This section provides an overview of the built-in Azure HCI security features. Implementing these features is highly recommended to help add extra layers of security to this solution.
Dell MC Nodes overview
Dell Solutions for Azure Stack HCI offers stretched cluster solutions with MC nodes from Dell Technologies. Built using industry-leading PowerEdge servers, MC nodes offer fully validated HCI nodes for a variety of use cases. A robust set of configurations and different models allows you to customize your infrastructure for application performance, capacity, or deployment location requirements.
Security
Security that is incorporated into the design is a key tenet of Microsoft Azure Stack Hub. Security features enabled for the solution are described in the following sections.
Firmware
The following are built-in security features in the Azure HCI solution that help protect the system's firmware:
- TPM 2.0 and SecureBoot are enabled by default.
- All firmware and driver update packages are signed.
- Firmware updates are secured with the use of Windows Cryptograms implementations.
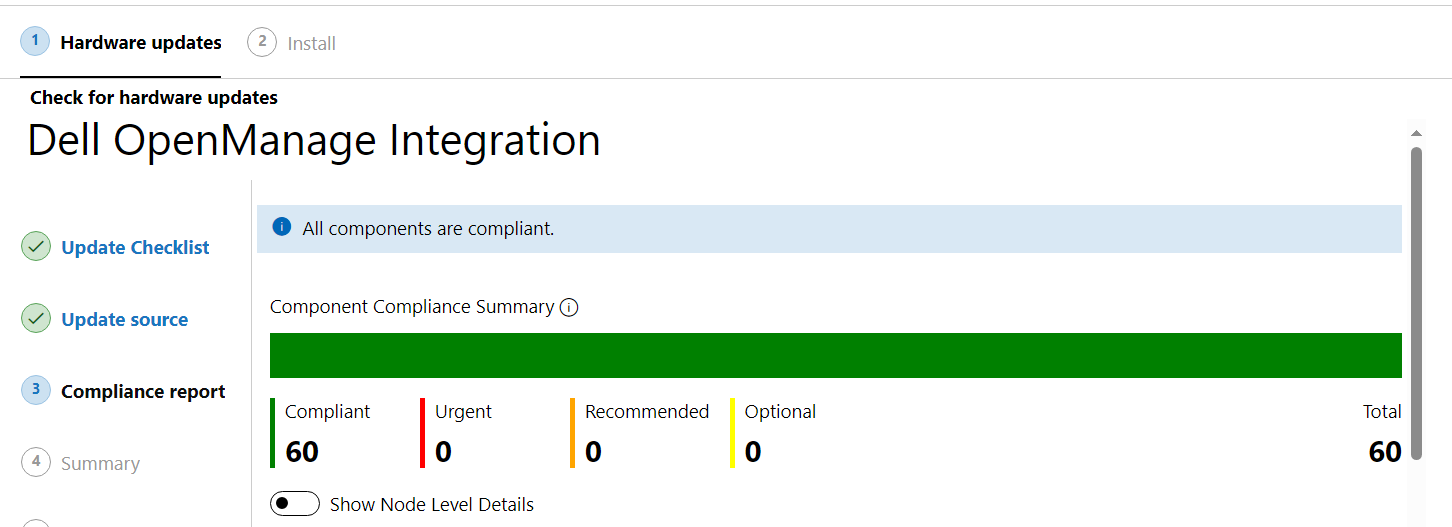
- It is highly recommended to apply all hardware upgrades and make sure all component compliance is addressed.
Software
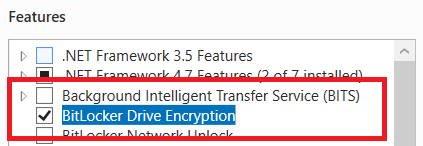
BitLocker is enabled on all hard drives. Bitlocker is a Windows disk encryption feature, designed to protect data by providing encryption for entire volumes.
BitLocker addresses the threats of data theft or exposure from lost, stolen, or inappropriately decommissioned devices.
BitLocker provides maximum protection when used with a Trusted Platform Module (TPM). A TPM is a hardware component installed in many devices and it works with BitLocker to help protect user data and to ensure that a computer has not been tampered with while the system is offline.
Under Server Roles, users can enable BitLocker for the entire volume.
BitLocker provides the following benefits:
- Defense Information System Agency (DISA) Security Technical Implementation Guide (STIG) class security policies are applied and enabled.
- Device guard and credential guard are enabled.
- Allowlisting is enabled to ensure that unknown software cannot be run on host systems.
- Defender is enabled on the Hardware Lifecycle Host (HLH) host for anti-malware.
- Federal Information Processing Standards (FIPS) 140-2 compliant crypto algorithms are used for internal stack communication.
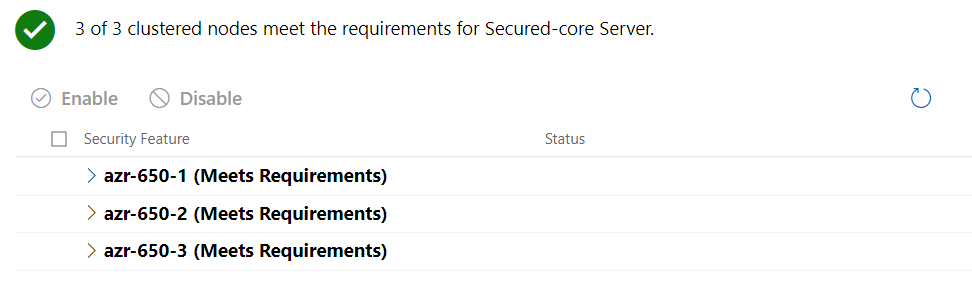
After all the security requirements are fulfilled, verify that the AX nodes have met the requirements.
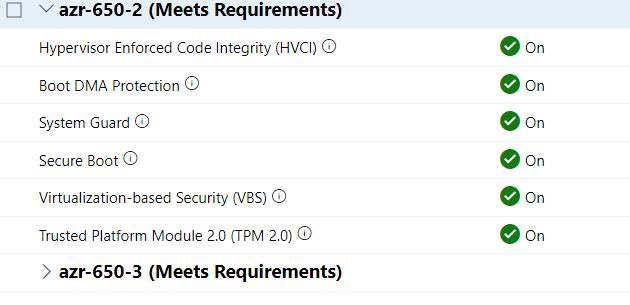
Secured-core server
Certified Secured-core server hardware from an OEM partner like Dell provides more security protections that are useful against sophisticated attacks. Certified Secured-core server hardware can provide increased assurance when handling mission-critical data in some of the most data sensitive industries.
A Secured-core server uses hardware, firmware, and driver capabilities to enable advanced Windows Server security features.
Cluster and network traffic
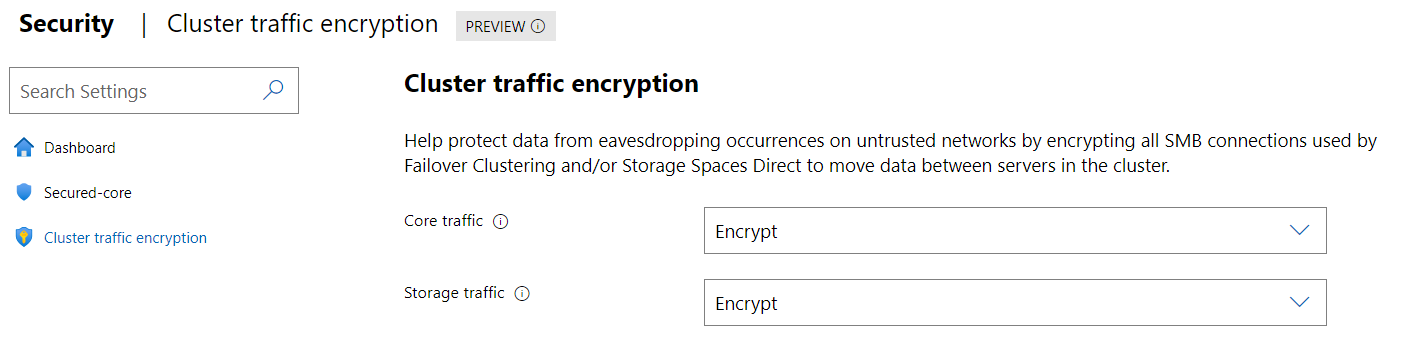
Users are recommended to encrypt cluster and network traffic. This can be done in the Cluster traffic encryption menu as shown in the following figure. Make sure to encrypt both Core and Storage traffic if possible.
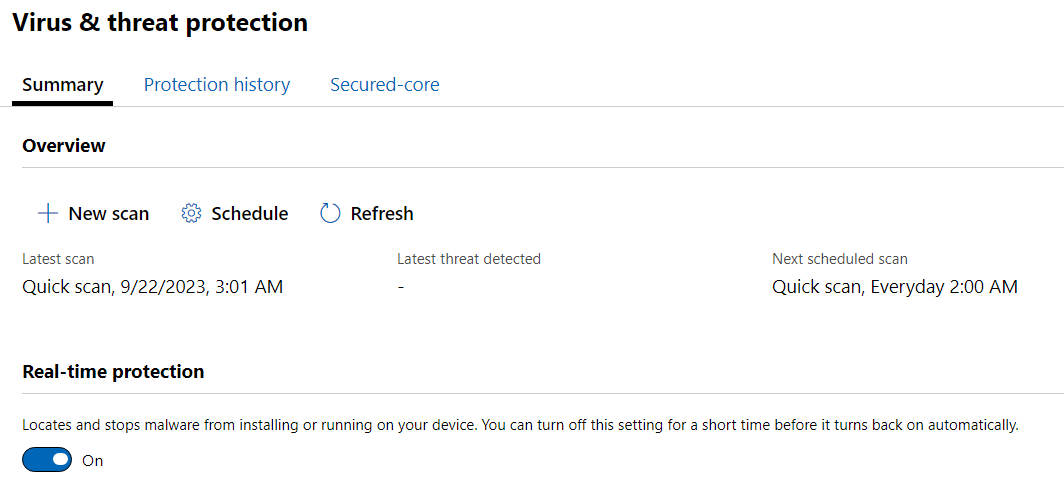
It is also recommended to enable periodic security protection and scanning by enabling the Virus & threat protection scan, as shown in the following figure.
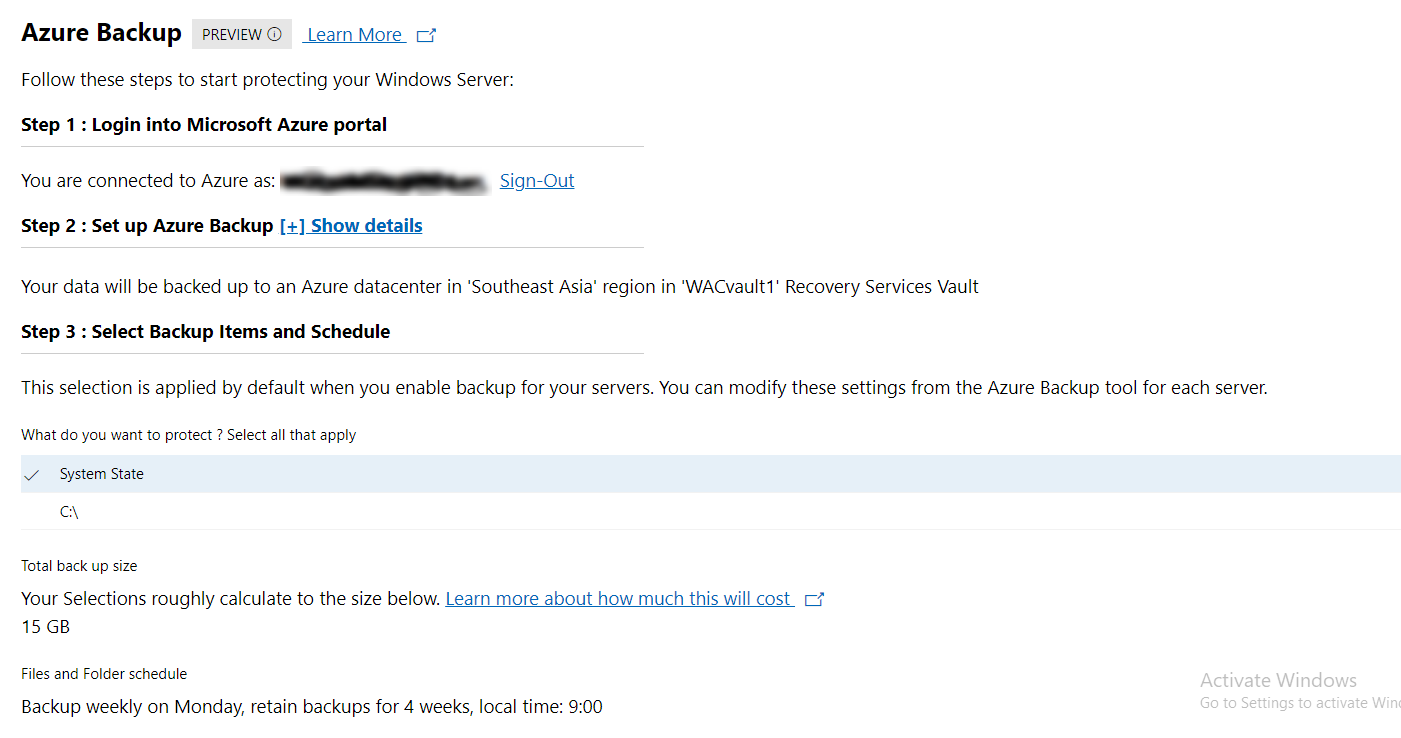
Data protection with Azure Backup
Azure Backup is a cost-effective, secure, one-click backup solution that is scalable based on customer backup storage needs. The centralized management interface makes it easy to define backup policies and protect a wide range of enterprise workloads.
Least-privilege authority
Dell Technologies hardware and software can enable multiple roles and users. To ensure security and meet least-privilege authorization requirements for Azure Stack Hub, Dell Technologies defines the operator and administrator roles at deployment to designate the minimum authorization that is required to perform each operation.
These roles include the following:
- Operator—Minimum privilege to read but not modify
- Server Admin—Full access to update, modify, reboot, and so on
- Switch Admin—Full access to reboot and update
Dell Technologies deployment engineers can help customers enable additional users and roles for the HLH.
Secrets rotation
Dell Technologies recommends that, on a regular cadence, users rotate secrets that are contained in the switches, HLH, and iDRACs (for example, passwords, certificates, or string keys). At the end of the deployment period, Dell Technologies assists the operator, if required, to set up accounts and remove any well-known usernames and passwords.
For more information about guidance on secrets in use and how to use the available tools, see Rotate secrets in Azure Stack Hub on the Microsoft website.
The following table lists the supported Azure Stack Hub rotation matrix.
| Certificate installed | Rotate certificate to | Supported | Azure Stack Hub release |
| Self-Signed | Enterprise | Supported | 1903 and later |
| Self-Signed | Public | Supported | 1803 and later |
| Self-Signed | Self-Signed | Not supported | N/A |
| Enterprise | Public | Supported | 1803 and later |
| Enterprise | Self-Signed | Not supported | N/A |
| Enterprise | Enterprise | This is supported in 1803 if customers use the same enterprise CA that is used at deployment. | 1803 and later |
| Public | Self-Signed | Not supported | N/A |
| Public | Enterprise | Not Supported | N/A |
| Public | Public | Supported | 1903 and later |
HLH-related password changes
By default, Windows Server 2022 account passwords on the HLH host and Management VM are set to expire after 30 days. This default includes the Administrator accounts and any other operator accounts that are created during deployment. These operating system account passwords can be changed through the system settings in Windows Server 2019.
If the passwords are allowed to expire, then users must open a console session to perform a reset. RDP connections are unable to connect if the password has expired. For the Management VM, users can open the console session from the Hyper-V manager on the HLH host. For the HLH host, users must use a physical console or iDRAC virtual console.
