Home > Storage > PowerScale (Isilon) > Product Documentation > Storage (general) > Dell PowerScale: Common AntiVirus Agent Solution > Architecture
Architecture
-
Architecture overview
Figure 1 illustrates a high-level architecture of the CAVA anti-virus solution for PowerScale. Dell Common Event Enabler (CEE) sits between the PowerScale cluster and the anti-virus applications. When clients trigger the scanning workflow, Dell PowerScale OneFS generates a request to the CEE or CAVA agent through the HTTP protocol. Then, the anti-virus application fetches the scanning files from PowerScale through the hidden SMB share called CHECK$. These files are scanned by the anti-virus applications.

Figure 1. The overall architecture of the CAVA solution for PowerScale
The detailed architecture is explained separately by three scanning workflows from the OneFS perspective:
- On-demand scan (also known as on-access scan): This scan is triggered by the proper SMB operation, such as a read or close operation, and depends on your scan profile. There are two scan profiles in OneFS:
- Standard profile: Captures a close and rename operation from an SMB perspective, and triggers the scan operation on the corresponding file.
- Strict profile: Captures a read, close, and rename operation from an SMB perspective, and triggers the scan operation on the corresponding file.
- Scheduled scan: This scan is triggered by the job engine either manually or by schedule.
- Manual scan: This scan is triggered by the CLI command or the corresponding PAPI call to scan a single file.
Generally, the CAVA solution provides better performance, lower total cost of ownership (TCO), and much less CPU and memory usage from the PowerScale perspective, compared with an anti-virus solution based on ICAP.
Note: ICAP is still supported, which remains unchanged from the previous versions of OneFS.
On-demand scan
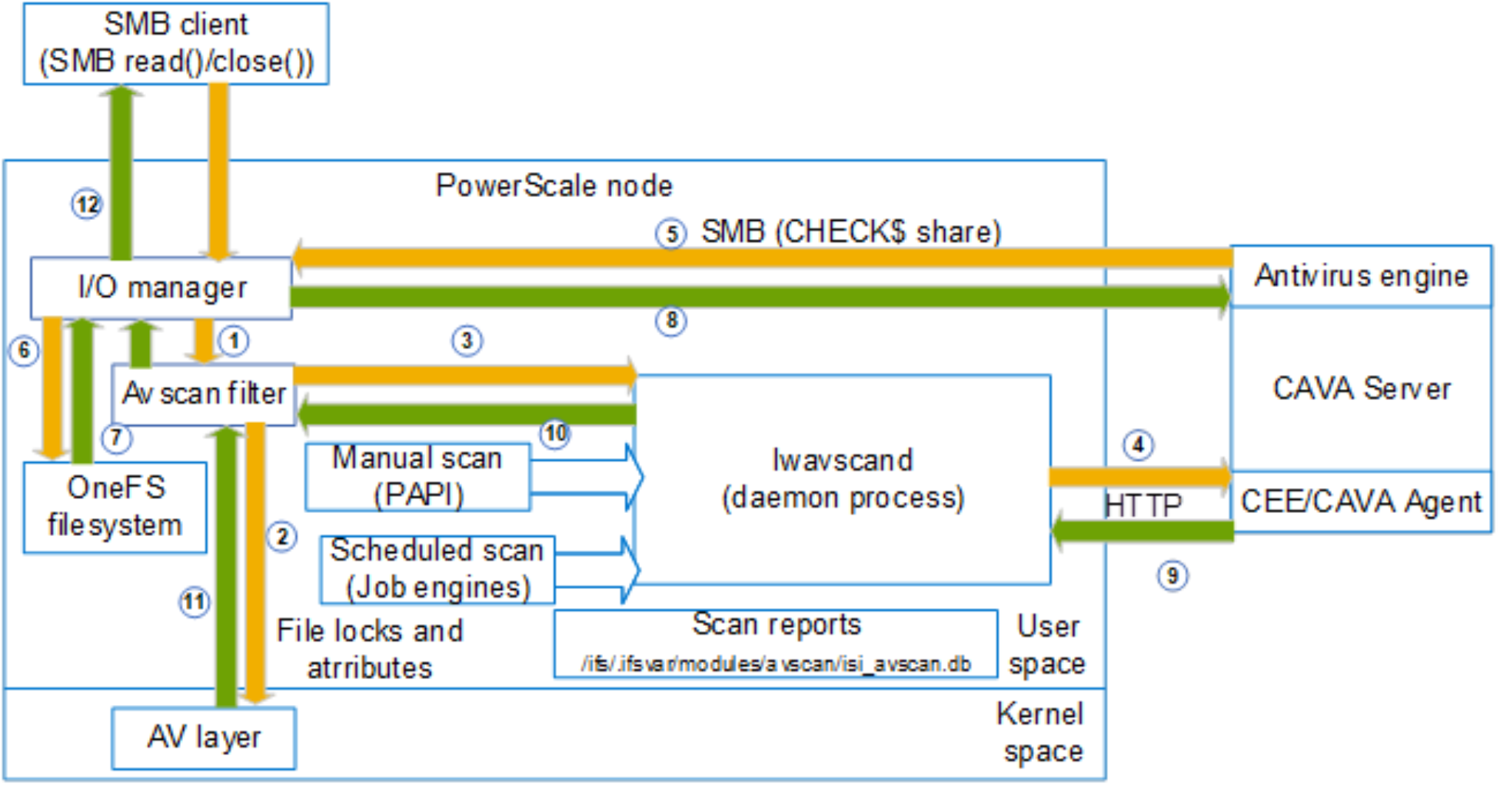
Figure 2. The workflow of the on-demand scan
Figure 2 shows the workflow of an on-demand scan. Depending on which scan profile is selected, the SMB requests with a read or close operation code are captured by the I/O manager in OneFS. It extracts the file path and name to provide to the Avscan filter, which can be configured on an access-zone basis. The Avscan filter will then filter according to the following aspects:
- File extension to include
- File extension to exclude
- File path to exclude
If the file matches all the criteria, an internal process lwavscand sends the HTTP scanning request to the CEE/CAVA agent. Simultaneously, OneFS sets the locks on this file. Then, the anti-virus application tries to fetch this file through the hidden SMB share CHECK$ from the file system on OneFS. CAVA supports only downloading a part of a file for scanning, which helps the performance. After the corresponding content is downloaded to the CAVA server, it runs the scan with the anti-virus engine, and CEE sends the scan results and response back to the process lwavscand. At this stage, some scanning attributes are written to this file and the lock is released. The scanning attributes are:
- Scan time
- Scan Result
- Anti-virus signature timestamp
- Scan current
The previous SMB workflow can then continue if the file is not infected. Otherwise, the file is denied access. If there are errors during the scan and the scan profile is strict, the setting Open on fail determines the next action.
Scheduled scan
Figure 3 shows the workflow of the scheduled scan in OneFS. The scheduled scan is triggered by the job engine. Similar to other jobs in OneFS, the impact and schedule configuration can be set accordingly. It also implements the filter, which is slightly different from the filter in the on-demand scan. The detailed filtering criteria are:
- File extension to include
- File extension to exclude
- File path to exclude
- File path to include (only in the scheduled scan)
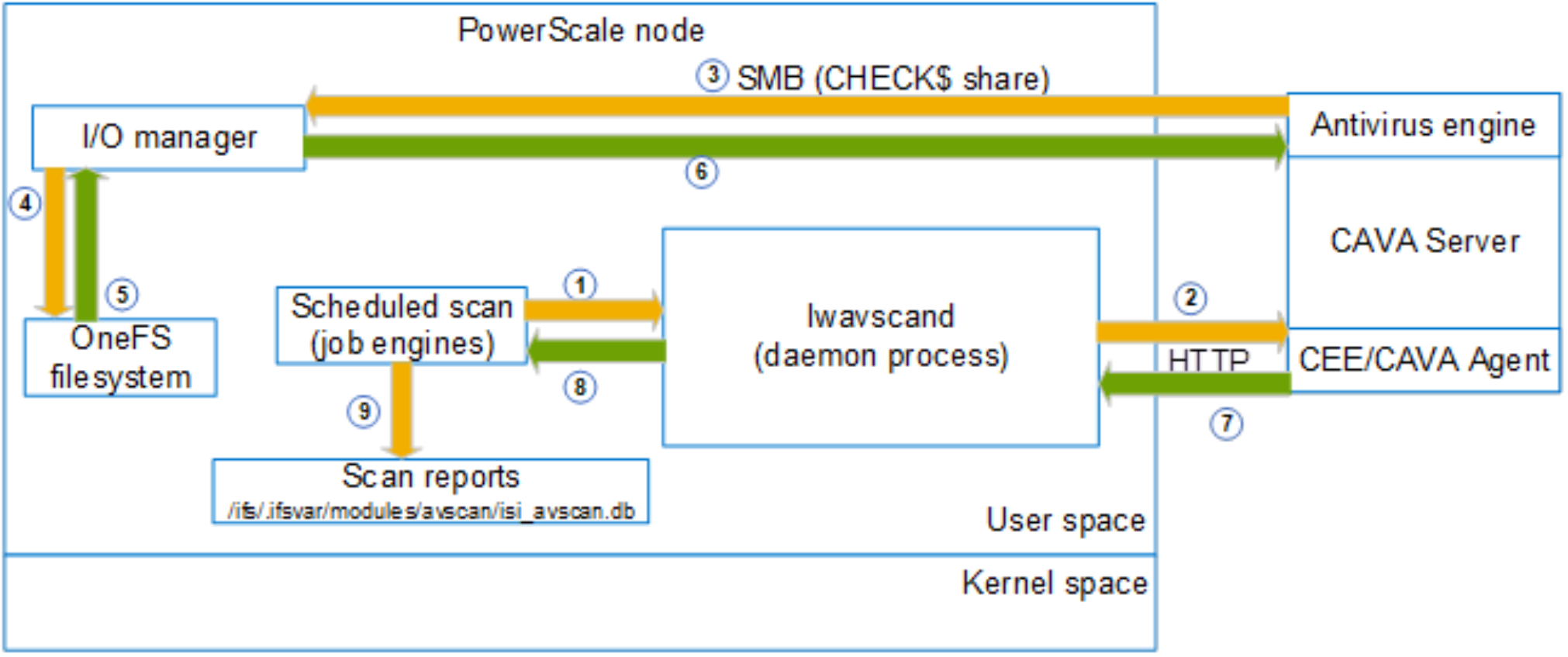
Figure 3. The workflow of the scheduled scan
If the file matches all the criteria, an internal process lwavscand sends the HTTP scanning request to the CEE/CAVA agent, and simultaneously, OneFS sets the locks on this file. The anti-virus application then attempts to fetch this file through the hidden SMB share CHECK$ from the file system on OneFS. CAVA supports only downloading a part of a file for scanning, which helps the performance. After the corresponding content is downloaded to the CAVA server, it runs the scan with the anti-virus engine, and CEE sends the scan results and response back to the process lwavscand. All the scanning attributes are recorded under /ifs/.ifsvar/modules/avscan/isi_avscan.db.
Manual scan
Figure 4 shows the workflow of a manual scan. The manual scan is triggered by the CLI, PAPI, or web interface. Unlike an on-demand scan or scheduled scan, it has no filters. The scanning files are directly assigned by the parameters. The daemon process lwavscand sends the HTTP scanning request to the CEE or CAVA agent, and simultaneously, OneFS sets the locks on this file. The anti-virus application then attempts to fetch this file through the hidden SMB share CHECK$ from the file system on OneFS. CAVA supports only downloading a part of the file for scanning, which helps the performance. After the corresponding content has been downloaded to the CAVA server, it runs the scan with the anti-virus engine, and CEE sends the scan results and responds to the process lwavscand. All the scanning attributes are recorded under /ifs/.ifsvar/modules/avscan/isi_avscan.db.

Figure 4. The workflow of manual scan
