Home > Storage > ObjectScale and ECS > Product Documentation > ECS IAM Introduction > IAM Overview
IAM Overview
-
Identity Access Management (IAM) is a web service that performs identification, authorization, and authentication to ECS resources for an IAM element. The goal of IAM is to assess if a given user or device has the right to access data within an ECS bucket. ECS IAM validates credentials/signatures for each transaction performed. It sits in the data path as part of authv2 or authv4 signature requirements.
IAM allows ECS to enforce high levels of granular permissions implemented as policies within a tenancy, allowing cross-tenancy access of buckets with roles and integration points for external identity managers, such as Microsoft Active Directory. IAM allows our enterprise customers to integrate ECS into their existing identity and access practice, and to maintain corporate security standards. Connecting ECS to external identity managers requires a process called federation. Federation is facilitated by the SAML protocol, which establishes a two-way trust between ECS and the external identity manager.
For customers who do not require such complex integration, IAM enhances their security posture and protects their data from modern threats through authorization and authentication. IAM provides password management that meets password best practices, such as minimum character lengths and complex passwords. IT administrators can use IAM-granted access rights based on user roles, which reduces the chances of granting authorized access rights to users who should not have them.
ECS IAM owns a dedicated database instance. This ECS IAM instance supports multiple-tenancy and allows each tenant owner to create their users, policies, and roles. These IAM elements are unique to that tenancy and cannot be shared across neighboring tenancies. IAM allows, if required, multiple tenancies within ECS to share resources. This can be achieved by using IAM roles. Roles are special IAM elements that accept users authenticating from alternate identity providers like Active Directory or across ECS tenancies. The role allows the external identity manager to identify and authorize the user, so that ECS IAM can authenticate the user against an attached policy.
ECS IAM conforms to the AWS S3 standard and accepts the common identification method of AccessKey and SecretKey. Thus, ECS IAM provides IAM users the ability to generate S3-specific AccessKey and SecretKey type credentials, as defined by AWS S3. The IAM authentication process is secured and facilitated by the AWS Signature v2 or v4.
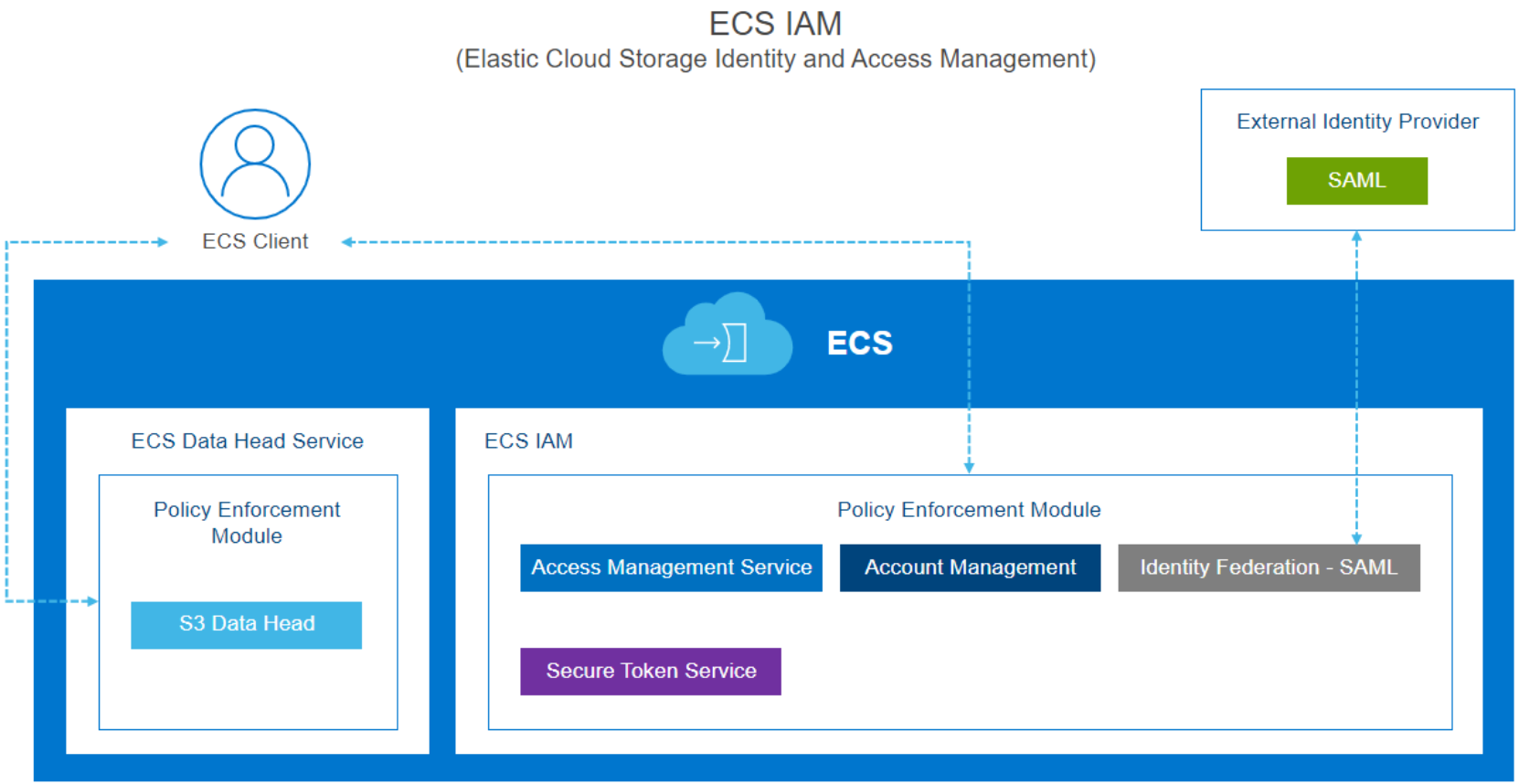
Figure 1. IAM architecture
IAM consists of the following components:
- Account management (managing identities—users, groups, and roles—and tagging IAM entities)
- Access Management Service (policies, permissions, and ACLs)
- Secure Token Service (temporary credentials)
