Home > Storage > ObjectScale and ECS > Product Documentation > ECS IAM Introduction > Request Authorization
Request Authorization
-
ECS IAM protects the following resources using the Policy Enforcement Module (PEM):
- Object Head API
- S3 (buckets and objects)
- STS API
- AssumeRole (provides temporary credentials for cross account access)
- AssumeRoleWithSAML (provides temporary credentials for SAML authenticated users)
- Management API
- IAM API
Request authorization for an S3 bucket operation
For bucket or bucket sub-resource operation requests, the system evaluates permission in user (user policy or resource-level policy), bucket context (bucket policy or ACL), and authorization process, as shown in the following figure.
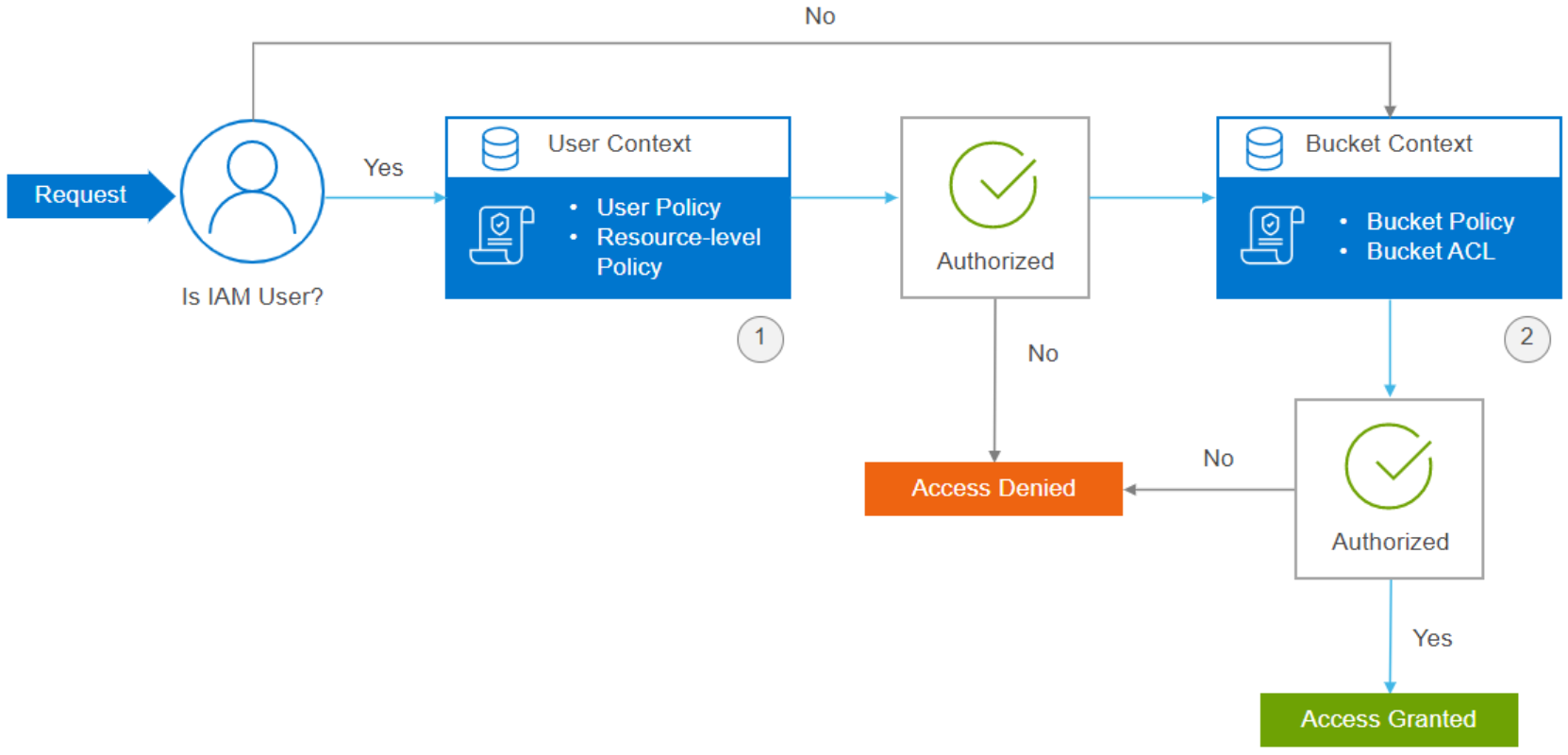
Figure 5. Request authorization for an S3 bucket
- User context: When there is a request from the IAM user, the system evaluates a subset of policies (bucket permissions in user policy) owned by the parent account (namespace admin). This subset of policies includes the user policy that the parent account attaches to the user.
- Bucket context: The system evaluates policies owned by the namespace admin account who owns the bucket. The bucket owner can grant permission by using a bucket policy or bucket ACL. The requester must have permissions from the bucket owner to perform a specific bucket operation.
Bucket owner (account)
Requestor
Bucket owner (account)
U1
The user or the bucket policy determines the access. There is no bucket ACL check.
A1
U2
U2 needs IAM policy from A2. If A1 bucket policy does not make a determination, then the system checks the bucket ACL.
A1
R1
IAM policy is not relevant for root user (R1). If A1 bucket policy does not make a determination, then the system checks the bucket ACL.
A1
R2
IAM policy is not relevant for root user (R2). If A1 bucket policy does not make a determination, then the system checks the bucket ACL.
Key: A1 = first account, A2 = second account, U1 = user from the first account, U2 = user from the second account, R1 = root user from the first account, and R2 = root user from the second account.
The default bucket ACL within an account for a bucket is accessed. The default bucket ACL across accounts for a bucket is not set. It will be denied if you do not set any ACL in the bucket.
Request authorization for an S3 object operation
For object operation requests, the system evaluates permission in user, bucket, and object context. The following figure shows the authorization process.
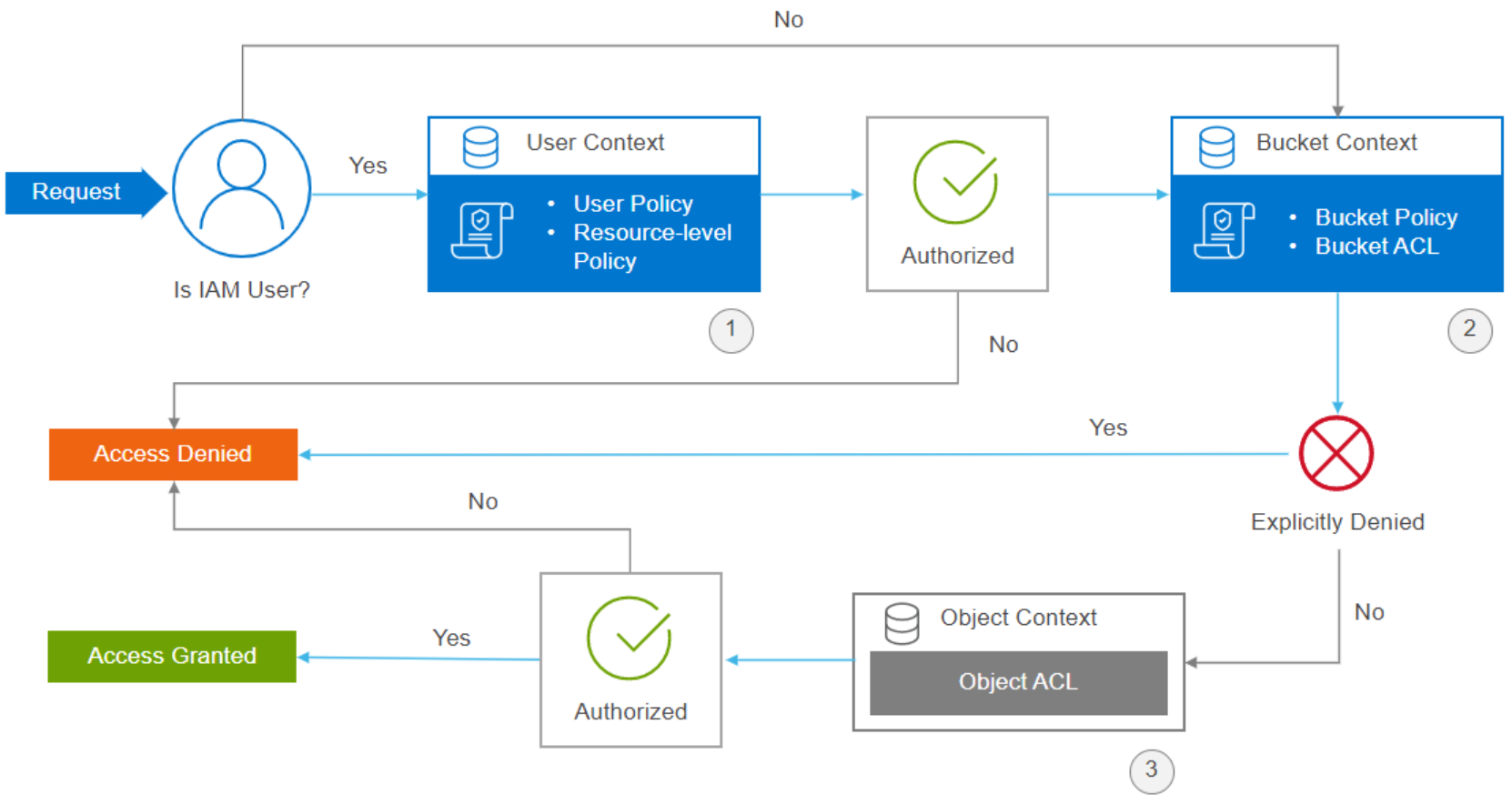
Figure 6. Request authorization for S3 object
- User context: When there is a request from the IAM user, the system evaluates a subset of policies owned by the parent account (namespace admin). This subset of policies includes the user policy that the parent account attaches to the user.
- Bucket context: System evaluates bucket policies. If the account (namespace admin) that owns the object in the request is not same as the bucket owner, in the bucket context, the system checks the policies if the bucket owner has explicitly denied access to the object. If there is an explicit deny set on the object, the system will reject request directly.
- Object context: If the bucket policy evaluation result is ALLOWED, object ACL could be skipped. If the bucket policy evaluation result is unknown, the system continues to evaluate the object ACL. The requester must have permissions from the object owner to perform a specific object operation.
Bucket owner (account)
Object owner (account)
Requestor (account, user)
Comments
A1
U1
Access determined by user/bucket policy. No object ACL check.
A1
A1
U2
U2 needs IAM policy. If A1 bucket policy does not make a determination, then object ACL check.
A1
R1
IAM policy not relevant. If A1 bucket policy does not make a determination, then object ACL check.
A1
A1
R2
IAM policy not relevant. If A1 bucket policy does not make a determination, then object ACL check
A1
A2
U1
U1 needs IAM policy or bucket policy allow. Object ACL needs to allow A1 access.
A1
A2
U2
U2 needs IAM policy allow. Bucket policy should not be denied (it cannot allow).
A1
A2
U3
U3 needs IAM policy allow. Bucket policy should not be denied (it cannot allow). Object ACL needs to allow A3 access.
A1
A2
R1
IAM policy not relevant. Bucket policy should not be denied (it cannot allow). Object ACL needs to allow A1 access.
A1
A2
R2
IAM policy not relevant. Bucket policy should not be denied (it cannot allow). Object ACL needs to allow A2 access.
A1
A2
R3
IAM policy not relevant. Bucket policy should not be denied (it cannot allow). Object ACL need to allow A3 access.
Key: A1 = first account, A2 = second account, A3 = third account, U1 = user from the first account, U2 = user from the second account, U3 = user from the third account, R1 = root user from the first account, R2 = root user from the second account, R3 = root user from the third account.
