Home > Storage > ObjectScale and ECS > Product Documentation > Dell ECS: High Availability Design > Advanced data-protection methods
Advanced data-protection methods
-
Within ECS, when an object is created it includes writing data, custom metadata, and ECS metadata. ECS metadata includes journal chunks and btree chunks. Each is written to a different logical chunk that contains ~128 MB of data from one or more objects. ECS uses a combination of triple mirroring and erasure coding to protect the data within a virtual data center (VDC)/site.
- Triple mirroring ensures that three copies of data are written, thus protecting against two node failures.
- Erasure coding provides enhanced data protection from disk and node failures. It uses the Reed Solomon erasure coding scheme, which breaks up chunks into data and coding fragments that are equally distributed across nodes within a VDC/site.
Depending on the size and type of data, data is written using one of the data protection methods shown in the following table.
Table 5. Data protection methods based on data type and size
Type of data
Data protection method used
Journal chunks
Triple mirroring
Btree chunks/custom metadata
Erasure coding with redundant data segments
Object data <128 MB
Triple mirroring plus in-place erasure coding
Object data >128 MB
Inline erasure coding
Note: In the all-flash architecture like EXF900, the btree chunks protection is triple mirroring.
Triple mirroring
The triple-mirror write method is applicable to the ECS journal chunks, of which ECS creates three replica copies. Each replica copy is written to a single disk on different nodes across failure domains. This method protects the chunk data against two-node or two-disk failures.
The following figure shows an example of triple mirroring whereby a logical chunk, containing 128 MB metadata, has three replica copies, each written to a different node.
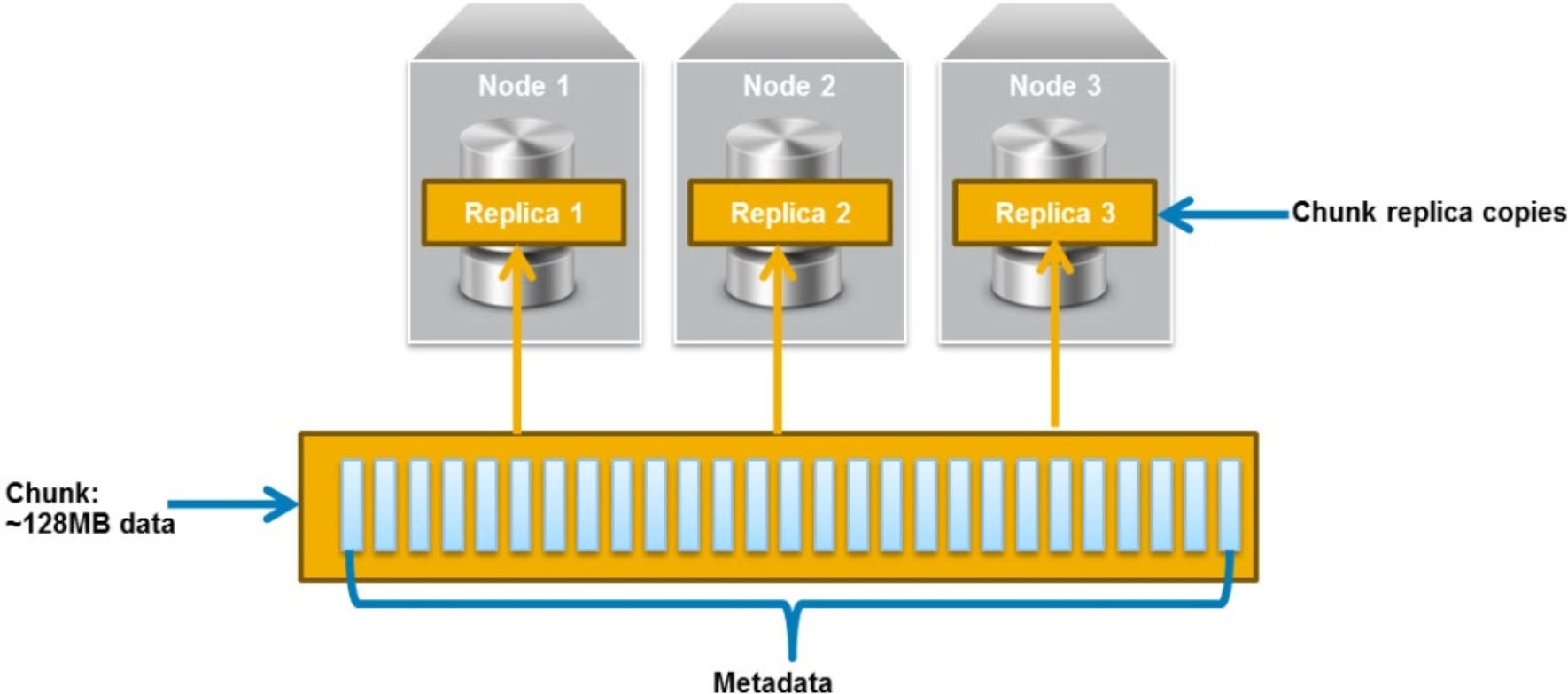
Figure 3. Triple mirroring
Erasure coding with redundant data segments
The erasure coding with redundant data segments write method is applicable to ECS btree chunks and custom object metadata. It includes 12 data segments, 12 replicated data segments, and 4 parity segments. The new btree chunk-redundant data EC scheme saves metadata protection overhead.
Triple mirroring plus in-place erasure coding
This write method is applicable to the data from any object that is less than 128 MB in size.
As an object is created, it is written to a chunk. ECS creates three replica copies of the chunk as follows:
- One copy is written in fragments that are spread across different nodes and disks. The distribution spreads the fragments across as many failure domains as possible. The size that gets written to each disk depends on the erasure coding scheme being used.
- If the erasure coding scheme is the default (12+4), each disk gets a maximum of ~10.67 MB
- If the erasure coding scheme is cold storage (10+2), each disk gets a maximum of ~ 12.8 MB
- A second replica copy of the chunk is written to a single disk on a node.
- A third replica copy of the chunk is written to a single disk on a different node.
This method provides triple mirroring and protects the chunk data against two-node or two-disk failures.
Other objects are written to the same chunk until it contains ~128 MB of data or after a predefined time. The Reed Solomon erasure coding scheme calculates coding (parity) fragments for the chunk and writes these fragments to different disks. This process ensures that all fragments within a chunk, including coding fragments, are written to different disks and distributed across failure domains.
Once the coding fragments have been written to disk, the second and third replica copies are deleted from disk. After this sequence is complete, the chunk is protected by erasure coding, which provides higher levels of availability than triple mirroring.
Inline erasure coding
This write method is applicable to the data from any object that is 128 MB or larger. Objects are broken up into 128 MB chunks. The Reed Solomon erasure coding scheme calculates coding (parity) fragments for each chunk. Each fragment is written to different disks and distributed across failure domains. The size that gets written to each disk depends on the erasure coding scheme being used.
- If the erasure coding scheme is the default (12+4), the fragments are spread across 16 disks, each fragment being ~10.67 MB.
- If the erasure coding scheme is cold storage (10+2), the fragments are spread across 12 disks, each fragment being ~ 12.8 MB.
Any remaining portion of an object that is less than 128 MB is written using the triple mirroring plus in-place erasure coding scheme. As an example, if an object is 150 MB, 128 MB is written using inline erasure coding. The remaining 22 MB is written using triple mirroring plus in-place erasure coding.
The following figure shows an example of how chunks are distributed across failure domains. This example has a single VDC/site that spans two racks, with each rack containing four nodes.
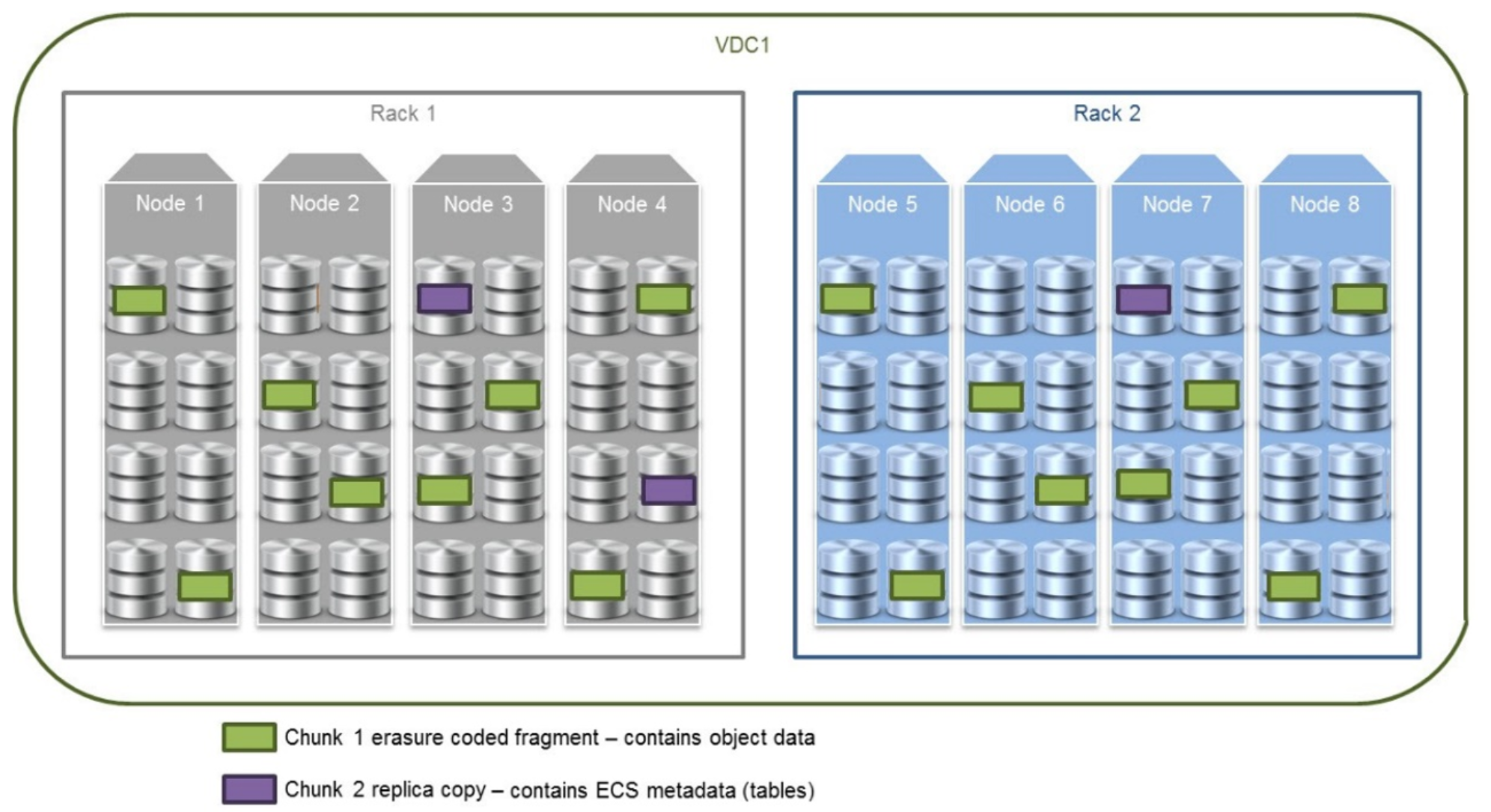
Figure 4. How chunks are distributed across failure domains
- Chunk 1 contains object data that has been erasure coded using an erasure coding of 12+4. Fragments are equally distributed across all eight nodes, four per rack. Each node contains two fragments, which it writes to two different disks.
- Chunk 2 contains ECS metadata (tables) and, thus, is triple mirrored. Each replica copy is written to a different node, each on a single disk. The copies span racks to provide the highest availability.
