Home > Storage > PowerMax and VMAX > Storage Admin > Persistent Storage for Containerized Applications on Kubernetes with PowerMax SAN Storage > CSM for authorization
CSM for authorization
-
CSM for authorization is the most effective way to enable fine-grained quotas for Kubernetes clusters consuming PowerMax storage. CSM for Authorization enables storage backend multitenancy by giving storage and Kubernetes administrators the ability to:
- Declare tenants to restrict the usage of storage (usually one per Kubernetes cluster)
- Apply RBAC on the resources created by the tenant
- Authenticate tenants with a JSON Web Token (JWT)
To support these use-cases, we need to deploy a proxy between the tenants (CSI drivers) and the storage system.
Once a policy is configured or modified by the storage administrator it applies immediately.
Storage administrators have an interface to create, delete, and manage roles and groups to which storage rules may be applied. Administrators or users, or both, can then generate authentication tokens that can be used by the Kubernetes administrator to use storage with proper access policies being automatically enforced.
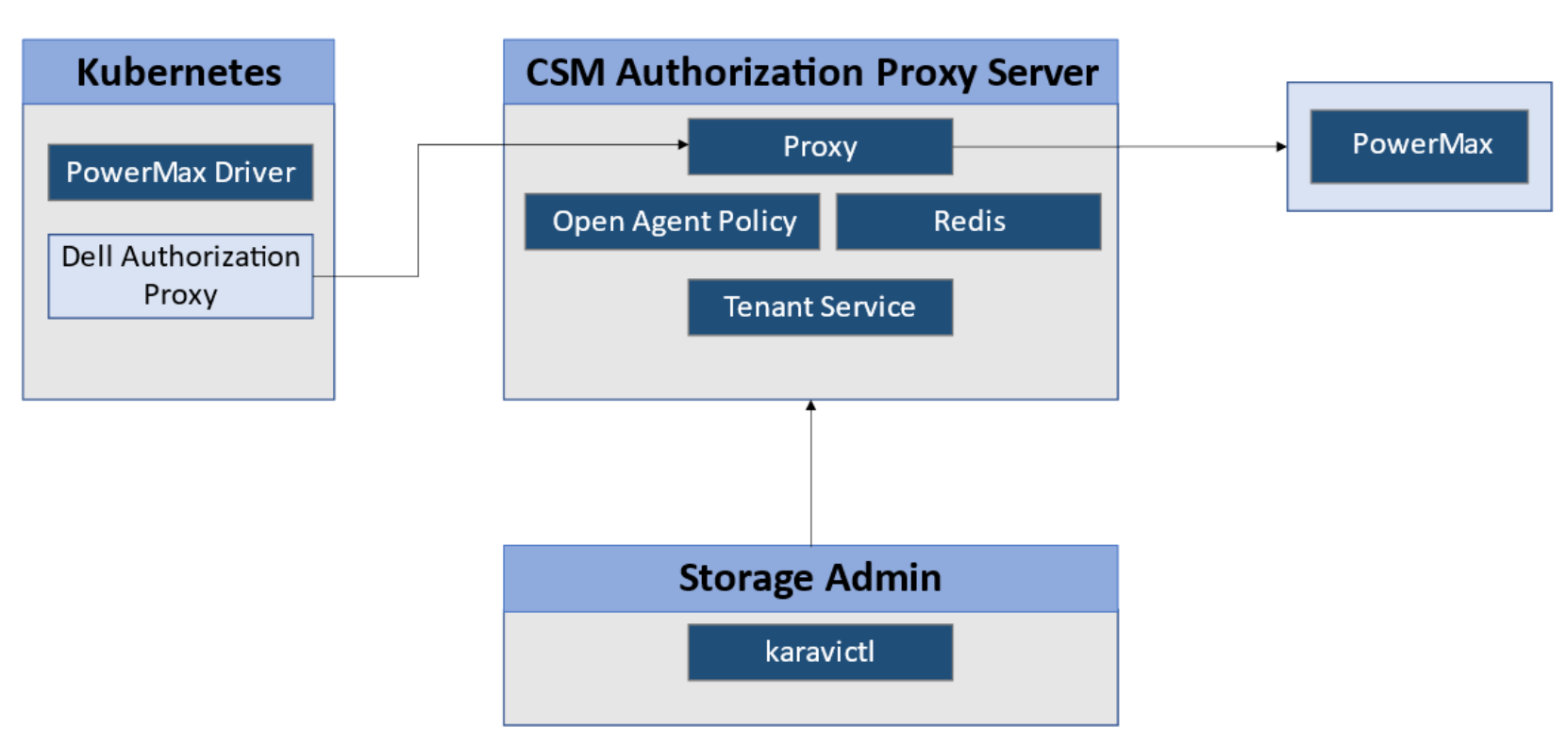
Figure 10. CSM for Authorization software architecture
When CSM for Authorization is used, the typical sequence of events is as follows:
- The storage admin declares the storage endpoints that Kubernetes users will have access to:
karavictl storage create \
--type powermax \
--endpoint ${UnisphereURL} \
--system-id ${SymmetrixID} \
--user smc \
--password ${ArrayPassword} \
--insecure
- The Kubernetes administrator requests storage capacity for one or many clusters.
For a new tenant:
karavictl tenant create -n k8s --insecure \
--addr "grpc.${AuthorizationProxyHost}"
Note: The URL must have the grpc prefix. You must have a DNS entry that resolves that name to the proxy host FQDN or IP address.
- The storage administrator applies the quota:
karavictl role create \
--role=k8s_pmax=powermax=${Symmetrix}=SRP_1=30000
Note: The quota size is given in bytes at the time of the release of this paper.
If the role already exists, you can update it with the same syntax and karavictl role update –role=...- The storage administrator maps the quota to the tenant:
karavictl rolebinding create --tenant k8s \
--role k8s_pmax --insecure \
--addr "grpc.${AuthorizationProxyHost}"
- The storage administrator generates the JWT:
karavictl generate token --tenant k8s --insecure \
--addr "grpc.${AuthorizationProxyHost}" \
| jq -r '.Token' > token.yaml
- The storage administrator sends the token.yaml to the Kubernetes administrator, who applies the JWT to authenticate queries against the proxy.
kubectl apply -f /tmp/token.yaml -n powermax
Note: This procedure assumes that the driver is installed with the Authorization enabled and the CSM Authorization Proxy URL, and the CSM Auth Proxy certificate was imported if trusted communication is required.
Once the quota is in place and JWT authentication is enabled, the Kubernetes administrator cannot access Unisphere credentials. The Kubernetes administrator can only issue queries against the PowerMax objects (LUN, masking view, snapshots) that can be managed with the Kubernetes administrator’s token.
