Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Dell PowerScale OneFS: Security Considerations > External key manager
None
-
PowerScale OneFS 9.2 and later releases support an external key manager by storing the 256-bit universal key (UK) in a key management interoperability protocol (KMIP)-compliant key manager server. The configuration steps in this section apply to brownfield and greenfield clusters with SEDs. Although the configuration in this section explains how to migrate keys to an external key manager, OneFS also supports a reverse migration.
Requirements
To store the UK on a KMIP server, PowerScale requires the following:
- OneFS 9.2 (or later) cluster with SEDs
- KMIP-compliant server:
- KMIP 1.2 or later
- KMIP storage array 1.0 or later with SEDS profile
- KMIP server host/port information
- X.509 PKI for TLS mutual authentication
- Certificate authority bundle
- Client certificate and private key
- Administrator privilege: ISI_PRIV_KEY_MANAGER
- Network connectivity from each node in the cluster to the KMIP server using an interface in a statically assigned network pool; for SED drives to be unlocked, each node in the cluster contacts the KMIP server at bootup to obtain the UK from the KMIP server, or the node bootup fails
- Not All Nodes On Network (NANON) and Not all Nodes On All Networks (NANOAN) clusters are not supported
Note: When configuring the external key manager, make sure that each PowerScale node in the cluster can communicate with the KMIP server using an interface in a statically assigned network pool to unlock the drives during the node boot process. If the KMIP server is unavailable or if network connectivity is not available, the node’s drives remain in a locked state.
KMIP and PowerScale tested compatibility
PowerScale OneFS has tested and confirmed KMIP compatibility as listed in the table below.
Table 1. PowerScale OneFS tested KMIP compatibility
KMIP Vendor
OneFS Version Tested
Thales KeySecure
OneFS 9.3.0.0
Thales e-Security keyAuthority
OneFS 9.3.0.0
IBM Secure Key Lifecycle Manager (SKLM)
OneFS 9.1.0.0
CloudLink Center
OneFS 9.5.0.0
Thales CipherTrust Data Security Platform
OneFS 9.7.0.0
Note: The OneFS version tested does not imply the KMIP vendor is not compatible with a more recent OneFS release, it is provided as a data point.
Note: PowerScale OneFS uses the Dell Key Trust Platform as the client for establishing connectivity to the KMIP server. Other KMIP platforms compatible with the Dell Key Trust Platform should also be compatible with OneFS. Also, PowerScale OneFS should be compatible with KMIP platforms that meet the previously outlined requirements.
Configuration
After you meet the previous requirements, to configure the external key manager, perform the following steps:
- Create server and client certificate bundles. The bundles must be X.509 public key infrastructure (PKI) certificates. The certificate formats supported are pem or PKCS #12 format.
For the server certificate bundle, the order of the bundles begins with the server certificate and ends with the root. This order includes any intermediates in between, excluding the KMIP server certificate. Each certificate must certify the one preceding it. For example, a certificate bundle could be in the following format:
- Intermediate certificate 3
- Intermediate certificate 2
- Intermediate certificate 1
- Root certificate
The client certificate bundle consists of the X.509 certificate followed by the private key. Optionally, the private key may also be encrypted, and password protected in the client certificate bundle. If the private key is encrypted, make a note of the password for use in later steps.
- Transfer the KMIP server and client certificate bundles to the cluster. Make a note of the file names and location.
- In the OneFS web interface, select Access > Key Management as shown in the following figure. Alternatively, in the OneFS CLI, run the following command:
isi keymanager kmip servers create
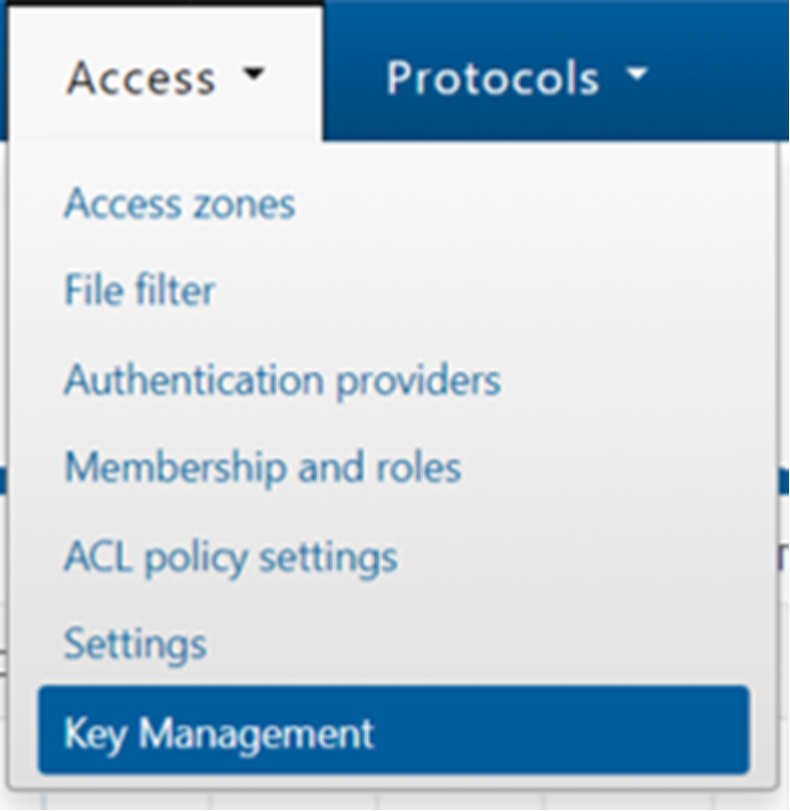
Figure 3. Key Management
- On the Key Management page, click the Key Server tab, select the Enable Key Management checkbox, and perform the following:
- Enter the KMIP Server Host and Server Port information.
- Specify the filename and location of the Server Certificate and Client Certificate bundle transferred to the cluster in step 2.
- If the client certificate bundle has an encrypted password, specify this password in the Client Certificate Password field, and click Submit, as shown in the following figure.
Alternatively, in the CLI, use the --host, --id, --ca-cert-path, --client-cert-path, and --set-client-cert-password options.
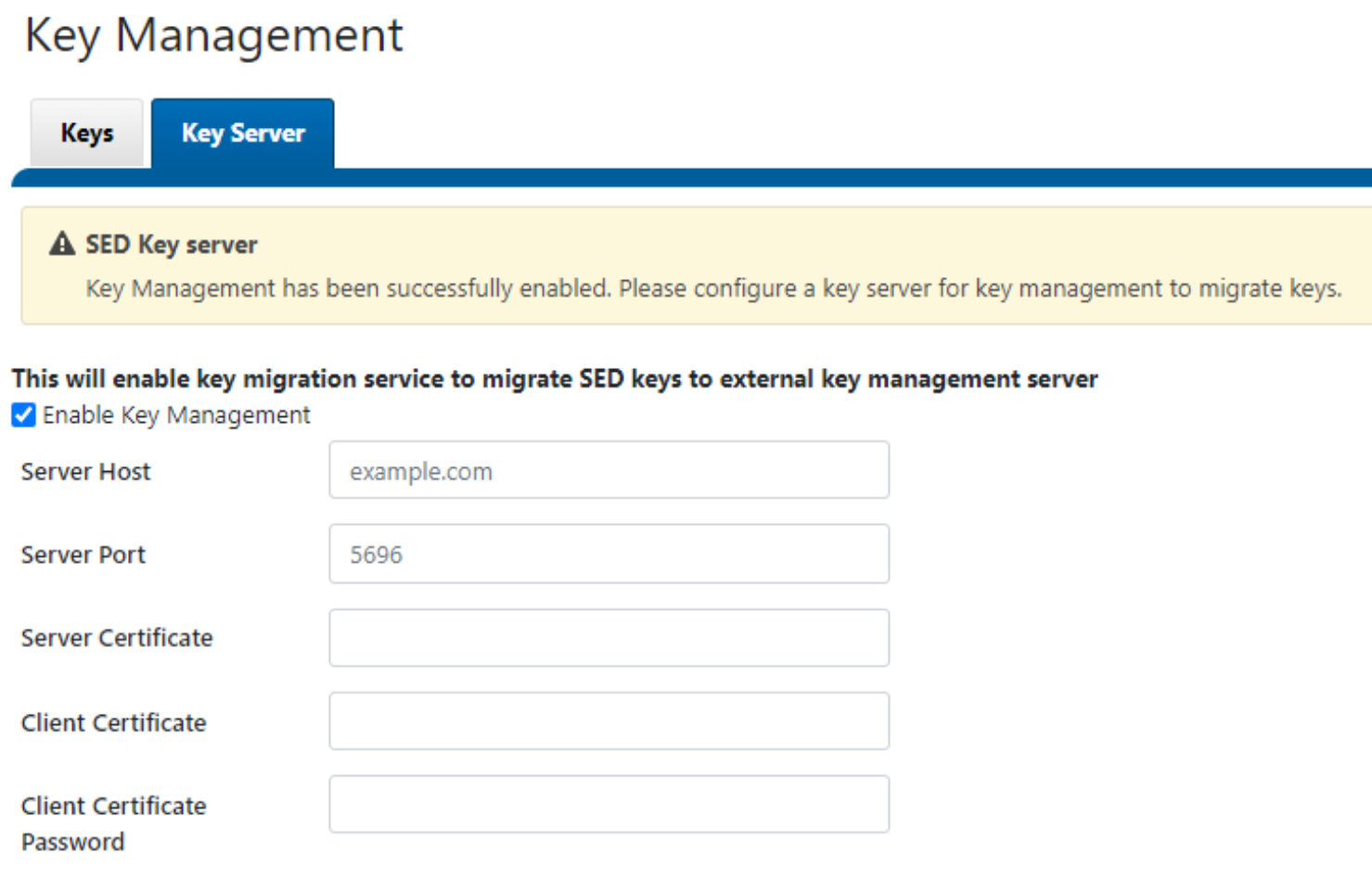
Figure 4. Key management server information
- OneFS contacts the KMIP server and confirms the connection or displays any errors, as shown in the following figure. If the connection is unsuccessful, check the certificate bundle requirements listed in step 1.
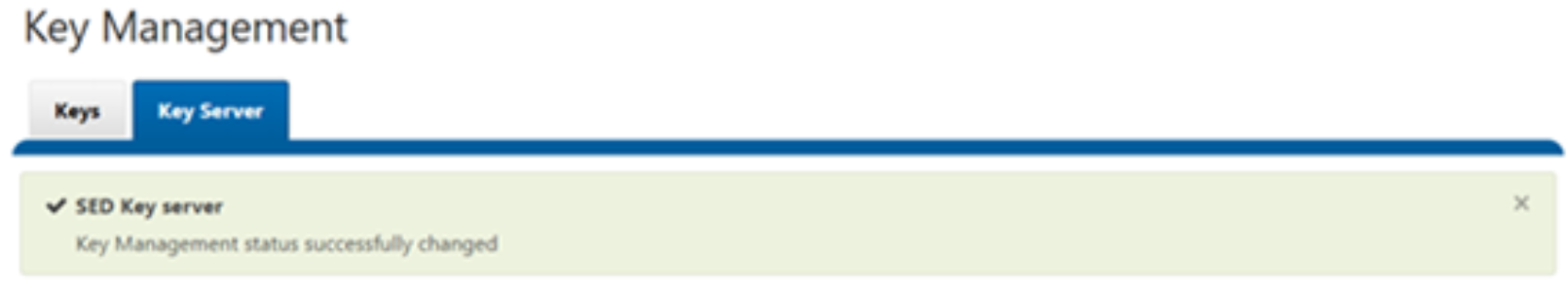
Figure 5. Key Management confirmation
- After you add the KMIP server, you can migrate the keys.
- Click the Keys tab to display all current universal keys on the cluster.
- Click Migrate all to migrate the keys to the KMIP server.
- In the Migrate all window, click Migrate to start the migration as shown in the following figure.
Alternatively, in the CLI, run the isi keymanager sed migrate server command.
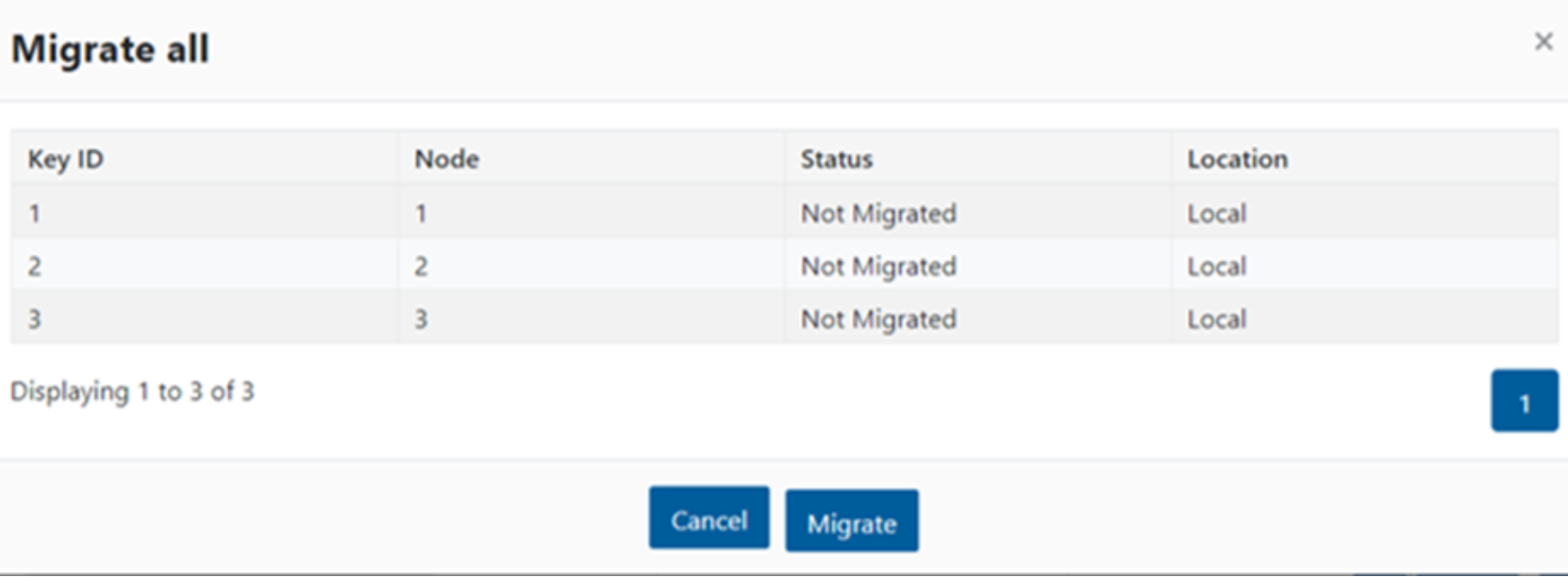
Figure 6. Universal key migration
- Depending on the cluster and network utilization, the key migration process may take several minutes or more to complete. A Migration in process message is displayed during this time, as shown in the following figure. Alternatively, in the CLI, run the isi keymanager sed status command.
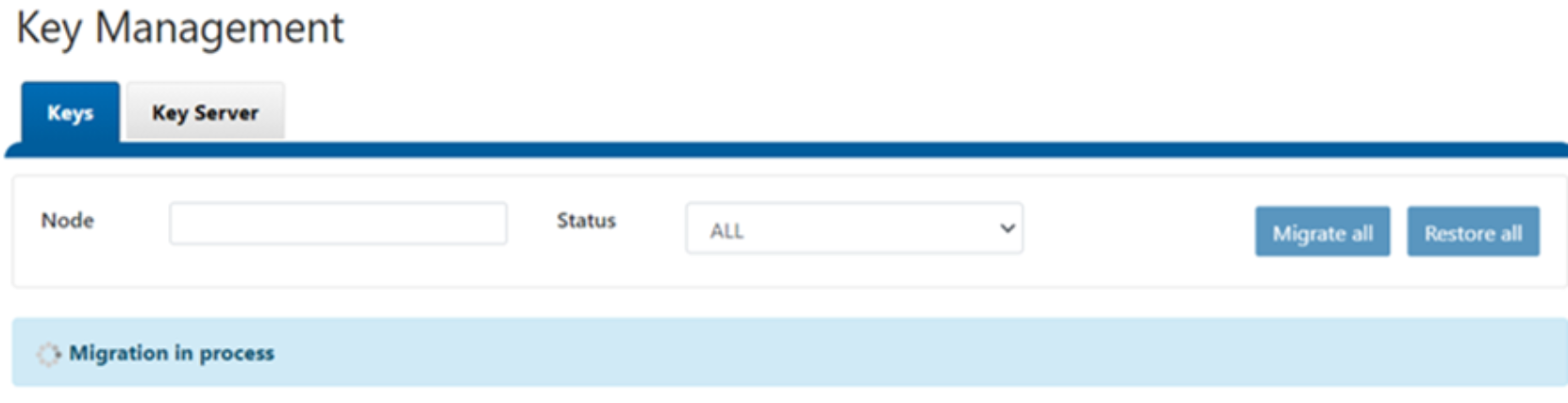
Figure 7. Migration in process
- After you complete the process, a Migration Successful message is displayed, and the Status for each Key ID is Migrated, as shown in the following figure. Alternatively, in the CLI, run the isi keymanager sed status command.
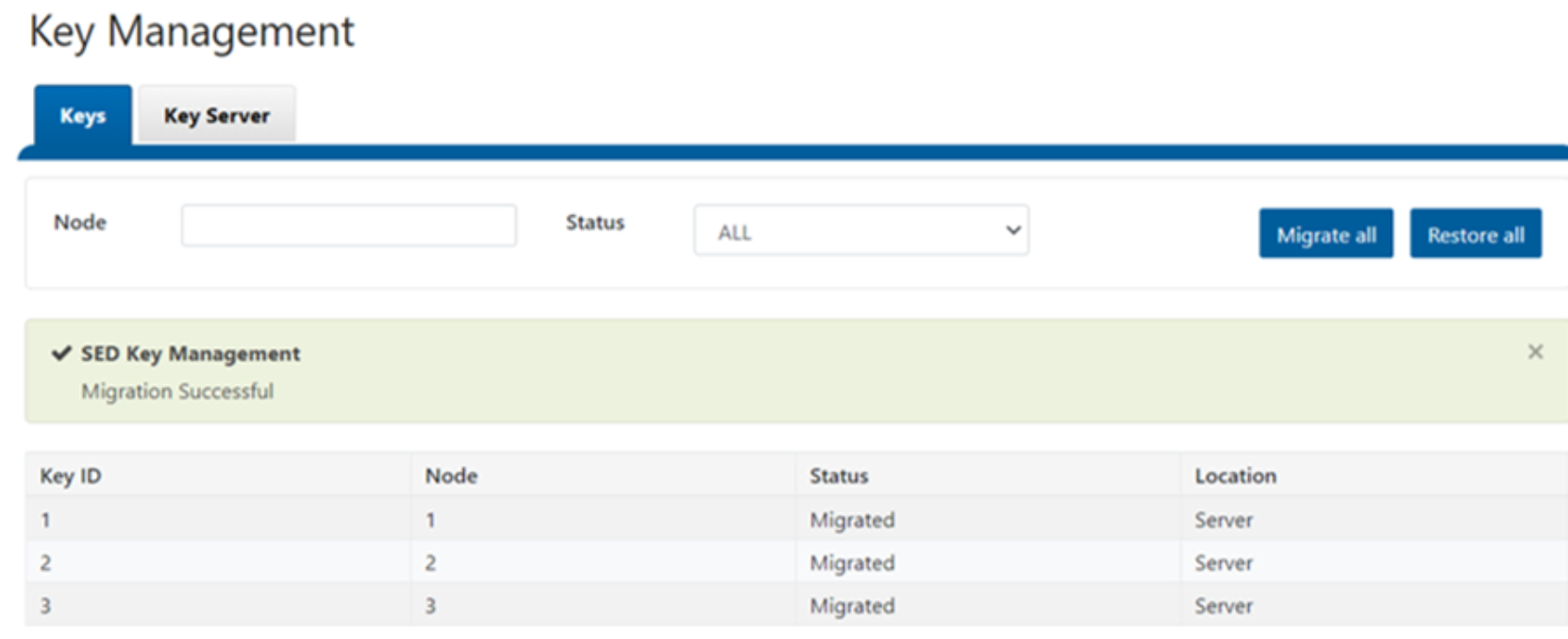
Figure 8. Migration successful
