Home > Workload Solutions > Container Platforms > Red Hat OpenShift Container Platform > White Papers > White Paper—Red Hat OpenShift Container Platform 4.12 on Dell Infrastructure > OpenShift cluster topologies
OpenShift cluster topologies
-
The following OpenShift cluster topologies provide different levels of server footprint and high availability (HA):
- Multinode cluster, which can be:
- A compact three-node cluster hosting the control plane and the data plane on the same nodes.
- A standard five-plus node cluster or the remote compute node cluster separating out the compute nodes from the control plane nodes.
- Single node cluster
- A cluster which bundles both control-plane and data-plane capabilities into a single server and provides users with a consistent experience across the sites where OpenShift is deployed.
Multinode cluster design
The following figure shows the design for a multinode OpenShift cluster on Dell infrastructure:
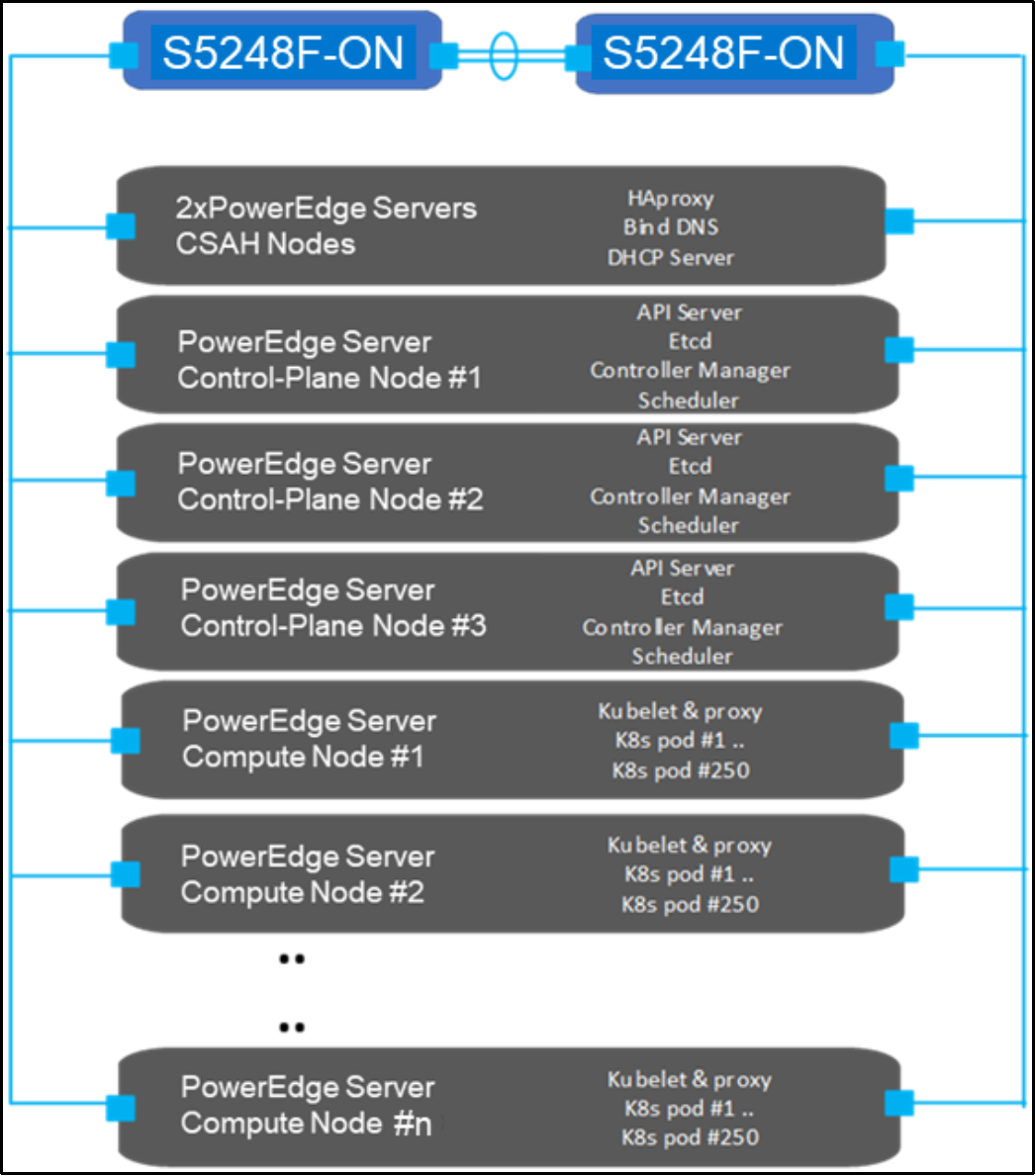
Figure 1. Multinode OpenShift cluster design
CSAH nodes
The deployment process requires an admin node called Cluster System Admin Host (CSAH). The CSAH node can also act as the provisioner node for deploying OpenShift Cluster Platform on Installer Provisioned Infrastructure (IPI). For more information, see Installation Overview.
Note: Red Hat official documentation does not refer to a CSAH node in the deployment process.
CSAH nodes are not part of the OpenShift cluster, but are recommended for OpenShift cluster administration and operation. CSAH nodes can also provision additional infrastructure services if required, such as Dynamic Host Configuration Protocol (DHCP), Preboot Execution Environment (PXE), Domain Name System (DNS), and HAProxy services for cluster deployment and operation.
You can use a single CSAH node for development and testing purposes, but this approach does not provide resilient load-balancing. For resilient load-balancing, Dell Technologies recommends:
- Using two CSAH nodes running HAProxy and KeepAlived. The OpenShift CLI tool oc and the authentication tokens that are required to administer the OpenShift cluster are installed on both CSAH nodes as part of the deployment process. Dell Technologies strongly discourages directly logging in to a control-plane node to manage the cluster.
- Storing backups of OpenShift authentication credentials outside the cluster for redundancy.
Note: Control-plane nodes are deployed using immutable infrastructure, further driving the preference for an administration host that is external to the cluster.
Bootstrap node
The CSAH nodes manage the operation and installation of the container ecosystem cluster. Cluster installation begins with creating a bootstrap VM on the primary CSAH node to install control-plane components on the nodes. The initial minimum cluster can consist of three nodes that run both the control plane and applications, or three control-plane nodes and at least two compute nodes.
Node components
Node components are installed and run on every node in the cluster. The following components are responsible for all node run-time operations:
- Kubelet: An agent that runs on each node to perform declarations or actions that are provided to the cluster-API.
- Kube-proxy: An instance of kube-proxy runs on every node of the cluster. The kube-proxy instance implements Kubernetes network services that run on the node, and also manages network connectivity and traffic route management.
- Container run-time: The chosen CRE must be deployed on each node in a Kubernetes cluster. The CRE must comply with the Kubernetes CRI specifications. OpenShift Container Platform defaults to the CRI-O container run-time and cannot be changed.
For more information, see Overview of nodes.
Control-plane nodes
Control-plane nodes implement control-plane infrastructure management. Three control-plane nodes establish a unified control plane for the operation of an OpenShift cluster. The control plane operates outside the application container workloads and provides the overall continued viability, health, availability, and integrity of the container ecosystem.
The control plane provides Kubernetes services and OpenShift services:
- Kubernetes services:
- API server: The API server exposes the Kubernetes control-plane API for other platform services (such as a web console) to consume and has API endpoints to manage cluster resources.
- etcd: This highly available and consistent key-value store can maintain Kubernetes cluster data. The etcd daemon runs on each control-plane node and requires a majority consensus to achieve a quorum (the formula is
 , where n is the number of control plane nodes). Three control-plane nodes are required for an OpenShift cluster, each running an etcd daemon, which means that quorum requires at least two control planes.
, where n is the number of control plane nodes). Three control-plane nodes are required for an OpenShift cluster, each running an etcd daemon, which means that quorum requires at least two control planes. - Scheduler: The Kubernetes scheduler assigns new pods to a node that are based on the resource requirements (such as CPU, RAM, and GPU) and the affinity and anti-affinity mechanisms.
- Controller manager: The controller managers run all controller processes. While each controller process is independent, the processes are run as a single executable to reduce complexity. The controllers include the node, replication, endpoints, service, and token controllers.
- OpenShift services:
- OpenShift API server: The OpenShift API server validates and configures the data for OpenShift resources such as projects, routes, and templates. The OpenShift API server is managed by the OpenShift API server operator.
- OpenShift Controller Manager: The OpenShift Controller Manager monitors etcd for changes to OpenShift objects such as project, route, and template controllers, and then uses the API to enforce the specified state. The OpenShift controller manager is managed by the OpenShift controller manager operator.
- OpenShift OAuth API server: The OpenShift OAuth API server validates and configures the data for OpenShift Container Platform authentication, such as users, groups, and OAuth tokens. The OpenShift OAuth API server is managed by the cluster authentication operator.
- OpenShift OAuth server: Users request tokens from the OpenShift OAuth server to authenticate themselves to the API. The OpenShift OAuth server is managed by the cluster authentication operator This Dell Validated Design (DVD) for OpenShift Container Platform 4.12 enables you to develop, validate, and deploy your containerized applications with a focus on running cloud-native applications on containers that are managed by OpenShift Container Platform. The solution has been optimized and validated for an on-premises bare-metal deployment of OpenShift Container Platform 4.12.
For more information, see Control plane architecture.
Backups and disaster recovery
Although OpenShift Container Platform is resilient to node failure, regularly backing up the etcd data store is recommended. These backups are a blocking procedure, so taking them at off-peak hours is recommended in production environments. For example, if you update a cluster within minor versions (such as from 4.12.2 to 4.12.3), take an etcd backup of the version of OpenShift Container Platform that is running on your cluster or clusters. Also take etcd backups 24 hours after the cluster has been installed to let the initial rotation of certificates occur and ensure that expired certificates are not present. For more information, see Backing up etcd.
Because of the etcd quorum requirements, if enough control-plane nodes fail (which would cause most control planes to stop operating), restoring from a previous cluster state becomes the only option for cluster recovery. Follow the steps in Restoring to a previous cluster state. If most control-plane nodes are still operating, which means that quorum can be achieved but there is no redundancy for further node failure, replace the unhealthy etcd members. Follow the steps in Replacing an unhealthy etcd member.
Compute nodes
In an OpenShift cluster, application containers are deployed to run on compute nodes by default. Cluster nodes advertise their resources and resource use so that the scheduler can allocate containers and pods to these nodes and maintain a reasonable workload distribution. The Kubelet service runs on all nodes in a Kubernetes cluster. This service receives container deployment requests and ensures that the requests are instantiated and put into operation. The Kubelet service also starts and stops container workloads and manages a service proxy that handles communication between pods that are running across compute nodes.
Logical constructs called machine sets define compute node resources. Machine sets can match requirements for a pod deployment to a matching compute node. OpenShift Container Platform supports defining multiple machine types, each of which defines a compute node target type.
You can add or delete compute nodes only if doing so does not compromise cluster viability. If the control-plane nodes are not designated as schedulable, at least two viable compute nodes must always be operating to run router pods that manage ingress networking traffic. Further, enough compute platform resources must be available to sustain the overall cluster application container workload.
For more information, see the following Red Hat OpenShift documentation:
- Advertise Extended Resources for a Node
- About control plane machine sets
- OpenShift Container Platform Ingress Operator
Single-node clusters
- In a single-node cluster, the control-plane node and the compute nodes are hosted on a single server. The primary use case for this type of deployment is edge computing workloads. Workloads that require independent Kubernetes clusters at edge sites can deploy a smaller OpenShift Container Platform footprint on edge-optimized Dell platforms.
- For optimal system resource usage, many operators are configured to reduce this footprint on a single-node cluster. To deploy a single-node cluster with Internet access, use the Assisted Installer for OpenShift Container Platform (access requires Red Hat login credentials).The assisted installer generates an on-demand discovery ISO that can boot the server. Installation is zero-touch, which means the assisted installer service drives the deployment and the installation process does not need to contact out-of-band (OOB) management platforms.
