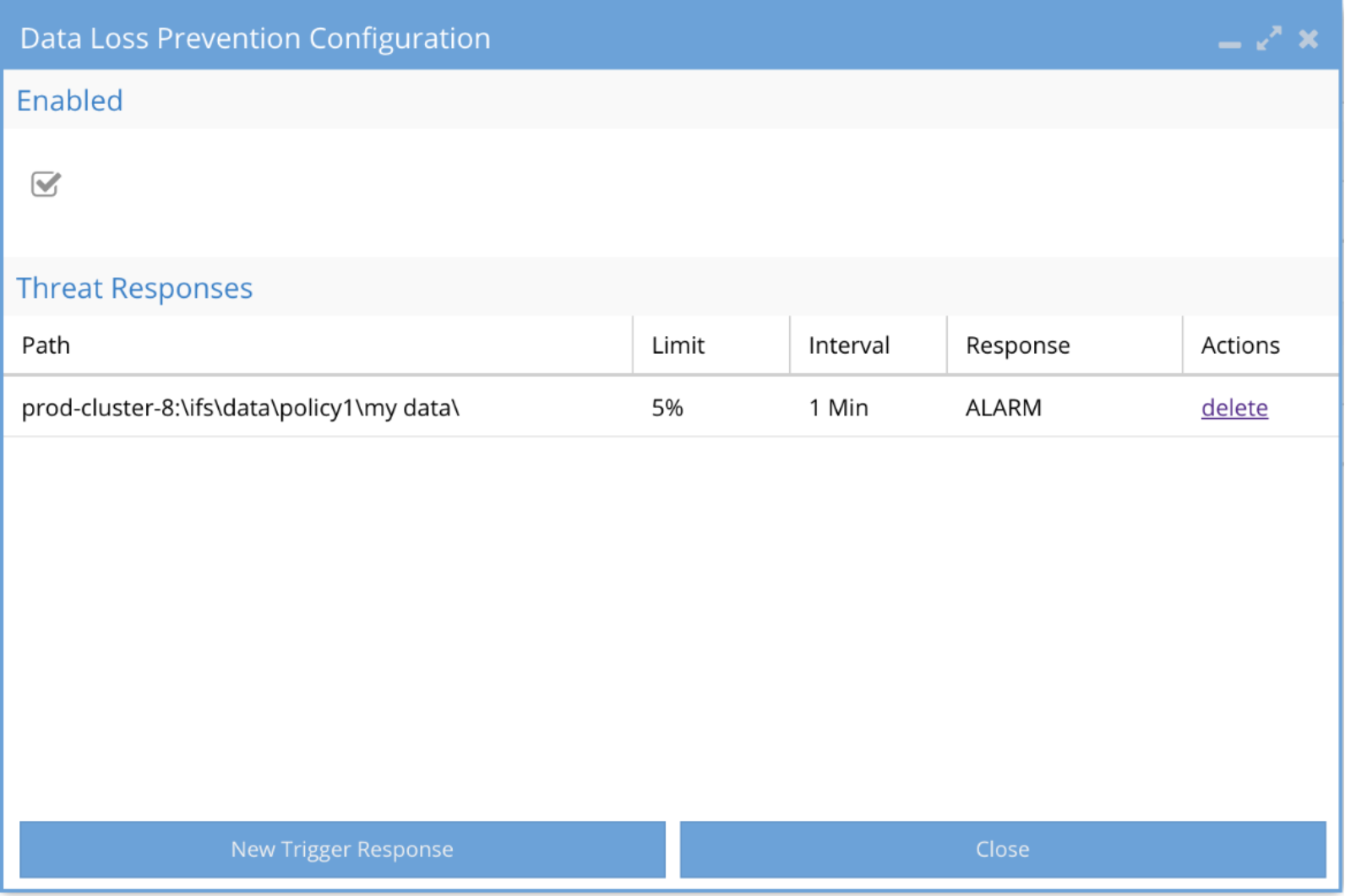
Figure 27. Data Loss Prevent Configuration window
WireTap
Administrators or security personnel can view a live feed of events in real-time using WireTap. The events are triggered by user actions. Rather than examining events independently, the captured events provide security staff with a comprehensive overview of the incident. Audit events are processed in real-time to stream the events directly to the WireTap UI.
Some real-time scenarios where a WireTap would be beneficial are:
- Specified path to monitor multiple users
- Monitor only a specific user
- Monitor a folder – with or without sub-folders
The WireTap UI displays the live events in real-time, as shown in the following figure.
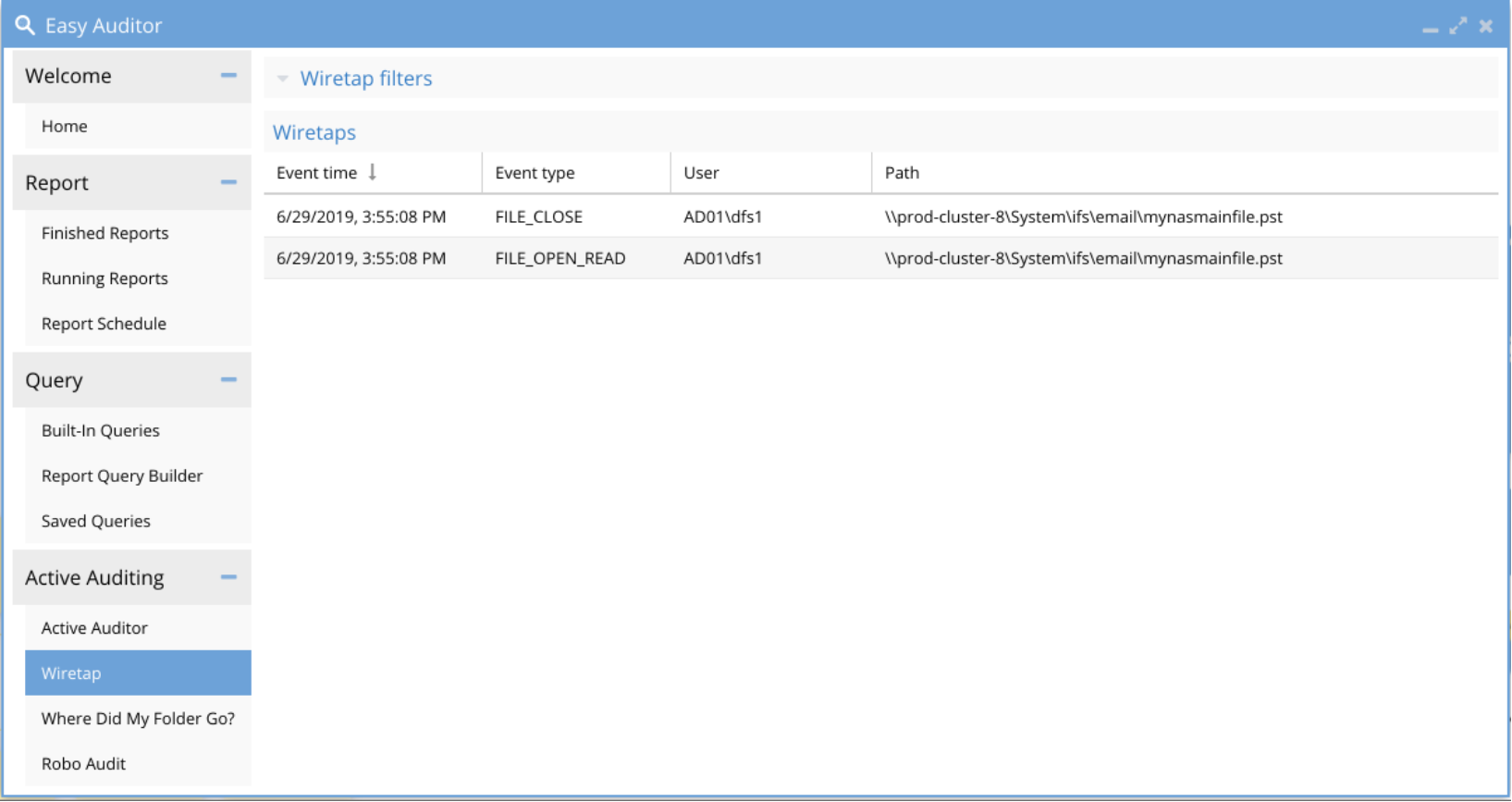
Figure 28. WireTap UI
Robo Audit
The Robo Audit feature allows administrators to test the cluster for audit events, to ensure that the audit and security features are functioning correctly. The feature creates an SMB connected user to create events, allowing verification of file and directory events. A complete report is generated logging the user functions to matching audit events. The Robo Audit jobs are also displayed in the UI, as shown in the following figure.
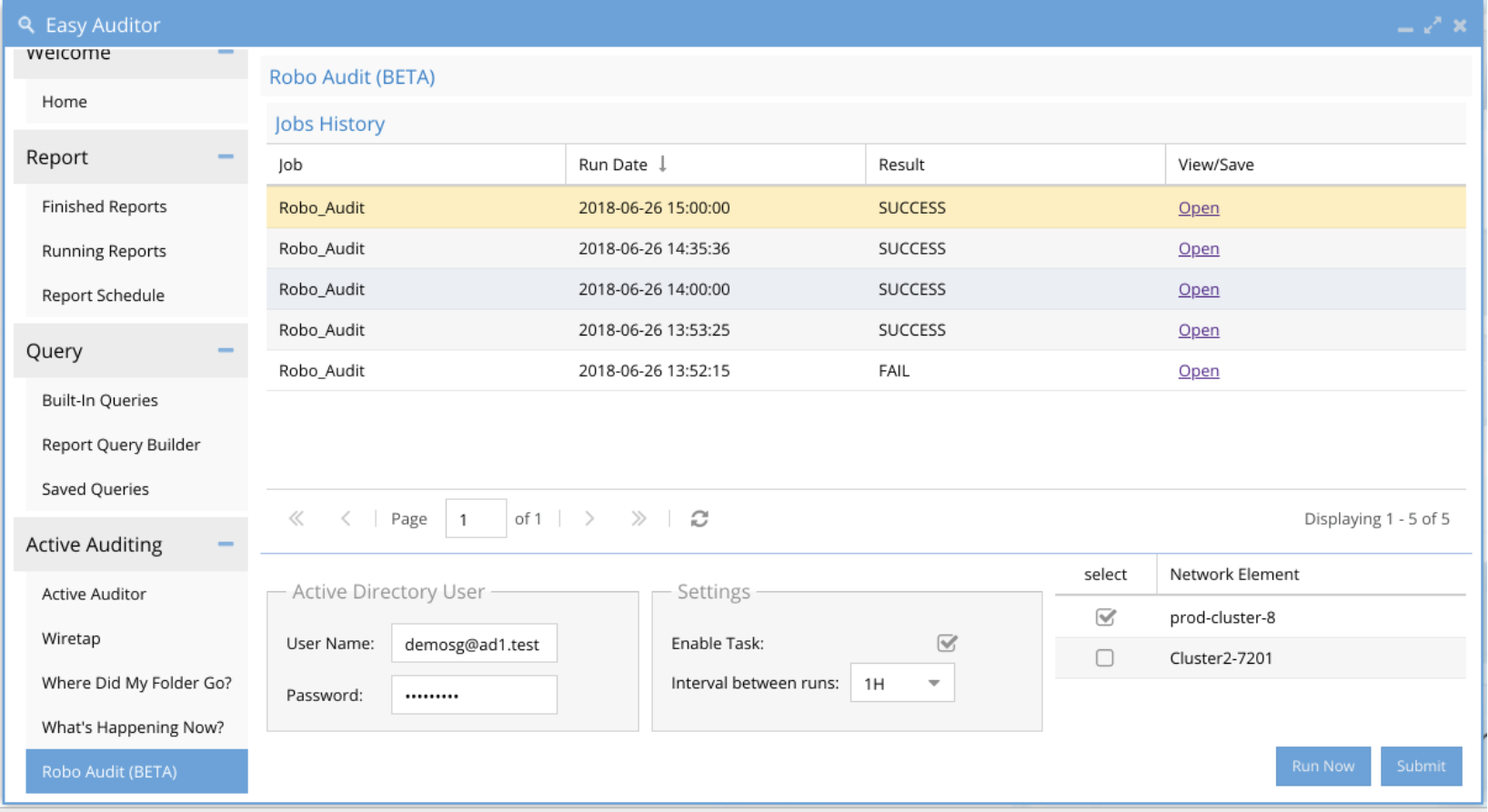
Figure 29. Robo Audit history
