Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Dell PowerScale: Answers to Common Questions about Audit/Syslog > Invalid access through the protocol
Invalid access through the protocol
-
Invalid access attempts through the protocol are logged in the protocol access audit log. To examine these attempts, use the following command:
isi_audit_viewer -t protocol|grep log
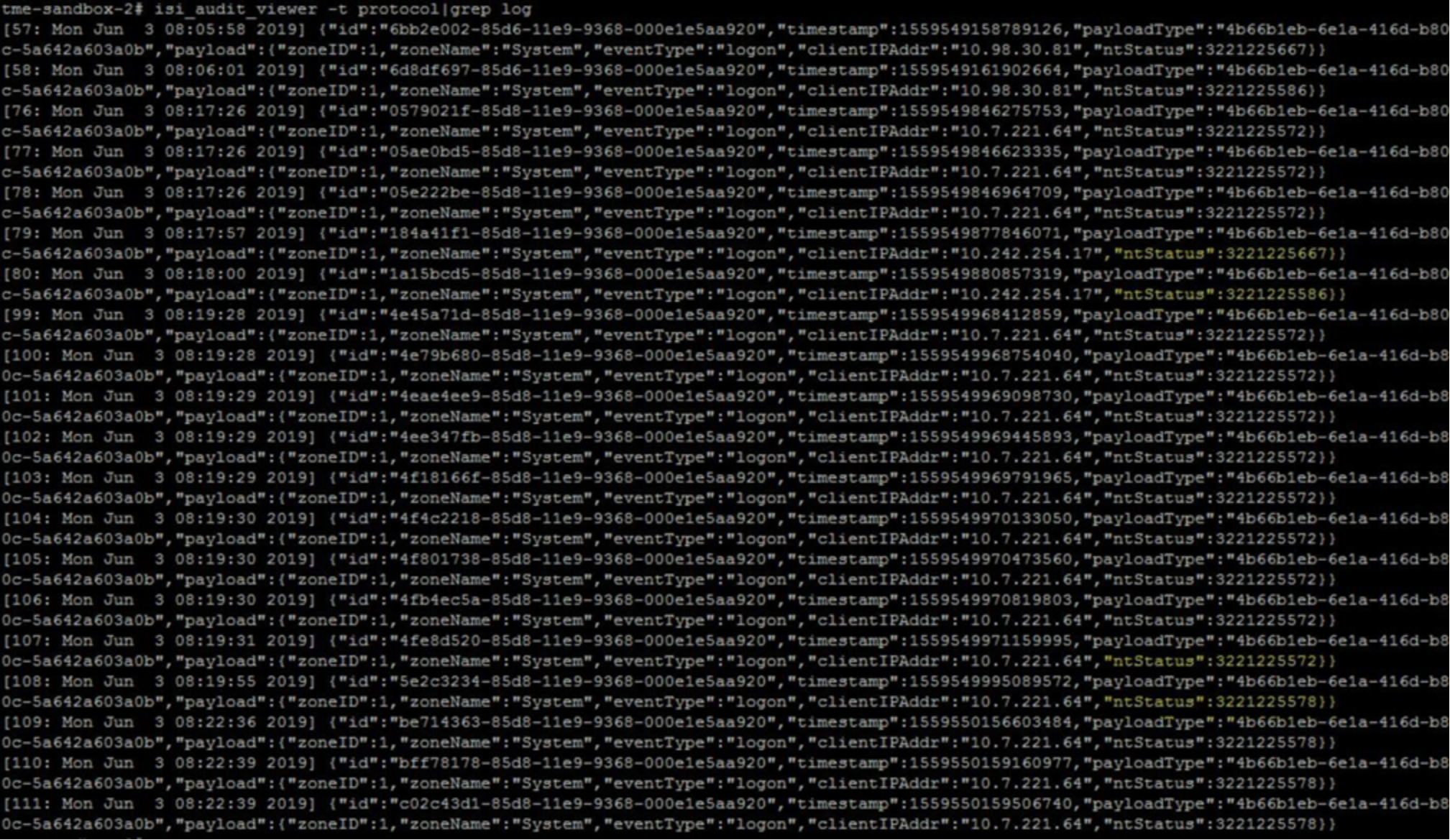
Figure 4. Audit log - Invalid access through the protocol
In the protocol access audit log file, you can examine the reasons for the invalid access in the ntStatus field. The following are some common codes for ntStatus
- 3221225578 - wrong password
- 3221225572 - no such user
- 3221225586 - account disabled
