Home > Storage > ObjectScale and ECS > Product Documentation > ECS Cyber Protection Suite Reference Architecture > ECS Cyber Protection Suite
ECS Cyber Protection Suite
-
Dell ECS offers a Cyber Protection Suite of advanced software to protect data throughout its lifecycle, as shown in the following figure. Considering the ransomware lifecycle, ECS’s software suite ensures cyber protection at each phase, while also planning for a potential ransomware attack. Administrators can select the data that is paramount for business continuity in the event of a ransomware attack. The ECS Cyber Protection Suite aligns with the cybersecurity framework defined by the National Institute of Standards and Technology (nist.gov).
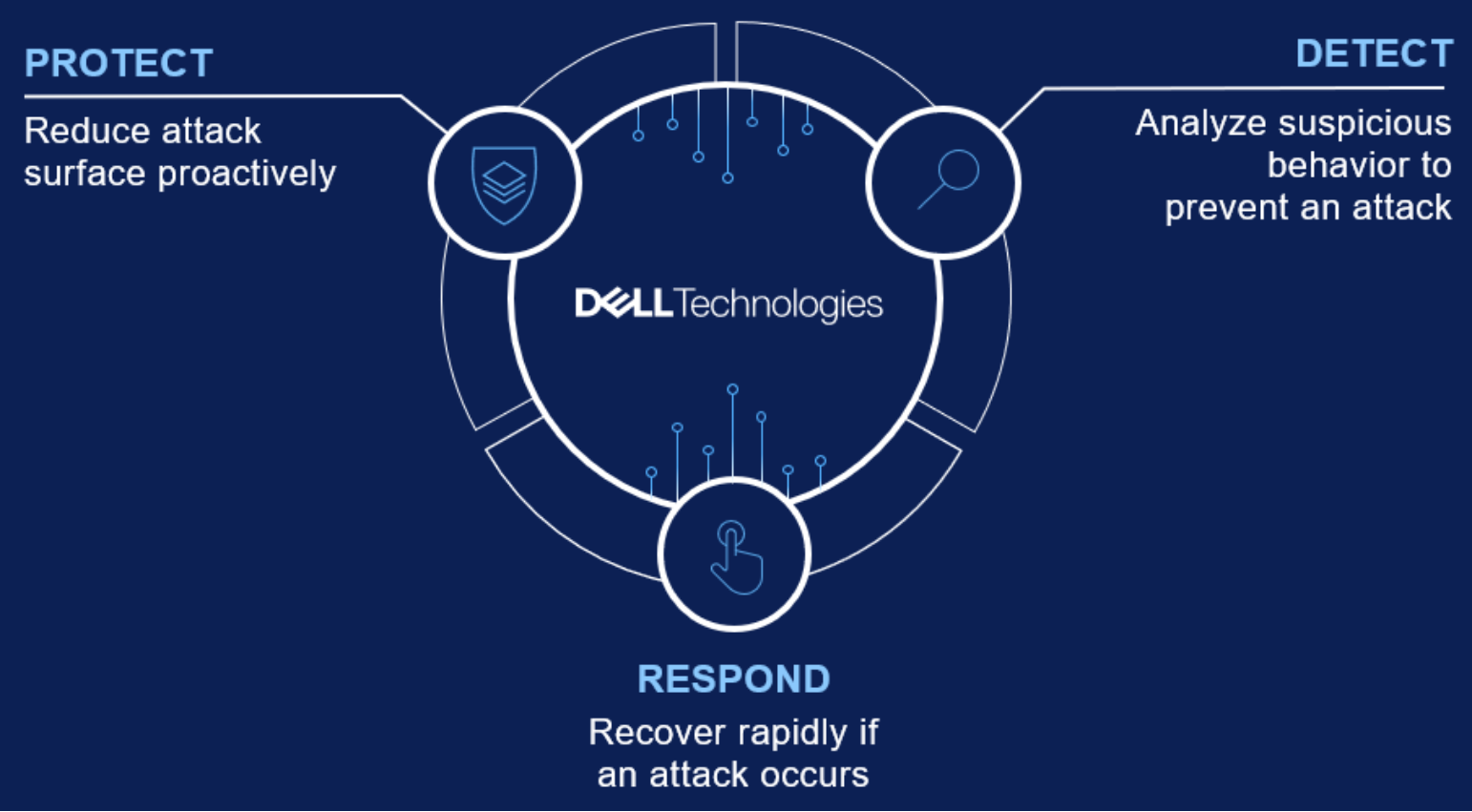
Figure 4. ECS Cyber Protection Suite
The three core pillars of the ECS Cyber Protection Suite are based on Protect, Detect, and Respond:
- The Protect pillar reduces the attack surface proactively with built-in capabilities and automated environment hardening at the data storage layer.
- The Detect pillar analyzes suspicious behavior to prevent an attack from occurring and shares threat intelligence across the enterprise cybersecurity solution stack.
- The Respond pillar plans for the worst-case scenario, where a ransomware attack takes place, by providing the tools to respond and recover from an attack.
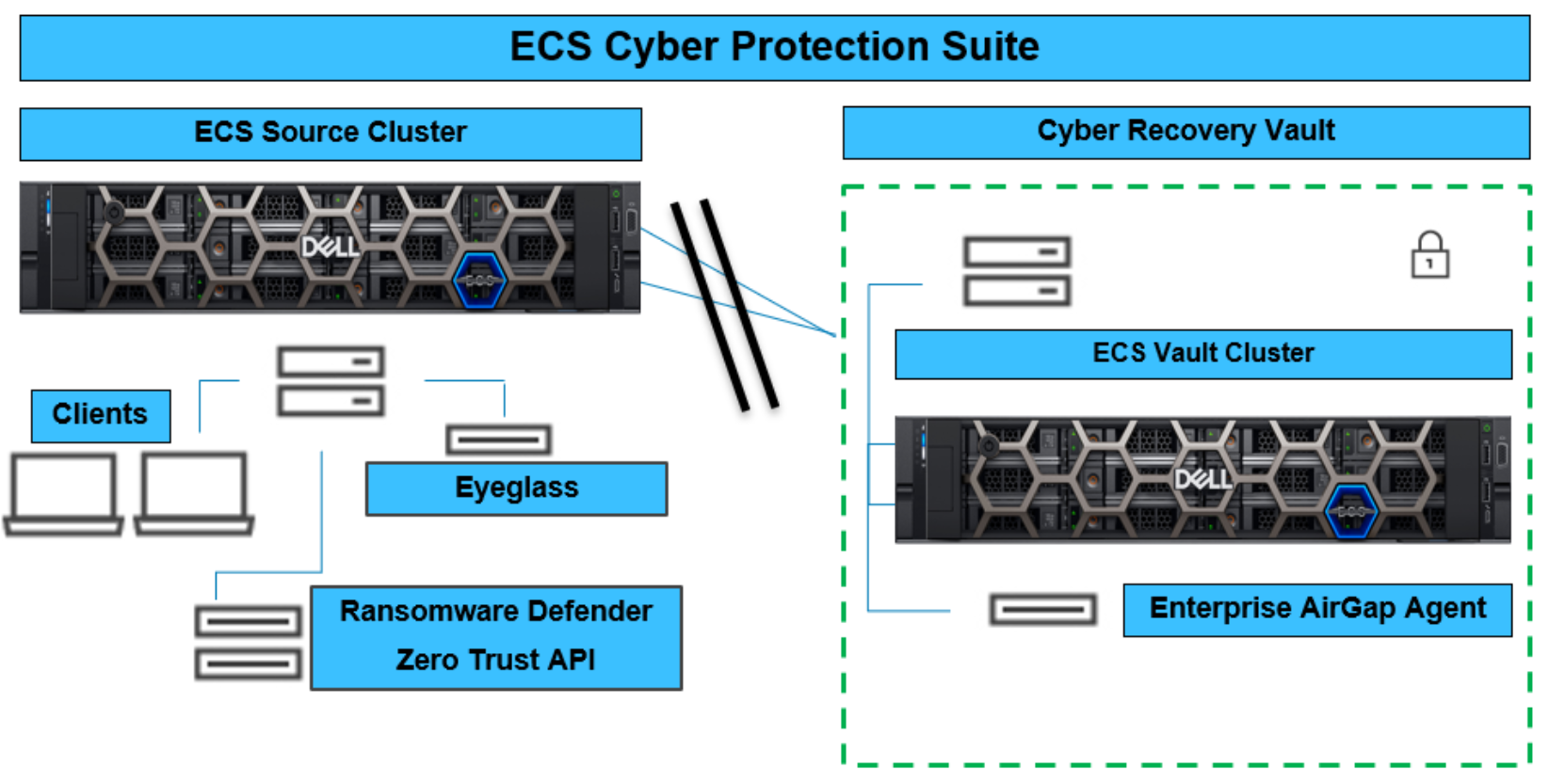
Figure 5. ECS Cyber Protection Suite
The ECS Cyber Protection Suite consists of modules that each perform a specific security function. When combined, the modules form a suite of advanced software to protect unstructured data from cyber threats.
Table 2. ECS Cyber Protection Suite
ECS Cyber Protection Suite
Eyeglass
Management control plane for the Cyber Protection Suite
Ransomware Defender
Real-time user behavior detection to detect and halt a ransomware attack through user lockouts and provide a recovery option at the object level (requires bucket versioning to be enabled)
Zero Trust API
Enables Extended Detection and Response (XDR) and Security Information and Event Management (SIEM) telemetry sharing and collection across the data center.
Enterprise Airgap Agent
Manages replication of an offline business continuity dataset in an automated cyber vault
