Home > Storage > ObjectScale and ECS > Product Documentation > ECS with HAProxy Load Balancer > HTTP/HTTPS configuration definitions
HTTP/HTTPS configuration definitions
-
In the previous example for handling HTTP requests described in HTTP, the frontend defined three different rules to handle the different ECS protocols (object, atmos and swift). Also, there was a separate frontend to handle HTTPS type of requests described in HTTPS. In the example shown in the following figure, there is a single frontend to handle both http and https type of traffic and a single rule. In order to handle virtual host style addressing (i.e., prepending bucket name to ECS base URL), a separate map file called host2backen.map is defined. This file contains two entries, the host header it needs to match and the destination backend name that will handle the request with the matching host header as illustrated in Figure 50.
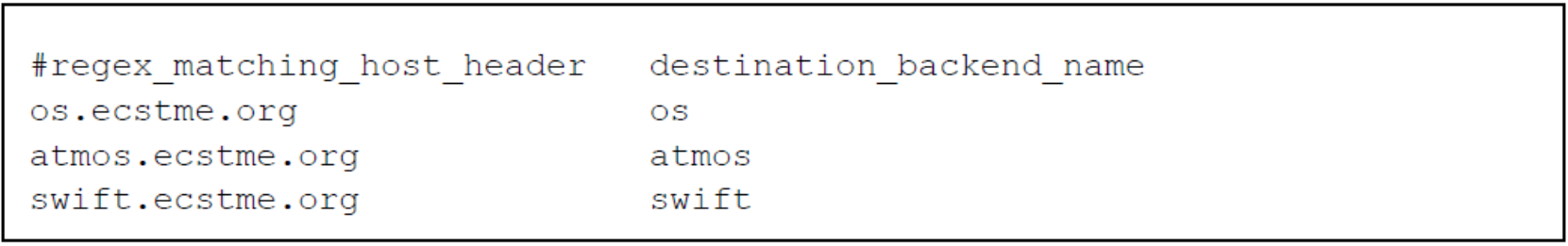
Figure 51. Example of map file for HAProxy
After the globals and defaults section of the configuration file in /etc/haproxy/haproxy.cfg, append the frontend block shown in Figure 50. The first line in the frontend block “http-in” tells HAProxy to listen for requests on port 80 for http requests and port 443 for https requests on all interfaces. It also specifies a single use_backend rule to route the traffic to the backend having the same name as the host header defined in the host2backend.map file. For instance, if the path of the user header request contains “os.ecstme.org, atmos.ecstme.org, or swift.ecstme.org” it will re-direct the request to appropriate named protocol backend such as os, atmos, and swift.
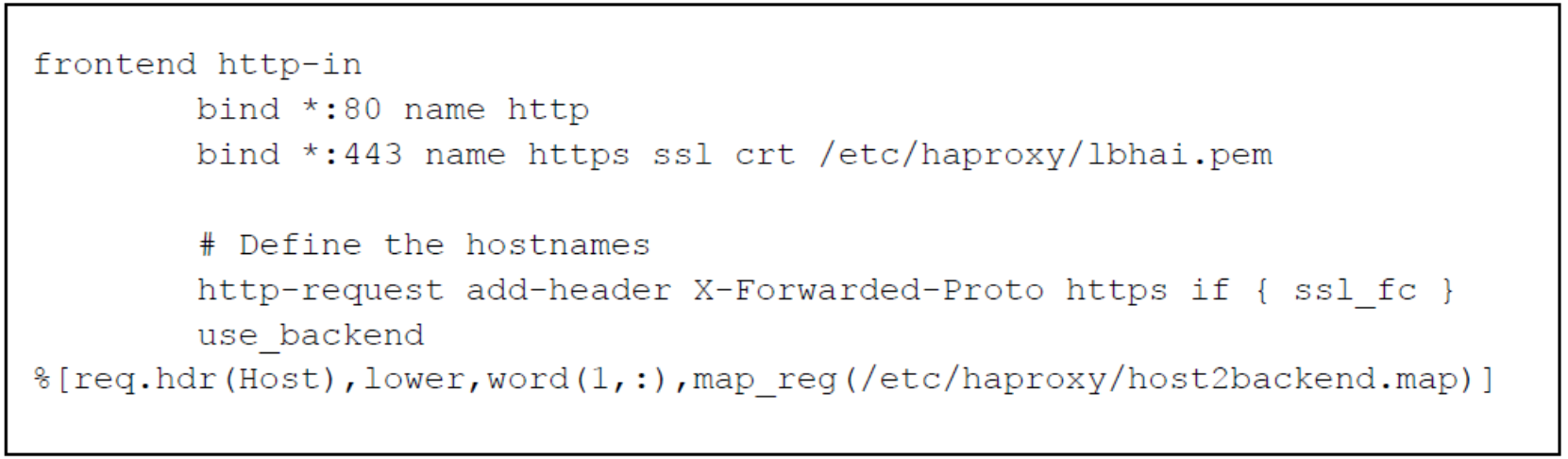
Figure 52. Example of frontend definitions for object access
Further append the haproxy.cfg file with the backend definitions of “os”, “swift”, and “atmos” specified as the named backend in host2backend.map file as shown in Figure 52. Each object protocol goes through a certain port thus all S3 requests for http go thru port 9020, Atmos, thru port 9022, and Swift thru 9024. So, for each protocol backend, a list of ECS nodes IP addresses and ports are specified in “server” line. Similar to the previous example described in Example deployments of ECS with HAProxy setup, the s3_backend and swift_backend, “check” is added at the end of the line to perform health checks on ECS services on each node using “S3 ping” or “Swift healthcheck” as specified in “option httpchk”. The “check” specified for atmos_backend will only check if the ECS node is reachable since this protocol does not yet have support for the “ping operation” to check the ECS services.
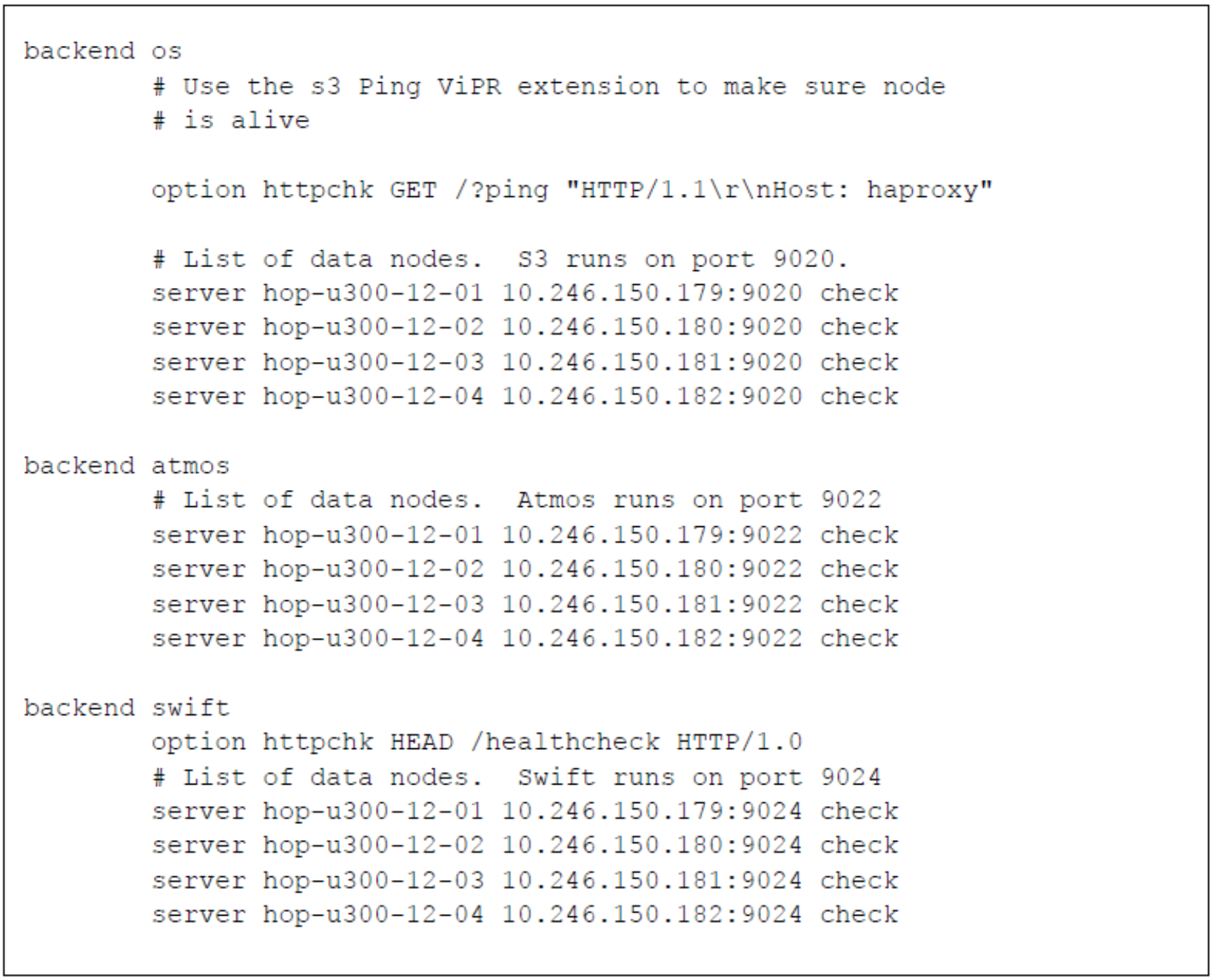
Figure 53. Example of backend definitions using map
This example provides a more manageable solution especially if the HAProxy server is forwarding different types of requests to numerous backend servers. Thus, a single frontend rule is able to handle other types of requests by adding another entry in the host2backend.map file which defines the host header to match and the name of backend handler in the configuration file.
