Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Access Control Lists on Dell EMC PowerScale OneFS > Data backup and restore privileges
Data backup and restore privileges
-
OneFS provides a role-based access control (RBAC) model to delegate administrative tasks to specific users. RBAC roles are assigned privileges and then assigned members. All users that are assigned to a role must connect to the system access zone to configure and manage the cluster. OneFS includes several integrated roles with predefined privileges and cannot be modified. You can also create custom roles to fit your environment.
Most privileges in the RBAC system pertain to allowing changes to cluster configuration. Two privileges (ISI_PRIV_IFS_BACKUP and ISI_PRIV_IFS_RESTORE) were added in OneFS 7.1.1 and later, which allow access to cluster data. When a user is a member of a role with either or both ISI_PRIV_IFS_BACKUP or ISI_PRIV_IFS_RESTORE privileges, the user can circumvent traditional file access checks (POSIX mode bits or ACLs) to back up or restore file data. These two privileges are supported over the following protocols: SMB, NFS, OneFS API, FTP and SSH.
Circumventing traditional file access checks is done by adding a combination of privileges and flags to the user's access token during authentication. For NFS, it requires the export enable --map-lookup-uid option. For SMB, these two OneFS privileges emulate the Windows privileges SE_BACKUP_NAME and SE_RESTORE_NAME, which means that normal file opens are still protected by file-system permissions. To enable the backup and restore privileges over the SMB protocol, files must be opened with the FILE_OPEN_FOR_BACKUP_INTENT option. When users employ Windows backup software such as Robocopy, the option is applied automatically. When users perform general file browsing using Windows File Explorer, the option is not applied.
You can assign the BackupAdmin role to a user in the system access zone by using the WebUI (shown in Figure 32) or the isi auth role command.
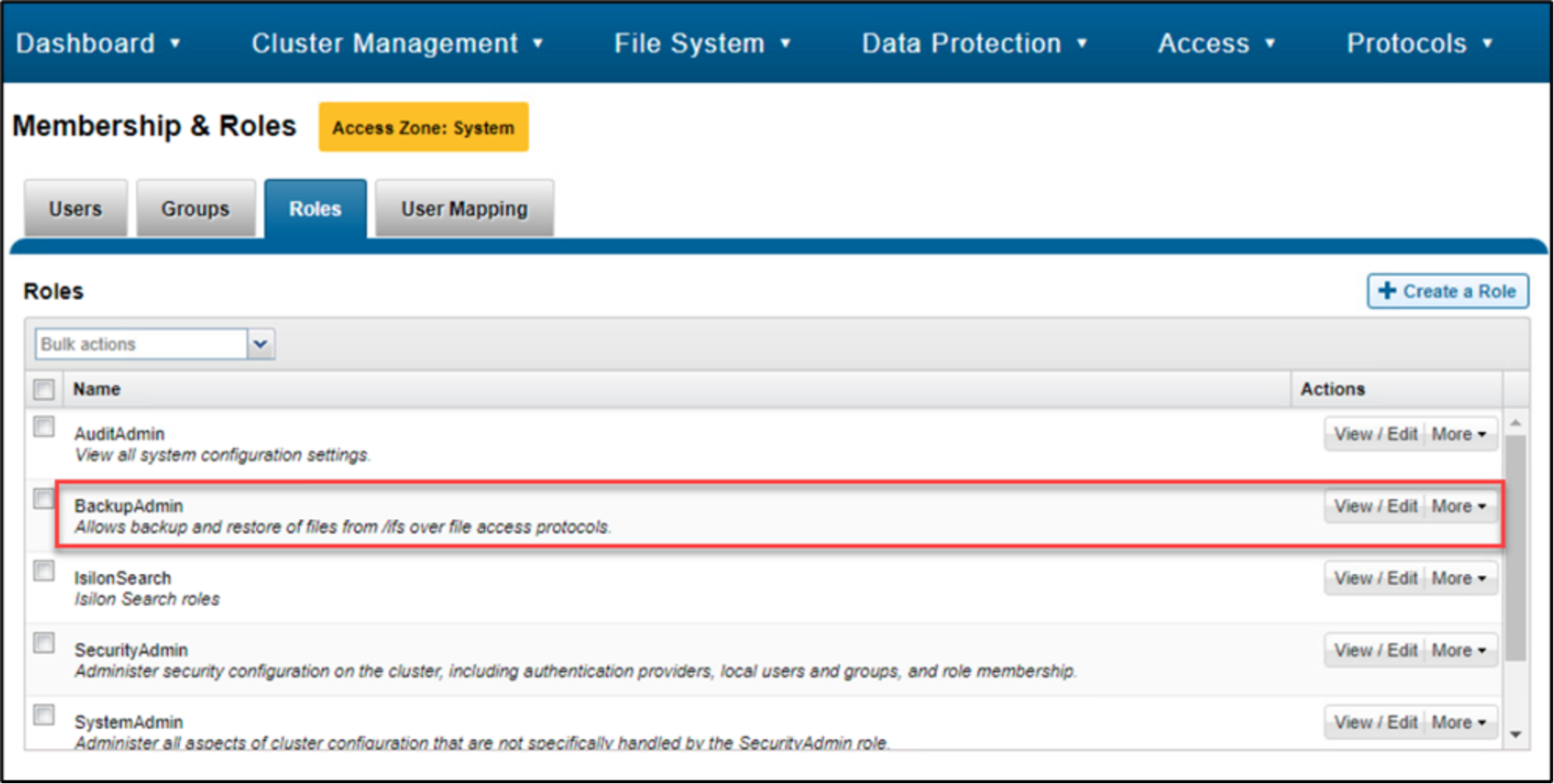
Figure 32. Role configuration WebUI
To verify if a user has the ISI_PRIV_IFS_BACKUP and ISI_PRIV_IFS_RESTORE privileges, use the command isi auth user mapping token. An example is shown in Figure 33.
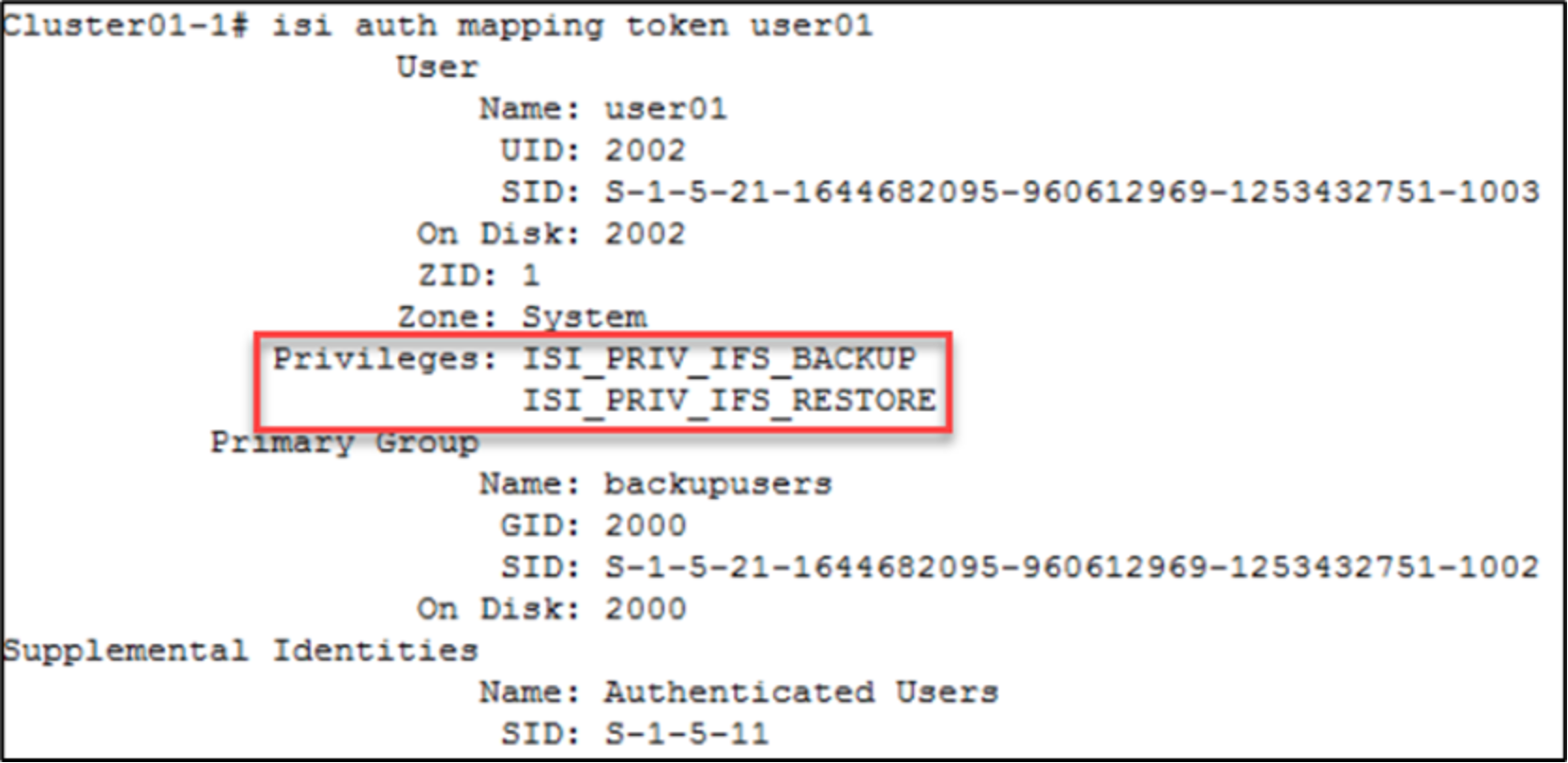
Figure 33. Verify user privileges
