Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Dell PowerScale OneFS: Security Considerations > Cluster services rekey
None
-
PowerScale OneFS 9.5.0.0 supports the rekey of cluster domains. For the rekey of SEDs, see PowerScale Data at Rest Encryption
PowerScale Data at Rest Encryption. This section is specific to the other cluster domains.View the available domains by running the isi keymanager cluster status command, as shown in the following figure.
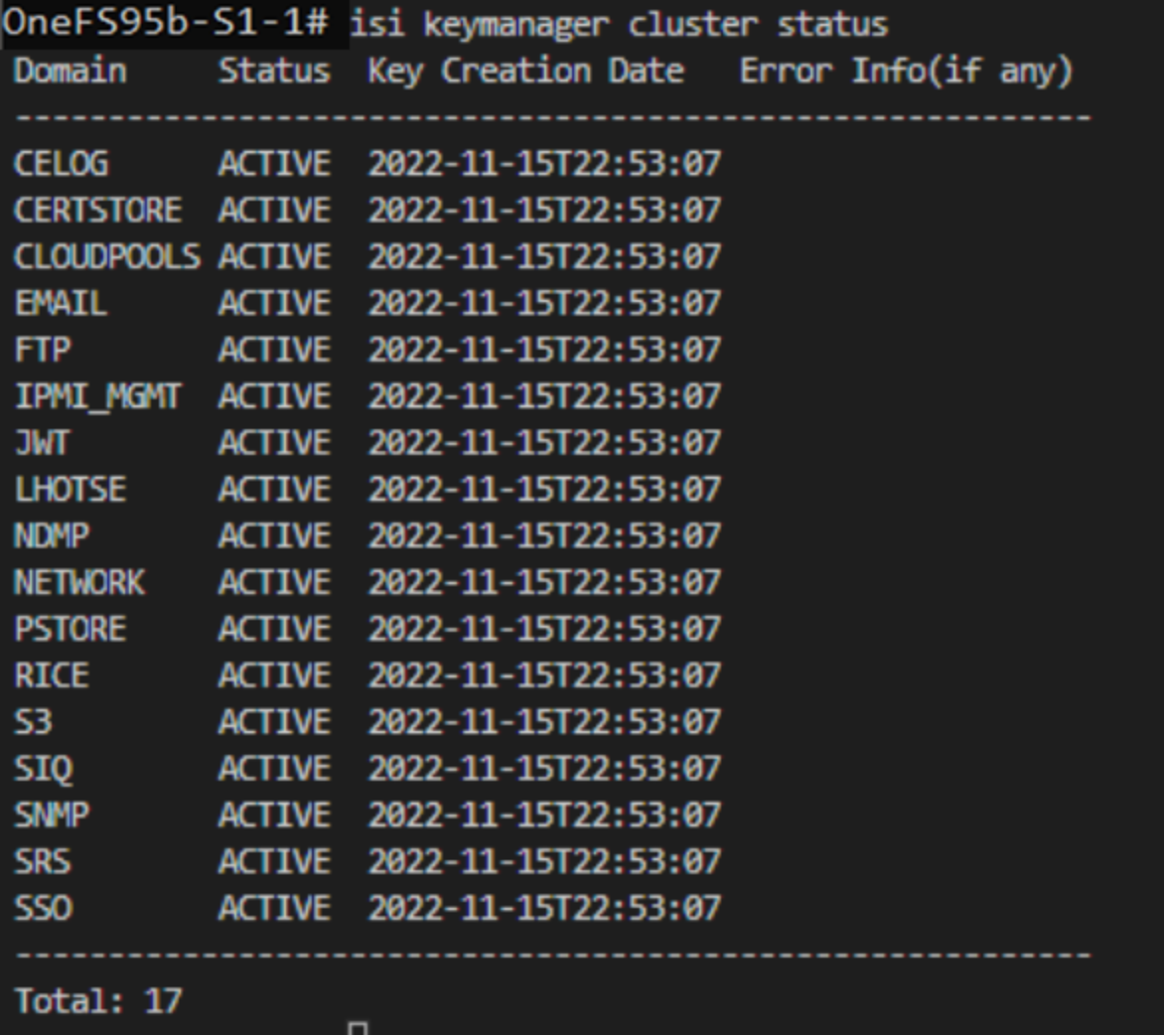
Figure 33. Key manager cluster status
The rekey process generates a new key and re-encrypts the entries for the domain. The old key is then deleted.
Considerations
The domain keys may be rekeyed on a specified schedule or as requested. Before configuring rekey, consider the following information:
- The rekey feature is only available after the OneFS 9.5.0.0 or later release is committed.
- During the rekey process, the old UK is only deleted after a successful re-encryption with the new UK. If for any reason the process fails, the old UK is available and remains as the current UK. The rekey daemon retries the rekey every 15 minutes if the process fails.
Configuration
Before starting a rekey process, ensure that you understand the preceding considerations. A rekey may be requested immediately or may be scheduled with a cadence. The rekey operation is available through the CLI and the WebUI. In the WebUI, go to Access > Key Management and select the SED/Cluster Rekey tab. This section explains the cluster rekey process; for SEDs, see PowerScale Data at Rest Encryption
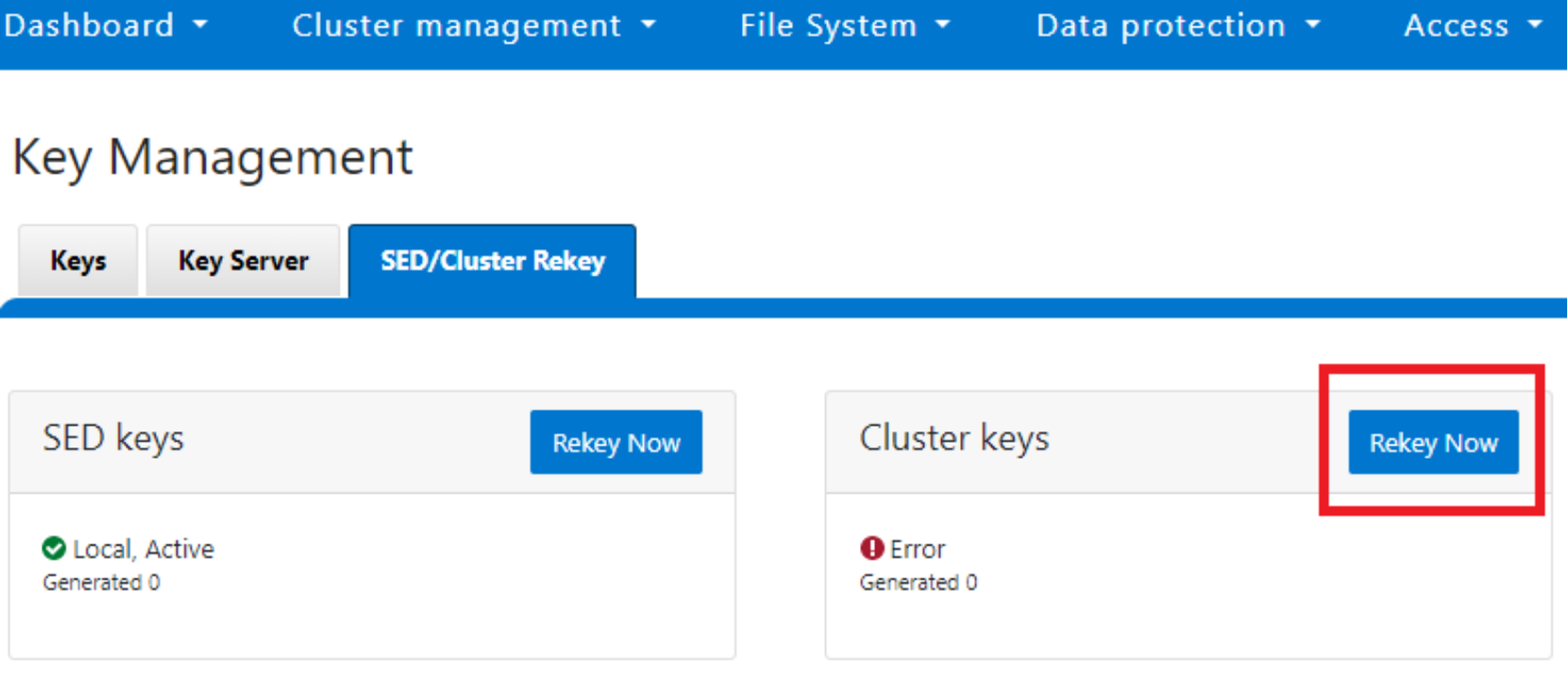
PowerScale Data at Rest Encryption.To start a rekey of the cluster domains immediately, from the CLI run the isi keymanager cluster rekey start command. Alternatively, from the WebUI, under the SED/Cluster Rekey tab, select Rekey Now, next to Cluster Keys, as shown in the following figure.
To schedule rekey of the cluster, from the CLI run the isi keymanager cluster rekey modify command with the --key rotation= option. Specify the frequency of the key rotation as an integer, sing Y for years, M for months, W for weeks, D for days, H for hours, m for minutes, and s for seconds. For example, to have the rekey operation scheduled for every 3 months, run the following command: isi keymanager cluster rekey modify --key rotation=3M.
Alternatively, from the WebUI, under the SED/Cluster Rekey tab, select the Automatic rekey for Cluster keys checkbox and specify the rekey frequency, as shown in the following figure. Then click Save.
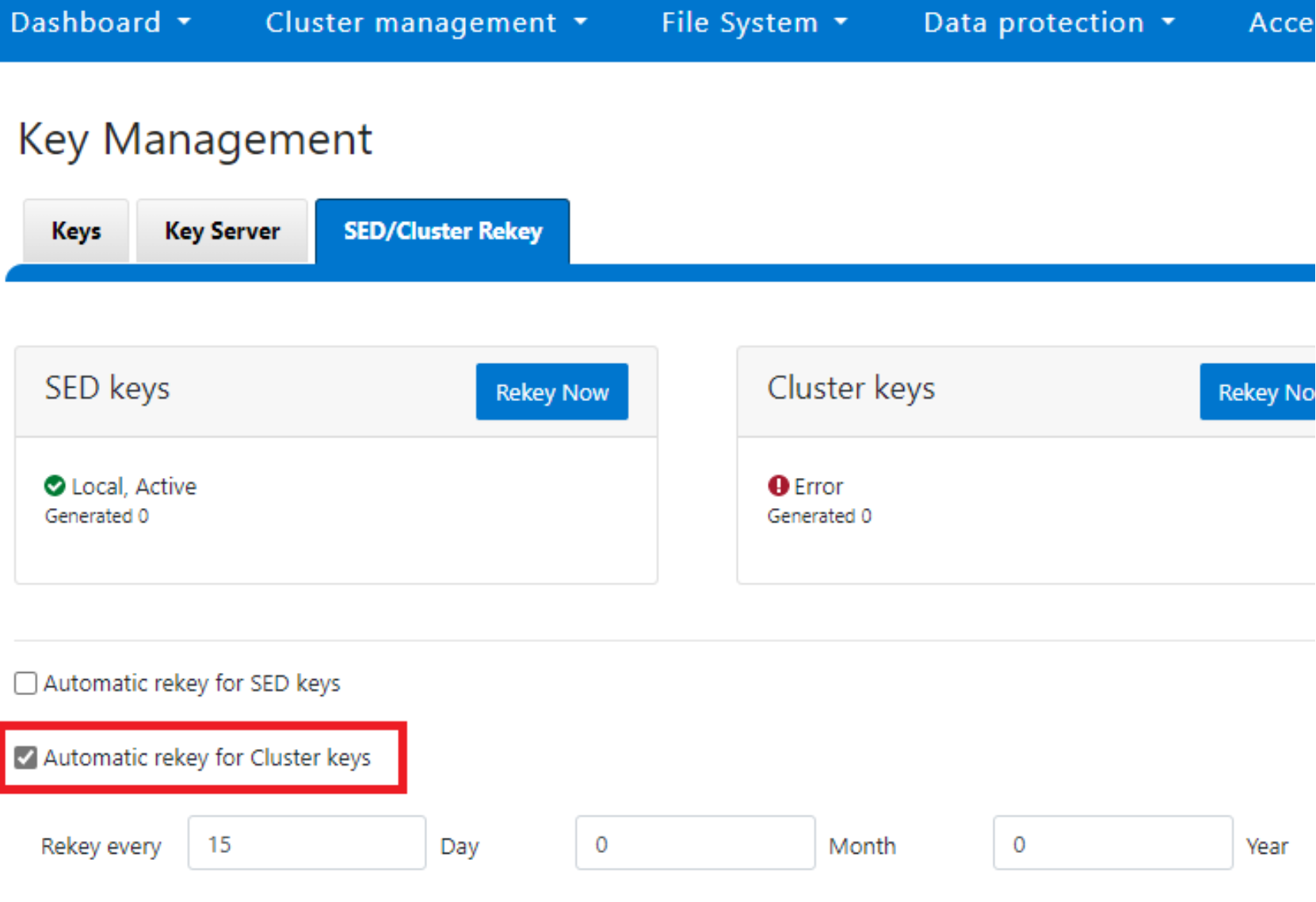
Figure 34. Automatic rekey for Cluster keys
Status and troubleshooting
To see the current rekey status in the CLI, run the isi keymanager cluster status command, as shown in the following figure.
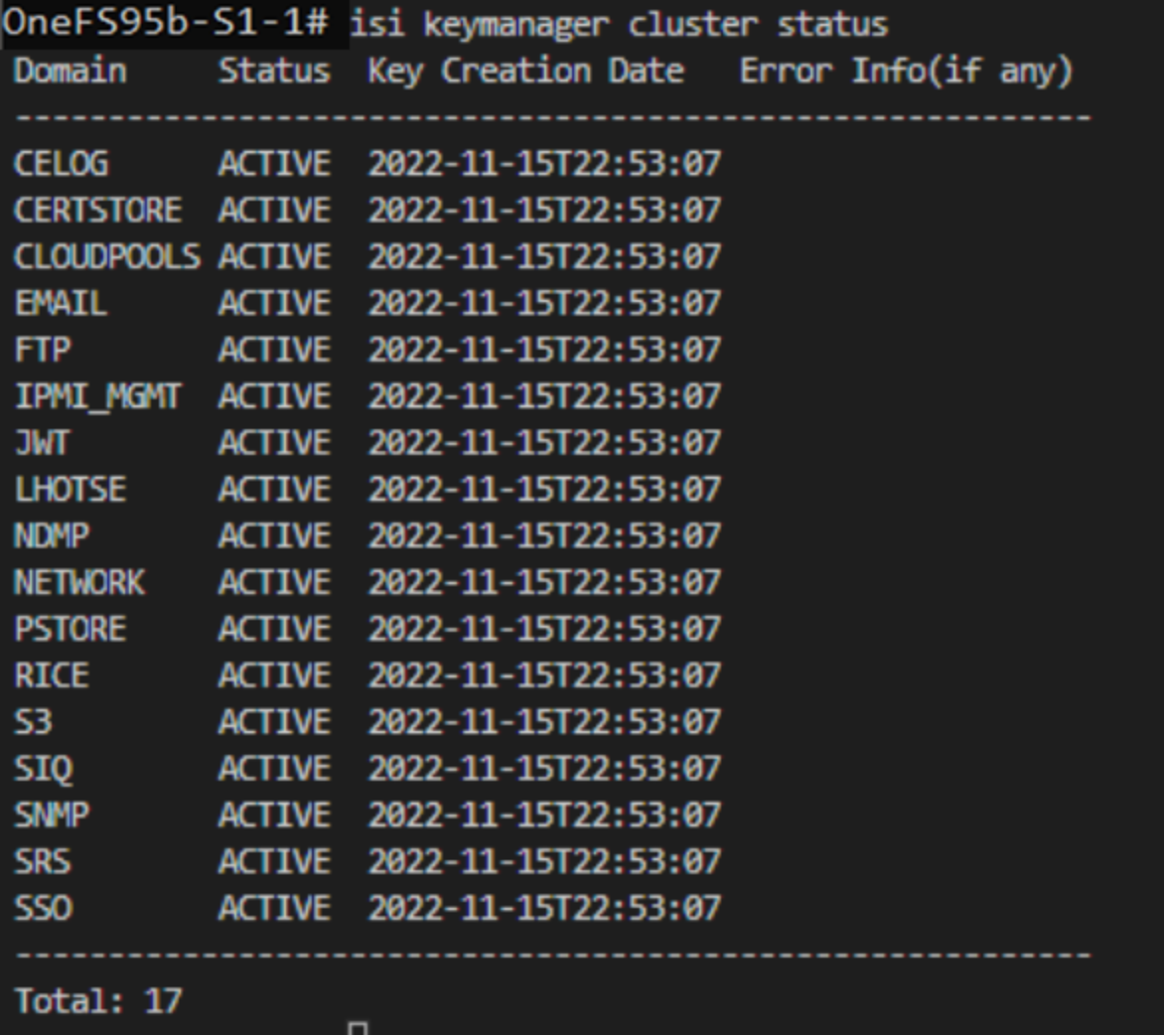
Figure 35. Key manager cluster status
If any errors occur during the rekey process, a CELOG event is generated with a KeyManagerRekeyFailed event. The rekey process is logged in /var/log/isi_km_d.log.
