Home > Workload Solutions > Container Platforms > Red Hat OpenShift Container Platform > Guides > Implementation Guide—Red Hat OpenShift Container Platform 4.12 on Intel-powered Dell Infrastructure > ObjectScale deployment
ObjectScale deployment
-
Overview
ObjectScale is a software-defined object scale solution based on containerized architecture. This section describes the steps for deploying ObjectScale on a Red Hat OpenShift cluster.
Deployment consists of the following high-level steps:
- Create and prepare necessary namespaces in OpenShift.
- Deploy bare-metal CSI drivers for ObjectScale.
- Install ObjectScale on OpenShift.
- Create an ObjectStore.
Prerequisites
Ensure that:
- CSAH or the admin node have Helm v3.12.1 installed. See Installing Helm.
- Access is available to ObjectScale software from Dell Support.
- Dell ObjectScale Community Edition v1.2.0 is downloaded from the Dell Support website. Copy and extract the .zip file onto the CSAH node.
- A Docker hub account for pulling images is available.
Set the node parameters
On each worker node:
- Connect to the node by running:
oc debug node/<worker node>
- When the prompt appears, run:
chroot /host
- On all the worker nodes, update the following parameters in the /etc/crio/crio.conf file:
- Set the pids_limit to 16384 or add the parameter under [crio.runtime]if it is not already present.
- Add insecure_registries = ["0.0.0.0/0"] under [crio.image]if they are not already present.
Use the following code excerpt to add the parameters:
[crio.runtime]
pids_limit = 16384
[crio.image]
insecure_registries = ["0.0.0.0/0"]
- Restart the crio service for the changes to take effect by running the following command:
sudo systemctl restart crio
Create namespaces
To create the necessary namespaces in OpenShift, on the CSAH node:
- Set the environment variables by running the following command:
export CSI_NS=csi-baremetal
export SSO_NS=openshift-secondary-scheduler-operator
export OBJECTSCALE_NS=objectscale-system
- Create namespaces for the secondary scheduler, bare metal CSI, and ObjectScale by running the following command:
oc create ns $SSO_NS
oc create ns $CSI_NS
oc create ns $OBJECTSCALE_NS
- To apply pod security privileges to the namespaces that you created in the previous step, run the following command:
oc label --overwrite ns $SSO_NS pod-security.kubernetes.io/enforce=privileged pod-security.kubernetes.io/audit=privileged pod-security.kubernetes.io/warn=privileged security.openshift.io/scc.podSecurityLabelSync="false"
oc label --overwrite ns $CSI_NS pod-security.kubernetes.io/enforce=privileged pod-security.kubernetes.io/audit=privileged pod-security.kubernetes.io/warn=privileged security.openshift.io/scc.podSecurityLabelSync="false"
oc label --overwrite ns $OBJECTSCALE_NS pod-security.kubernetes.io/enforce=privileged pod-security.kubernetes.io/audit=privileged pod-security.kubernetes.io/warn=privileged security.openshift.io/scc.podSecurityLabelSync="false"
- Create the role and role binding based on the Role sample file and the RoleBinding sample file. Update any fields as necessary.
oc project $CSI_NS
oc create -f <role yaml file>
oc create -f <role binding yaml file>
- Create a docker registry pull secret in all three namespaces:
oc create secret docker-registry dockercreds --docker-server=docker.io/objectscale --docker-username=<docker username> --docker-password=<docker password> --docker-email=<docker account email> -n $SSO_NS
kubectl create secret docker-registry dockercreds --docker-server=docker.io/objectscale --docker-username==<docker username> --docker-password=<docker password> --docker-email=<docker account email> -n $CSI_NS
kubectl create secret docker-registry dockercreds --docker-server=docker.io/objectscale --docker-username==<docker username> --docker-password=<docker password> --docker-email=<docker account email> -n $OBJECTSCALE_NS
Deploy bare-metal CSI drivers for ObjectScale
On the CSAH node:
- Set the environment variables by running the following command:
export REGISTRY=docker.io/objectscale
export DOCKER_REGISTRY_SECRET=dockercreds
export CSI_VERSION=1.2.0-629.b170400
export CSI_OPERATOR_VERSION=1.2.0-116.57df4c8
export CHARTS_DIR=/home/core/objectscale
- Extract the CSI Helm charts.tgz file by running the following command:
tar zxf dellemc-csi-helm-charts-1.2.0-116.57df4c8.tgz
- Install the secondary scheduler operator by running the following command:
helm install secondary-scheduler-operator $CHARTS_DIR/dellemc-csi-helm-charts/secondaryscheduleroperator-$CSI_OPERATOR_VERSION.tgz -n $SSO_NS --set global.registry=$REGISTRY --set image.tag=$CSI_OPERATOR_VERSION --set global.registrySecret=$DOCKER_REGISTRY_SECRET
- Wait for the secondary scheduler operator to start. Verify that the secondary scheduler operator pods are in the Running state by running the following command:
oc get pod -n $SSO_NS
- Install the CSI bare-metal operator by running the following command:
helm install csi-baremetal-operator $CHARTS_DIR/dellemc-csi-helm-charts/csi-baremetal-operator-$CSI_OPERATOR_VERSION.tgz --set global.registry=$REGISTRY --set global.registrySecret=$DOCKER_REGISTRY_SECRET --set image.tag=$CSI_OPERATOR_VERSION --namespace $CSI_NS
- Wait for the CSI bare-metal operator pods to start, and then verify that the Operator pod is in the Running state by running the following command:
oc get pod -n $CSI_NS
- Start the CSI bare-metal deployment by running the following command:
helm install csi-baremetal $CHARTS_DIR/dellemc-csi-helm-charts/csi-baremetal-deployment-$CSI_OPERATOR_VERSION.tgz --set image.tag=$CSI_VERSION --set global.registry=$REGISTRY --set global.registrySecret=$DOCKER_REGISTRY_SECRET --set scheduler.patcher.enable=true --set platform=openshift --set driver.drivemgr.type=halmgr --namespace $CSI_NS
The CSI bare-metal deployment starts after approximately five minutes.
- Verify that the new CSI storage classes are created:
oc get sc
The following is sample output from the command:
NAME PROVISIONER RECLAIMPOLICY VOLUMEBINDINGMODE ALLOWVOLUMEEXPANSION AGE
csi-baremetal-sc (default) csi-baremetal Delete WaitForFirstConsumer false 21d
csi-baremetal-sc-hdd csi-baremetal Delete WaitForFirstConsumer false 21d
csi-baremetal-sc-hddlvg csi-baremetal Delete WaitForFirstConsumer true 21d
csi-baremetal-sc-nvme csi-baremetal Delete WaitForFirstConsumer false 21d
csi-baremetal-sc-nvme-raw-part csi-baremetal Delete WaitForFirstConsumer false 21d
csi-baremetal-sc-nvmelvg csi-baremetal Delete WaitForFirstConsumer true 21d
csi-baremetal-sc-ssd csi-baremetal Delete WaitForFirstConsumer false 21d
csi-baremetal-sc-ssdlvg csi-baremetal Delete WaitForFirstConsumer true 21d
csi-baremetal-sc-syslvg csi-baremetal Delete WaitForFirstConsumer true 21d- When the new CSI pods and all the containers are in the Running state, check the number of containers in the Ready column (for example, 4/4) by running the following command:
oc get pod -n $CSI_NS
Install ObjectScale on OpenShift
Follow these steps:
- Extract the ObjectScale helm charts.tgz file by running the following command:
tar zxf objectscale-helm-charts-1.2.0.tgz
- To view the Dell End User License Agreement (EULA), run:
helm show readme $CHARTS_DIR/objectscale-portal-1.2.0.tgz | more
The EULA Revision Date value is shown in the last line of the readme file in the format ddMMMYYYY.
- Set an environment variable for the date, for example:
export EULA_DATE=09Sep2020
- Deploy ObjectScale in your OpenShift cluster using a cluster-admin user by running the following command:
helm install objs $CHARTS_DIR/objectscale-portal-1.2.0.tgz --set global.registry=docker.io/objectscale --set global.registrySecret=$DOCKER_REGISTRY_SECRET --set global.storageClassName=csi-baremetal-sc-nvmelvg --set global.secondaryStorageClass=csi-baremetal-sc-ssdlvg --set global.platform=OpenShift --set global.schedulerName=csi-baremetal-scheduler --namespace $OBJECTSCALE_NS --set accept_eula=$EULA_DATE
This step installs the ObjectScale Portal UI, ObjectScale Manager, DECKS, and KAHM on the OpenShift cluster.
It takes 15 to 20 minutes for all the services to start.
- Get a list of all the Kubernetes applications to ensure that all the ObjectScale components are present by running the following command:
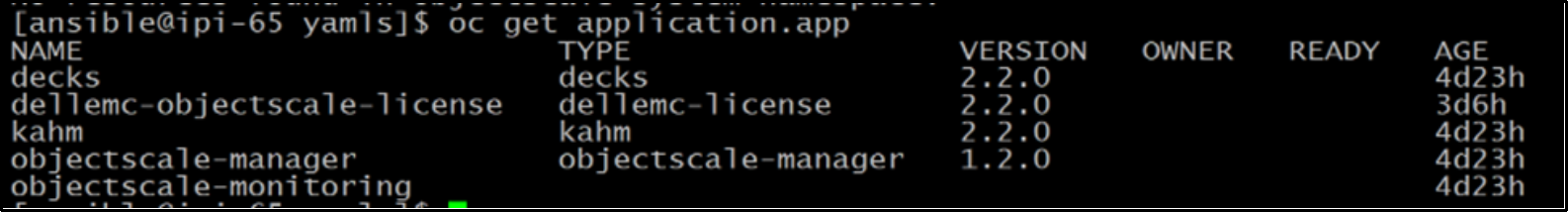
oc get application.appFigure 18. Sample command output – ObjectScale applications
- After a few minutes, verify that the ObjectScale components are in the Deployed status by running the following command:
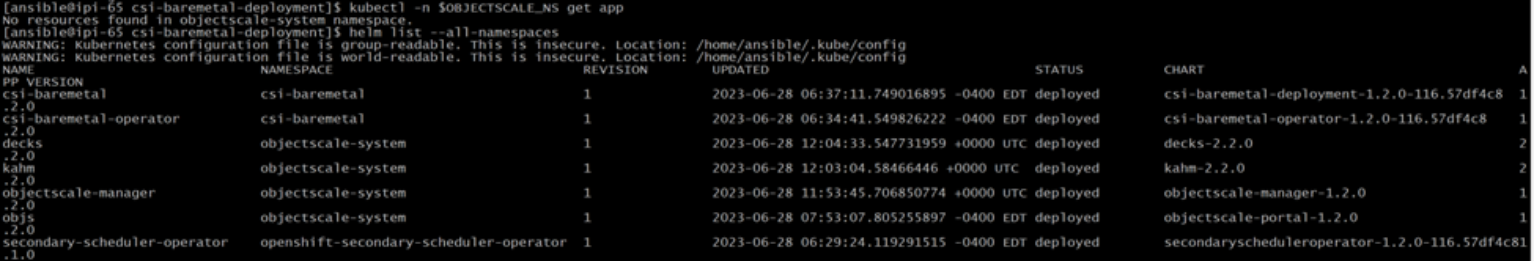
helm list --all-namespacesFigure 19. Sample output – ObjectScale components status
- Install the csi-baremetal-alerts chart into the default namespace by running the following command:
helm install csi-baremetal-alerts --namespace $CSI_NS $CHARTS_DIR/csi-baremetal-alerts-1.2.0.tgz
- After the installation is complete, edit the objectscale-portal-external service to change it to the NodePort type. Run the following command:
oc edit svc objectscale-portal-external -n $OBJECTSCALE_NS
Follow this spec definition example:
spec:
clusterIP: 172.30.22.231
clusterIPs:
- 172.30.22.231
externalTrafficPolicy: Cluster
internalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- name: https
nodePort: 32096
port: 4443
protocol: TCP
targetPort: 4443
selector:
app.kubernetes.io/component: objectscale-portal
app.kubernetes.io/name: objectscale-manager
sessionAffinity: None
type: NodePort
- Identify the port to be used to access the ObjectScale UI by running the following command:
oc get svc -A | grep objectscale-portal-external
objectscale-portal-external LoadBalancer 172.30.252.135 <pending> 4443:32467/TCP 27d
objectscale-portal-external-in NodePort 172.30.103.73 <none> 4443:32096/TCP,8080:32560/TCP 27d
- Based on the output of the command, the port for accessing the web UI is 32096. You can access the ObjectScale console through a browser at https://<worker-node-ip>:32096.
Create an ObjectStore
To create an ObjectStore, you must:
- Apply an ObjectScale license.
- Create an account and a user.
- Create an ObjectStore instance.
- Add accounts to the ObjectStore.
Apply an ObjectScale license
To apply an ObjectScale license:
- Log in to the ObjectScale web UI.
- Expand the Administration tab to view the ObjectScale license settings.
- Select Licensing and click Apply.
- In the Apply License area, browse to the ObjectScale license file and upload it. Click Apply.
- Expand the license in the Licensing table to display details about the ObjectScale license and the enabled features and capacities.
Create an account and a user
To create an account and a user:
- Expand the Manage S3 section on the left pane, and click Accounts.
- Click New account.
- Provide a name in the alias field, enable or disable encryption, and click Save.
- Click the newly created account name.
- On the Users tab, click New User.
Note: It is only possible to create a bucket in ObjectStore after associating one or more accounts to the ObjectStore. An access key pair for the user is needed for bucket authentication.
- Provide a name for the user.
In the Permissions tab, you can assign policies to give the user access to different components in the ObjectScale console.
- In the Policies tab, select all the policies that you want to assign to the user.
- In Tags, add the necessary tags for user identification.
- Review the details and create the user.
- Download the .csv file containing the access key and secret access key for the user.
Create an ObjectStore instance
To create an ObjectStore instance:
- Create a new namespace on the cluster by running the following command:
oc new-project objectstore
- On the ObjectScale portal UI, expand Manage S3 in the left pane.
- Click ObjectScale and select Object Stores.
- Select the new namespace from the dropdown menu and click New Object Store.
- Provide a name for the new object store instance, verify the namespace, and select the version you require.
- Choose User Storage Class and System Storage Class names from the dropdown menu and click Advanced.
- On the Topology page, select the nodes to be used for creating the object store instance.
- On the Storage tab, edit storage and memory details of nodes as required. For example, edit the replicas for server storage and volumes to determine the storage capacity for user buckets in this object store instance.
- In the Connectivity tab, change the S3 service type from load balancer to NodePort.
This change enables http ports for an insecure connection.
- In the Review and Save tab, verify the details and create the object store instance.
When all the components are created and all the pods are running, the object store instance state changes to "Started" and Health changes to "Available."
Add accounts to the ObjectStore
To add accounts to the object store instance:
- Expand Manage S3 in the left pane and click the ObjectScale tab.
- On the ObjectStore tab, click the name of the object store instance and select Accounts.
- Click Add and select the Account ID of the object store instance. Enable or disable encryption as required.
- If needed, add a bucket default quota to limit the bucket size. To do this, enter values for Block Writes at Quota and Notification as required and click Save.
Leave these fields empty if no restrictions are to be applied.
All users in the account gain access to buckets in the object store instance based on the policies you attach to the individual user.
Create a bucket
Buckets are object containers that are used to store and control access to objects.
To create a bucket:
- Expand Manage S3 in the left pane and click the Buckets tab.
- Select the namespace, object store instance, and account from the dropdown menus. Click New Bucket.
- In the General tab, provide a name for the bucket and verify the namespace, object store instance, and account details. Click Next.
- In the Policy tab, create a bucket policy if needed. Click Next.
- In the Control tab, enable or disable versioning, object lock, quotas, and encryption. Click Next.
- If required, create events in the Event Rule tab. Click Next.
- Review the details in the Review tab. Click Save.
