Home > Storage > PowerMax and VMAX > Storage Admin > iSCSI Implementation Guide for Dell EMC Storage Arrays Running PowerMaxOS > Core components of iSCSI
Core components of iSCSI
-
iSCSI architecture is made up of a set of core components. These components are initiator and target nodes, iSCSI names, IP Interfaces, sessions and connections, and security.
Initiators and target nodes
A storage area network (SAN) consists of two types of equipment: initiator and target nodes. Initiators, such as hosts, are data consumers. Targets, such as disk arrays or tape libraries, are data providers. iSCSI based SANs use initiators and targets in the same manner.
- iSCSI initiator nodes are typically host-based software or hardware that sends data to and from iSCSI target nodes (storage arrays). In data migration between storage arrays, the source array can act as an initiator.
- iSCSI target nodes expose one or more SCSI LUNs to specific iSCSI initiators. On the enterprise storage level, iSCSI target nodes are logical entities, not tied to a specific physical port.
iSCSI initiators must manage multiple, parallel communication links to multiple targets. Similarly, iSCSI targets must manage multiple, parallel communication links to multiple initiators. Several identifiers exist in the iSCSI protocol to make this happen, including iSCSI Name, ISID (iSCSI session identifiers), TSID (target session identifier), CID (iSCSI connection identifier) and iSCSI portals.
Names
iSCSI nodes are identified by a unique iSCSI Name. iSCSI names are a human readable ASCII string and must be unique on a per NetID/Network ID basis. iSCSI names can be both user and algorithmically generated. iSCSI Names are formatted in two different ways:
- Enterprise Unique Identifier (EUI): eui.0123456789ABCDEF
- iSCSI Qualified Name (IQN): Most commonly used naming format: iqn.2001-05.com.mircosoft:ProdHost
IP interfaces
iSCSI Nodes are accessed through IP Interfaces (sometimes called Network Portals). iSCSI IP Interfaces contain key network configuration information such as:
- IP Address
- VLAN information
- TCP Port Number
An iSCSI IP Interface can only provide access to a single iSCSI node; however, an iSCSI node can be accessed through multiple IP Interfaces.
Sessions and connections
iSCSI initiator and target nodes communicate by a linkage called an iSCSI session. The session is the vehicle for the transport of the iSCSI PDUs between the initiators and target nodes. Each session is started by the initiator logging into the iSCSI target. The session between the initiator and target is identified by an iSCSI session ID. Session IDs are not tied to the hardware and can persist across hardware swaps.
Session components are tied together by a TCP/IP connection. The IP addresses and TCP port numbers in the IP interfaces define the end points of a connection. The iSCSI protocol allows for multiple connections within a single session (MC/S) as means to provide connection resiliency to a target that is presenting volumes to the host; however, MC/S is rarely done with enterprise iSCSI connections as most enterprise implementations use host-based multipath I/O software (MPIO). Using host-based MPIO, a single host initiator can access the same devices by presenting them through multiple targets on the storage array. This allows the host to see the devices through multiple paths. Each path from the initiator to the targets will have its own session and connection. This connectivity method is often referred to as “port binding.” The diagram below shows these iSCSI connectivity methods:
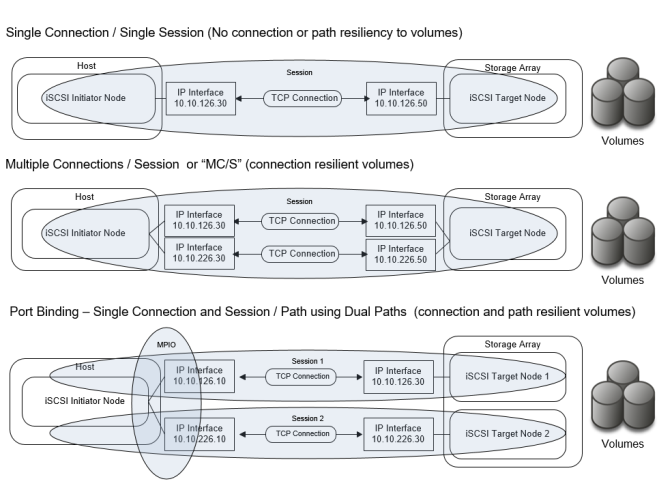
Figure 1. iSCSI connectivity methods
Security and authentication
The most commonly used iSCSI authentication method is Challenge Handshake Authentication Protocol (CHAP). CHAP verifies identity using a hashed transmission of a secret key between initiator and target. The iSCSI specification RFC 7143 defines that CHAP security is the only “must-support” authentication protocol. All other protocols such as Kerberos are considered to “in addition to” CHAP.
The CHAP secret key is a user-defined string up to 32 ASCII characters, or 64 binary characters (binary values should be prefixed with the string “0x”). Note: Windows users need to specify a secret key between 12 and 16 ASCII characters. The users also create a credential name (CHAP username) string between 8 and 256 ASCII characters. For more information about CHAP iSCSI considerations, refer to RFC 7143 section 9.2.1, which can be found at https://tools.ietf.org/html/rfc7143.
Using CHAP, the target initiates the challenge to the initiator for the secret key. It periodically repeats the challenge to guard against replay attacks. CHAP can be a unidirectional /one-way protocol, in which only the target authenticates the initiator, but it can be implemented in two directions (bidirectional and mutual) where the initiator also authenticates the target to provide security for both ends. The following bullets detail these methods:
- In one-way CHAP authentication, also called unidirectional, the target authenticates the initiator, but the initiator does not authenticate the target. With CHAP one-way authentication, the storage array challenges the host during the initial link negotiation process and expects to receive a valid credential and CHAP secret in response. When challenged, the host transmits a CHAP credential and CHAP secret to the storage array. The storage array looks for this credential and CHAP secret internally or on a network “RADIUS” server. Once a positive authentication occurs, the storage array sends an acceptance message to the host. However, if the storage array fails to find any record of the credential or secret pair, it sends a rejection message, and the link is closed.
- In two-way CHAP authentication, also called bi-directional or mutual, an additional level of security enables the initiator to authenticate the target after the target authenticates the initiator. With two-way CHAP authentication, the host challenges and authenticates the storage array. This provides an extra layer of authentication and security in the iSCSI configuration as both the target and initiator act as authenticators and peers.
