Home > Storage > PowerScale (Isilon) > Product Documentation > Protocols > Dell EMC PowerScale OneFS S3 Overview > OneFS S3 request authentication
OneFS S3 request authentication
-
OneFS S3 authenticates requests with a signing mechanism, either AWS Signature Version 2 or AWS Signature Version 4. Authenticated requests must include a signature value that authenticates the request sender. Each of these requires the user to have an access ID and a secret key. The user must get these credentials through the OneFS WebUI or CLI before performing signed S3 requests. Figure 6 shows a result of generating the access ID and secret key for the admin user through the WebUI.
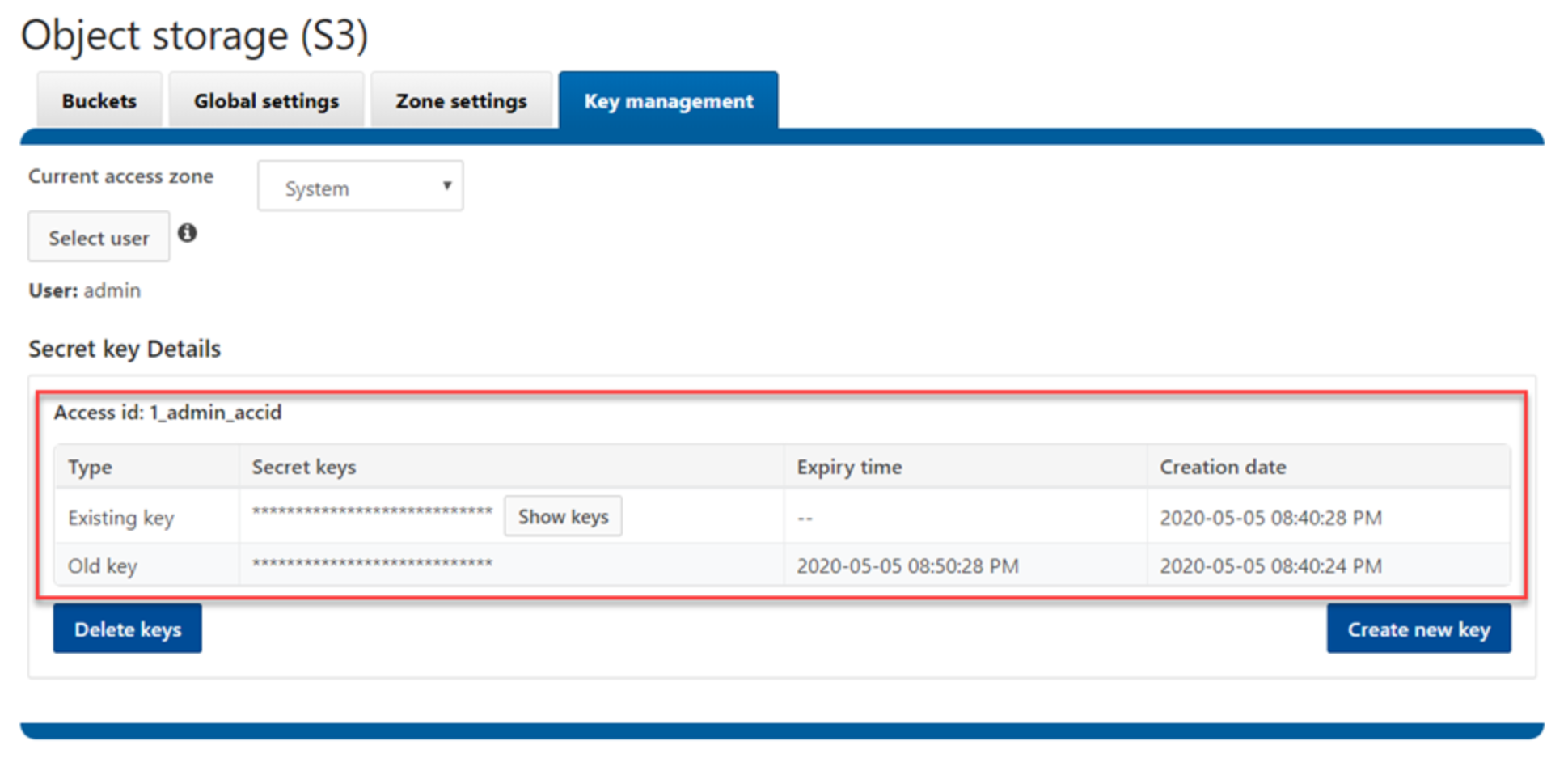
Figure 6. Generate access ID and secret key using the WebUI
The access ID indicates who the user is. OneFS generates one access ID per user. For example, OneFS may generate access ID 1_joe_accid for user joe. The prefix number represents the user’s access zone ID. Each access ID would have a latest secret key without an expiry time set and an old secret key that has an expiry time set.
The secret key is used to generate the signature value along with several request-header values. After receiving the signed request, OneFS uses the access ID to retrieve a copy of the secret key internally, recompute the signature value of the request, and compare it against the received signature. If they match, the requester is authenticated, and any header value that was used in the signature is now verified to be untampered as well.
OneFS treats unauthenticated requests as anonymous requests made by the nobody user (UID 65534). If an object is uploaded to a bucket through an unauthenticated request, the nobody user owns the object and has FULL_CONTROL to the object. To prevent an anonymous request from modifying OneFS buckets and objects, we recommend not to use ACLs that give the nobody user write access to your bucket.
For example, use the following OneFS CLI to grant or revoke write permissions on the bucket for the nobody user.
# isi s3 buckets modify <bucket> --add-ace="name=nobody,type=user,perm=write" --zone=<name>
# isi s3 buckets modify <bucket> --remove-ace="name=nobody,type=user,perm=write" --zone=<name>
