Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Access Control Lists on Dell EMC PowerScale OneFS > OneFS user mapping
OneFS user mapping
-
When OneFS authenticates a user, it generates an access token and triggers the user-mapping service on the cluster. The user-mapping service combines access tokens from different directory services into a single, final access token. By default, OneFS automatically maps user accounts with the exact same name from different directory services. For example, the user-mapping service maps a user DEMO\janed from Microsoft Active Directory to a user janed from LDAP and generates an access token that combines the user and group membership information from the two accounts.
A OneFS administrator can also define their own user-mapping rules to control the user-mapping behavior. It is important to know the following information when creating user-mapping rules:
- User-mapping rules are applied at the access-zone level. You can only create user-mapping rules for specific access zone if you are connected to the OneFS System access zone.
- When changing user-mapping rules on one node, OneFS will propagate the change to the other nodes.
- OneFS reloads the configuration when user-mapping rule changes occur.
There are five operations involved when creating user-mapping rules:
- Insert fields from a user: This modifies an existing access token by adding fields to it. Fields specified in the options list (user, group, or groups) are copied from new identity and inserted into the identity in the token.
- Append field from a user: This also modifies an access token by adding fields to it. The mapping service appends the fields that are specified in the list of options (user, group, or groups) to the first identity in the rule. All appended identifiers become members of the supplemental groups list.
- Replace one user with a different user: This removes the token and replaces it with a new token that is identified by the second username.
- Remove supplemental groups from a user: This modifies an access token by removing the supplemental groups.
- Join two users together: This inserts the new identity into the token. This operation combines two user access tokens together into a single access token containing the information from both users.
For details on configuring user-mapping rules, refer to the PowerScale OneFS Web Administration Guide.
The example in Figure 36 shows the result after joining two users together. In this example, user01 from PowerScale local is joined with demo\janed from Active Directory.
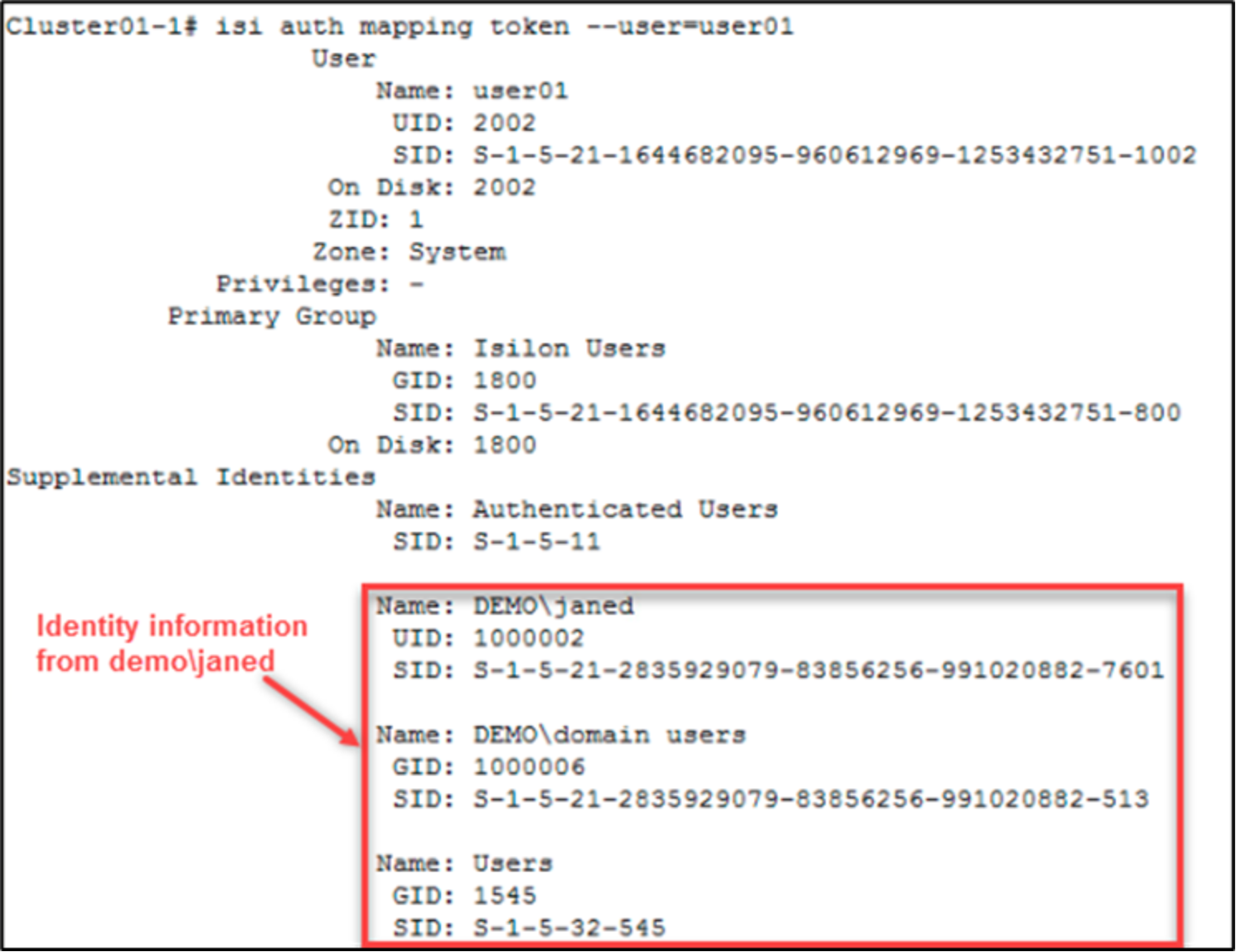
Figure 36. OneFS user mapping
The next example in Figure 37 assumes there is a directory which does not allow user01 to access the directory, but allows demo\janed to read the directory.
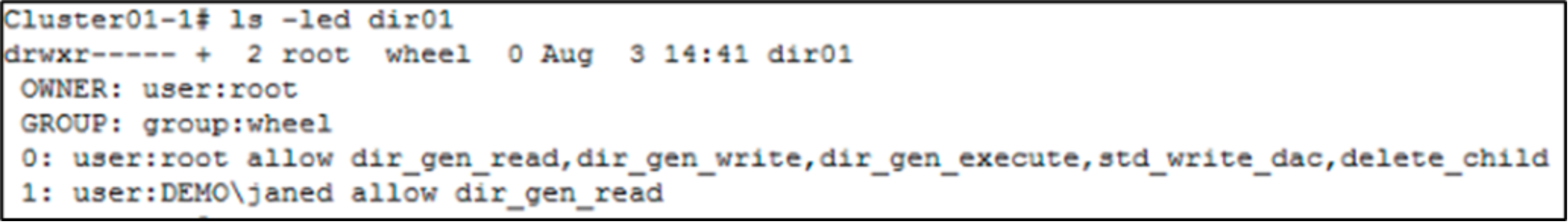
Figure 37. ACL of the directory
Because there is a user-mapping rule to join the two users together, using the isi command to check permissions of user01 on the directory shows that user01 also has permission to read the directory (see Figure 38). This command result only evaluates the ACL permission and does not involve the share-level permissions.
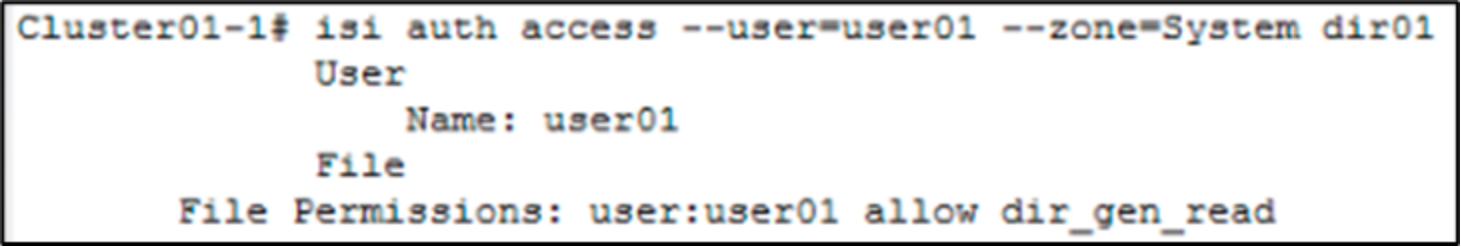
Figure 38. Effective permissions of user01
