Home > Storage > PowerScale (Isilon) > Product Documentation > Management and Migration > Dell PowerScale: Non-Disruptive Upgrade Best Practices > Signed upgrade
Signed upgrade
-
Overview
From OneFS 9.4.0.0, we introduced the signed upgrades feature. By using this, all upgrades like OneFS, firmware, and patches must be signed before they can be installed using the upgrade framework. The following are the new components of this feature:
- A new .isi package format. This format applies to all the packages of OneFS upgrade, patch, firmware, and DSP.
- A new OneFS Catalog. This component has been added to store signed packages on the cluster for use by the upgrade framework. It is designed to protect customers against malicious use of upgrade packages to compromise cluster security.
the .isi format
The Integrated Signature Install package (.isi) format is designed to enable a customer to download a package, verify its authenticity, review README text and install it on the cluster without needing to unpack anything. It also enables automatic verification and enforcement of signed packages by the upgrade framework.
Starting a signed upgrade is similar to starting an upgrade in previous versions with one exception. All upgrades must be started using a signed .isi package in place of the usual .tar or .pkg file.
The following are a few examples:
# isi upgrade start --install-image-path=/ifs/install.isi --parallel
# isi upgrade firmware start --fw-pkg /ifs/firmware.isi --parallel
# isi upgrade patches install /ifs/patch.isi --parallel
# isi_dsp_install /ifs/drive_firmware.isi
A .isi file is essentially a tarball file with a security footer as shown in Figure 5. The footer contains a manifest of data regions, cryptographic signature, cryptographic timestamp and a few other values used for verifying the file integrity. The manifest is a list of data regions within the file where the main package tarball is in region 1 and may be followed by other regions that can contain README text data or additional upgrade packages.
The first region is special because it can be accessed by older OneFS versions that are not aware of the .isi format, provided that the data is in tar format or another format that can handle unexpected trailing data.
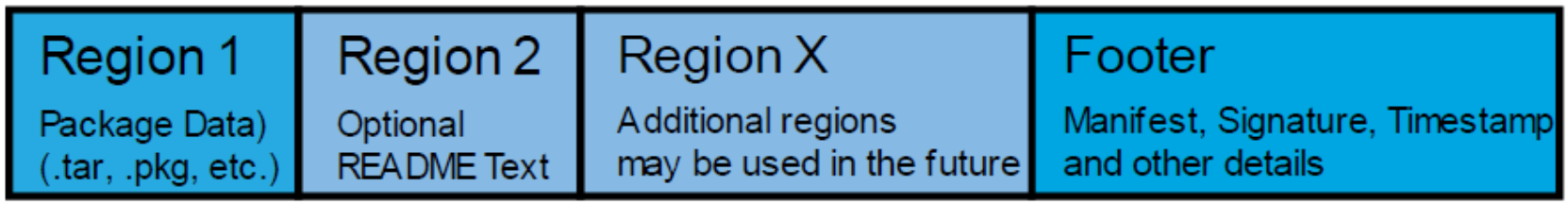
Figure 5. .isi file format
OneFS Catalog
The OneFS Catalog is the repository to store .isi files on the cluster that have been previously verified. Verified items in the catalog are called "artifacts". New files that are added to the catalog will be copied to the temp directory /ifs/.ifsvar/catalog/pending for verification. Once verified, the artifact will be stored in /ifs/.ifsvar/catalog/artifacts with a filename that corresponds to the SHA256 hash of the .isi file. Also, a database entry will be added to /ifs/.ifsvar/catalog/catalog.db.
The catalog serves two main functions:
The first is to provide a location that is only accessible by the root account to store files that have been verified so that they can be installed without worrying about tampering from non-privileged users. All non-root accounts including admin, compadmin or users in the wheel group do not have direct access to the catalog directory.
The second purpose of the catalog is to provide a PAPI interface so that non-privileged users can run approved functions on items in the catalog directory. It is possible for users with the appropriate RBAC role to import, export, verify, and remove items in the catalog. If the catalog directory, contents, or database is damaged, there is also a repair function to correct the issue without the user needing any directory access to the directory. This is especially important on compliance mode clusters where root access is not available.
Users can interact with the catalog using the "isi upgrade catalog" command set or related PAPI handlers. To verify the package signature, use the following command:
# isi upgrade catalog verify --file=/ifs/install.isi
Item Verified
---------------------------
/ifs/install.isi True
---------------------------
Total: 1
To have a deep insight of the package details, use the following command:
# isi_packager view --package=/ifs/install.isi
== Region 1 ==
Type: OneFS Install Image
Name: OneFS_Install_0x904005000000001_B_9_4_0_001(RELEASE)
Hash: 35a0901e35f7f3fa6a15c8bde7a91fc575855b164a83ed4938e69d70fd758069
Size: 361651596
== Footer Details == Format Version: 1
Manifest Size: 296
Signature Size: 3068
Timestamp Size: 1374
Manifest Hash: 8baf4591f2f68a2a31980c58d243a5781a1e0afaf122881360529b70ffc6ecb7 Signature Hash: 7cf6efb229847e6f7bb5ca52c3810d4c53325b0258f63060a7df6cfbd86e5ac1 Timestamp Hash: 47c653e9db3fef41146ad1cd4cdfbcee953c30add5febc6d0850ec56d9b0b0e7
== Signature Details ==
Fingerprint: 37c57297522afcd5890dfc24990a944598e69077
Issuer: Entrust Code Signing CA - OVCS2
Subject: US / Texas / Round Rock / Dell Technologies Inc.
Organization: Dell Technologies Inc., Powerscale OneFS
Expiration: 2022-08-17 17:44:43
Ext Key Usage: codeSigning
To import a signed package, use the following command. A package will automatically be verified when it is imported.
# isi upgrade catalog import --file /ifs/export.isi
Use the following list command, to view the ID, type, description and whether it contains the README file of a signed package.
# isi upgrade catalog list
ID Type Description README
-----------------------------------------------------
a75fb OneFS OneFS 9.4.0.0_build(1)style(5) -
-----------------------------------------------------
To export the artifact in the catalog to the OneFS file system, use the following command:
# isi upgrade catalog export --id=a75fb /ifs/export.isi
To view the README file or the release notes of the signed package, use the following command:
# isi upgrade catalog readme --file HealthCheck_9.2.1_2021-09.isi | less Updated: September 02, 2021
******************************************************************************** HealthCheck_9.2.1_2021-09: Patch for OneFS 9.2.1.x.
This patch contains the 2021-09 RUP for the Isilon HealthCheck System
******************************************************************************** This patch can be installed on clusters running the following OneFS version:
* 9.2.1.x
