Home > Storage > PowerScale (Isilon) > Product Documentation > Management and Migration > Dell PowerScale: Integrating OneFS with Kerberos Environment for Protocols > NFS Kerberos authentication
NFS Kerberos authentication
-
There are four authentication methods (also known as security types) supported by OneFS: UNIX, Kerberos5, Kerberos5 Integrity, and Kerberos5 Privacy. Use the sec mount option on NFS client to specify a security type. Table 1 shows the details of the sec option. sec=sys is the default mount option; each NFS operation includes the UID/GID of users and authentication to servers. This authentication method has a risk of spoofing by a different user with same UID/GID. It also has a vulnerability of being tampered with a third party between the client and server on the network. For NFSv3, using Kerberos authentication would mitigate this situation, but is still not completely secure, because Kerberos is only applied to the NFS packets and not the auxiliary services such as Network Lock Manager (NLM), Network Status Monitoring (NSM), or mountd. For NFSv4, it is designed as a single protocol without any auxiliary service required, and all NFS operations are authenticated and protected by Kerberos.
In an environment that requires high security for NFS, it is recommended to use NFSv4 instead of NFSv3 and to integrate Kerberos authentication with NFS.
Table 1. Mount security types
Options
Authentication methods
Description
sec=sys
UNIX (also known as AUTH_SYS)
The default setting, which uses local UNIX UIDs and GIDs by means of AUTH_SYS to authenticate NFS operations
sec=krb5
Kerberos only
Use Kerberos V5 instead of local UNIX UIDs and GIDs to authenticate users.
sec=krb5i
Kerberos with integrity
Use Kerberos V5 for user authentication and perform integrity checking of NFS operations using secure checksums to prevent data tampering.
sec=krb5p
Kerberos with integrity and encryption
Use Kerberos V5 for user authentication, integrity checking, and encrypt NFS traffic to prevent traffic sniffing. This is the most secure setting, but it also has the most performance overhead involved.
To use NFSv4, you must have an identical NFSv4 domain name configured on OneFS cluster and NFSv4 clients. With NFSv4 domain, the NFSv4 represents users and groups in the form of user@domain or group@domain in the results of a get attribute (GETATTR) operation and in the arguments of a set attribute (SETATTR) operation. Figure 4 shows a capture of a NFSv4 GETATTR operation. As Figure 4 shows, the user/group names have an NFSv4 domain suffix @vlab.local in the GETATTR operation.
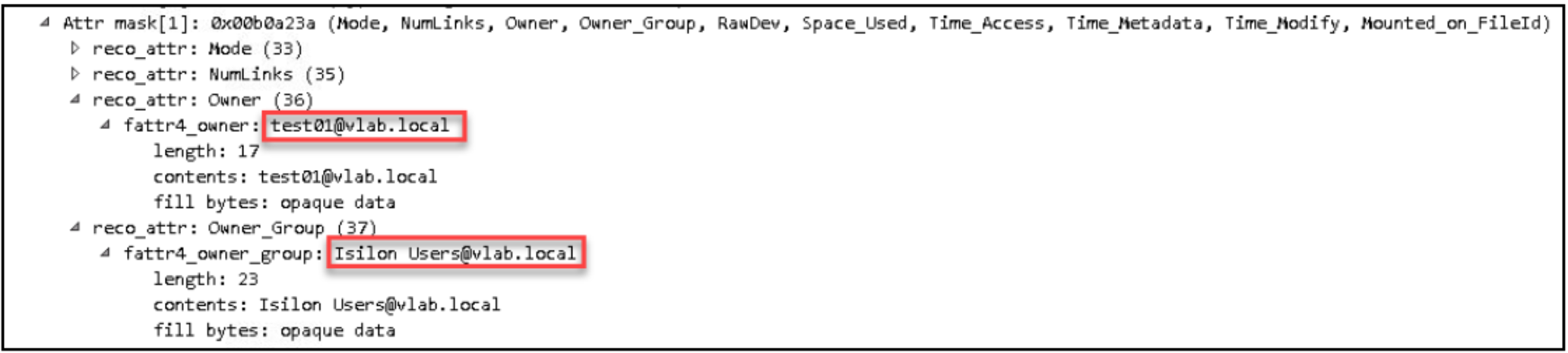
Figure 4. NFSv4 user and group format
The Kerberos-related configurations for NFSv3 and NFSv4 are the same. The following subsections show the key configurations on OneFS when using Microsoft Kerberos or MIT Kerberos and provide a sample configuration for CentOS 7 Linux clients as an example in Appendix B: Sample configuration for Kerberizing CentOS 7.
