Home > Storage > PowerFlex > White Papers > Migrating Data to Dell PowerFlex File Servers using Datadobi StorageMAP > Setup
None
-
Configure Migration options in StorageMAP
During migration setup, multiple groups of options can be configured. The first level Job Options window consists of:
- NAS general options
- Advanced NAS options
- SMB general options
- Advanced SMB options
- NFS general options
- Advanced NFS options
NAS general options
The following figure shows the job options:
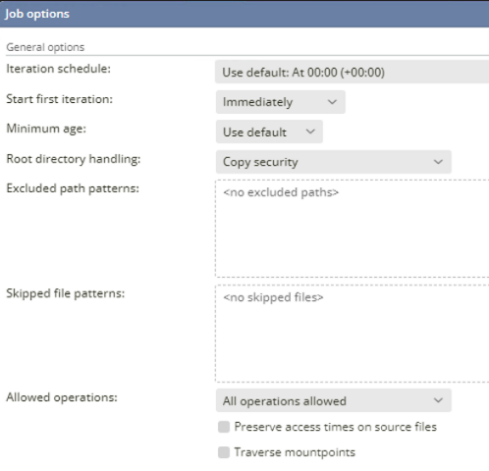
Figure 35. NAS general options
Description of the key options in this screen:
- Iteration schedule: Allows you to define when migration iterations run. By default, the migration starts an iteration at midnight, but there are different values to choose from:
- Other: Allows you to define a custom iteration schedule.
- Use default: Refers to the default schedule as defined in global settings. The value for the default global iteration schedule setting can be changed under Configuration > Global Settings > Job Settings.
- Manual: In this mode you must manually start the next process iteration in the detail screen of the respective processes. Once started, it will run the process for the migration path and pause it again before starting the next process step or iteration.
- Presets: Predefined schedules are sets of starting times, for example every 6 hours would be 0:00, 6:00, 12:00 and 18:00.
- Start the first iteration: Allows you to bypass the iteration schedule and start the first iteration immediately.
- Minimum age: Defines the minimum amount of time a file needs to be unmodified before it will be considered for the next iteration. With this setting you can avoid migrating files that are updated constantly during the steady state process. The globally defined default is set to 1 hour and can be changed in Configuration > Global Settings, Migration Settings.
- Root directory handling: Allows you to determine how StorageMAP should copy the security (permission bits or ACL) of the root folder of the migration to the target. The possibilities are:
- Copy security: Ensures that the StorageMAP copies the security as defined in the source. This is the default setting.
- Don’t copy security: Instructs the StorageMAP not to copy any security settings from the source.
- Convert inherited security to explicit: Copies the security as is but the inherited flag is stripped from each ACE (if present).
- Consolidate root folder: Allows you to migrate directories from several source paths into one target path.
- Consolidate sub folders: Allows you to run the consolidation for the root folder and its first level sub-folders.
- Excluded path/file patterns: Directories or files matching these patterns are excluded from migration and will not be copied from the source file server.
- Skipped path/file patterns: Directories or files matching these patterns are skipped during iterations that are not part of a dry run or switchover.
An example of Excluded/Skipped patterns is shown in the following figure:
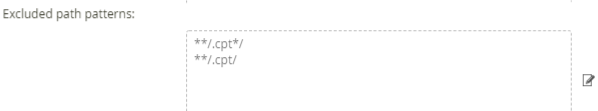
Figure 36. Excluded path pattern
For more information about excluded/skipped path/file patterns and examples see StorageMAP Online Help from Datadobi documentation.
- Allowed operations: Gives you the option to restrict operations that are allowed during migration.
- All operations allowed
- No deletes
- No deletes or updates
- Preserve access times on source: Allows you to preserve the access time of the source files when migrating the data to the target file server.
NAS advanced options
The options shown in the following figure can be set for NAS advanced options for NAS-to-NAS scenarios:
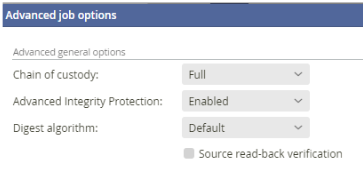
Figure 37. NAS advanced options
- Chain of custody: Specifies for which set of data you would like to generate a Chain of Custody (CoC) entry in the Chain of Custody File (CoCf). This feature provides a full record of migration activity, including timestamps and digests, which is important for auditing purposes. You can choose between the following:
- Full (default): To generate a CoC for all of the data. This means that a CoC will be generated for pre-existing data on the target in addition to generating a CoC for the data that is migrated during this process. The pre-existing data will be validated by comparing it with the source.
- Migrated data: To limit the generation of a CoC to the data that is copied during this migration process. This means that the data that already exists on the target will not be included in the CoCf of this migration.
- None: If you do not wish to keep a CoC for this migration at all. Additionally, files that are modified on the target before a switchover, will be overwritten because there is no CoC.
- Advanced Integrity Protection: Allows you to enable or disable the Advanced Integrity Protection (AIP) setting. Enabling this setting ensures that StorageMAP generates a timely warning when the data on the target is externally modified.
- Digest algorithm: Allows you to choose the hashing algorithm used to compute the digest value, to verify the migrated data and potentially generates a CoC.
- Source read-back verification: Causes StorageMAP to read back the data from the source a second time, after it has been copied, to verify that the source potentially did not supply any corrupt data.
SMB general options
The options shown in the following figure can be set for SMB migration for NAS-to-NAS scenarios:
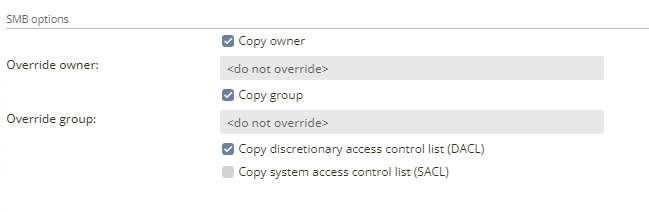
Figure 38. SMB general options
- Follow junctions: By default, StorageMAP skips junctions when these are discovered.
- Copy owner: This copies the owner of the Security Descriptor. When not set, it is left blank on the data on the target file server.
- Override owner: This owner is used for all the migrated files and directories.
- Copy group owner: This copies the group owner of the Security Descriptor. When not set, it is left blank on the data on the target file server.
- Override group: This group is used for all the migrated files and directories.
- Copy discretionary access control list (DACL): A DACL identifies the trustees that are allowed or denied access to files or directories.
- Copy system access control list (SACL): A SACL contains access control entries (ACEs) that specify the types of access attempts that generate audit reports.
SMB advanced options
For SMB migrations the following advanced options are available:
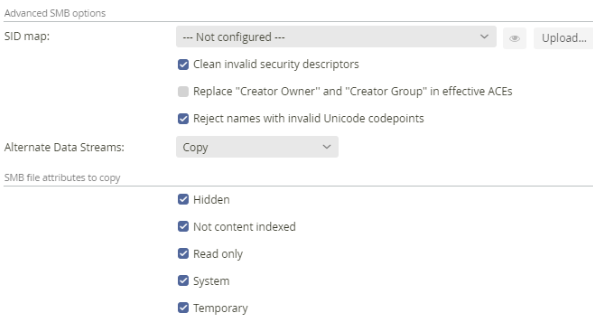
Figure 39. SMB advanced options
- SID map: To specify SID mapping from source to target.
- Clean invalid security descriptors: StorageMAP cleans up any invalid security descriptors that are found on the source platform before copying them to the target.
- Replace "Creator Owner" and "Creator Group" in effective ACEs. These are two well-known SIDs that can be used in inheritable ACEs. Some file servers are tolerant to them appearing in effective (inherited) ACEs; others may refuse to do that. When this option is enabled, StorageMAP replaces these SIDs in effective ACEs by the actual owner and group SIDs of the file.
- Alternate Data Streams:
- Copy: Copies alternate data streams and report errors on failure.
- Copy, ignore errors: Tries to copy alternate data streams, but does not report errors when it fails.
- Don’t copy: Skips alternate data streams.
- SMB file attributes to copy (Hidden, Not content indexed, Read only, System, and Temporary).
NFS general options
The following options can be set for NFS migrations:
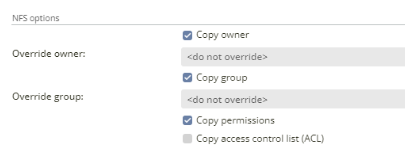
Figure 40. NFS general options
- Copy owner: Copy the owner ID
- Copy group: Copy the group ID
- Copy permissions: Copy the POSIX permissions bits
- Copy access control list (ACL): Copy the POSIX ACL (NFSv3 only) or NFSv4 ACL if present. For NFSv3 to NFSv4 migrations, StorageMAP converts POSIX ACLs to NFSv4 ACLs automatically.
NFS advanced options
The following options can be set for NFS migrations:
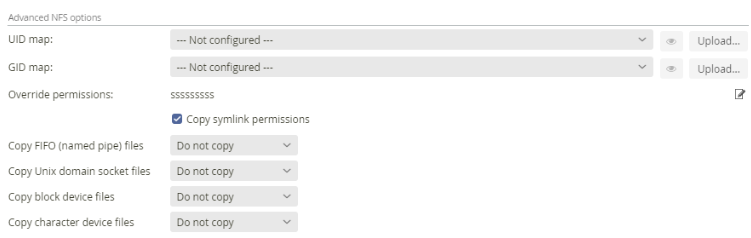
Figure 41. NFS advanced options
- UID map: Here you can specify the UID mapping to be used between source and target.
- GID map: Here you can specify the GID mapping to be used between source and target.
- Override permissions: Allows you override the value of each individual POSIX permission.
- Copy symlink permissions: Allows you to copy symlink permissions.
- Copy FIFO (named pipe) files: Allows you to copy FIFO (named pipe) files. A FIFO file is a special file used for exchanging data between processes running on the same UNIX host. Options include Do not copy, Copy (with ACLs) and Copy (without ACLs).
- Copy UNIX domain socket files: Allows you to copy domain socket files. A UNIX domain socket file is a special file used for exchanging data between processes running on the same UNIX host. Options include Do not copy, Copy (with ACLs) and Copy (without ACLs).
- Copy block device files: Controls whether to recreate block device files on the target.
- Copy character device files: Controls whether to recreate character device files on the target.
