Home > Storage > ObjectScale and ECS > Product Documentation > ECS Cyber Protection Suite Reference Architecture > Ransomware lifecycle
Ransomware lifecycle
-
A ransomware attack starts with an infection and ultimately leads to extorting capital from an organization, based on the value of the business operations or the data. The following figure summarizes the four stages in the ransomware lifecycle.
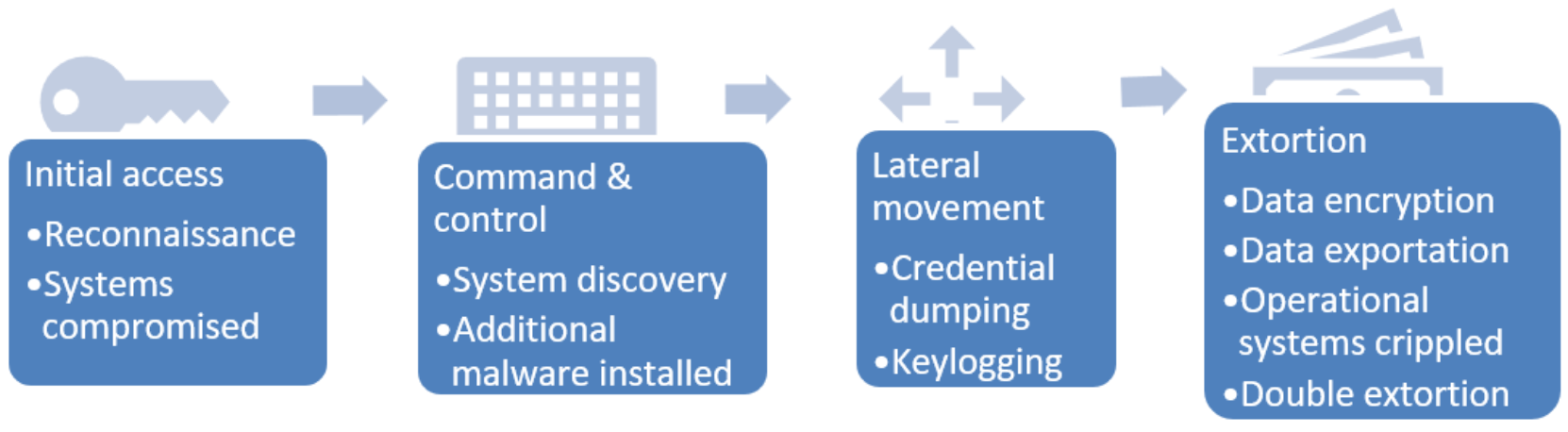
Figure 2. Ransomware lifecycle
During the Initial Access phase, the malicious parties gather information about the target network. The malicious parties look to exploit known vulnerabilities in software or devices on the target network. After a single system is compromised, the door is now open to spread the malware and begin the next phase.
In the Command & Control phase, the malicious party looks to collect detailed information about the target’s network. The process includes understanding what data is valuable for the organization and what systems have the greatest dependencies. When the target systems are characterized, the malicious parties adapt the attack accordingly. Additional malware can be installed at this point.
After the target system’s most valuable data and operations are identified, the next step is to thwart any potential system recovery. Gaining access to the most valuable data and systems requires credential access. The process of gaining access to these systems may be through credential dumping and keylogging.
The final phase is exfiltration and encryption of the organization’s data. During this phase, any valuable data is encrypted and/or exported. If the ransomware party determines that the choke point of the target organization is daily operations, the operational systems are crippled. After the most valuable points are compromised, the ransomware party begins the demand process, as shown in the following figure. In modern ransomware attacks, malicious parties use double extortion, by not only encrypting data, but also by retaining a copy of the data offsite. The offsite data can be sold to the highest bidder or simply dumped online to damage the company’s reputation.
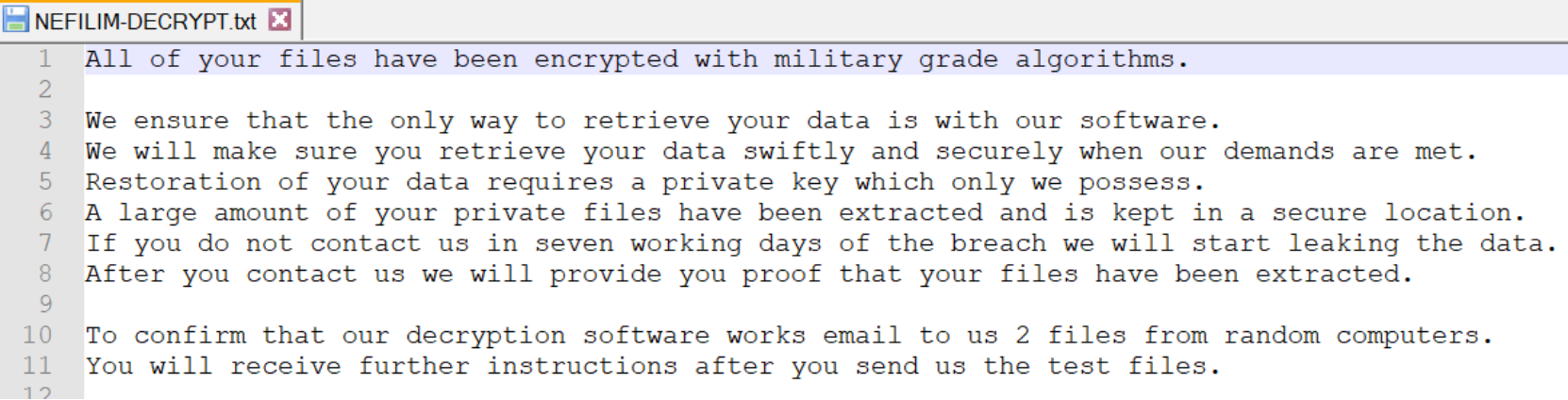
Figure 3. Example ransomware note
