Home > APEX > Cloud Platforms > Guides > Dell APEX Cloud Platform for Microsoft Azure Tech Book > Intrinsic infrastructure security features
Intrinsic infrastructure security features
-
Dell APEX Cloud Platform for Microsoft Azure comes bundled with intrinsic infrastructure security management features. Combined with the security features that come out-of-the-box with Azure Stack HCI, your platform is fully protected against current and future threats.
The two security management features leveraged in Dell’s APEX Cloud Platform for Microsoft Azure are:
- Infrastructure lock
- Secured-core server
Infrastructure lock
Infrastructure Lock is a feature of Dell APEX Cloud Platform Foundation Software. The Dell APEX Cloud Platform extension in Windows Admin Center provides a toggle switch that enables and disables the System Lockdown feature of Dell iDRAC on a cluster-wide basis.
Enabling Infrastructure Lock on all the MC nodes in a cluster:
- Protects against unintentional or malicious changes to critical configuration settings in the BIOS or iDRAC
- Prevents unapproved updates of BIOS, iDRAC, firmware, and drivers
All the MC nodes in a cluster will have System Lockdown disabled after initial cluster deployment. However, it is strongly advised to enable it after the platform is fully operational.
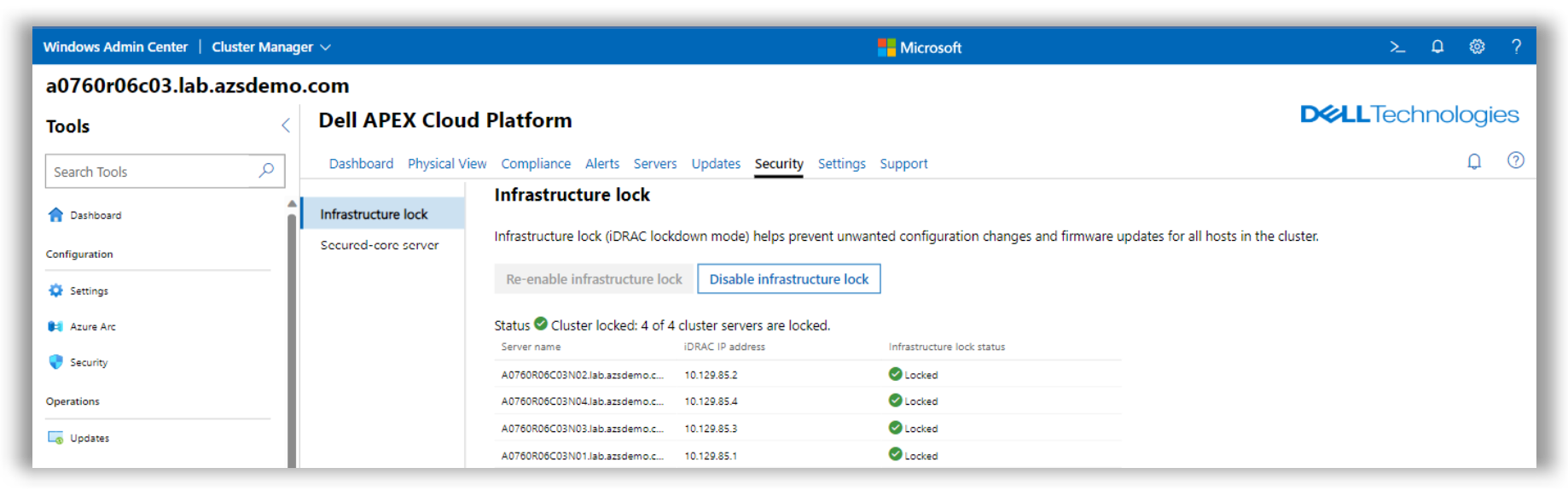
Figure 45. Infrastructure lock can be easily enabled in a cluster wide basis, protecting MC nodes against malicious changes
When infrastructure lock is enabled, the iDRAC UI will alert about the impossibility of performing configuration changes in that server as expected.

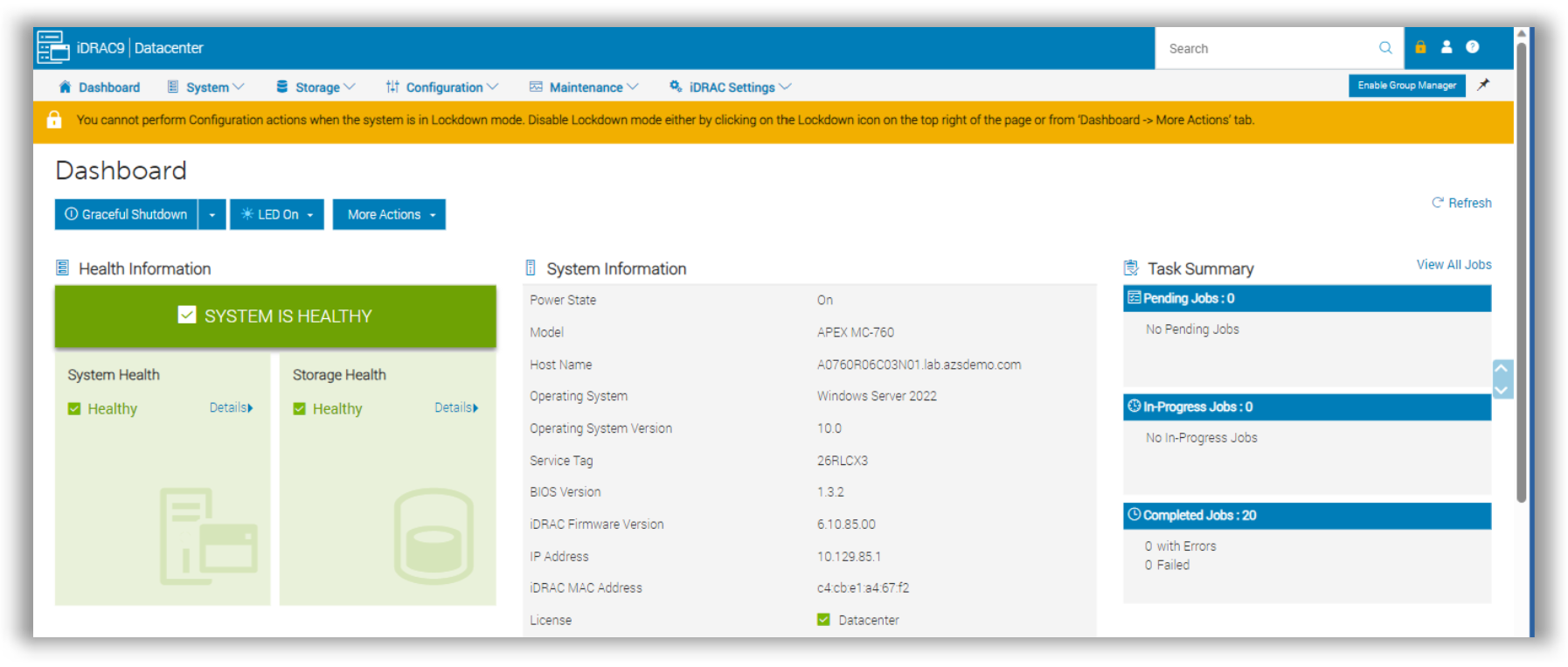
Figure 46. MC-760 iDRAC console showing infrastructure lock enabled, thus impeding configuration changes
Secured-core server
Secured-core server helps proactively defend against and disrupt many of the paths attackers might use to exploit a system by establishing a hardware root-of-trust, protecting firmware, and introducing virtualization-based security.
To fully enable secured-core server, settings must be configured in the BIOS and operating system. In the case of Dell APEX Cloud Platform for Microsoft Azure, a secured-core server is fully enabled during initial deployment.
If any required settings get changed, you can return them to fully secured-core server compliant using the Windows Admin Center extension with no disruption to running workloads.
Secure-core server policies can only be modified in the nodes of the Azure Stack HCI cluster if infrastructure lock is disabled. If this happens in any node of a cluster, it is very simple to bring the node/nodes back to full security by navigating to the Security tab in the Windows Admin Center extension and Re-enabling secured-core server.

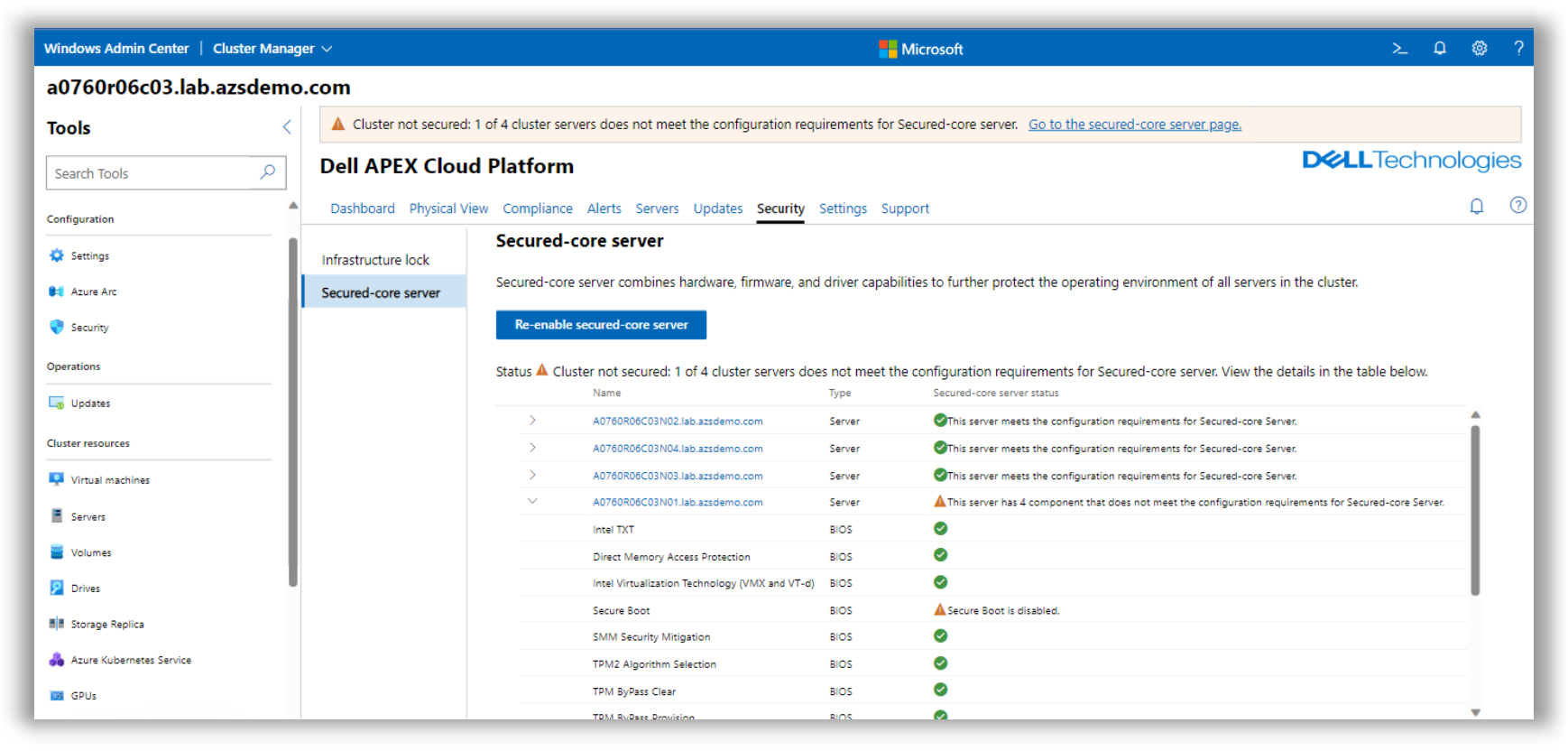
Figure 47. A node in the Azure Stack HCI cluster is not meeting the Secure-core server requirements, as the Secure Boot policy has been disabled
To correct these configuration settings requires restarting the cluster node. This will be done in a non-disruptive manner by placing the affected node in maintenance mode and Live Migrating the running VMs to another node.
By leveraging these two security features, Infrastructure Lock and secured-core server, we can maintain a strong security posture on these infrastructure platforms.
