Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Dell PowerScale OneFS: Security Considerations > Protect cardholder data
None
-
The second pair of requirements focuses on protecting cardholder data when it is stored and throughout the transmission.
Requirement 3: Protect stored account data
Account data is protected by using encryption, truncation, hashing, and masking. The goal of these requirements ensures that if unauthorized access to cardholder data takes place, the data is of no use and not readable without the proper cryptographic keys.
Requirement 3.5.1 specifies that the cardholder Primary Account Number (PAN) must be unreadable anywhere it is stored. The data is unreadable through the use of security processes, including:
- One-way hashes based on strong cryptography, (hash must be of the entire PAN)
- Truncation (hashing cannot be used to replace the truncated segment of PAN)
- Index tokens and pads (pads must be securely stored)
- Strong cryptography with associated key-management processes and procedures
The security processes must be part of the workflow ensuring only the PAN is unreadable when it is stored on PowerScale nodes, as shown in the following figure.
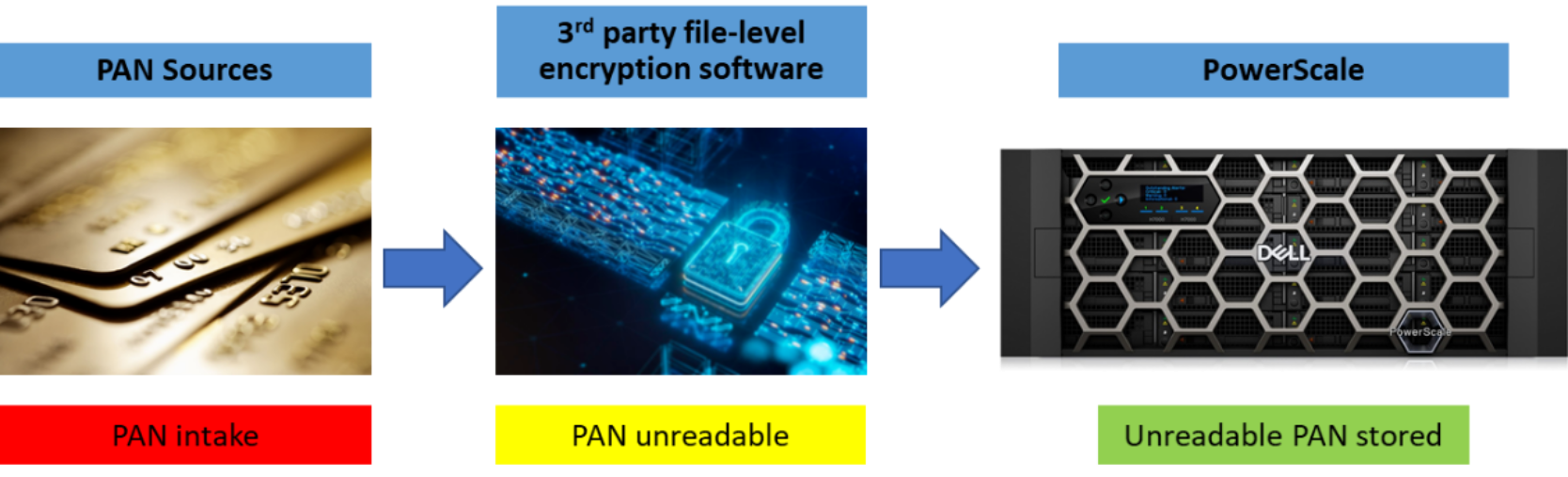
Figure 14. File-level encryption workflow
PowerScale OneFS meets the other requirements for storing cardholder data by using self-encrypting drives (SEDs), providing a solution for the security of data through Data-at-rest encryption (DARE). Data written to a SED is encrypted when it is stored. SEDs require a key each time the drive is accessed by OneFS. Further, as Requirement 3.5 states, to secure the keys of each SED, OneFS uses an encryption key management system, wrapping encryption keys with key encrypting keys, and an external key manager. For more information about SEDs and DARE, see PowerScale Data at Rest Encryption
PowerScale Data at Rest Encryption.The other requirements in this section are enforced through policies, procedures, and processes external to the PowerScale cluster.
Requirement 4: Protect cardholder data with strong cryptography during transmission over open, public networks
This requirement is specific to data transmission across open, public networks such as the Internet and cellular or satellite communication.
OneFS support encryption for SyncIQ, ensuring data replication traffic between two clusters is secure. SyncIQ encryption offers over-the-wire, end-to-end encryption for data replication, protecting and securing in-flight data. For more information about SyncIQ encryption, see the Dell PowerScale SyncIQ: Architecture, Configuration, and Considerations white paper.
NFS is encrypted using Kerberos and SMBv3 provides encryption. For more information, see the Dell PowerScale: Integrating OneFS with Kerberos Environment for Protocols and PowerScale: Solution Design and Considerations for SMB Environments white papers.
