Home > Storage > ObjectScale and ECS > Product Documentation > ECS Cyber Protection Suite Reference Architecture > AirGap Enterprise design considerations
AirGap Enterprise design considerations
-
This section describes design considerations for AirGap Enterprise.
Network design
For the ECS Cluster in the environment, adding a firewall to the Cyber Recovery Vault is a recommended configuration. A firewall could be used in place of the switch routing between the source cluster and the vault cluster, as shown in Figure 19.
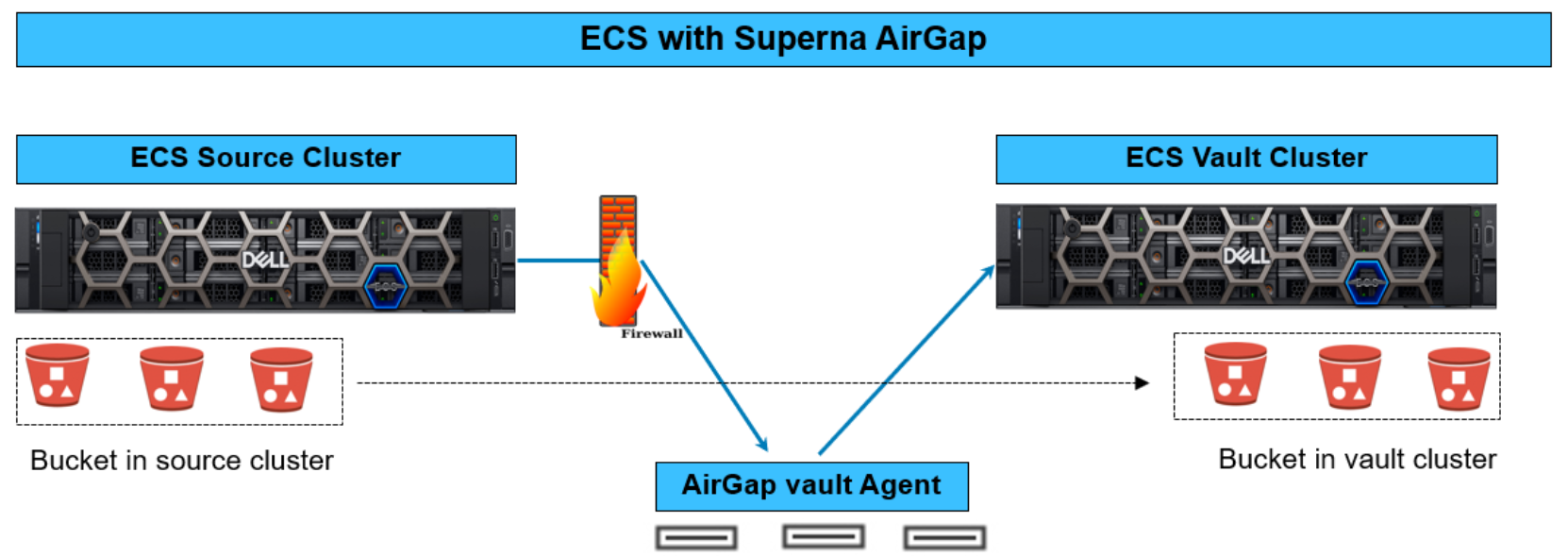
Figure 19. ECS Source Cluster to Vault Cluster topology
Depending on the switch vendor, configuration, and release, a firewall provides additional protection in most cases. The level of additional protection is difficult to gauge because each switch and firewall vendor implements different security functions. Consider how the specific switch compares with the specific firewall.
Business continuity dataset and cluster node platforms
During the design phase, consider how the business continuity dataset that is stored on the ECS Vault Cluster impacts the node quantity and platform of the source and vault cluster. The first step is identifying the business continuity dataset, because several departments must agree on what data is critical for business continuity.
When the dataset is defined, the next step is to consider how quickly the dataset is changing. Based on the frequency of dataset changes, from a business continuity perspective, organizations must consider the stale data that occurs as the dataset ages from the last update. From this data point, extract the size and frequency of the dataset changes. If the dataset has significant changes in a short time span, this will impact how quickly the dataset can be replicated from the source to the vault cluster. The dataset replication speed depends on many factors, but mainly the source and vault cluster sizes, available bandwidth, node platforms, and overall cluster resources. If the source and vault cluster are composed of a larger quantity of nodes, data replication is faster. Further, more vault agent streams should be created between the clusters, increasing replication throughput if you want to have a better performance for the source and vault cluster nodes.
Access control and management
On the source cluster, administrators should be assigned with the minimum required Role Based Access Control (RBAC). On the vault cluster, only the Chief Security Officer (CSO) or other senior security management staff should have access. For more information about configuring RBAC for ECS, see ECS Security Configuration and Hardening Guide.
Although AirGap Enterprise is part of the Ransomware Defender module, it allows for a separate user role to manage the AirGap function. Similar to the vault cluster access, it is also best practice to have the CSO or other senior security management assigned the role of managing AirGap Enterprise. The administrators managing Ransomware Defender must be separate from the staff managing the AirGap function. Ransomware Defender has a role specifically for AirGap. In the following figure, a dedicated role option is available in Ransomware Defender for AirGap.
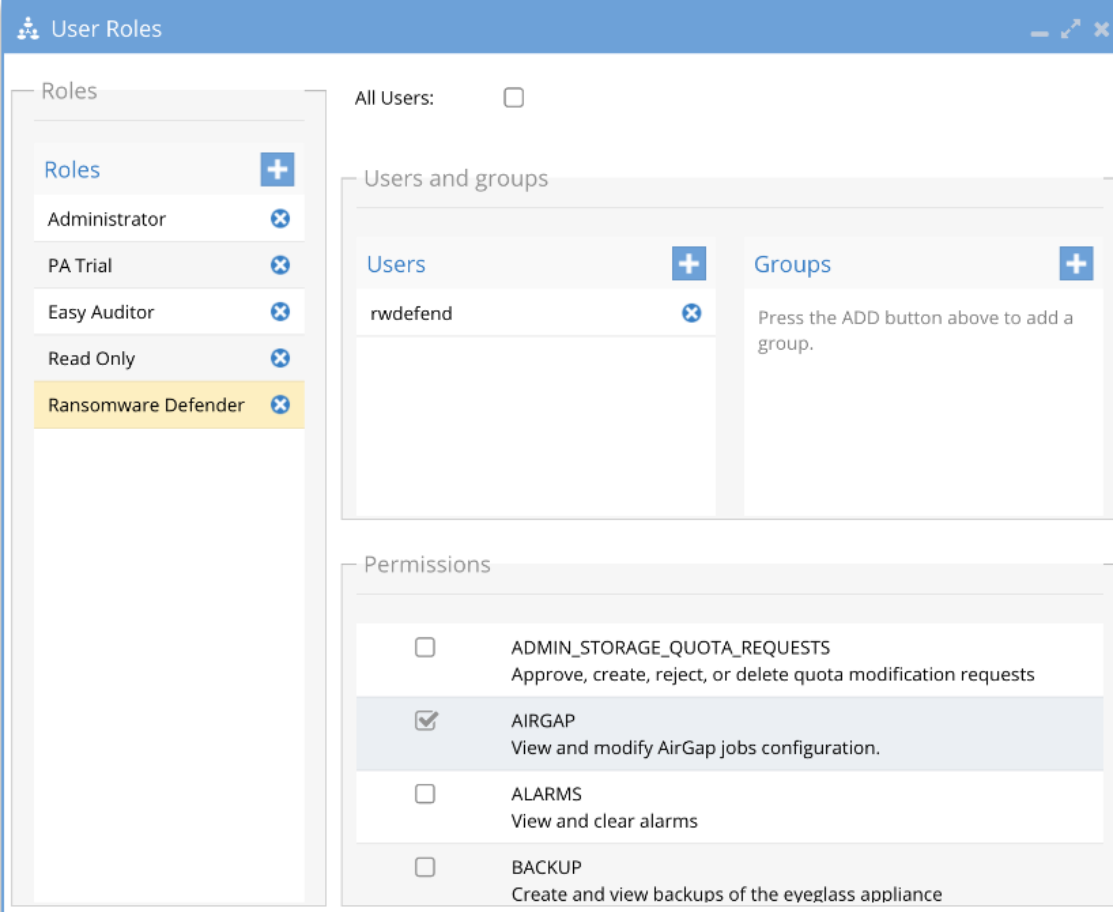
Figure 20. AirGap user role in Ransomware Defender
