Home > Storage > PowerScale (Isilon) > Product Documentation > Management and Migration > Dell PowerScale: Integrating OneFS with Kerberos Environment for Protocols > Microsoft Kerberos using AD
Microsoft Kerberos using AD
-
Considerations for Kerberized NFS with AD
When configuring NFS on OneFS with Microsoft AD Kerberos, consider the following items:
- The time must be synchronized across NFS clients, OneFS cluster nodes, and the Kerberos server (Windows Active Directory in this case). It is recommended to use an NTP server in a Kerberos environment.
- Kerberos relies on being able to resolve host names. Thus, it requires a DNS for host resolution.
- Consistent UID/GID information for domain user accounts from NFS clients and OneFS. It is recommended to enable RFC2307 attributes in AD for this purpose. (For details, see the article Clarification regarding the status of Identity Management for Unix (IDMU) & NIS Server Role in Windows Server 2016 Technical Preview and beyond.) Required attributes include uidNumber, gidNumber, loginshell, unixHomeDirectory.
- OneFS cluster joins to a domain by creating an Active Directory authentication provider with RFC2307 enabled.
- Add the Active Directory authentication provider to an access zone.
- Configure SmartConnect for the access zone in advance. SPNs for SmartConnect zone names must be created.
- Enable OneFS NFS exports with the Kerberos security type.
- Clients should use the SmartConnect zone name and the domain user for accessing NFS exports.
- SPNs for NFS for OneFS and client must exist.
3.1.2 Configurations for Kerberized NFS with AD
The following configurations illustrate key steps to use NFS Kerberos authentication.
- Create an Active Directory authentication provider using the isi CLI command. NFS clients cannot recognize the auto-generated UID/GID assigned by OneFS, so we need to enable Service for UNIX with ---sfu-support option for consistent UID/GID information. This will specify that OneFS retrieves the UID/GID from AD RFC2307 attributes instead of using an auto-generated UID/GID.
# isi auth ads create --name=example.com --user=administrator -groupnet=groupnet0 --sfu-support=rfc2307 --kerberos-nfs-spn=true
- Add the Active Directory authentication provider to the access zone.
# isi zone zones modify --name=KrbZone --add-auth-providers=lsaactivedirectory-provider:EXAMPLE.COM
- Configure SmartConnect on the OneFS cluster and the DNS server.
- Check whether SmartConnect zone name SPNs are created on Active Directory by using the following isi CLI command:
# isi auth ads spn check --provider-name=EXAMPLE.COM
Possible missing SPNs:
HOST/sc01
HOST/sc01.example.com
nfs/sc01.example.com
When joining an Active Directory domain, the cluster will register the cluster name and any SmartConnect zone names as Service Principal Names (SPNs) configured on the cluster with the machine account on the domain. Any additional SmartConnect zone names created after joining the cluster to the domain must have SPNs manually added.
To fix all the missing SPNs quickly, use the following command:
# isi auth ads spn fix --provider-name=EXAMPLE.COM --user=administrator
If you have access rights to log on to your Active Directory domain controller server, you can find and edit the associated SPNs under the advanced feature view in the attribute editor tab for the OneFS cluster machine account, as shown in Figure 5
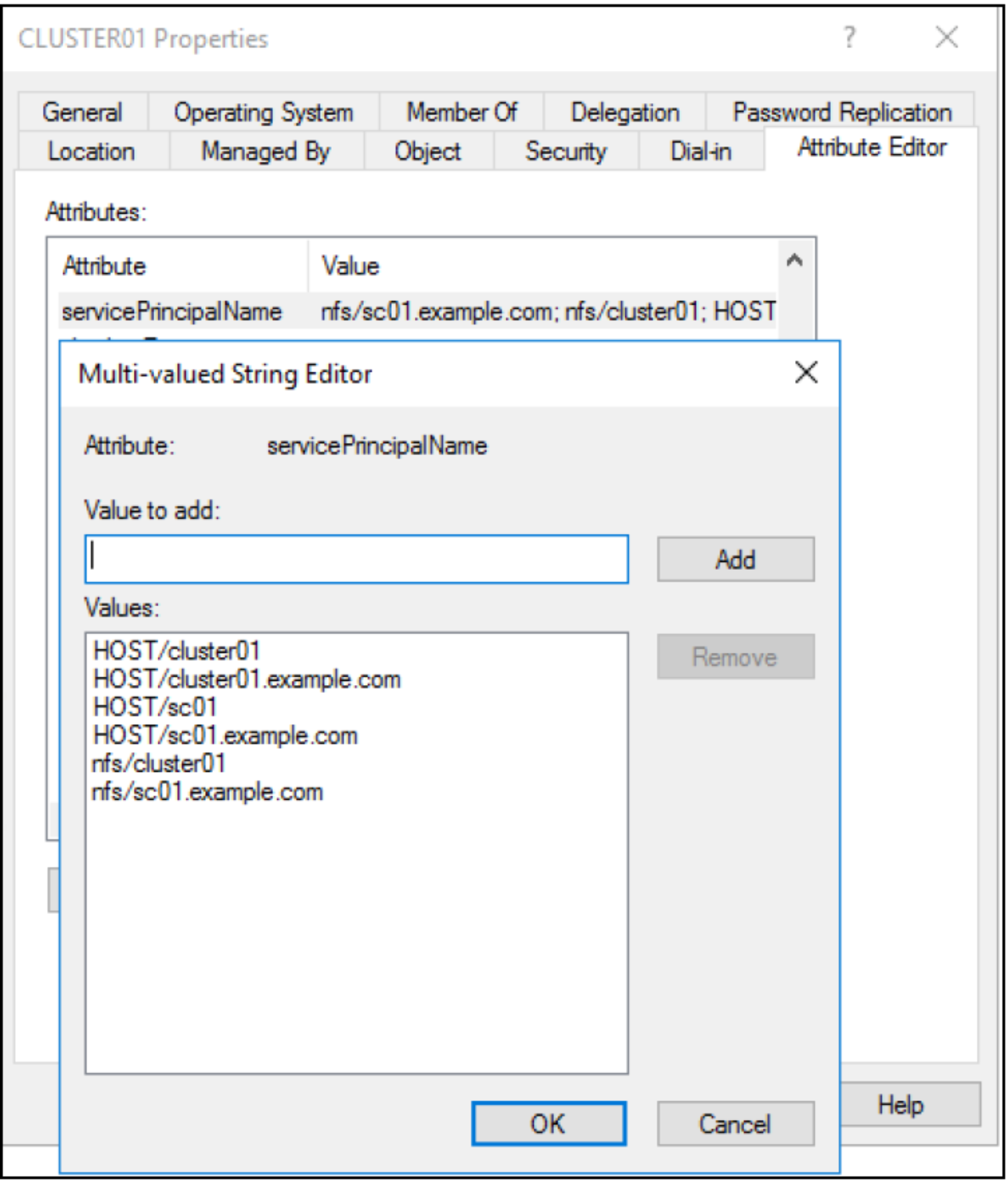
Figure 5. Check SPNs in AD
- For NFSv4, enable the NFSv4 service and configure the NFSv4 domain name in the specific access zone.
# isi nfs settings global modify --nfsv4-enabled=true
# isi nfs settings global view
NFSv3 Enabled: Yes
NFSv4 Enabled: Yes
NFS Service Enabled: Yes
# isi nfs settings zone modify --zone=KrbZone --nfsv4-domain=example.com
# isi nfs settings zone view --zone=KrbZone
NFSv4 Domain: example.com
NFSv4 Replace Domain: Yes
NFSv4 No Domain: No
NFSv4 No Domain UIDs: Yes
NFSv4 No Names: No
NFSv4 Allow Numeric Ids: Yes
- Create an NFS export with the Kerberos security type enabled on the OneFS cluster. The following command enables all supported security types. See Table 1 for details about security types.
# isi nfs exports create --paths=/ifs/nfs --zone=KrbZone --securityflavors=unix,krb5,krb5i,krb5p
- Kerberize the NFS client by integrating with AD and mount NFS export with Kerberos authentication using the sec option, as shown in Table 1. See the section Kerberize CentOS 7 with Active Directory for a CentOS 7 sample configuration.
