Home > Storage > PowerScale (Isilon) > Product Documentation > Cloud > APEX File Storage for Microsoft Azure: Deployment Guide > Deploy APEX File Storage for Microsoft Azure
None
-
Overview
Before following the steps in this section, make sure you have met all the Prerequisites and fulfilled all the preparation work in the previous sections.
Prepare main.tf
The main.tf file is the main configuration file in a Terraform project and it invokes the OneFS module for deployment. The following is an example of the main.tf file:
module "powerscale" {
source = "dell/powerscale/azurerm"
version = "1.0.0"
subscription_id = var.subscription_id
image_id = var.image_id
cluster_name = var.cluster_name
cluster_nodes = var.cluster_nodes
max_num_nodes = var.max_num_nodes
node_size = var.node_size
os_disk_type = var.os_disk_type
data_disk_type = var.data_disk_type
data_disk_size = var.data_disk_size
data_disks_per_node = var.data_disks_per_node
smartconnect_zone = var.smartconnect_zone
external_nsg_name = var.external_nsg_name
external_nsg_resource_group = var.external_nsg_resource_group
external_subnet_name = var.external_subnet_name
hashed_root_passphrase = var.hashed_root_passphrase == null ? var.default_hashed_password : var.hashed_root_passphrase
hashed_admin_passphrase = var.hashed_admin_passphrase == null ? var.default_hashed_password : var.hashed_admin_passphrase
internal_nsg_name = var.internal_nsg_name
internal_nsg_resource_group = var.internal_nsg_resource_group
internal_subnet_name = var.internal_subnet_name
network_id = var.network_id
resource_group = var.resource_group
use_disk_encryption = var.use_disk_encryption
disk_encryption_set_name = var.disk_encryption_set_name
disk_encryption_set_resource_group = var.disk_encryption_set_resource_group
resource_tags = var.resource_tags
identity_list = var.identity_list
}
Note: Make sure you have the right source and version of the module. For a detailed explanation of other parameters and fields refer to the section - Terraform input variables.
Prepare terraform.tfvars
The terraform.tfvars file is used in Terraform to assign values to input variables that are declared in other configuration files, such as variables.tf. It externalizes variable definitions, allowing users to set specific values for variables without modifying the main configuration file directly. When running Terraform commands, such as terraform apply, the values from terraform.tfvars will be automatically used.
The following is an example of the terraform.tfvars file, which is used to create a 3-node cluster. For a detailed explanation of all the variables refer to the section - Terraform input variables.
# Subscription
subscription_id = "d9338087-1c11-49bd-9f55-904a2e52b491"
# Resource Group
resource_group = "playground"
# Cluster OS Information
cluster_name = "c1"
image_id = "/subscriptions/d9338087-1c11-49bd-9f55-904a2e52b491/resourceGroups/playground/providers/Microsoft.Compute/images/ga"
# Hashed Password (Default)
default_hashed_password = "$5$a1b2c3d4e5f6f7$dtfoem8FDBRPZpIY.vdU9NRxbSmWswJerIF3oQabRx."
# Cluster Scale
node_size = "Standard_D32ds_v5"
cluster_nodes = 3
max_num_nodes = 3
# Networking Information
smartconnect_zone = "foo.bar"
network_id = "/subscriptions/d9338087-1c11-49bd-9f55-904a2e52b491/resourceGroups/playground/providers/Microsoft.Network/virtualNetworks/vnet"
addr_range_offset = 5
external_subnet_name = "frontendSubnet"
internal_subnet_name = "backendSubnet"
data_disk_type = "Premium_LRS"
# Network Security Group
internal_nsg_name = "nsg"
internal_nsg_resource_group = "playground"
external_nsg_name = "nsg"
external_nsg_resource_group = "playground"
# Storage Configuration
os_disk_type = "Premium_LRS"
data_disk_size = 12
data_disks_per_node = 3
# Disk Encryption Configuration
use_disk_encryption = true
disk_encryption_set_name = "tmeDiskEncryptionSet"
disk_encryption_set_resource_group = "playground"
identity_list = ["/subscriptions/698d6dde-d358-40ee-b489-3d9900a3a157/resourceGroups/Thunder-cloud-rg /Microsoft.ManagedIdentity/userAssignedIdentities/demo-identity"]
Terraform input variables
Terraform lets you customize Terraform modules without altering the module's own source code. The Terraform module for APEX File Storage for Microsoft Azure supports the input variables listed in Table 6.
Table 6. Supported input variables for APEX File Storage for Microsoft Azure
Variable Name
Description
resource_group
The Azure resource group which will host the Azure resources for APEX File Storage for Microsoft Azure. See the section Azure Resource Group.
network_id
The URI of the Azure virtual network created in the section Azure Virtual Network and Subnets.
node_size
Azure virtual machine instance type. Possible values are described in the section Supported cluster configuration.
cluster_name
The name for APEX File Storage for Microsoft Azure.
cluster_nodes
The number of nodes that will be deployed for APEX File Storage for Microsoft Azure.
internal_subnet_name
Azure subnet for Internal/Backend network. See the section Azure Virtual Network and Subnets.
external_subnet_name
Azure subnet for External/Frontend network. See the section Azure Virtual Network and Subnets.
addr_range_offset
The offset of the starting IP address. It applies to both internal and external networks for APEX File Storage for Microsoft Azure. In the following example, the CIDR for the internal subnet is 172.21.23.32/27, the CIDR for the external subnet is 172.21.23.0/27 and the add_range_offset is 5, which means the starting IP for the internal network is 172.21.23.37 and the starting IP for the external network is 172.21.23.5.
Notes:
- Azure reserves the first five IP addresses in the subnet. In this case, it is 172.21.23.32 to 172.21.23.36 for the internal subnet and 172.21.23.0 to 172.21.23.4 for the external subnet.
- When you create a 2nd instance of APEX File Storage for Microsoft Azure, we recommend that you carefully review the parameter add_range_offset, leaving enough room for IPs where the 1st one can grow. Otherwise, you will see the IP overlap between the two instances.
max_num_nodes
The maximum number of nodes to which APEX File Storage for Microsoft Azure can scale-out.
default_hashed_password
Default hased password for both root and admin account
hashed_root_passphrase
Hashed root password for APEX File Storage for Microsoft Azure
cluster_admin_passphrase
Hasshed admin password for APEX File Storage for Microsoft Azure
image_id
The URI of the image file of APEX File Storage for Microsoft Azure. See the section Upload the image file to APEX File for more details.
smartconnect_zone
OneFS SmartConnect zone fully qualified domain name (FQDN)
identity_list
Azure managed identity
Important: If you plan to enable the OneFS network failover features like SmartConnect, dynamic IP pools, and so on, you must follow the steps in the section Azure Managed Identity and specify the URI of the identity to this parameter.
os_disk_type
Disk type for Operating System (OS). Possible values are:
- Standard_LRS
- StandardSSD_LRS
- Premium_LRS
data_disk_type
Data disk type. Possible values are:
- Standard_LRS
- StandardSSD_LRS
- Premium_LRS
data_disk_size
Data disk size in GB.
data_disks_per_node
The number of data disks per node.
timezone
Timezone for APEX File Storage for Microsoft Azure
internal_nsg_name
Azure Network Security Group (NSG) for internal/backend network.
internal_nsg_resource_group
The Azure resource group for internal NSG
external_nsg_name
Azure Network Security Group (NSG) for external/frontend network.
external_nsg_resource_group
The Azure resource group for external NSG
use_disk_encryption
Type of disk encryption, possible values are:
- true: use CMK
- false: use PMK
Note: disk_encryption_set_resource_group and disk_encryption_set_names are only valid when use_disk_encryption is set to true.
disk_encryption_set_resource_group
The Azure resource group for the disk encryption set
disk_encryption_set_name
The name of the disk encryption set.
Parameter image_id and network_id
To get the value of the parameters image_id and network_id, navigate to the overview page of Azure image and virtual network:
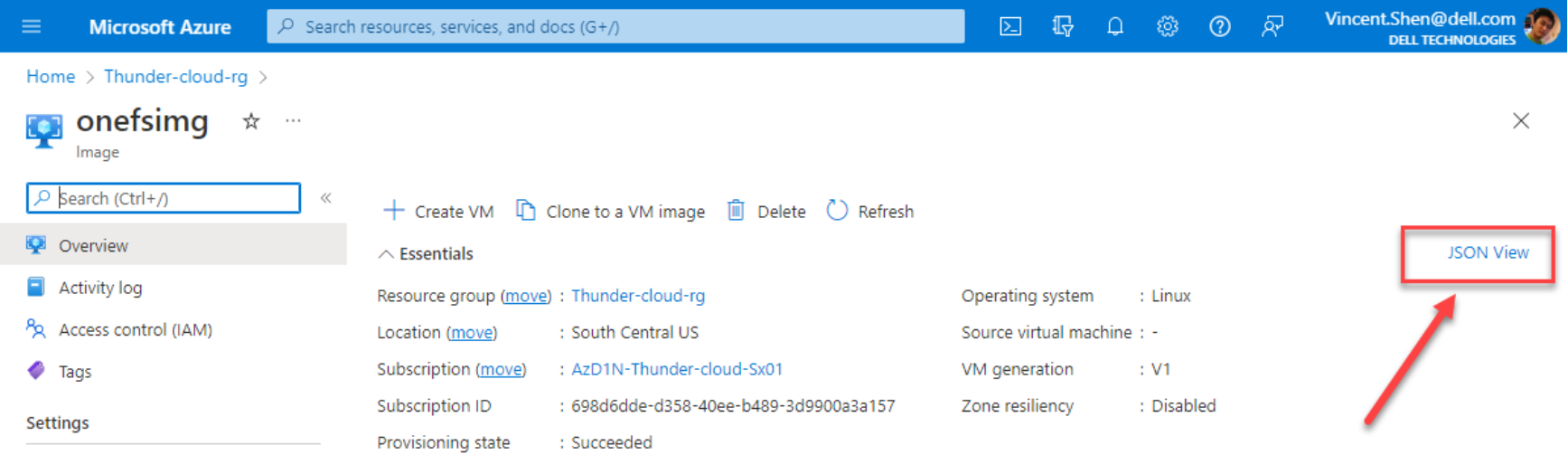
Figure 15. Overview page of image file for OneFS
Click the link JSON View, and click Copy to clipboard:
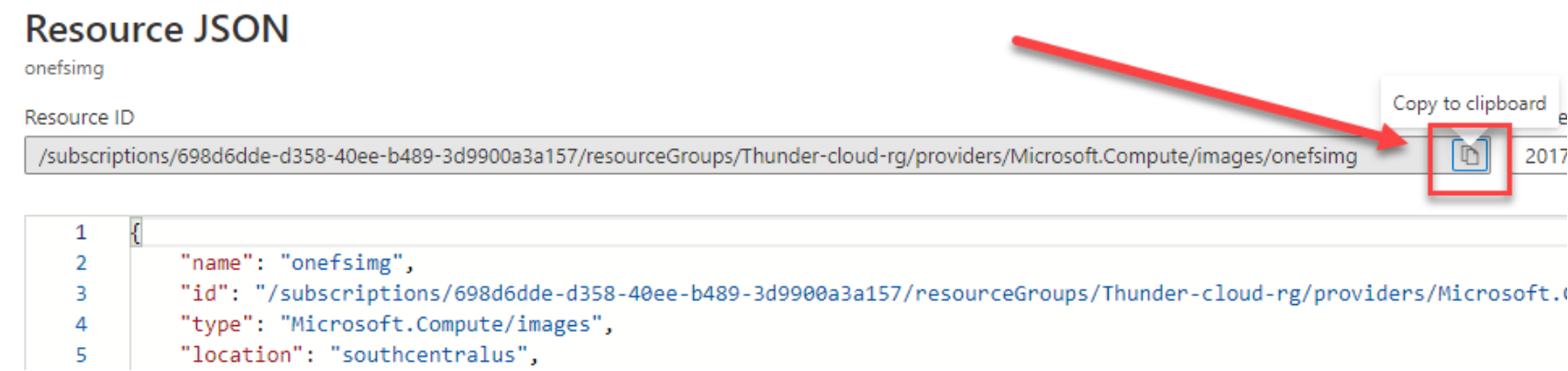
Figure 16. Copy URI of image file for OneFS
Hashed admin or root password
On using the default_hashed_password input parameter, both the root and admin users will be assigned the same password as provided in default_hashed_password.
To use different passwords for the root and admin, an end-user can specify hashed_root_passphrase and hashed_admin_passphrase respectively.
To generate the hashed password, use the following command:
openssl passwd -5 -salt `head -c 8 /dev/random | xxd -p` "<replace-password-here>"
In the above command, head -c 8 /dev/random | xxd -p is used to generate an 8 byte random string in its hexadecimal representation which is used as the salt for producing the hashed output.
Disk Encryption
By enabling disk encryption via setting the use_disk_encryption input parameter to true, it is possible to use an existing disk encryption set in Azure to encrypt both the OS disks and data disks created by Terraform.
Note that the name of the existing disk encryption set and the resource group it is located in will need to be added to the disk_encryption_set_name and disk_encryption_set_resource_group input parameters respectively.
Initialize Terraform
Initialize the Terraform configuration, where it configures the backend, installs all required providers and modules used in the Terraform script, and creates a lock file if it does not already exist. To do that:
- At a Command Prompt, change to the directory where the Terraform scripts are located.
- Run the command:
>terraform.exe init
- If everything goes fine, you will see the following message:
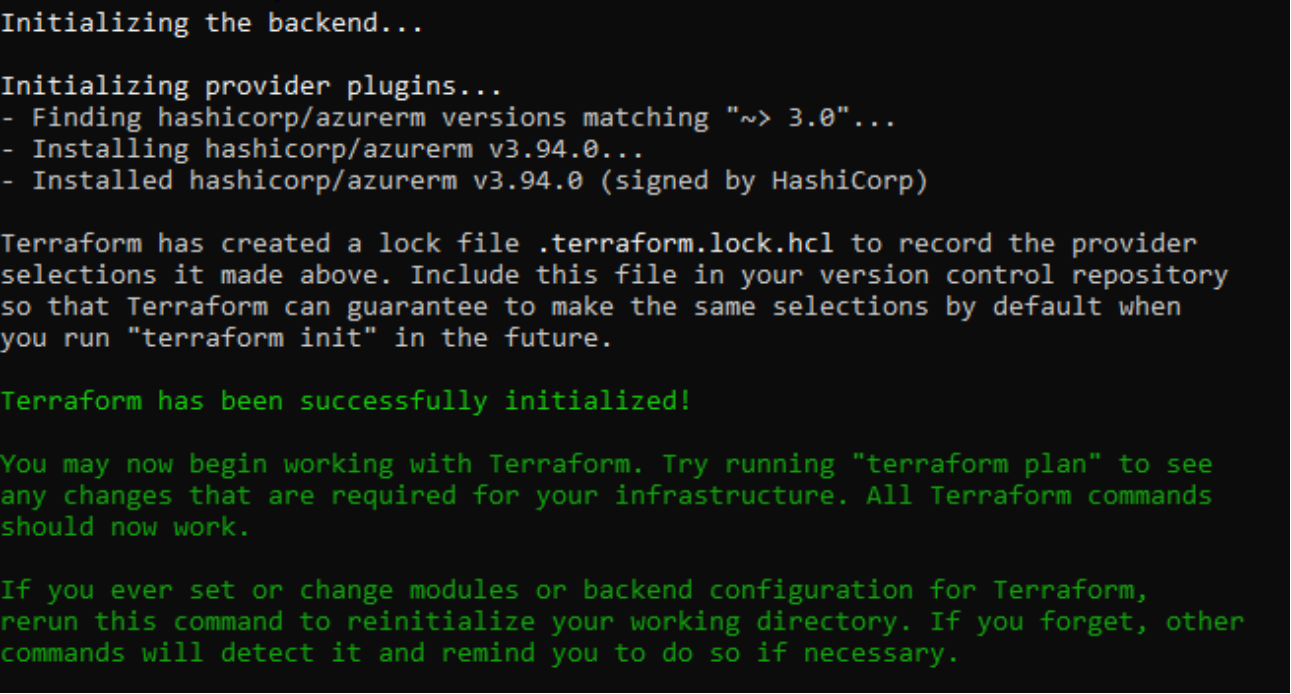
Figure 17. Successful message
- To validate your configuration, use the following command:
>terraform.exe validate
APEX File Storage for Microsoft Azure Deployment
To deploy an instance of APEX File Storage for Microsoft Azure, run the following commands:
# terraform apply
- Enter yes after you have previewed and confirmed the changes.
Do you want to perform these actions?
Terraform will perform the actions described above.
Only 'yes' will be accepted to approve.
Enter a value: yes
- When the deployment is complete, output similar to the following appears:
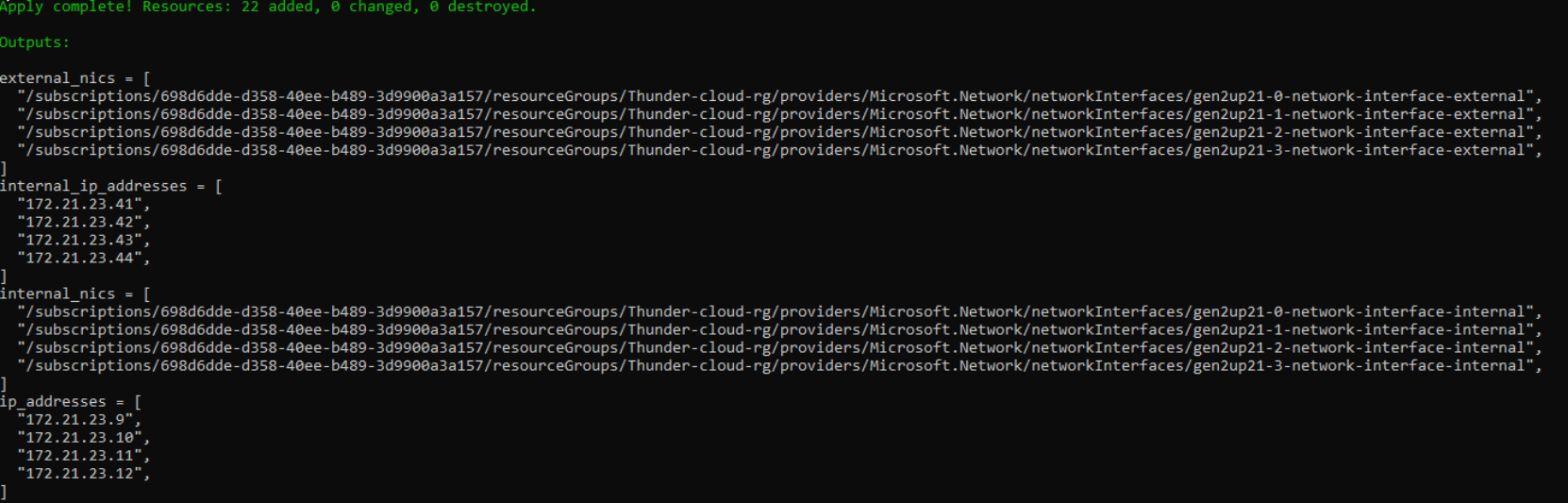
Figure 18. Terraform output after the success
Note: After the deployment completes, the nodes will not be immediately available, because they will undergo an automatic configuration process to form a cluster, which requires a few minutes.
- In this example, you can use the IPs from ip_addresses in Figure 18 to connect to your APEX File Storage for Microsoft Azure.
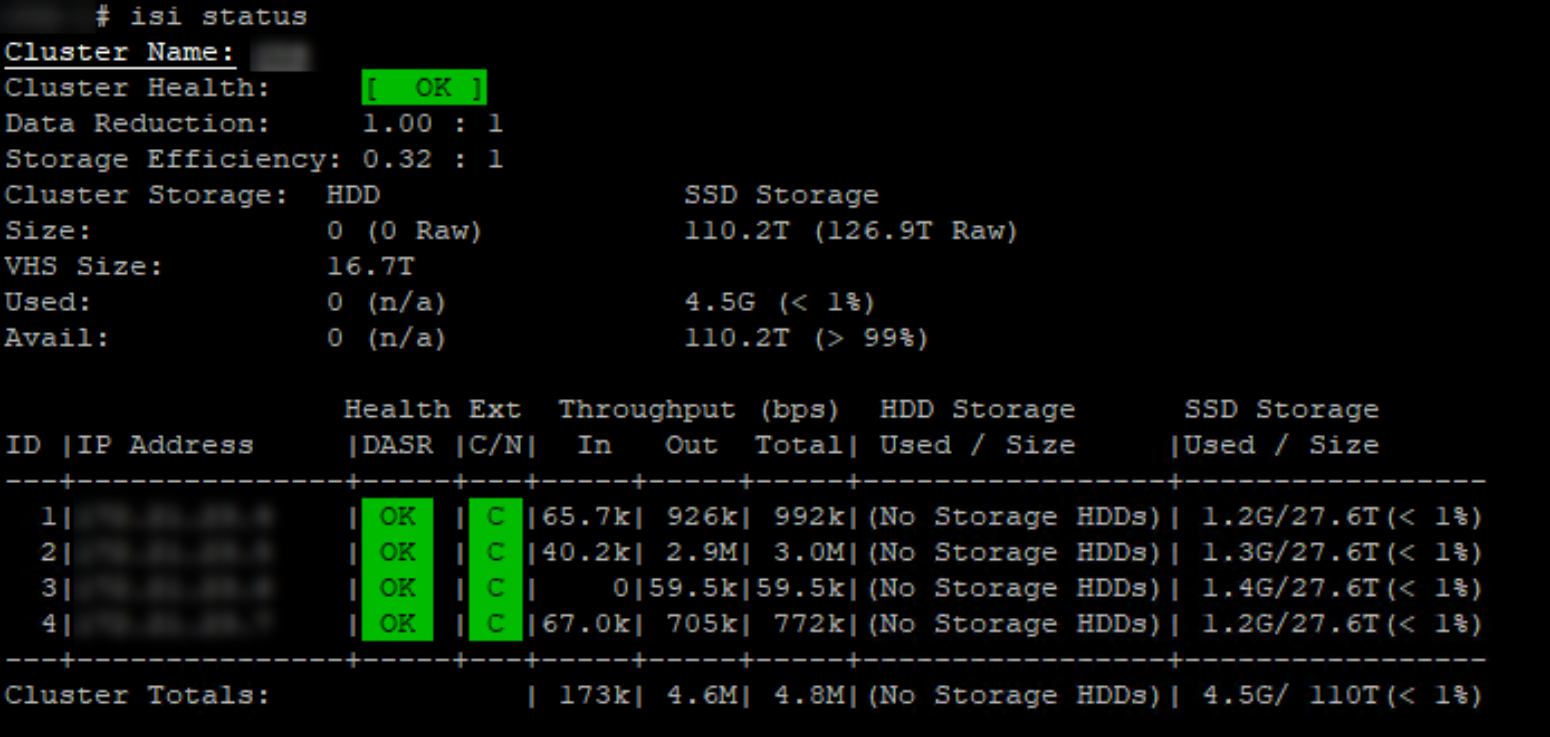
Figure 19. Cluster status for APEX File Storage for Microsoft Azure
Note: There is a known issue that the inline deduplication and inline compression feature is not enabled by default at the disk pool level. The first major release (MR) will fix it after GA. You can also reach out to your sales representative if you need an immediate fix.
