Home > Storage > ObjectScale and ECS > Product Documentation > Deploying the Elastic Stack with Searchable Snapshots and Frozen Tier > Install the S3 plugin on Elasticsearch
Install the S3 plugin on Elasticsearch
-
You must have the S3 Plugin installed on each Elasticsearch server. The commands used for this process are shown below for reference.
Note: The S3 plugin is included in Elasticsearch 8.x by default.
Reference the below link to install the S3 plugin for Elasticsearch 7.x
For earlier versions of Elasticsearch, install the S3 Plugin on each Elasticsearch node https://www.elastic.co/guide/en/elasticsearch/plugins/current/repository-s3.html.
When the S3 Plugin successfully completes and Elasticsearch services are restarted, you can use several methods to configure the S3 repository that points to ECS:
- Defined in the elasticsearch.yml file
- Created in the Snapshot and Restore section in Stack management
- Using the REST API
We chose to create the S3 repository using the Elasticsearch REST API. (Note that we used Elastic Stack version 8.1.3 in this document.)
Note: The API can be invoked using various tools such as curl or postman. You can also use the Developer Console from the Kibana UI.
Add the ECS Access and secret keys to the Elastic keystore
Most client settings can be added to the elasticsearch.yml configuration file except for secure settings, which you add to the Elasticsearch keystore. So, to keep our S3 credentials secure, we add them to the Elasticsearch keystore. The following commands prompt for the key:
./elasticsearch-keystore add s3.client.default.access_key
./elasticsearch-keystore add s3.client.default.secret_key
Note: Because keystore settings are secure and reloadable, we can add/update them without restarting the service or cluster by using the reload_secure_settings API.
Register a S3 snapshot repository
curl -X PUT "10.246.156.180:9200/_snapshot/ecs-repo" -H 'Content-Type: application/json' -d'
{
"type": "s3",
"settings": {
"bucket": "elastic-snapshots",
"base_path": "snapshots",
"endpoint": "s3.example.com",
"protocol": "https",
"path_style_access": "true"
}
}
'
Register a S3 Repository for frozen snapshots
curl -X PUT "10.246.156.180:9200/_snapshot/ecs-frozen-repo" -H 'Content-Type: application/json' -d'
{
"type": "s3",
"settings": {
"bucket": "elastic-frozendata",
"base_path": "snapshots",
"endpoint": "s3.example.com",
"protocol": "https",
"path_style_access": "true"
}
}
'
Note: if deployed in a corporate environment, there may be a need for corporate CA certificates to be added to the Elastic KeyStore for verification.
Let’s look at each of the client settings in more detail. Note that the entire list of settings can be referenced here.
- Bucket: Name of the bucket to store our snapshots.
- Base_path (optional): Path to the repository data within the bucket.
- Endpoint: ECS requires an IP Load Balancer to distribute traffic to each node in the VDC.
- Protocol: Specifies whether HTTP or HTTPS is to be used.
- Path_style_access: Specifies whether to use Path or Virtual-Host style access.
There are a few methods to verify that the S3 snapshot repository was successful created. From Kibana, navigate to Stack Management>Snapshot and Restore>Repositories.
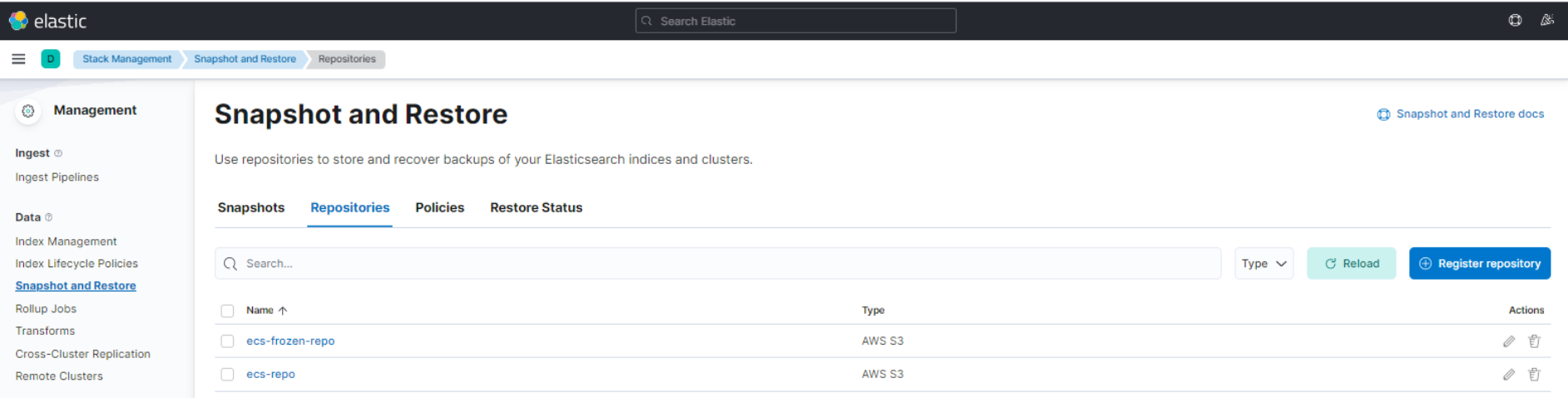
Figure 6. List the Snapshot Repositories
Or by using the Get snapshot API using curl or the developer console.
[root@logstash ~]# curl -X GET "10.246.156.180:9200/_snapshot?pretty"
{
"ecs-repo" : {
"type" : "s3",
"uuid" : "WrFYcF-tQQWW7fHJ61rP7A",
"settings" : {
"bucket" : "elastic-snapshots",
"path_style_access" : "true",
"base_path" : "snapshots",
"endpoint" : "s3.example.com",
"protocol" : "http"
}
},
"ecs-frozen-repo" : {
"type" : "s3",
"uuid" : "FH6JTt8qQHqcf174nxaICg",
"settings" : {
"bucket" : "elastic-frozendata",
"path_style_access" : "true",
"base_path" : "snapshots",
"endpoint" : "s3.example.com",
"protocol" : "http"
}
}
}
