Home > Storage > PowerFlex > White Papers > Dell APEX Block Storage for AWS: Deploying PostgreSQL on Dell PowerFlex > Solution overview and architecture
None
-
Introduction
Running mission-critical applications in the public cloud is gaining popularity with businesses. Part of the attraction to public cloud includes a robust set of software tools, services, and dynamic scale. These tools and services allow organizations to shift their focus from infrastructure to core competencies.
Dell APEX Block Storage for AWS provides the advantages of scale, performance, and a native feature set to enterprise applications, including local and remote replication, high availability (HA), resiliency, and CloudIQ security.
Dell APEX Block Storage for AWS can be rapidly deployed in AWS through a web portal that automates the initial deployment and used to expand an existing cluster making the process simple and quick. The scale-out design allows for independent storage and compute instances that can be spread across AWS Availability Zones (AZs) to provide higher resiliency even if an AZ is down. Dell APEX Block Storage for AWS provides a choice of Elastic Block Storage (EBS) for more flexibility, or native attached NVMe SSD drives for increased performance.
Solution overview
This solution describes the logical and network architectures for PostgreSQL deployment on Dell APEX Block Storage for AWS using Amazon EC2 instances. PostgreSQL deployment on Dell APEX Block Storage for AWS uses a bastion node that has access to both private and public subnets, allowing the database EC2 instances to use just the private subnet.
Logical architecture
The following figure shows the two-layer Dell APEX Block Storage for AWS system using an Amazon instance store (native attached NVMe SSD drives) deployed in a single availability zone.
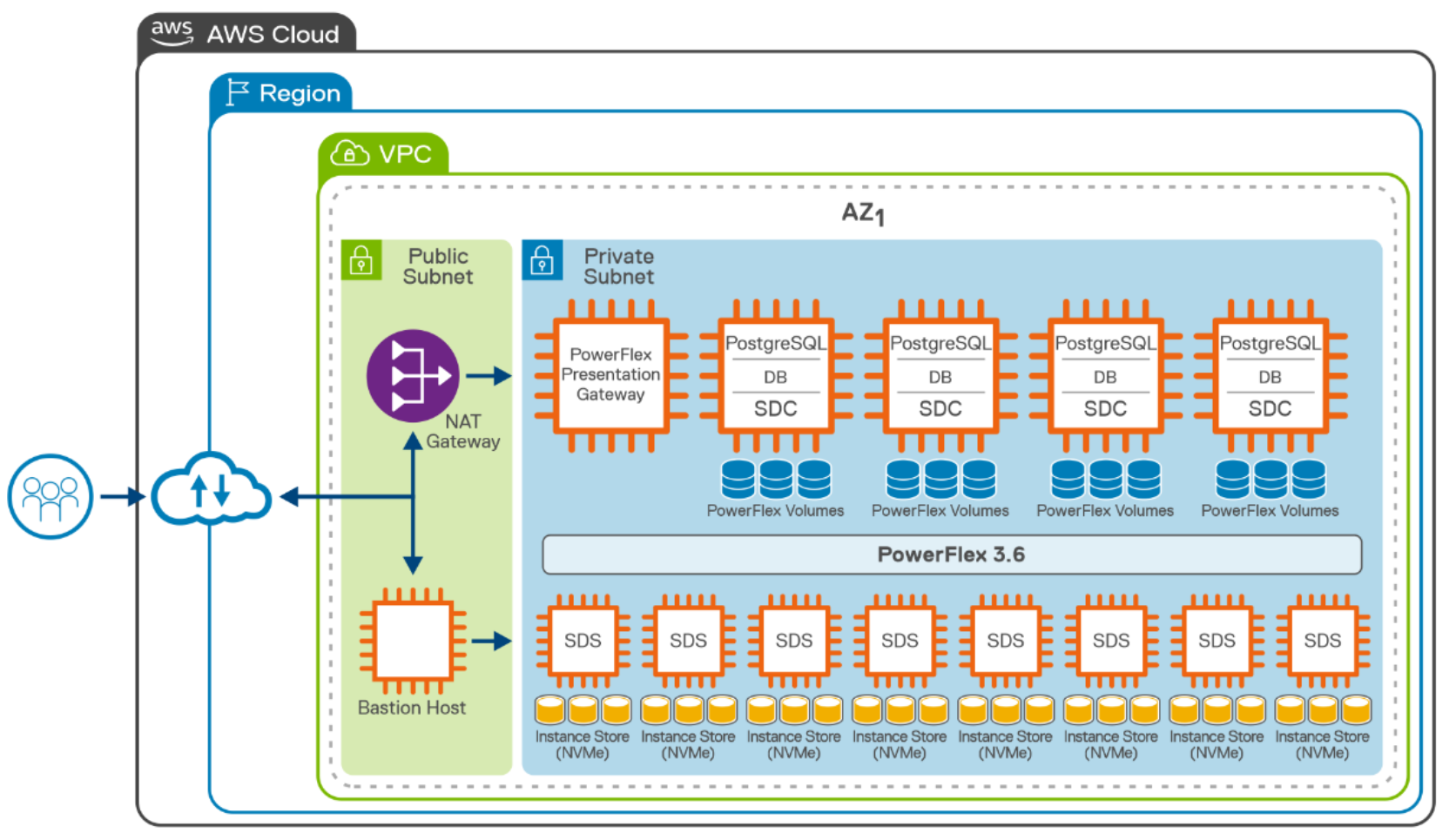
Figure 3. Logical architecture of PostgreSQL deployment on AWSThe SDS is installed on eight AWS EC2 instances of i3en.12xlarge type with Red Hat Enterprise Linux AMI. The EC2 instances that are deployed as storage nodes in AWS are backed by native NVMe SSD drives. The NVMe SSDs are locally attached at the instance level. The native attached NVMe SSD drives are ephemeral storage. Instances that are terminated will have the NVMe devices wiped, in accordance with AWS design.
There are eight SDS instances that are configured into a single protection domain. The storage devices from all the SDSs contribute to the overall capacity of nearly 75 TB of block storage.
Volumes of required capacity can be created and mapped to the database application. The data is maintained in a mesh mirrored layout so that each piece of data has two copies (primary and secondary) stored on two different storage optimized Amazon EC2 instances (SDS). The copies are evenly distributed across the SDS instances, which enable the system to maintain data availability and high performance if there is a failure of a storage device or Amazon EC2 storage optimized instance.
The PowerFlex cluster, gateway, and presentation server EC2 instances are installed in a private subnet range. A Windows bastion node has access to private and public subnet. The bastion node uses the Windows 2016 AMI for remote access of the instances in the private subnet as the workload stays entirely in private subnet.
Note: The bastion EC2 instance can use any operating system for administration purposes (such as Windows or Linux) with focus on security.
The following figure shows the Dell APEX Block Storage for AWS storage instances used for a two-layer deployment:
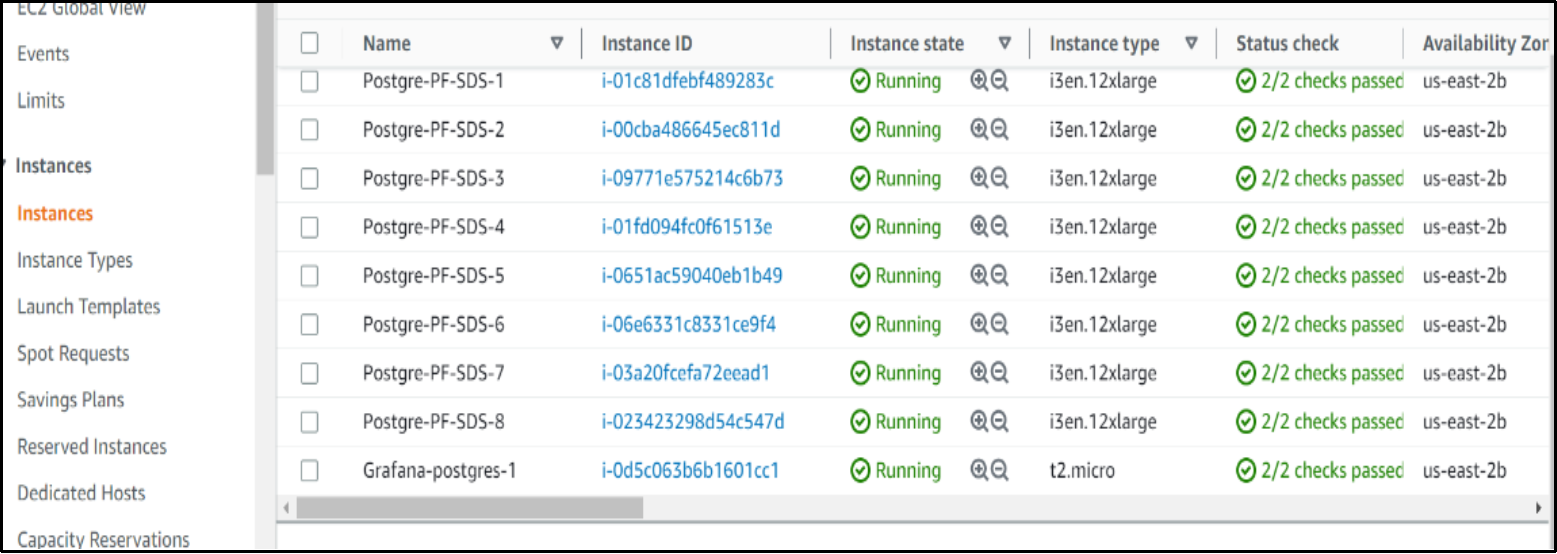
Figure 4. Amazon EC2 storage optimized instances (NVMe SSDs)The following figure shows the Dell APEX Block Storage for AWS compute instances that are deployed for a two-layer deployment:
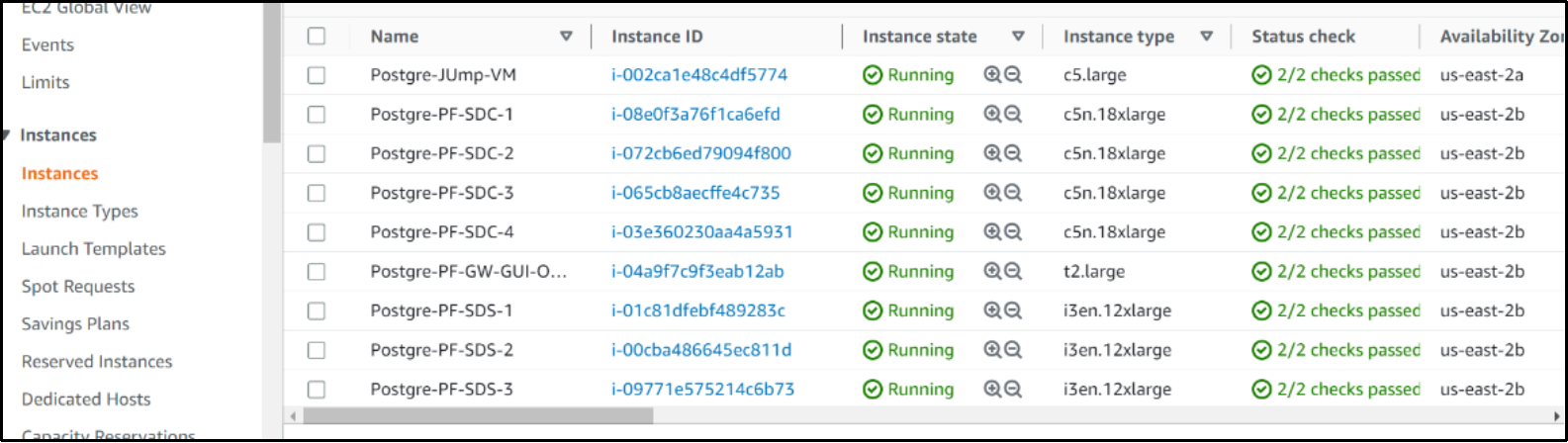
Figure 5. Amazon EC2 instances for compute (SDC)
The SDC is installed on each EC2 instance of type c5n.18xlarge. PostgreSQL database is deployed on these compute nodes within a private subnet that can access storage volumes for database workloads. AWS recommends allowing only application servers within the VPC or a bastion host within the VPC to access the database instances.
Network architecture
The following figure shows the network architecture for Dell APEX block storage deployed in a single Availability Zone within AWS region.
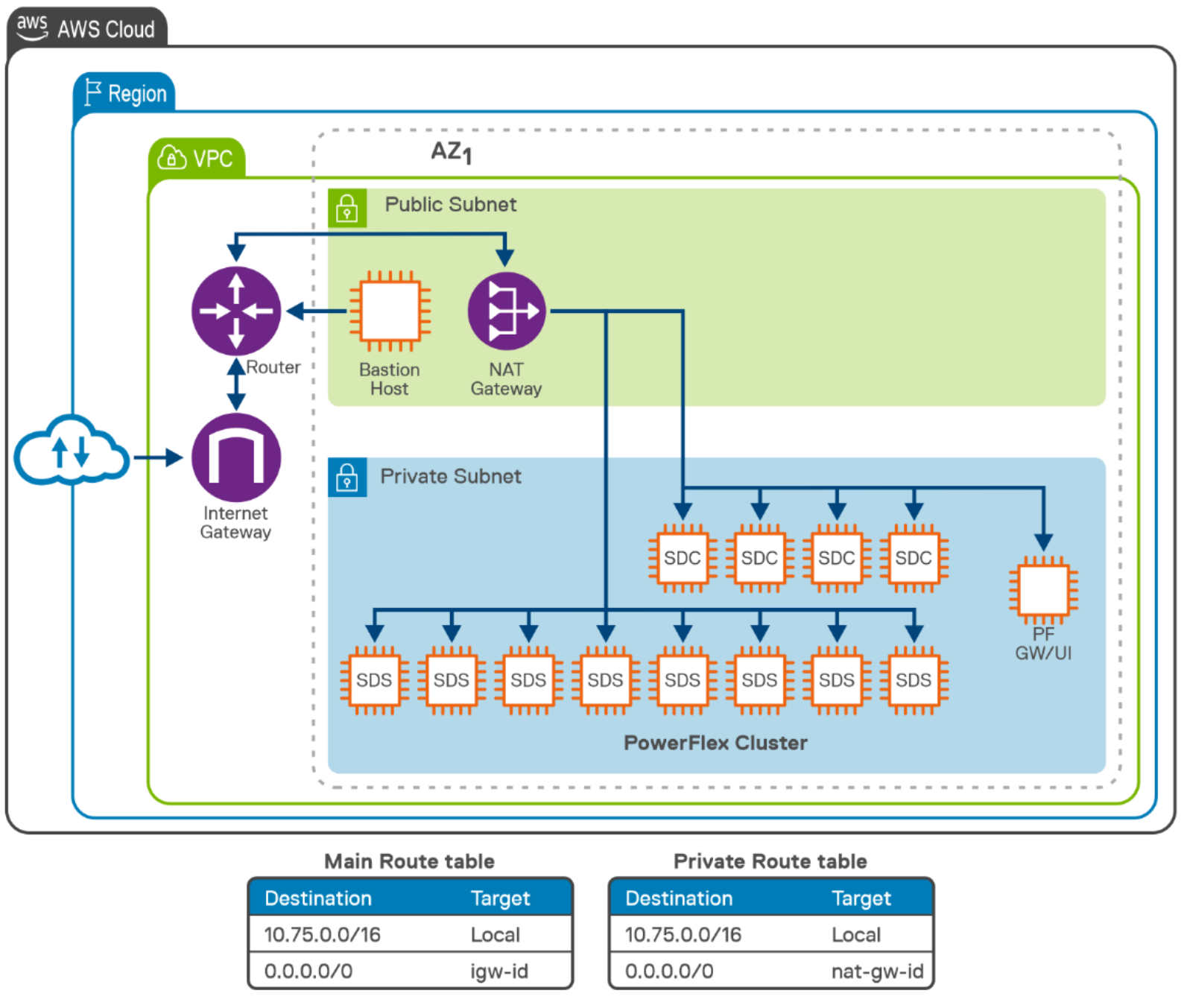
Figure 6. Network architecture on AWSThe above network architecture diagram shows the logical separation for the EC2 instance network to enable access to private and public subnets. A VPC is created in a region and private, and public subnets are also created in the chosen availability zone within that region. A security group is created to enable or customize inbound and outbound traffic rules at the subnet level. For Internet access, NAT gateway is configured that allows and routes traffic from the EC2 instance using the router that is created in the VPC.
In this example, the Dell engineering team created two separate routing tables:
- The main route table enables the public subnet to access the Internet through an Internet gateway.
- The private route table enables the private subnet to control the flow of traffic within the VPC.
It is recommended to use public subnets for external-facing resources and private subnets for internal resources. The bastion host has access to private and public subnets. The entire cluster is accessed through the bastion host, while the instances running the database workload stays entirely in the private subnet.
