Home > Workload Solutions > Container Platforms > Red Hat OpenShift Container Platform > Archive > Implementation Guide—Red Hat OpenShift Container Platform 4.10 on AMD-powered Dell Infrastructure > Overview
Overview
-
Using Dell Container Storage Modules
Dell Technologies Container Storage Modules (CSMs) are an extension to the traditional CSI drivers. CSMs enable simple and consistent integration for cloud-native stateful applications. As part of this validated design, the Dell OpenShift engineering team validated two of the CSMs—Authorization and Observability—on PowerMax and PowerStore servers respectively.
The following table shows the support matrix for Dell CSM and CSI drivers. For more information, see the Dell Technologies Container Storage Modules page.
Table 4. Dell CSM-CSI support matrix
CSM module
CSI PowerFlex v2.3.0
CSI PowerScale v2.3.0
CSI PowerStore v2.3.0
CSI PowerMax v2.3.0
Authorization v1.3
✔️
✔️
❌
✔️
Observability v1.2
✔️
❌
✔️
❌
Replication v1.3
❌
✔️
✔️
✔️
Resiliency v1.2
✔️
✔️
❌
❌
CSM Authorization
This section describes how to deploy CSM Authorization and CSI drivers for PowerMax. A Helm-based approach is used for deployment of both the CSM and the CSI.
Note: Helm-based CSM Authorization deployment requires a persistent volume (PV) other than the PowerMax CSI that is deployed after the CSM. If a PV is not available, it is possible to deploy the CSM on another OpenShift cluster that has network connectivity to the primary cluster.
The high-level steps for CSM Authorization deployment are:
- Installing CSM Authorization using Helm
- Configuring Authorization objects
- Installing PowerMax CSI driver using Helm
Prerequisites
Ensure that:
- Storage Class is available on the cluster to create the PV that the CSM requires.
- DNS A-record is created.
- Helm 3 is installed on the CSAH node.
Installing CSM Authorization using Helm
To deploy CSM Authorization, perform the following steps on the CSAH node:
- Clone the Git repository:
[core@csah-pri ~]$ git clone https://github.com/dell/helm-charts.git
- Create a namespace for CSM Authorization:
[core@csah-pri ~]$ oc new-project authorization
- Use this sample file to create the karavi-config-secret secret:
[core@csah-pri helm-charts]$ oc create secret generic karavi-config-secret -n authorization --from-file=config.yaml=<config file>
- Use this sample file to create the myvalues.yaml file to be used for CSM installation. Update the file parameters as applicable.
[core@csah-pri helm-charts]$ helm -n authorization install authorization -f myvalues.yaml charts/csm-authorization
- Fetch the LoadBalancer port assigned to the authorization-nginx-ingress-controller service. This port is used in further commands to create CSM Authorization objects.
[core@csah-pri helm-charts]$ oc get svc authorization-ingress-nginx-controller -n authorization
authorization-ingress-nginx-controller LoadBalancer 172.30.32.204 <pending> 80:31305/TCP,443:30172/TCP 5d21h
From the output in the preceding example, the port is 30172.
Configuring Authorization objects
The Karavictl CLI is required to create and manage CSM Authorization objects—Storage Systems, Tenants, Roles, and RoleBindings. The CLI can be installed on the CSAH node.
- Download karavictl binary from the GitHub repository.
- Copy the binary into /usr/local/bin/.
- Create Authorization objects.
In the following commands, the authorization hostname is csm-authorization.dcws.lab and the ingress port is 30172. Set these values to the hostname that you configured while installing CSM and the port you assigned to authorization-ingress-nginx-controller service in Installing CSM Authorization using Helm.
- Storage System
[core@csah-pri helm-charts]$ karavictl storage create --type powermax --endpoint https://<PowerMax unisphere IP>:8443 --system-id <PowerMax id> --user <PowerMax unisphere user> --password <PowerMax unisphere user password> --insecure --array-insecure --addr "storage csm-authorization.dcws.lab:30172"
- Tenant
[core@csah-pri helm-charts]$ karavictl tenant create --name Finance --insecure --addr "tenant. csm-authorization.dcws.lab:30172"
- Role
[core@csah-pri helm-charts]$ karavictl role create --insecure --addr role.csm-authorization.dcws.lab:30172 --role=<role name>=powermax=<PowerMax id>=<PowerMax storage resource pool name>=<storage quota for the role>
- Role Binding
[core@csah-pri helm-charts]$ karavictl rolebinding create --tenant <tenant name> --role <role name> --insecure --addr "tenant.csm-authorization.dcws.lab:30172"
- Generate a token and save it in the token.yaml file:
[core@csah-pri helm-charts]$ karavictl generate token --tenant Finance --insecure --addr "tenant.csm-authorization.dcws.lab:30172" | jq -r '.Token' > token.yaml
This token is used to create the secret in the namespace where the CSI driver will be installed.
Installing PowerMax CSI driver using Helm
Prerequisites
Ensure that:
- All the compute nodes have the iscsi service enabled.
- All the compute nodes can reach the proxy server pods that were created in Installing CSM Authorization.
Steps
The CSI driver is deployed along with the authorization sidecar containers to enable the CSM. To deploy the Dell CSI driver for PowerMax:
- Clone the git repository for the CSI driver:
[core@csah-pri ~]$git clone -b v2.3.0 https://github.com/dell/csi-powermax.git
- Create a namespace and the secrets that are required by the driver. Use the token.yaml file that you generated in step 4 of Configuring Authorization objects for this step.
[core@csah-pri ~]$ oc new-project powermax
[core@csah-pri ~]$ oc apply -f token.yaml -n powermax
- Using this sample file for guidance, update the required parameters and create the karavi-authorization-config.json file. This file is used to create the karavi-authorization-config secret.
[core@csah-pri ~]$ oc -n powermax create secret generic karavi-authorization-config --from-file=config=karavi-authorization-config.json -o yaml --dry-run=client | oc apply -f -
- Create proxy-server-root-certificate secret with empty data:
[core@csah-pri ~]$ oc -n powermax create secret generic proxy-server-root-certificate --from-literal=rootCertificate.pem= -o yaml --dry-run=client | oc apply -f -
- Using this sample file for guidance, create the PowerMax settings YAML file and run the installer to deploy the CSI driver. (The installer is in the dell-csi-helm-installer directory.)
[core@csah-pri dell-csi-helm-installer]$ ./csi-install.sh --namespace powermax --skip-verify-node --values <PowerMax settings yaml file>
- To validate the configuration, create a PVC with a capacity that is greater than the allowed quota.
The PVC remains in a pending state and you will see an error message similar to the following snippet when the PVC is described:
csi-powermax.dellemc.com_powermax-controller-7b55954769-vztql_49f40103-71ca-4518-8f22-e1e02b374cb2 failed to provision volume with StorageClass "powermaxsc-iscsi": rpc error: code = Internal desc = Could not create volume: pmax-bd536f220d: couldn't create volume. error - request denied: no roles in [FinanceRole] allow the 115344000 Kb request on powermax/000297901797/SRP_1
CSM Observability
The section describes how to deploy CSM Observability for PowerStore.
The high-level steps for CSM Observability deployment are:
- Install CSM Observability using the installer
- Deploy the postinstallation dependencies
Prerequisites
Ensure that:
- Helm 3.3 is installed on the CSAH node
- Dell CSI driver for PowerStore is deployed. See Provisioning PowerStore storage.
Installing CSM Observability using the installer script
To deploy CSM Observability:
- Clone the git repository by running:
[core@csah-pri ~]$ git clone https://github.com/dell/karavi-observability.git
- Change to the installer directory:
[core@csah-pri ~]$ cd karavi-observability/installer
- Use this sample file to create a myvalues.yaml file with all the configuration parameters, and then run the installer:
[core@csah-pri installer]$ ./karavi-observability-install.sh install --namespace <namespace where observability will be installed> --values myvalues.yaml
- Validate that the pods are in a running state:
[core@csah-pri installer]$ oc get pods -n <observability namespace>
NAME READY STATUS RESTARTS AGE
karavi-metrics-powerstore-7f64dddd55-8g59v 1/1 Running 0 20h
karavi-observability-cert-manager-74555ff9c8-s5nmm 1/1 Running 0 20h
karavi-observability-cert-manager-cainjector-7d4f86fbb7-4ln7z 1/1 Running 0 20h
karavi-observability-cert-manager-webhook-86f5f456fb-9sdfq 1/1 Running 0 20h
karavi-topology-54ff74c46f-86tbn 1/1 Running 0 20h
otel-collector-84879ff78c-vmw6g 2/2 Running 0 20h
Deploying the postinstallation dependencies
CSM Observability requires the following components:
- Prometheus
- Grafana along with dashboards
Prometheus deployment
To deploy Prometheus:
- Add the Helm chart repository for Prometheus:
[core@csah-pri installer]$ helm repo add prometheus-community https://prometheus-community.github.io/helm-charts
WARNING: Kubernetes configuration file is group-readable. This is insecure. Location: /root/.kube/config
WARNING: Kubernetes configuration file is world-readable. This is insecure. Location: /root/.kube/config
"prometheus-community" has been added to your repositories
[core@csah-pri installer]$ helm repo add stable https://charts.helm.sh/stable
WARNING: Kubernetes configuration file is group-readable. This is insecure. Location: /root/.kube/config
WARNING: Kubernetes configuration file is world-readable. This is insecure. Location: /root/.kube/config
"stable" has been added to your repositories
[core@csah-pri installer]$ helm repo update
WARNING: Kubernetes configuration file is group-readable. This is insecure. Location: /root/.kube/config
WARNING: Kubernetes configuration file is world-readable. This is insecure. Location: /root/.kube/config
Hang tight while we grab the latest from your chart repositories...
...Successfully got an update from the "dell" chart repository
...Successfully got an update from the "prometheus-community" chart repository
...Successfully got an update from the "stable" chart repository
Update Complete. ⎈Happy Helming!⎈
- Using this sample file, create a prometheus-values.yaml file with all the configuration parameters and install Prometheus in the same namespace as CSM Observability:
[core@csah-pri installer]$ helm install prometheus prometheus-community/prometheus -n <observability namespace> -f prometheus-values.yaml
Grafana deployment and configuration
To deploy Grafana:
- Add the Helm chart repository for Grafana:
[core@csah-pri installer]$ helm repo add grafana https://grafana.github.io/helm-charts
WARNING: Kubernetes configuration file is group-readable. This is insecure. Location: /root/.kube/config
WARNING: Kubernetes configuration file is world-readable. This is insecure. Location: /root/.kube/config
"grafana" has been added to your repositories
[root@ocp10-csah installer]# helm repo update
WARNING: Kubernetes configuration file is group-readable. This is insecure. Location: /root/.kube/config
WARNING: Kubernetes configuration file is world-readable. This is insecure. Location: /root/.kube/config
Hang tight while we grab the latest from your chart repositories...
...Successfully got an update from the "dell" chart repository
...Successfully got an update from the "grafana" chart repository
...Successfully got an update from the "prometheus-community" chart repository
...Successfully got an update from the "stable" chart repository
Update Complete. ⎈Happy Helming!⎈
- Using this sample file, create a grafana-values.yaml file with all the configuration parameters, and then install Grafana in the same namespace as CSM Observability:
[core@csah-pri installer]$ helm install grafana grafana/grafana -n <observability namespace> -f grafana-values.yaml
- Verify that all the pods for Karavi Observability, Prometheus, and Grafana are in a running state:
[core@csah-pri installer]$ oc get pods
NAME READY STATUS RESTARTS AGE
grafana-65664685f9-vj4zc 3/3 Running 0 2h
karavi-metrics-powerscale-56569fc59d-k546l 1/1 Running 0 2h
karavi-metrics-powerstore-fc9f6657b-lghsx 1/1 Running 0 2h
karavi-observability-cert-manager-74555ff9c8-j29xd 1/1 Running 0 2h
karavi-observability-cert-manager-cainjector-7d4f86fbb7-k67cz 1/1 Running 0 2h
karavi-observability-cert-manager-webhook-ddb4f6b8-k2bbq 1/1 Running 0 2h
karavi-topology-779499b58d-qtkxl 1/1 Running 0 2h
otel-collector-596b74666c-4dkhl 2/2 Running 0 2h
prometheus-server-7dc7c7bffb-9d9v7 1/1 Running 0 2h
- Check the services and fetch the port for accessing the Grafana UI:
[core@csah-pri installer]$ oc get svc grafana
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
grafana NodePort 172.30.215.181 <none> 80:31472/TCP 2h
The output shows that the Grafana UI is accessible through port 31472.
- Log in to the Grafana UI from a web browser using the credentials specified in the YAML file in step 2. From the left-side menu in the Grafana UI, import the preconfigured observability dashboards.
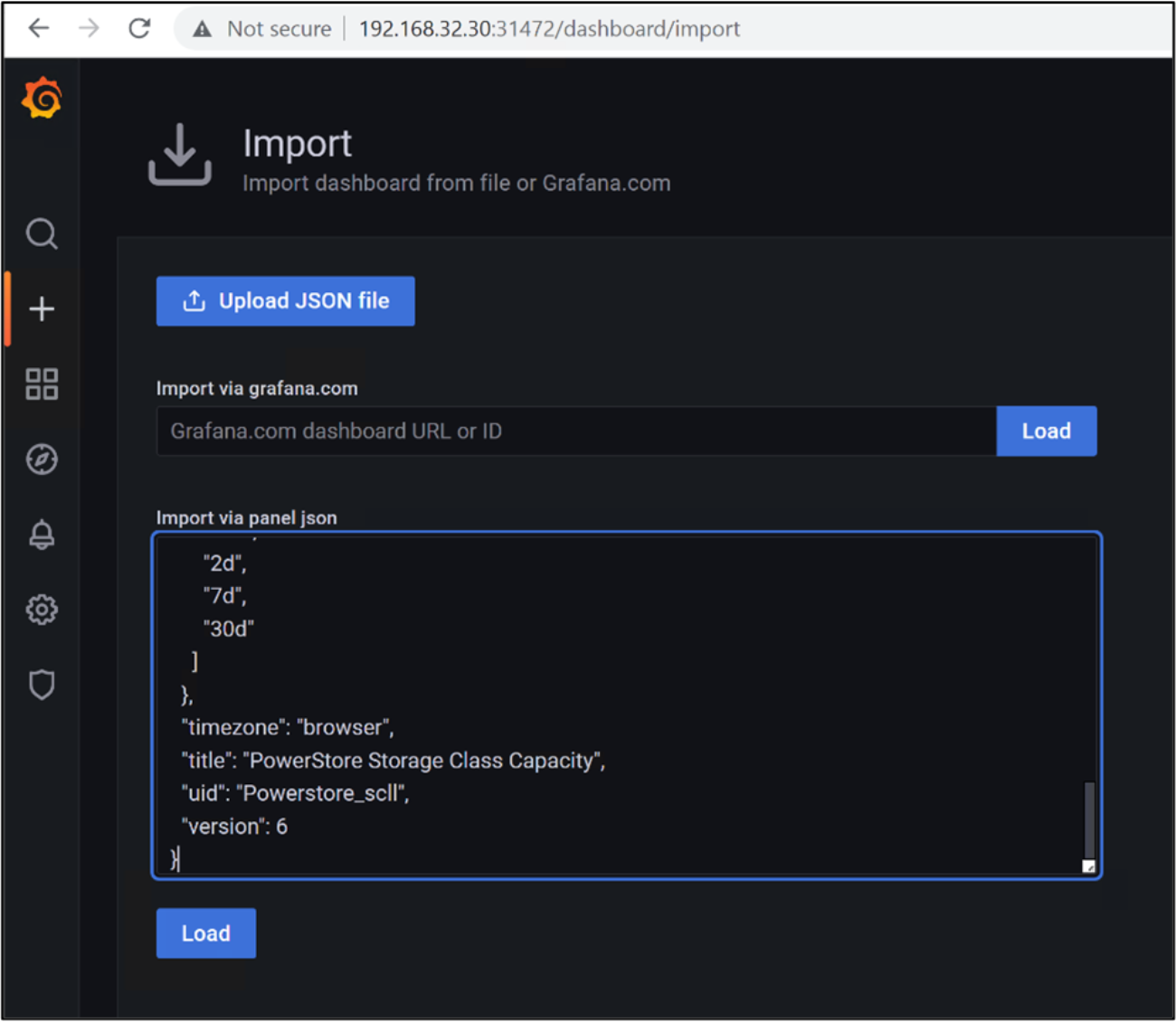
Figure 24. Importing the Grafana dashboards
The following figures show the Grafana dashboards:

Figure 25. PowerStore Filesystem I/O metrics
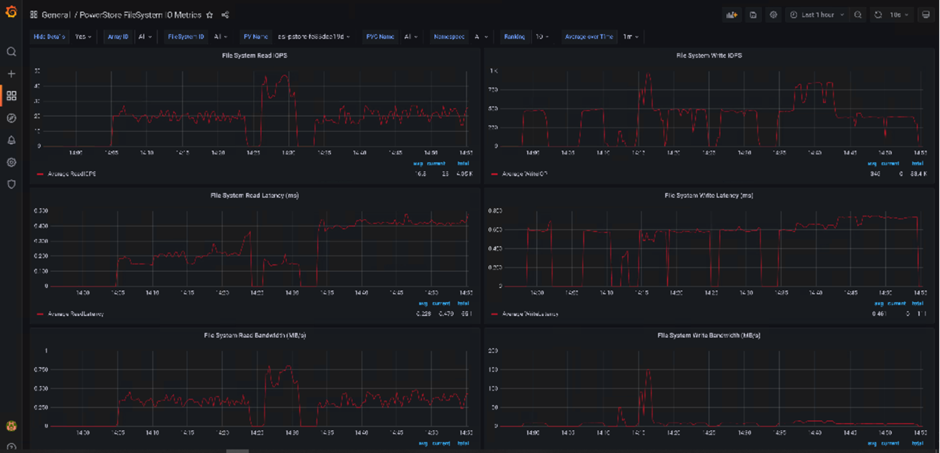
Figure 26. PowerStore Storage Class capacity
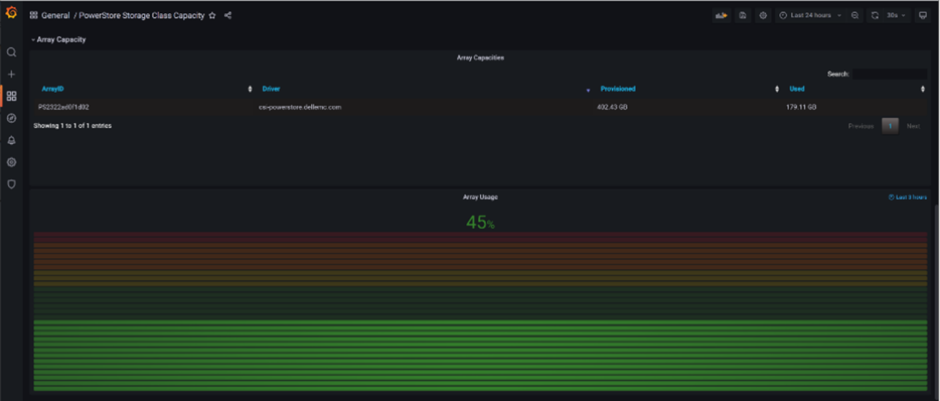
Figure 27. PowerStore CSI driver topology
