Home > Workload Solutions > Container Platforms > Red Hat OpenShift Container Platform > Archive > Design Guide—Dell Ready Stack for Red Hat OpenShift Container Platform 4.3 CSI Attached Storage > Enterprise applications
Enterprise applications
-
Today’s applications are developed using cloud-native principles. These applications offer the agility, speed, and composability of microservices architecture. Enterprise deployment of these applications comes with the following additional requirements:
- Enterprises require geographically distributed deployment of container platforms as a means of “disaster avoidance”.
- Large enterprise deployments might need to cater to many internal and external partners and customers. This consideration requires multitenancy and user access roles in the container platform deployments. Security and isolation are required between microservices.
- Infrastructure requirements must meet the application needs of network connectivity, storage capacity, and compute.
Site deployment models
A key decision about multisite OpenShift Container Platform 4.3 deployment was to deploy multiple OpenShift clusters across multiple sites. Dell Technologies strongly discourages spanning a single cluster across multiple geographical sites because Kubernetes has low latency requirements. Enterprises must deploy a single cluster or multiple highly scalable large clusters in each data center. A major advantage of this model of deployment is disaster avoidance. Service can continue even when a disaster occurs at a site.
The following figure shows a multisite deployment of this solution:
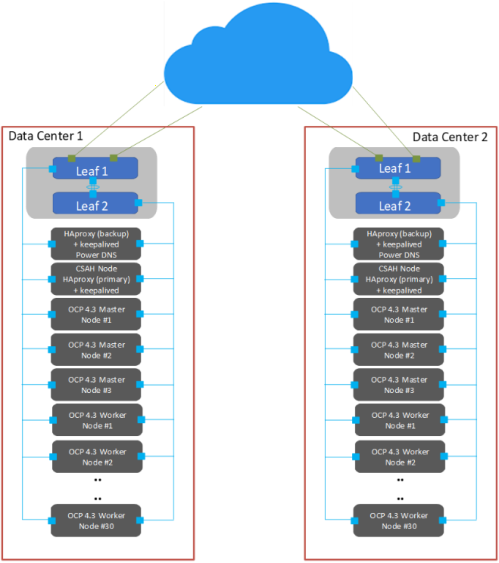
Figure 8. Multisite OpenShift Container Platform deployment
As shown in Figure 8, key technical components of the solution include:
- RedHat OpenShift Container Platform 4.3
- Load balancer: Global traffic manager (GTM) and local traffic manager (LTM)
- Data center hardware infrastructure
Role-based access control
Access control has implications for what multitenancy means throughout the infrastructure: Portal access and views, logging information, and usage information must be linked to the user role. For example:
- A provider administrator must be able to see usage and metering information for the entire infrastructure.
- A tenant administrator requires access only to the infrastructure that is assigned to that tenant.
- Tenant users require access only to assets and resources that they are permitted to manage.
Role-based access control (RBAC) in OpenShift Container Platform 4.3 can be linked to your Microsoft Active Directory identity management environment or other supported identity managers. This link gives control over user and group access to the container ecosystem infrastructure and services, providing a good foundation for multitenancy support. The following table shows the supported roles:
Table 10. Role-based access control in OpenShift Container Platform 4.3
Role
Description
Admin
Project manager
basic-user
User who can retrieve information about projects and users
cluster-admin
A superuser who can perform any action in any project
cluster-status
User who can retrieve cluster status information
Edit
User who can modify objects in a project
self-provisioner
User who can create their own projects
View
User who can see most objects in a project
cluster-reader
User who can read, but not view, objects in the cluster
Security and isolation
OpenShift Container Platform 4.3 is built on the concept that each project that runs within a cluster can be isolated from every other project. The project manager must have the administrative privilege to be able to see any other project in the cluster.
Performance monitoring and logging
Cloud service providers typically require the ability to monitor and report on system utilization. OpenShift Container Platform 4.3 includes Prometheus system monitoring and metering and provides capability for extensive data logging. For more information about obtaining cluster resource consumption to drive usage billing through third-party application software, see the following Red Hat documentation:
- About cluster monitoring
- Examples of using metering
- About cluster logging and OpenShift Container Platform
The cluster monitoring operator controls the monitoring components that are deployed. The Prometheus operator controls Prometheus and Alertmanager instances. The platform monitors the following stack components:
- Stack component
- CoreDNS
- Elasticsearch
- etcd
- Fluentd
- HAProxy
- Image registry
- Operator Lifecycle Manager (OLM)
- Telemeter client
- Kubelets
- Kubernetes apiserver
- Kubernetes controller manager
- Kubernetes scheduler
- Metering
- OpenShift apiserver
- OpenShift controller manager
