Home > Storage > ObjectScale and ECS > Product Documentation > ECS Cyber Protection Suite Reference Architecture > Cyberattacks
Cyberattacks
-
Malicious parties use cyberattacks to gain unauthorized access to corporate networks, with a common goal of total control over an organization’s data. From a corporate view, data can be protected through traditional Disaster Recovery (DR) measures, allowing business continuity in the event of a disaster. DR measures focus on the administrative Recovery Point Objective (RPO) and Recovery Time Objective (RTO) requirements for the specified datasets. However, the concepts of DR differ from cyber protection, in that cyber protection focuses on data fidelity to address the malicious use of an organization’s data.
Cyberattacks include malware, phishing, and ransomware:
- Phishing is a scam attempt, where users are convinced to provide credentials or personal details through various campaigns.
- Malware is a type of software allowing malicious parties unfettered access to IT systems for data theft and service disruptions.
- Ransomware is a form of malware that encrypts data and allows the malicious parties to exfiltrate sensitive data, rendering files and dependent systems unusable and held captive until a ransom is fulfilled.
Ransomware
Ransomware is the largest cyber threat to organizations. Ransomware completely cripples an organization’s ability to function. All necessary data is encrypted or exfiltrated, and the various systems that depend on the data to function are rendered useless. The organization is no longer able to function as a business. At this point, the malicious party makes a ransom request. If the request is not fulfilled in the specified period, the data is either permanently deleted, dumped online, or is sold to the highest bidder.
Given ransomware’s ability to completely debilitate a business’s primary function, the damage from a typical ransomware attack is often very costly. Ransomware can also cause businesses to lose access to important data through encryption and exfiltration, leading to further financial losses. It is important for organizations to prepare for and mitigate the risks associated with ransomware attacks. Ransomware has become extremely prevalent with constant attacks, as shown in the following figure that maps ransomware attacks in the United States since 2018.
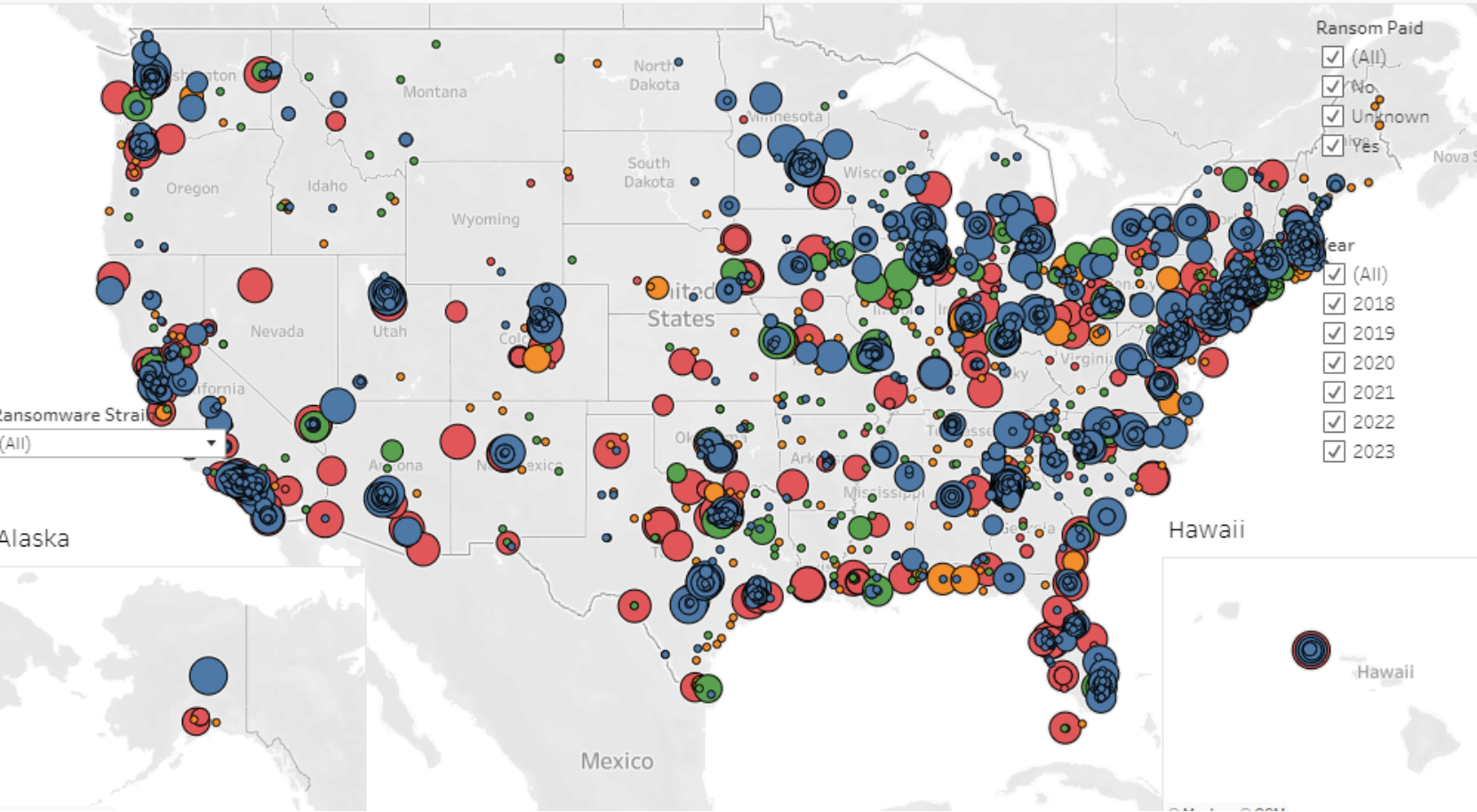
Figure 1. Heat map of US ransomware attacks since 2018
(Credit: https://www.comparitech.com/ransomware-attack-map)
Top ransomware attacks by payout
A ransom is not always paid out by organizations and there is not always a guarantee that data will be decrypted. In some cases, even after the ransom is paid, the data is not decrypted, or the decrypting key does not work as promised. The decrypting key may not work at all, or it may only work for certain file types. Malicious parties target larger organizations that depend on extensive operations, allowing the ransomware to have the greatest impact on the critical functioning of the company. The largest ransomware payouts, as of April 2023, are listed in the following table.
Table 1. Largest ransomware payouts
Company
Payout
Source
CNA Financial
$40 million
CNA Financial Paid Hackers $40 Million in Ransom After Cyberattack (businessinsider.com)
JBS
$11 million
JBS: Cyber-attack hits world's largest meat supplier - BBC News
Colonial Pipeline
$5 million
Colonial Pipeline reportedly paid $5M to hackers after ransomware attack - CNET
CWT Global
$4.5 million
'Payment sent' - travel giant CWT pays $4.5 million ransom to cyber criminals | Reuters
Brenntag
$4.4 million
Chemical distributor pays $4.4 million to DarkSide ransomware (bleepingcomputer.com)
Ransomware evolution
The impacts of ransomware vary, based on the type of ransomware and the attack vectors. Ransomware has gained significant notoriety recently, as it has evolved with modern attack vectors.
Recent forms of ransomware are developed using a subscription model for Ransomware as a Service (RaaS). The ransomware developers allow attackers to use the RaaS tools that are ready to deploy, and the developers get a percentage of the ransom payout. The general availability of these ready to deploy tools creates an environment with more widespread attacks and new vectors. Each attacker uses a unique vector, creating more attack variations.
Given the RaaS model, malicious parties now have access to ransomware that is already tested and ready to deploy. The attacker is now decoupled from the ransomware developer, multiplying the number of attackers. Each attacker provides a novel approach to infecting clients using different vectors. The increase in vectors and approaches creates a challenging cybersecurity environment for organizations.
