Home > Storage > PowerScale (Isilon) > Product Documentation > Management and Migration > Dell PowerScale: Integrating OneFS with Kerberos Environment for Protocols > Configurations for Kerberized SMB access
Configurations for Kerberized SMB access
-
The following configurations illustrate key steps to use SMB Kerberos authentication from both the cluster side and the Windows client side.
- Create an Active Directory authentication provider using the isi CLI command.
# isi auth ads create --name=example.com --user=administrator -groupnet=groupnet0
- Add the Active Directory authentication provider to an access zone.
# isi zone zones modify --name=zone01 --add-auth-providers=lsaactivedirectory-provider:EXAMPLE.COM
- Configure SmartConnect on the OneFS cluster and the DNS server.
- Check whether SmartConnect zone name SPNs are created on Active Directory by using the following isi CLI command:
# isi auth ads spn check --provider-name=EXAMPLE.COM
Possible missing SPNs:
HOST/sc01
HOST/sc01.example.com
nfs/sc01.example.com
For SMB Kerberos, HOST/SmartConnect_zone_name SPNs are required. From the output above, create the following SPNs using the isi CLI command.
# isi auth ads spn create --provider-name=EXAMPLE.COM --user=administrator --spn=HOST/sc01.example.com
# isi auth ads spn create --provider-name=EXAMPLE.COM --user=administrator --spn=HOST/sc01
Alternately, you can fix all missing SPNs quickly, with the following command.
# isi auth ads spn fix --provider-name=EXAMPLE.COM --user=administrator
If you have access rights to log on to your Active Directory domain controller server, you can find the associated SPNs under the advanced feature view in the attribute editor tab, as shown in Figure 2.
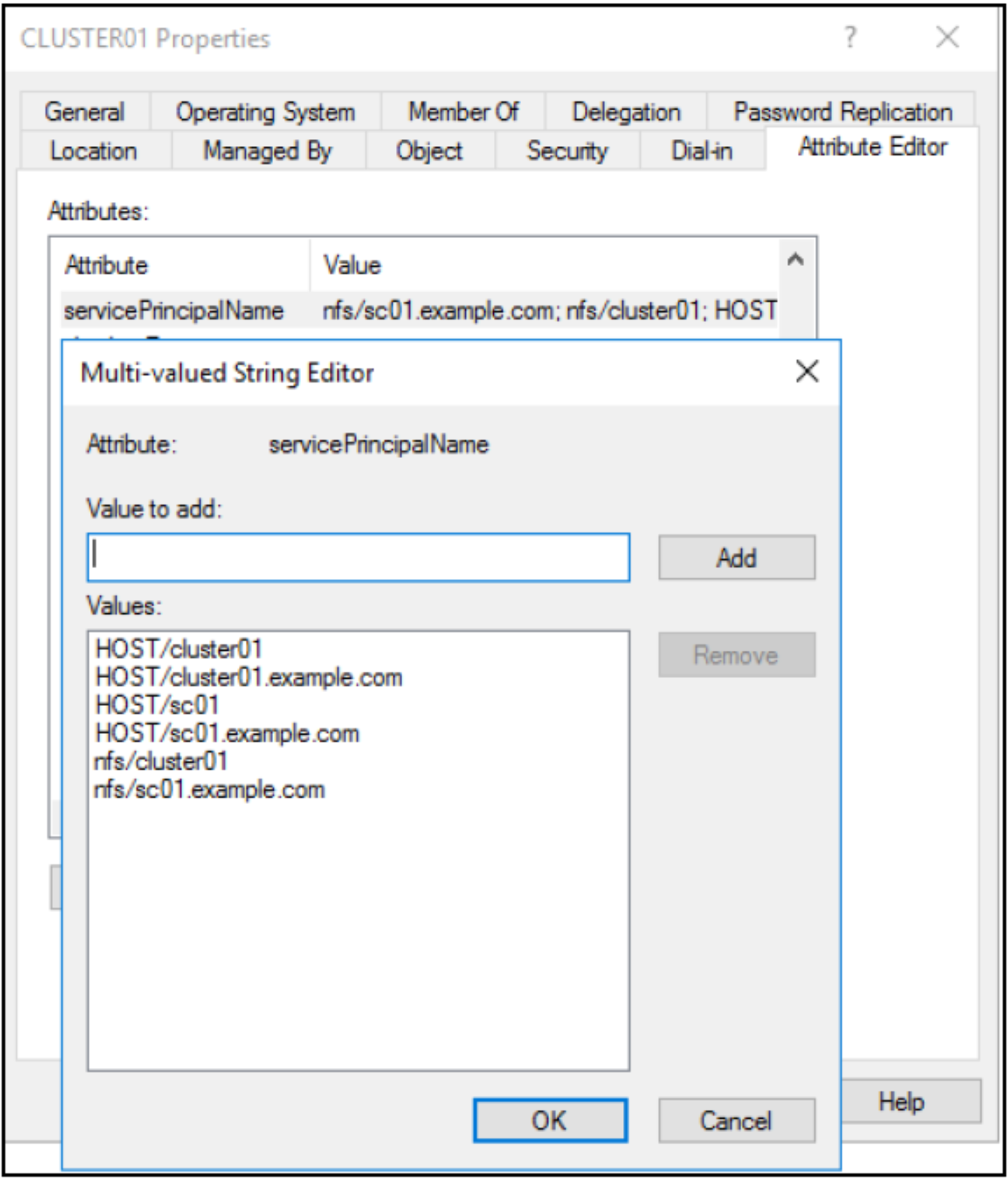
Figure 2. Check SPNs in AD
- To leverage SMB Kerberos authentication, clients in an AD domain need to access the SMB share using SmartConnect FQDN along with an AD user account. If the current Windows login user is a domain user who has access rights to the SMB share, the Windows client will transparently authenticate using its logon credentials and will prompt for credentials if the Windows credentials failed. For a NetBIOS Name Service (NBNS) enabled Windows environment, SMB Kerberos authentication may still be effective even though a Windows client is not a domain member.
- To verify that Kerberos is being used, capture network packets during the SMB connection or use the klist command. Figure 3 shows an example of the klist command.
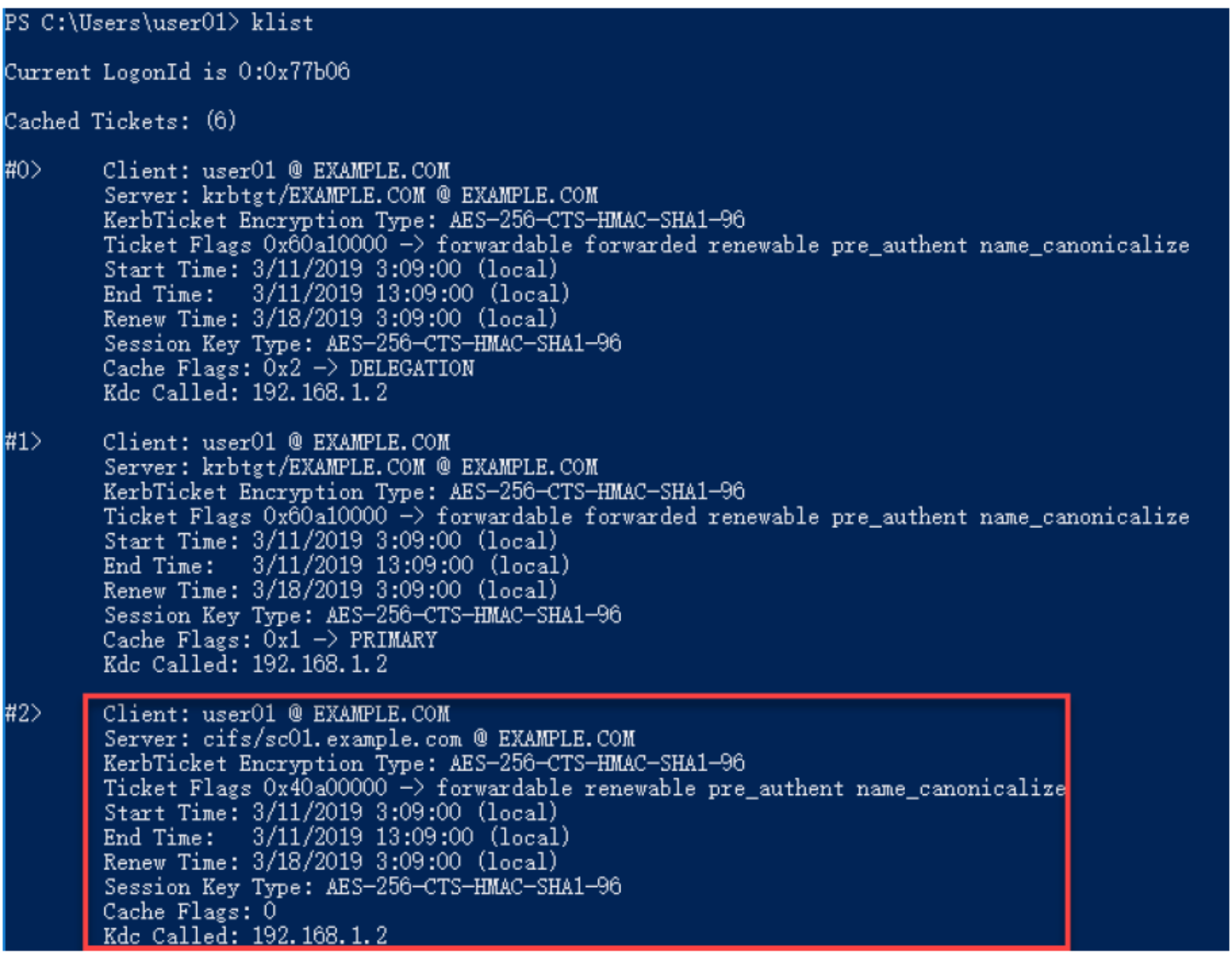
Figure 3. Confirm that Kerberos is used
