Home > Storage > ObjectScale and ECS > Product Documentation > Dell ECS: Data at Rest Encryption > External key management
External key management
-
External Key Management support was added from ECS 3.3 onwards. It supports external key managers that are Key Management Interoperability Protocol version 1.4 (KMIP v1.4) compliant. Prior to ECS 3.6, the Master Key and the Rotation keys were generated and stored securely in the External Key Manager (EKM). Since ECS 3.6, only the Master Key is generated and stored securely in the EKM.
Table 1. Additional EKM supported for each release
ECS Release
Additional EKM supported
ECS 3.3
Safenet KeySecure (Gemalto Safenet)
ECS 3.4
IBM SKLM 3.0 (Security Key Lifecycle Manager).
ECS 3.6
Safenet KeySecure 8.11
ECS 3.8.0.1
Thales CipherTrust
Figure 3 shows the key hierarchy used in EKM. The principal difference from native key management is that generation and storage of the master key happens in EKM. Like native key management, the Master key is used to derive the virtual master key. Each namespace in ECS associates to a Namespace Key, and a virtual master key protects it. A virtual master key is a key that is derived from the Master Key and RT Data Encryption Key, and the virtual master key is never persisted to disks. All buckets within a namespace associate to a Bucket Key, and the corresponding Namespace Key protects the Bucket Key. Data for each object is encrypted using a unique object key, which is protected using a virtual bucket key. The virtual bucket key is derived from the Bucket and Rotation key and is not saved to disks.
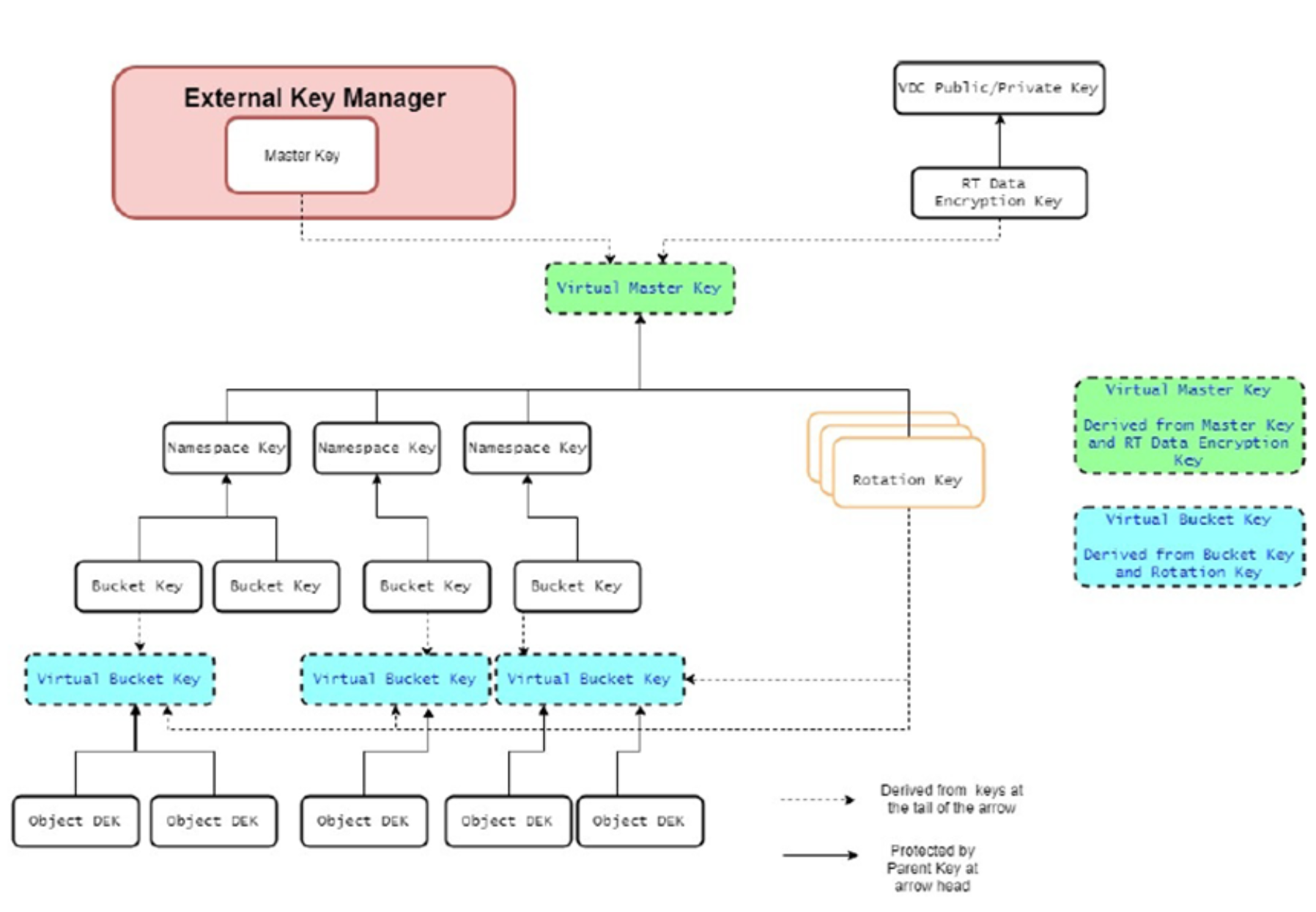
Figure 3. External key management key hierarchy
Figure 4 shows the location of EKM managed keys in ECS systems. The Master Key is generated and stored securely in the External Key Manager (EKM). The Namespace Key and Rotation Key are wrapped using AESKeyWrapRFC5649 by the virtual master key. The Bucket Key is wrapped using AESKeyWrapRFC5649 by the Namespace Key. These wrapped keys are stored in the Resource Table (RT) like the natively managed keys. The virtual bucket key wraps the object keys using AESKeyWrapRFC5649 and stores them in the object table.
Communication with EKMs is protected by mTLS using server and client certificates. When ECS persists or retrieves the keys, only the encrypted data is transported across nodes of a VDC or across VDCs. Decryption of key happens locally at each service that requires a specific key.
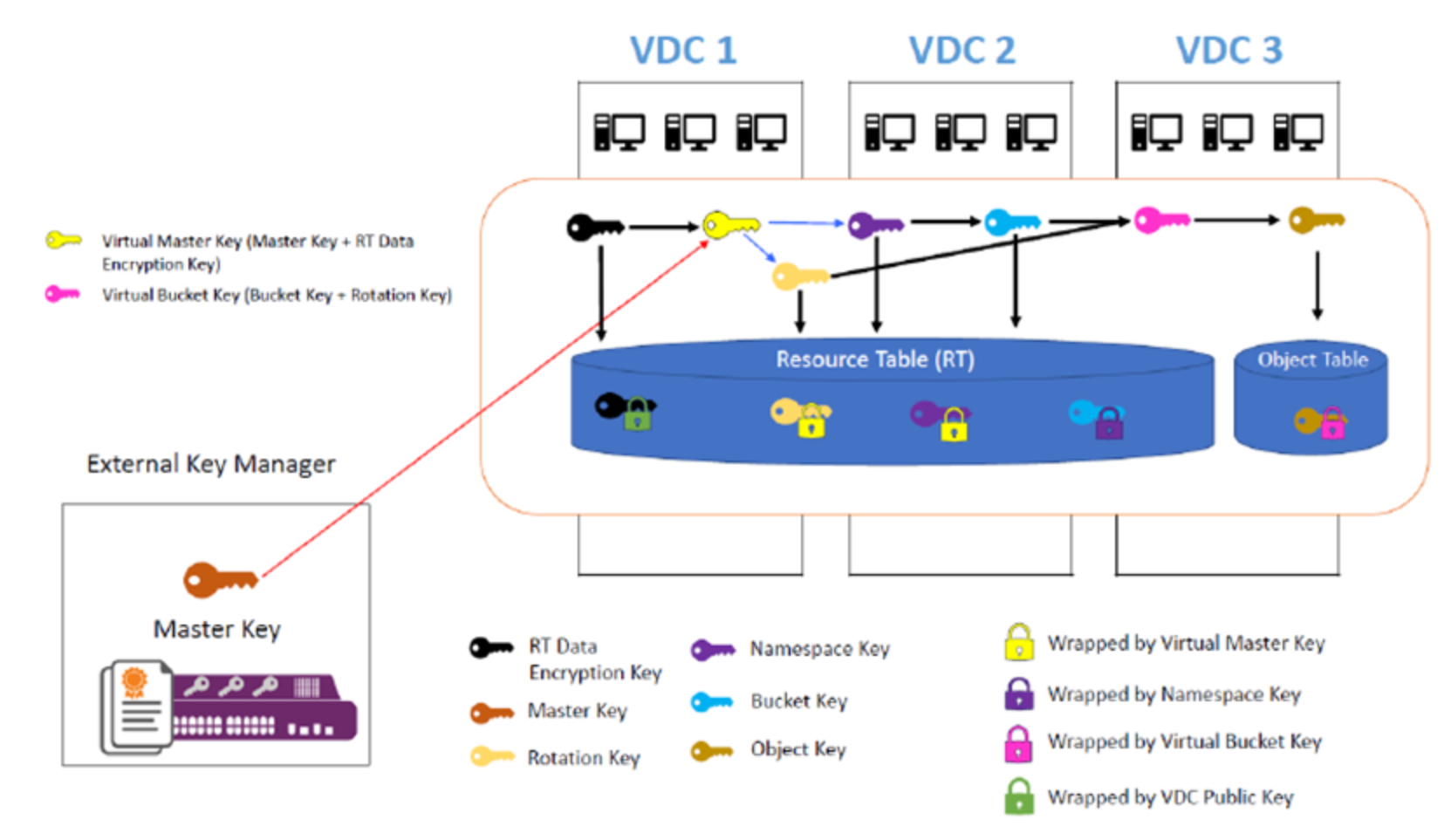
Figure 4. Storage Locations of EKM Managed keys
