Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Access Control Lists on Dell EMC PowerScale OneFS > ACL policy in OneFS
ACL policy in OneFS
-
All of the previous examples are based on the default OneFS cluster ACL policy. The ACL policy is a cluster global setting and is not access-zone aware. It controls how permissions are processed and managed. For example, with default policy settings, OneFS ACL entries are not inheritable and can be created through the SMB or NFSv4 protocols. New permissions added by chmod command will be merged with a file’s original ACL.
The ACL policy setting is divided into two categories: general ACL settings and advanced ACL settings.
OneFS has three default, predefined policies:
- Balanced: This default setting enables the OneFS cluster to operate in a mixed environment including UNIX and Windows.
- UNIX only: This policy provides UNIX semantics to OneFS.
- Windows only: This policy provides Windows semantics to OneFS.
Users can also configure both general and advanced ACL policy options manually to fulfill their requirements. However, it is not recommended to modify these options at will unless they are well understood and tests are conducted before applying changes to production environments. For the complete list of available options, refer to section 9 of the PowerScale OneFS Web Administration Guide. Error! Reference source not found. shows the differences between the three predefined policies.
Table 5. Predefined ACL policies
ACL policy option
ACL policy option value
Balanced
UNIX only
Windows only
ACL creation through SMB
Allow ACLs to be created through SMB
Use the chmod command on files with existing ACLs
Merge the new permissions with the existing ACL
Remove the existing ACL and set UNIX permissions instead
Deny permission to modify the ACL
Use the chown and chgrp commands on files with existing ACLs
Modify the owner or group and the ACL permissions
Modify only the owner or group
Allow the file owner and users with WRITE_DAC and WRITE_OWNER permissions to change the mode or owner of the file (Windows model)
Allow only the file owner to change the mode or owner of the file (UNIX model)
ACL creation through SMB
When ACL creation through SMB is enabled, a OneFS real ACL is created when a new file is created over SMB. OneFS ACL can be modified with Windows Explorer commands. If creating ACLs through SMB is not allowed, when modifying the ACL through SMB in Windows, the modification will not be applied on the OneFS side.
This example uses the balanced default ACL policy and creates a new directory smb_dir through SMB in Windows using the account demo\janed. Shown in Error! Reference source not found., the OneFS real ACL is created.
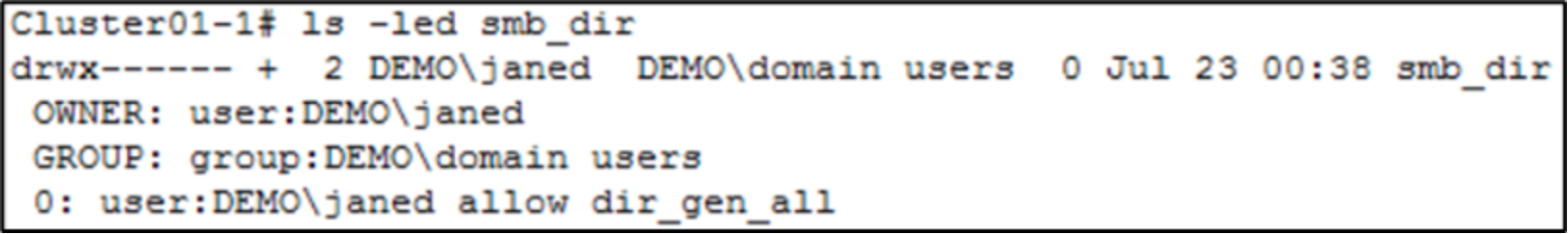
Figure 16. OneFS real ACL created through SMB
If not allowing ACLs to be created through SMB, repeat the prior procedure. The newly created directory only has POSIX mode bits and an associated synthetic ACL. See Figure 17.
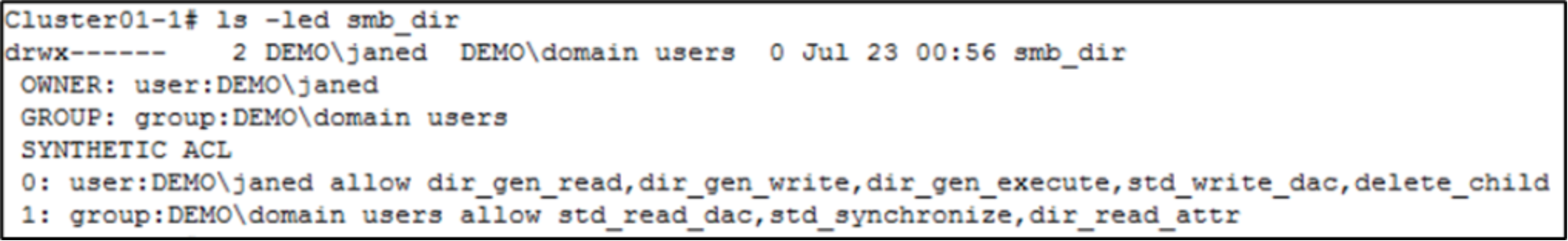 7.
7. Figure 17. ACL creation through SMB disabled
Use chmod command on files with existing ACLs
This command has six options to control permissions when running traditional chmod command on files with a real ACL. Error! Reference source not found. shows the options and descriptions.
Table 6. Chmod options on OneFS
Option
Description
Remove the existing ACL and set UNIX permissions instead
This option can cause information from ACLs to be lost, especially when SMB is used in the environment.
Remove the existing ACL and create an ACL equivalent to the UNIX permissions
This option also causes ACL information to be lost, although the option can create UNIX permissions instead.
Remove the existing ACL and create an ACL equivalent to the UNIX permissions, for all users or groups referenced in the old ACL
This option improves matters over the first two settings because it preserves the access of all the groups and users who were listed in the ACL.
Merge the new permissions with the existing ACL
This option merges the new permissions with the ACL, and is the recommended setting in a mixed environment because it best balances the preservation of security with the expectations of users.
Deny permission to modify the ACL
This option can cause the owner of a file to be unable to change its permission on the file.
Ignore the operation if the file has an existing ACL
Nothing will be modified on the exiting ACL.
Figure 18 shows the results of the default settings. When adding new permissions with chmod, the original ACL information is not lost and the new permission is merged.
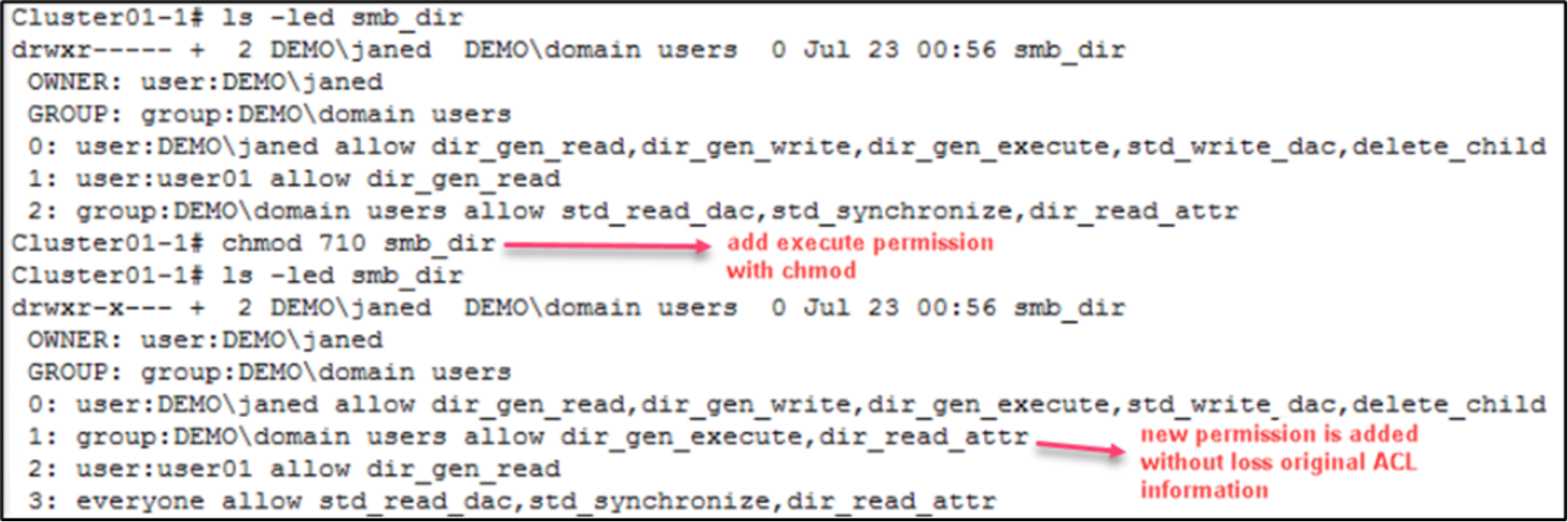
Figure 18. Merge newly added permission
Repeating the same procedure under the UNIX only policy, the original ACL information is removed as shown in Figure 19. If the same operation is performed under the Windows only policy, a permission denied prompt occurs.
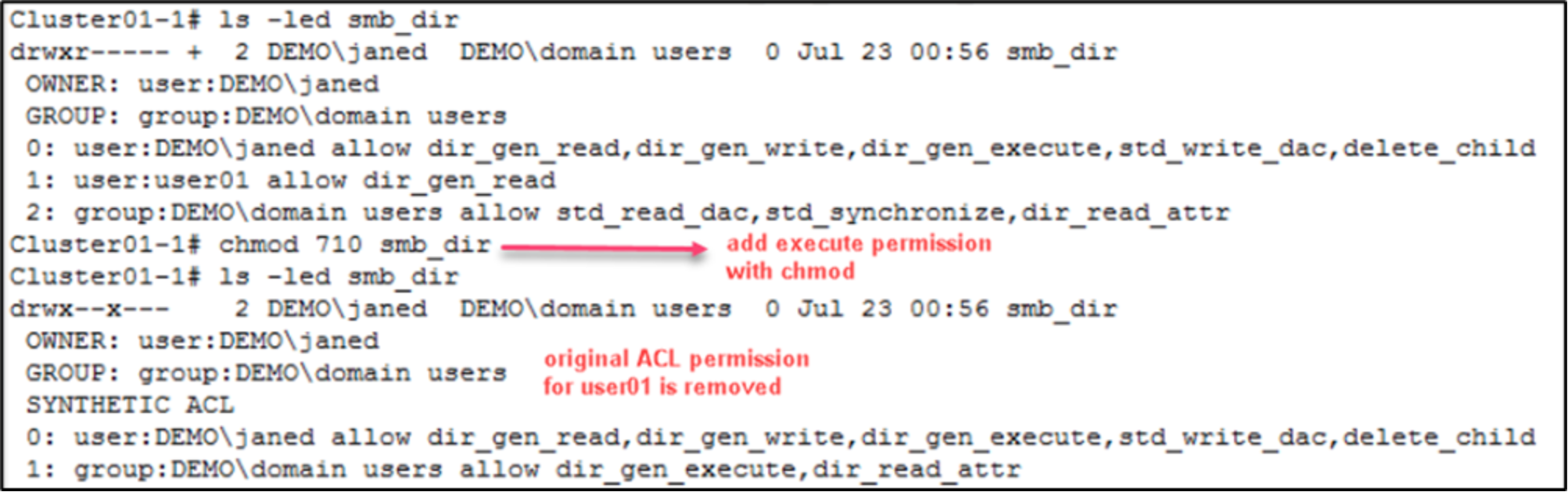
Figure 19. UNIX only behavior
Use chown and chgrp commands on files with existing ACLs
Traditionally, when the ownership of a file is modified in a Windows SMB environment, the ownership’s associated ACEs are not modified and the original permissions are kept. In contrast to Windows, when attempting to change the ownership of a file in a NFS environment, the ownership’s associated permissions are modified.
When running a chown or chgrp command over an NFS client on a file stored by SMB, the conflict between the two models becomes crucial. OneFS provides the option to modify the chown or chgrp behaviors to follow the Windows SMB model or NFS model. It also allows you to ignore the operation if the file has an existing OneFS real ACL.
As Figure 20 shows, under the balanced policy or UNIX only policy, OneFS changes a file’s permission while changing the ownership.
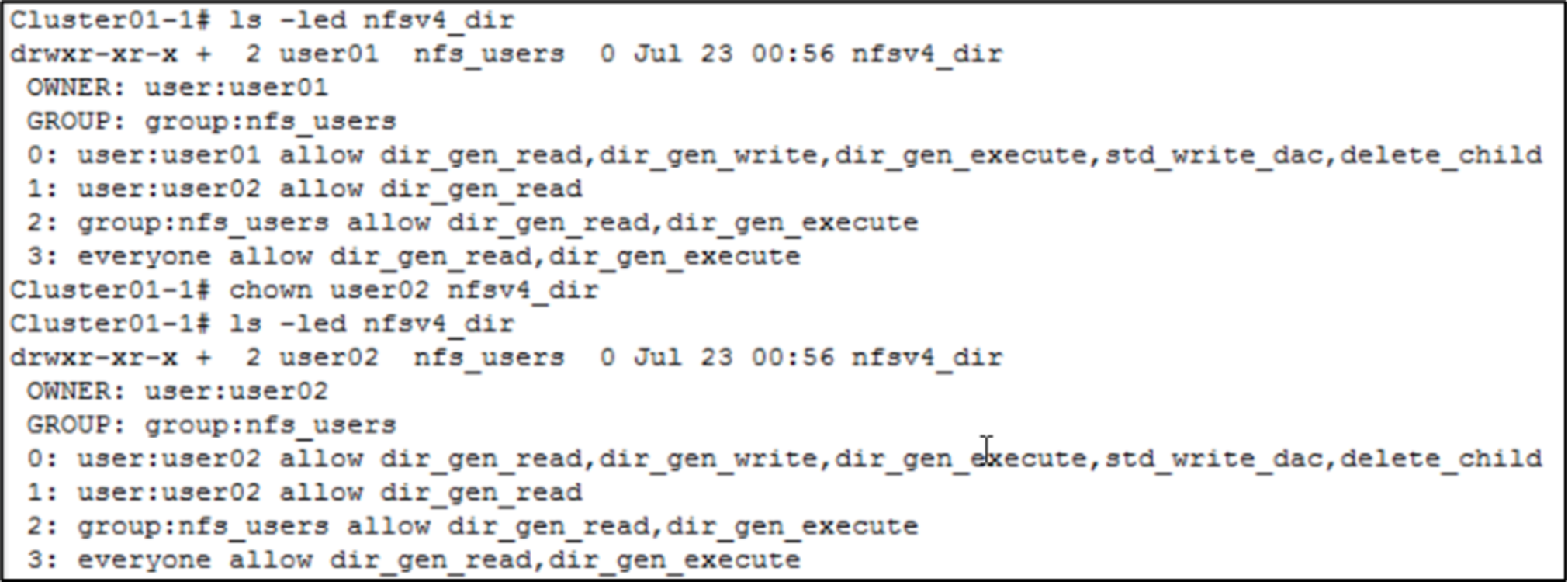
Figure 20. Change ownership
Under the Windows only policy, OneFS will not change file permissions. Shown in Figure 21, OneFS only modifies the owner of the file and keeps the original ACL information.
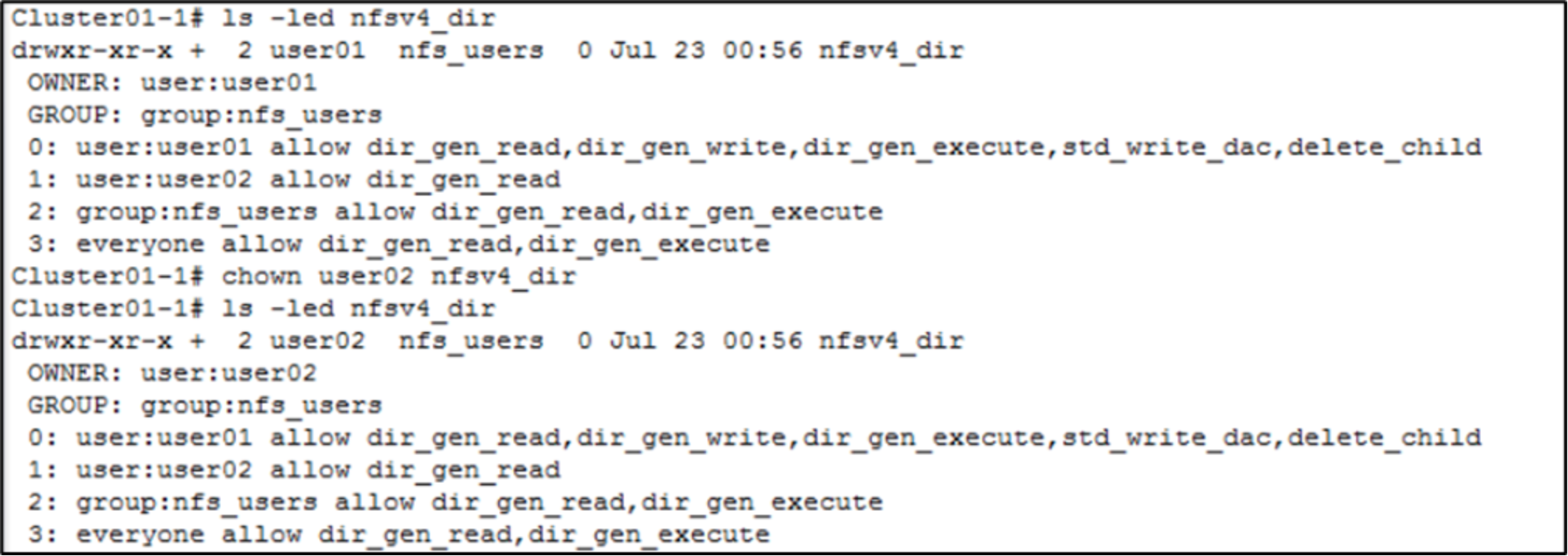
Figure 21. Change ownership under Windows only policy
Synthetic deny ACEs
In Windows, the everyone identity includes every user and group including the owner and the owner group. In POSIX mode bits, the other identity strictly includes everybody except the owner and the owner group on the file. When the other identity has permissions which are not granted to the owner and the owner group, to accurately portray the POSIX mode bits semantics in a OneFS synthetic ACL, deny ACEs are needed for the owner or the owner group.
Due to the difference between everyone in Windows and other in POSIX mode bits, when generating a OneFS synthetic ACL using POSIX mode bits, this setting controls whether OneFS modifies the synthetic ACL by removing deny ACEs. This assumes there is a file containing POSIX mode bits -rwxr-xrwx. By default, OneFS will remove the deny write permission ACEs for the owner group, as shown in Figure 22.
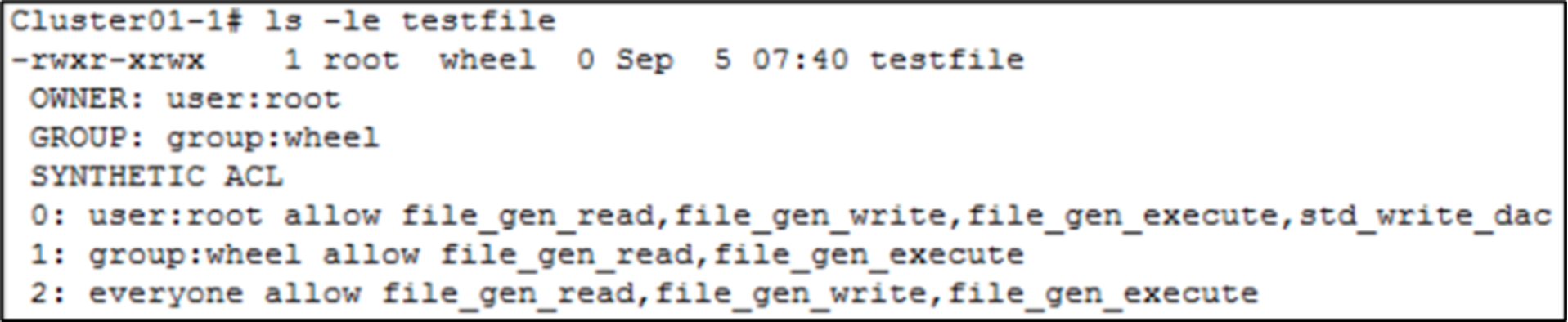
Figure 22. Synthetic ACL with deny ACEs removed
This example changes the ACL policy setting to keep the deny ACEs for the owner group. Shown in Figure 23, the deny ACEs for the owner group are generated in the synthetic ACL.
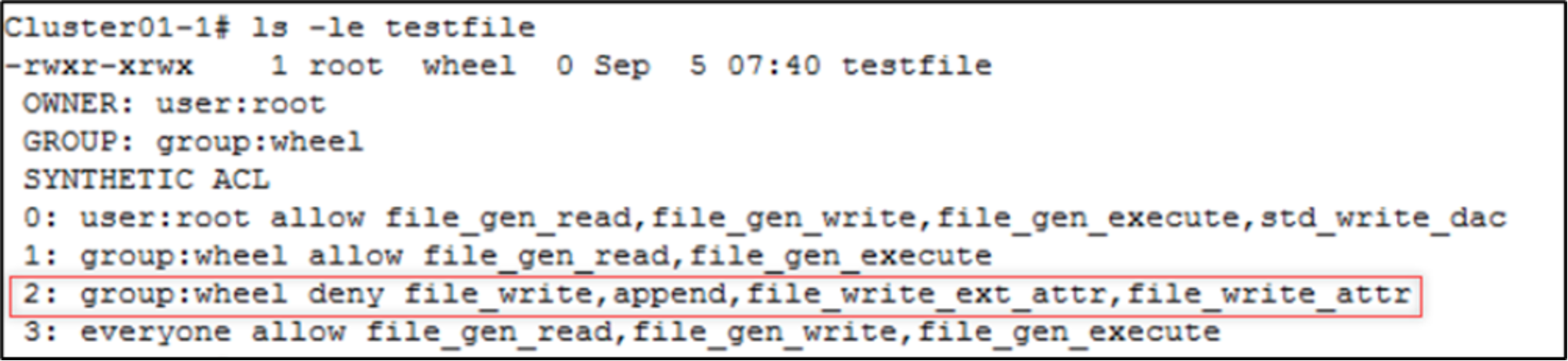
Figure 23. Synthetic ACL without deny ACEs removed
