Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Access Control Lists on Dell EMC PowerScale OneFS > NFS export and SMB share settings
NFS export and SMB share settings
-
The following settings are checked before on-disk permission checking and can impact a user’s effective permission on a file.
- Root or non-root user mapping and map lookup UID options of a NFS export
- SMB share permission settings which restrict users to accessing a SMB share
NFS export map options
Root or non-root user mapping
By default, an NFS export on OneFS maps the root user to the nobody user, an unprivileged user account. In this way, a remote root user on the client does not get the root permission on the file system. This behavior is also known as root squash. OneFS also allows mapping other non-root users to a specific user that is used to access the files. By default, this setting is disabled. When enabling the non-root user mapping, all the permission checking is based on the new user that you specify, so when a client user gets the wrong permission to the export files, it is likely that the export user mapping setting is enabled.
Viewing and changing the NFS export mapping settings is performed through the Web UI (shown in Figure 34) or the isi nfs exports modify command.
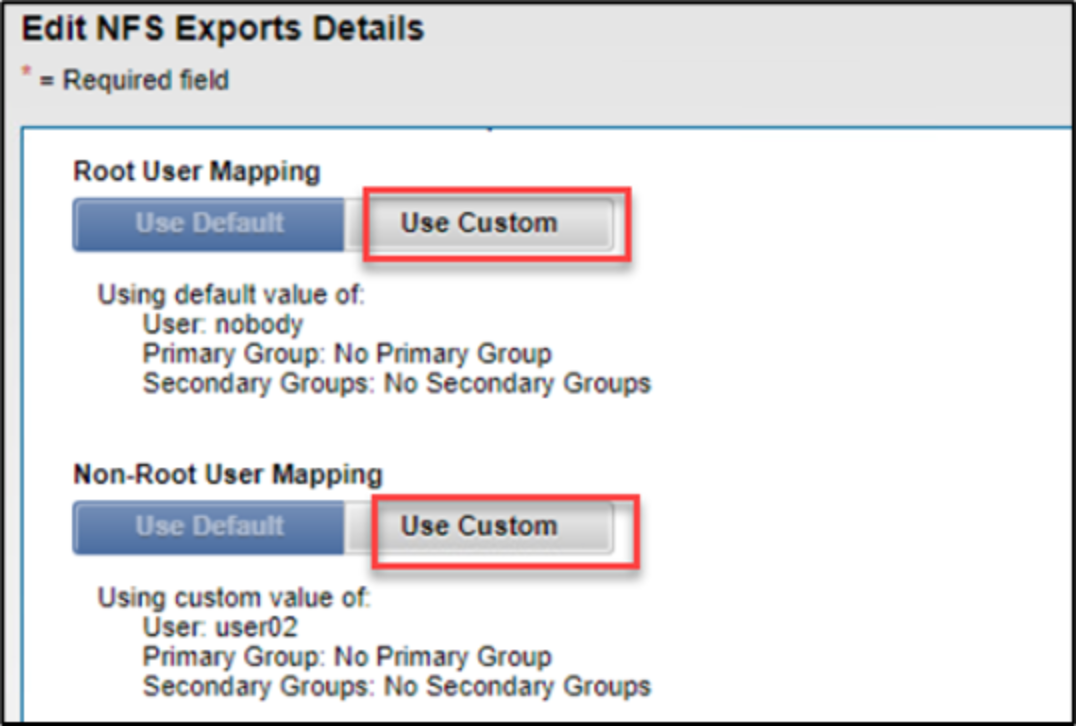
Figure 34. Export user mapping
Map lookup UID option
When an NFS client sends a series of calls to a server, the NFS RPC header contains the following information:
- User UID
- One primary GID
- Up to 15 supplemental GIDs
By default, when a server receives this list of GIDs, it trusts the GIDs are complete and checks the file-system permissions using only these GIDs.
When using the NFS AUTH_SYS authentication security type and a user is a member of more than 16 groups, the permissions may be improperly applied. This is a limitation of NFS in which a request is sent to a server from a client, the GID list sent by the client is truncated, and only a portion of group information is sent to the server. For example, userA belongs to group20, and group20 has access to a file. Group20 is truncated because it exceeds the 16-group limit and userA is denied access by the NFS server. Conversely, if the group is denied access to the file, the user would be allowed to access the file by accident.
To eliminate this limitation, OneFS provides an NFS export option called map-lookup-uid. By default, it is disabled. Once it is enabled, OneFS will not trust the GID information received from client. It will only look at the user’s UID and ignore the GIDs. Then, OneFS performs a lookup of the UID in the connected authentication providers (local, NIS, LDAP, or RFC-2307-enabled AD) to determine group membership. Finally, OneFS performs the permission checking based on the result of the lookup.
The map-lookup-uid option is enabled using the WebUI or isi command. It is more convenient to enable it using the following command: isi nfs exports modify exportID –-map-lookup-uid=true.
SMB share permission
As a user traverses an SMB path on an PowerScale cluster, the first location that the user can be denied access is at the share level. When the share permission is combined with on-disk permission (POSIX mode bits or ACLs), the more restrictive permission always applies. For example, if the share permission is set to allow everyone read access, and the on-disk permission allows users to read and write. Finally, the share permission applies and the user is not allowed to change a file.
To view the share permission, use either the WebUI or isi command. As Figure 35 shows, everyone on the default ifs SMB share has full control at the share level, and the effective permission is determined by on-disk permissions.
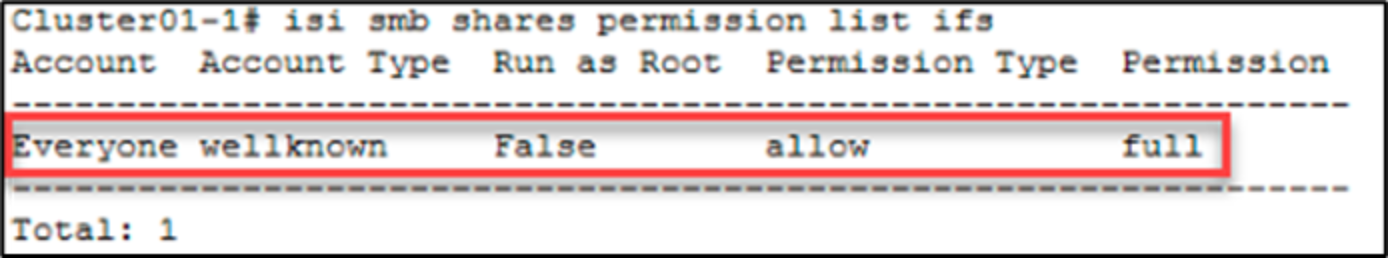
Figure 35. SMB share permission
Note: OneFS allows administrators to enable the run-as-root option on an SMB share permission. This option is disabled by default. When enabled, a user has root access to files and directories under the share.
