Home > Storage > PowerMax and VMAX > Data Protection > Dell EMC PowerMax: End-to-End Efficient Encryption > Encrypting a volume
Encrypting a volume
-
Efficient encryption from the host using Thales is set per volume. You can set encryption on a subset of volumes, and not all volumes are required to participate in end-to-end efficient encryption. Encryption on the back-end with D@RE encrypts all data, regardless if it set for efficient encryption or not.
You can encrypt a volume in two steps:
- Create an encryption-capable volume
- Guard a volume
Creating an encryption-capable volume
The encryption capable attribute identifies volumes that participate in encryption from the host and benefit from the PowerMax data reduction capabilities. You cannot add the attribute to an existing volume or remove it after a volume is created. A volume that is created with the encryption-capable attribute does not automatically encrypt the host data, and it must go through the encryption process. If a capable volume is to be encrypted, it must be guarded.
You can set a volume as encryption capable when creating a volume using one of the following methods:
- Solutions Enabler: Add the option -eff_encrypt_capable (Figure 5).
- Unisphere: Apply the setting under the Advanced tab (Figure 6)
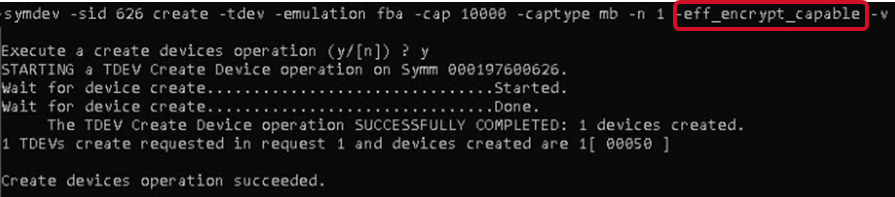
Figure 5. Creating a volume through Solutions Enabler with the -eff_encrypt_capable option
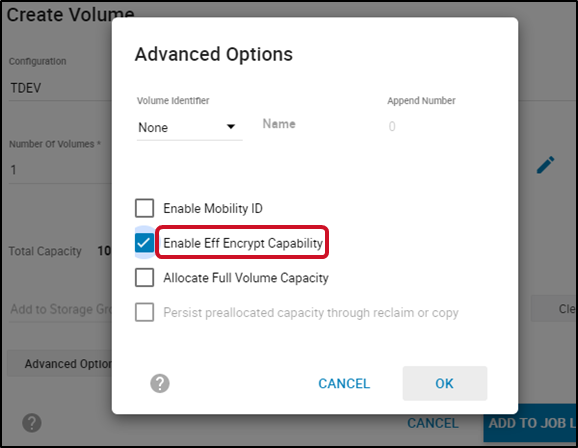
Figure 6. Creating an encryption-capable volume through Unisphere
After you create a volume, the volume properties reflect it as encryption-capable, as shown in the following two figures.
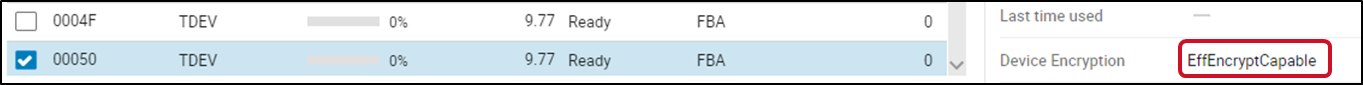
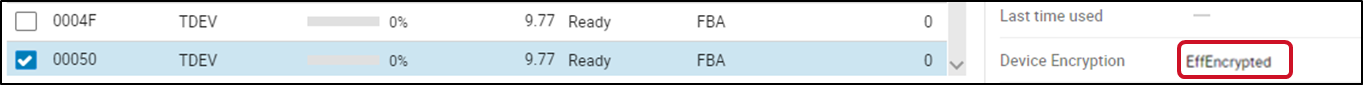
Figure 7. Viewing volume properties using Unisphere
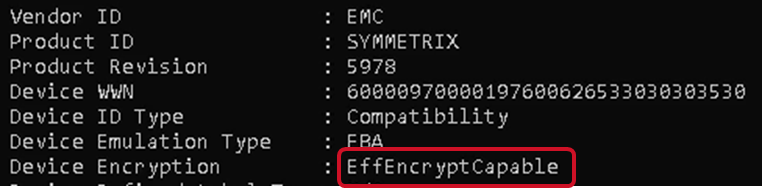
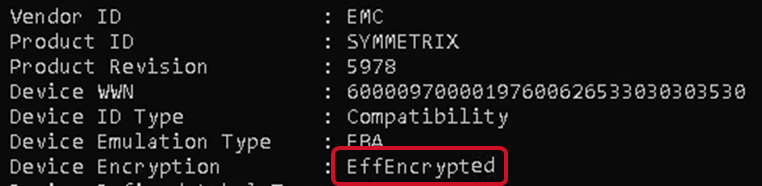
Figure 8. Viewing volume properties using Solutions Enabler > symdev show command
Guarding a volume
Guarding an encryption-capable volume activates encryption for all I/O to that volume from the host application. Guarding a capable volume encrypts all new data and does not encrypt any data that had previously been written to that volume.
Guarding a volume requires the following configuration:
- VTE enabled host
- Access to set policy on the DSM
For more information about guarding a volume, see the Thales Data Security Manager, DSM Administration Guide for DSM release and Thales VTE Agent Installation and configuration Guide for VTE release.
The following is an example of the process for guarding a volume.
- Use the symdev show command to show the volume physical name.
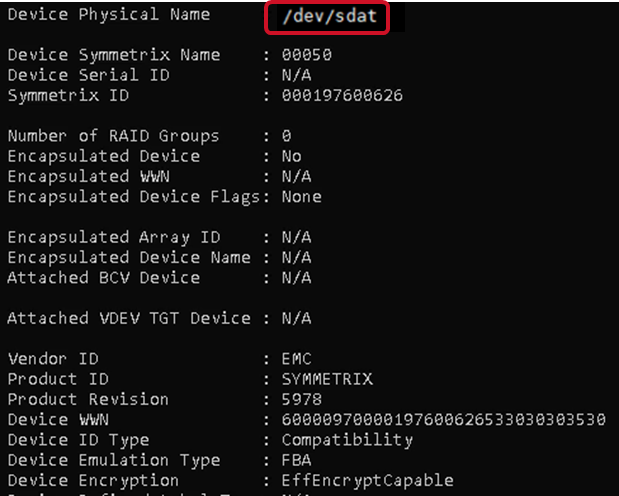
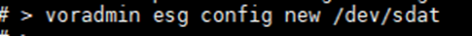
- From the VTE enabled host, enter the VTE-specific command voradmin esg config new <volume_physical_name> to prepare the volume to be encrypted.
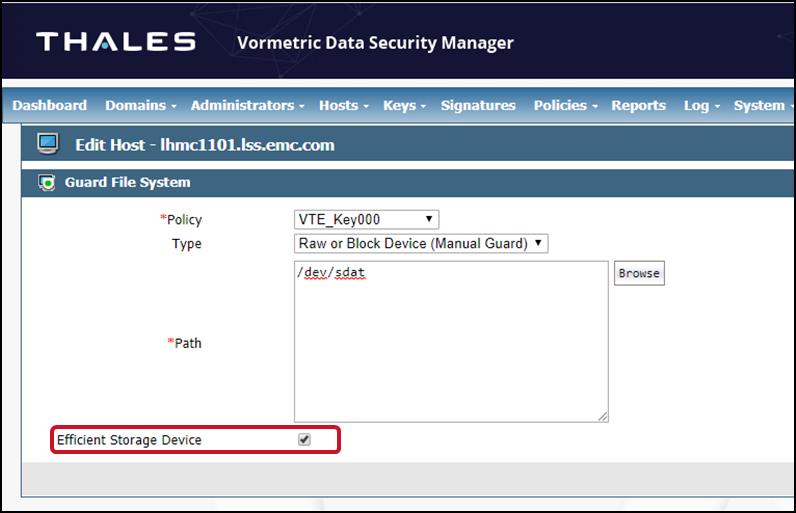
- DSM sets the encryption policy, and the volume path is identified using the volume physical name. Check the Efficient Storage Device option in DSM.
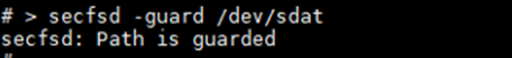
- Guard the volume with the VTE command secfsd -guard <volume_physical_name>.
Once the policy is set and the volume is guarded, DSM and PowerMax generate and share encryption keys (see Figure 1).
The volume properties from Unisphere and Solutions Enabler reflect the new encryption status.