Home > Storage > PowerScale (Isilon) > Product Documentation > Security and Compliance > Access Control Lists on Dell EMC PowerScale OneFS > ACL on Windows NTFS and SMB
ACL on Windows NTFS and SMB
-
Windows has an access-control model that determines who can access resources in the operating system. Windows applications call access control functions to set who can access specific resources, or to control access to resources provided by the application. See the Microsoft article on Access Control for more details.
An ACL is a key part of the Windows access model. In Windows, ACLs can provide access control to an Active Directory service object. Routines for ACL creation and modification of ACLs are included in Active Directory Service Interfaces (ADSI). The Windows ACL can also provide access control to NTFS file system objects, and the ACLs associated with these file system objects can be managed through Windows Explorer and the command-line tool.
Because SMB is designed for the Windows environment, the SMB ACL is compatible and has the same concepts and definitions as the Windows NTFS ACL. This section discusses the Windows NTFS ACL to show how ACL technology is designed and implemented on the Windows platform.
Security descriptor
A security descriptor contains the security information associated with a file system object, including the owner and primary group, DACL, and SACL of an object.
Run the get-acl PowerShell cmdlet to view the security descriptor of a file-system object.
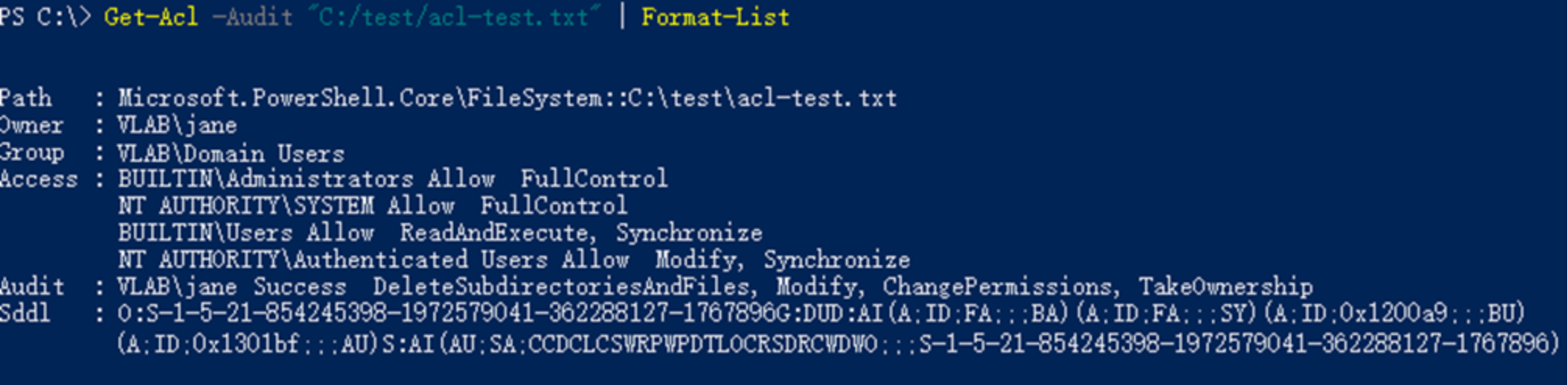
Figure 39. Windows security descriptor
Figure 39 displays the following details:
- Path: This lists the Windows PowerShell path to the file (<provider>::<resource-path>).
- Owner and Group: This is the owner and security group of the file.
- Access: The discretionary access control list (DACL) contains a list of the access control entries for the file. The DACL list is controlled by the owner.
- Audit: The system access control list (SACL) contains a list of entries.
- Sddl: The security descriptor of the resource is displayed in a single text string in the Security Descriptor Definition Language (SDDL) format.
DACL and SACL
A Windows security descriptor contains two types of ACLs (DACL and SACL) for a file system object.
- Discretionary access control list (DACL): This specifies the allowed or denied access rights to a user or group. When a process tries to access a system object, the system checks the ACEs in the object's DACL to determine whether to grant access to it.
- System access control list (SACL): This allows administrators to audit access attempts to a file-system object. An ACE in a SACL can generate audit events when an access attempt fails, when it succeeds, or both. For more information about how to use SACLs on Windows, see the Microsoft articles on Configuring Audit Policies and how to Apply a basic audit policy on a file or folder.
Windows ACE
The ACE is an element in an ACL, and an ACL can have zero or more ACEs. Each ACE controls access to a file-system object by a specified user or group. There are two types of ACEs in a DACL: the first is the access-allow ACE and the second is the access-deny ACE, and both contain the following information:
- User/group: A security identifier (SID) that identifies the trustee to which the ACE applies
- ACE inheritance: A set of inheritance flags that indicate whether the subdirectory and files can inherit the ACE
- ACE type: A flag that indicates the type of ACE (allow or deny)
- Access right: The access rights specified by the ACE
ACE inheritance
An ACE can be explicitly set on an object or it can be inherited. Inheritance allows permissions to be layered or overridden as needed in an object hierarchy and allows for simplified permission management.
There are five flags to indicate ACE inheritance. An ACE only applies to the current file or directory if no ACE inheritance flag is specified. Table 13 shows the five ACE inheritance flags and meanings.
Table 13. Windows ACE inheritance
ACE inheritance flag keyword
Flag set on file or directory
Description
(OI) Object inherit
Directory only
Indicates that an ACE applies to a current directory and files within the directory
(CI) Container inherit
Directory only
Indicates that an ACE applies to a current directory and subdirectories within the directory
(IO) Inherit only
Directory only
Indicates that an ACE applies to subdirectories only, files only, or both within the directory
(NP) No propagate inherit
Directory only
Indicates that an ACE applies to the current directory, only the first-level contents of the directory, or both, but not to the second-level or subsequent contents
(I) Inherited
File or directory
Indicates that an ACE is inherited from the parent directory
Windows Explorer provides a UI to configure ACE inheritance, as highlighted in Figure 40. To access the UI, right-click a directory and click Properties > Security > Advanced > Permissions > Add.
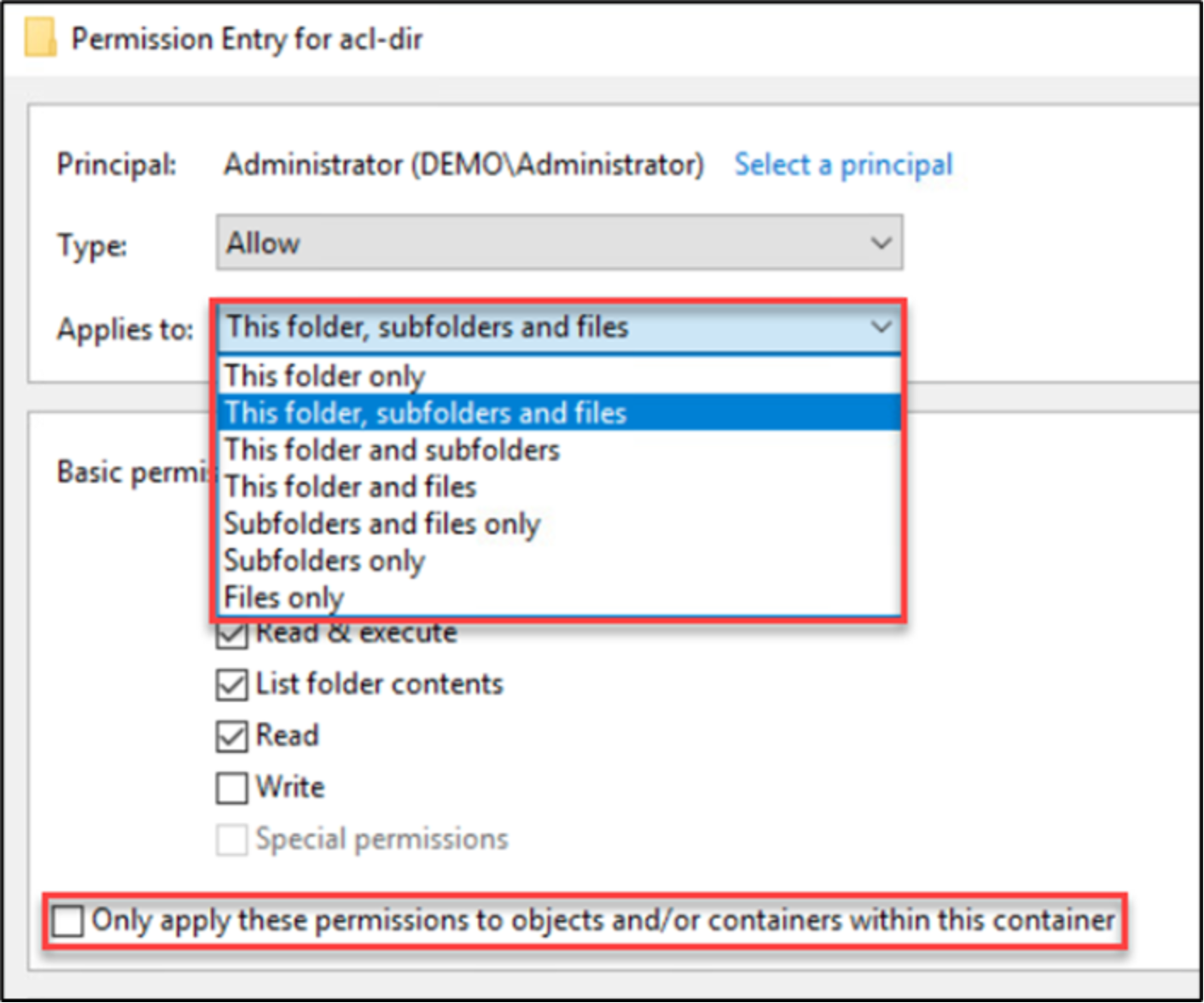
Figure 40. Configuring ACE inheritance flags
Table 14 shows the relationship between each UI option and the exact flags contained.
Table 14. Inheritance UI options
Windows Explorer UI option
Contained ACE inheritance flags
This folder only
No flags, an ACE applies only to the current directory
This folder, subfolders, and files
(OI) (CI)
This folder and subfolders
(CI)
This folder and files
(OI)
Subfolders and files only
(OI) (CI) (IO)
Subfolders only
(CI) (IO)
Files only
(OI) (IO)
Only applies these permissions to objects, containers within this container, or both
(NP)
Order of ACEs in a DACL
When users or groups access a file-system object, the system iterates through the ACEs in the object's DACL until it finds ACEs that allow or deny the requested access.
The access rights that a DACL allows a user could vary depending on the order of ACEs in the DACL. In Windows, a specific ordering of ACEs (a canonical ordering) is enforced. The ordering impacts how permissions are applied, and the rules for ordering are as follows:
- All explicit ACEs are placed before any inherited ACEs.
- Within the group of explicit ACEs, access-denied ACEs are placed before access-allowed ACEs.
- Inherited ACEs are placed in the order in which they are inherited. ACEs inherited from the child object's parent come first, then ACEs inherited from the grandparent, and so on, up the tree of objects.
- For each level of inherited ACEs, access-denied ACEs are placed before access-allowed ACEs.
Access rights
An access right corresponds to a set of operations that a user or group can have on a file-system object. The Windows DACL can be associated with many different Windows system objects, not just files and directories.
Table 15 to Table 17 show Windows NTFS access rights and their associated options in the Windows Explorer UI. To access this UI, right-click a directory and click Properties > Security > Advanced > Permissions > Add.
Table 15. NTFS generic access right
Constant
Keyword
Windows Explorer UI option
Description
GENERIC_ALL
GA
Full control
All possible access rights; maps to Full Control (F)
GENERIC_EXECUTE
GE
N/A
Execute access; maps to RC, S, X, RA
GENERIC_READ
GR
Read
Read access (R); contains permissions RD, RC, RA, REA
GENERIC_WRITE
GW
Write
Write access (W); contains permissions WD, AD, WA, WEA
Table 16. NTFS standard access rights
Constant
Keyword
Windows Explorer UI option
Description
DELETE
DE
Delete
The right to delete the object
READ_CONTROL
RC
Read permissions
The right to read the information in the object's security descriptor, not including the information in the system access control list (SACL); Read permissions
SYNCHRONIZE
S
N/A
The right to use the object for synchronization, which enables a thread to wait until the object is in the signaled state; some object types do not support this access right
WRITE_DAC
WDAC
Change permissions
The right to modify the discretionary access control list (DACL) in the object's security descriptor; change permissions
WRITE_OWNER
WO
Take ownership
The right to change the owner in the object's security descriptor. Take ownership.
Table 17. File-system object access rights
Constant
Keyword
Windows Explorer UI option
Description
FILE_READ_DATA
RD
Read data
The right to read data from the file
FILE_LIST_DIRECTORY
List folder
The right to list the contents of a directory
FILE_WRITE_DATA
WD
Write data
The right to write data to the file
FILE_ADD_FILE
Create files
The right to create a file in a directory
FILE_APPEND_DATA
AD
Append data
The right to append data to the file.
FILE_ADD_SUBDIRECTORY
Create folders
The right to create a subdirectory in a directory
FILE_READ_EA
REA
Read extended attributes
The right to read extended attributes
FILE_WRITE_EA
WEA
Write extended attributes
The right to write extended attributes
FILE_EXECUTE
X
Execute file
The right to execute a file
FILE_TRAVERSE
Traverse folder
The right to traverse a directory
FILE_DELETE_CHILD
DC
Delete subfolders and files
The right to delete a directory and all the files it contains (its children), even if the files are read-only
FILE_READ_ATTRIBUTES
RA
Read attributes
The right to read file attributes
FILE_WRITE_ATTRIBUTES
WA
Write attributes
The right to change file attributes
Windows Explorer UI basic and advanced permissions mapping
For the convenience of routine permissions management, Windows defines several basic permissions that contain a set of individual advanced permissions. To view these options through the Windows Explorer UI, right-click a file and click Properties > Security > Advanced > Permissions > Add. Table 18 shows the mapping between the permissions.
Table 18. Basic and advanced permissions in the Windows Explorer UI
Advanced permissions
Basic permissions
Full control
Modify
Read and execute
Read
Write
Traverse folder/ execute file
List folder/read data
Read attributes
Read extended attributes
Create files/write data
Create folders/append data
Write attributes
Write extended attributes
Delete subfolders and files
Delete
Read permissions
Change permissions
Take ownership
Synchronous
A.1.2 Examples
The following examples use the Windows Explorer UI to set permissions and the icacls command-line tool to check the exact permissions applied.
Example 1: Windows NTFS ACL’s ACE inheritance
This example removes all inherited ACEs from the top-folder and adds four new ACEs, shown in Figure 41 Error! Reference source not found. The following ACEs are added:
- ACE 0: Grants group Administrators the Full control permission on the folder, and propagates permissions to all subfolders and files. This means the ACE contains inheritance flags (OI)(CI).
- ACE 1: Grants user janed the Read permission on the folder only. No inheritance flag is set on this ACE.
- ACE 2: Grants user johnd the Read permission on all subfolders and files under the folder, not the folder itself. This means the ACE contains inheritance flags (OI)(CI)(IO).
- ACE 3: The last ACE has the option enabled (highlighted with the red rectangle), which means the ACE will only apply to the first-level content within the folder. This ACE only grants user joedthe Read permission on first-level contents of the folder. This means the ACE contains inheritance flags (OI)(CI)(NP)(IO).
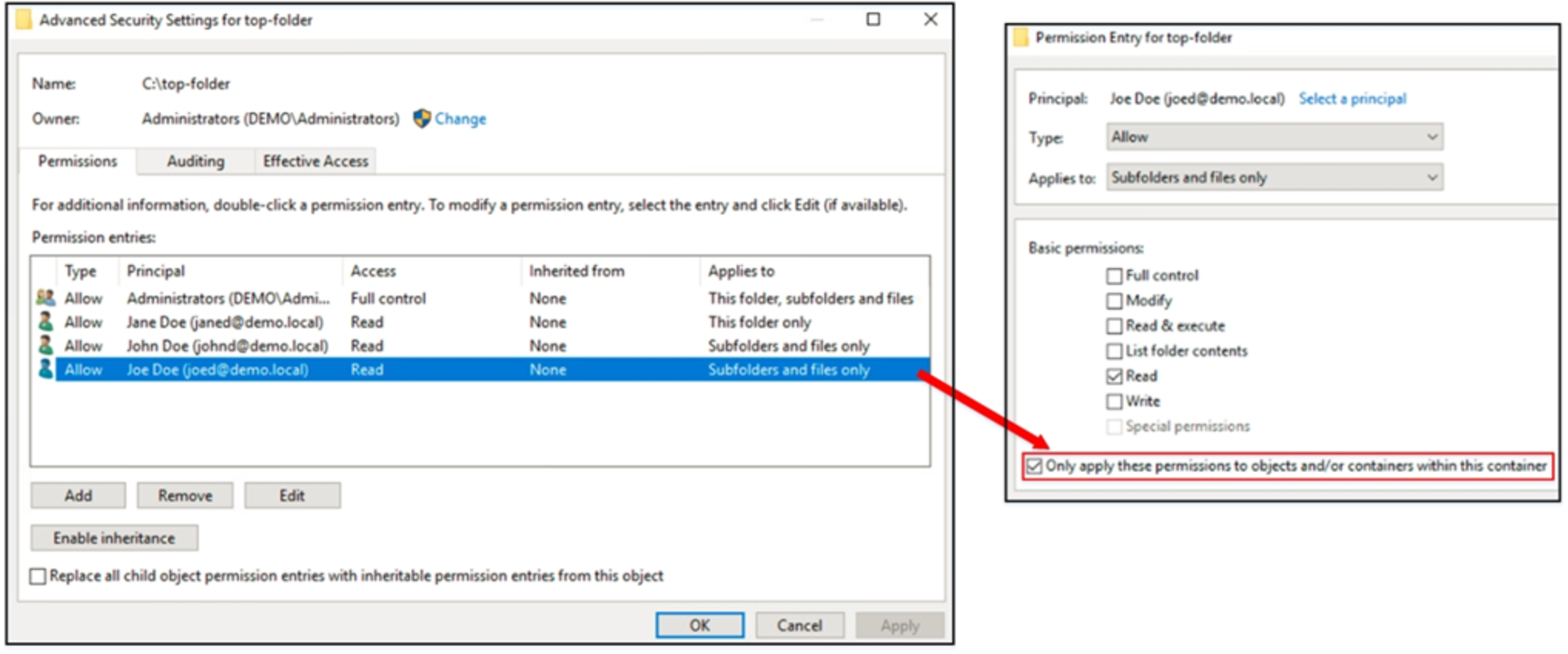
Figure 41. ACEs of top-folder
Use the iscacls command to check the inheritance flags on the folder’s ACL, as shown in Figure 42:
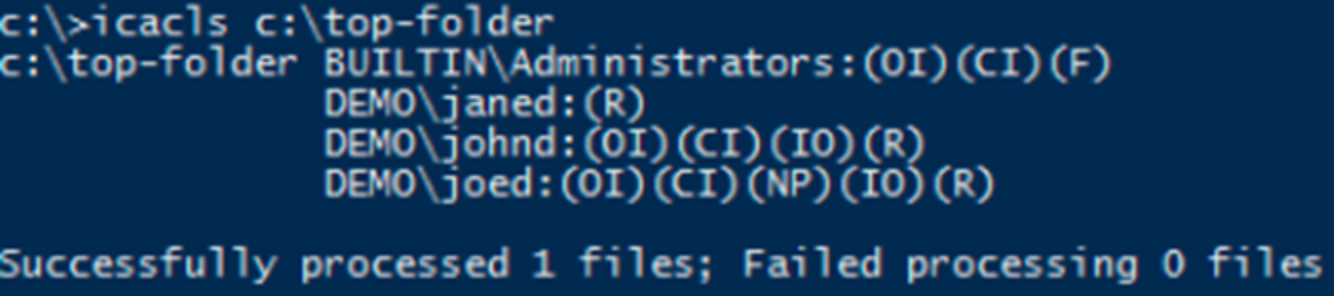
Figure 42. Inheritance flags
Now, verify the ACE inheritance on the first-level folder and second-level folder under the top-folder.
As Figure 43 shows, ACE 1 is not inherited to the folder-level-1. The rest of ACEs are inherited as expected.
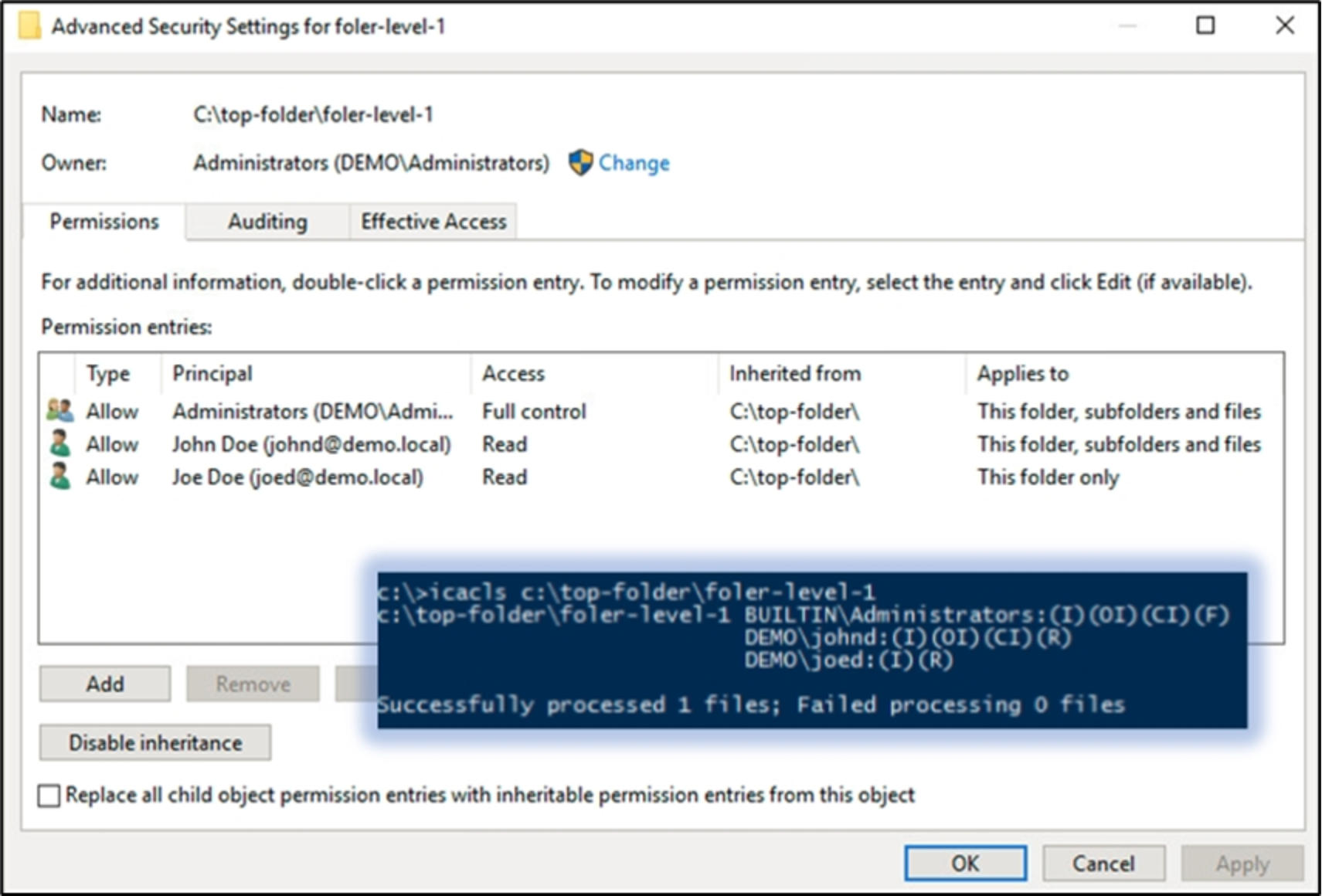
Figure 43. ACEs on first-level folder
As Figure 44 shows, ACE 1 is not inherited to the folder-level-2 and ACE 3 is also not inherited because it is applied a (NP) flag on top-folder. The rest of ACEs are inherited as expected.
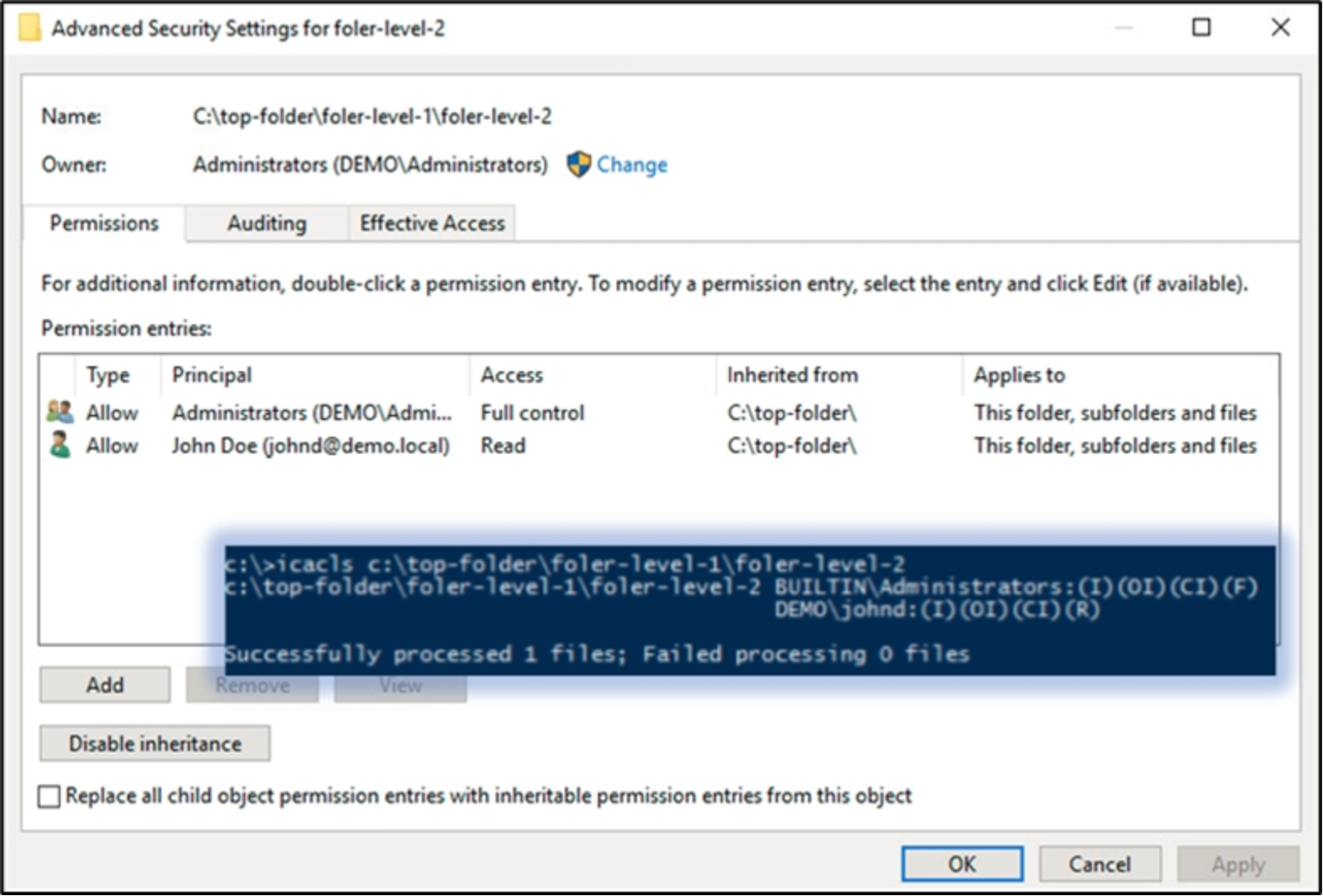
Figure 44. ACEs on second-level folder
Example 2: Order of ACEs in a DACL
Add access-allow ACEs and access-deny ACEs on both top-folder and folder-level-1 as shown in Figure 45
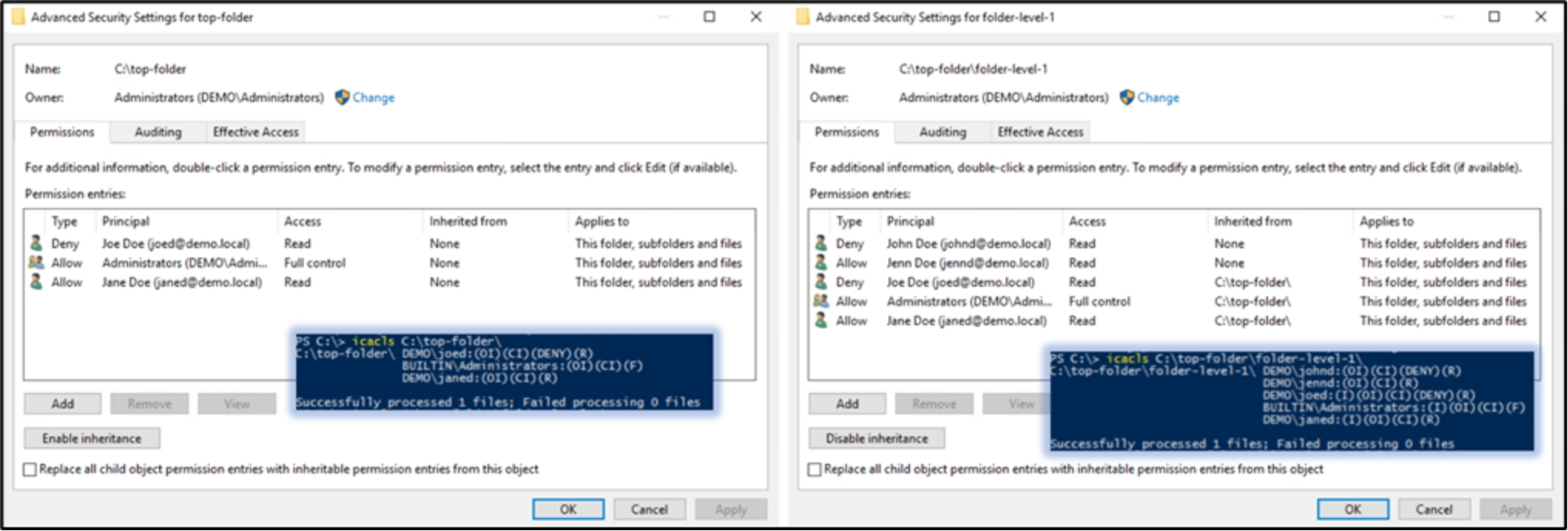
Figure 45. ACEs on top-folder and folder-level-1
As mentioned in section A.1.1, the order of ACEs on folder-level-2 is as expected. Shown in Figure 46, a group of all the explicit ACEs (highlighted in red) are placed before any other inherited ACEs, and then a group of ACEs (highlighted in blue) inherited from the parent folder folder-level-1 come first, then ACEs (highlighted in yellow) are inherited from the grandparent folder top-folder. Meanwhile, in each group of ACEs, access-deny ACEs are always placed before access-allow ACEs.
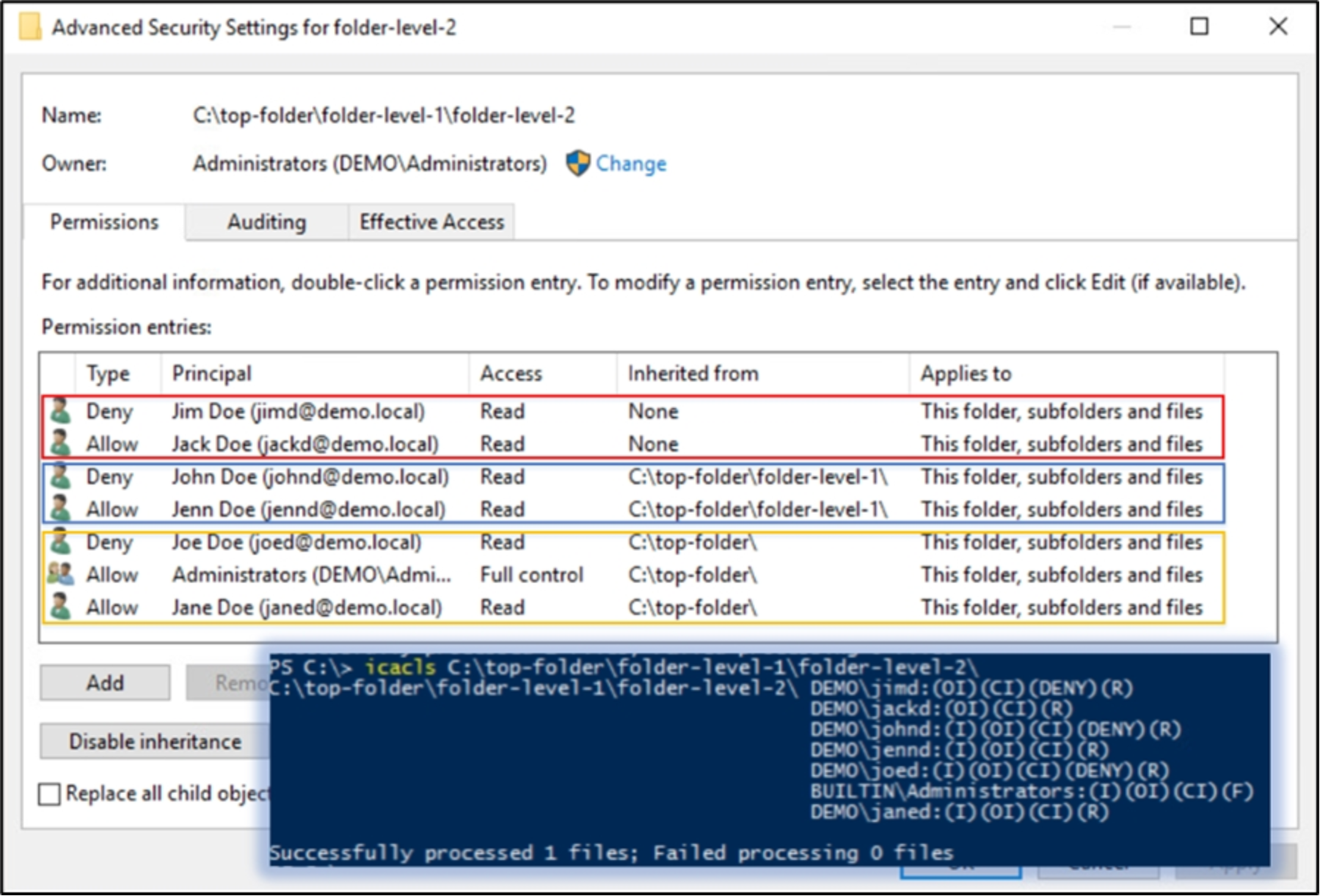
Figure 46. Order of ACEs on folder-level-2
